Security Protocols II: Syntax and Operational Semantics (Part 1)
Security Protocols II: Syntax and Operational Semantics (Part 1)
Security Protocols II: Syntax and Operational Semantics (Part 1)
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
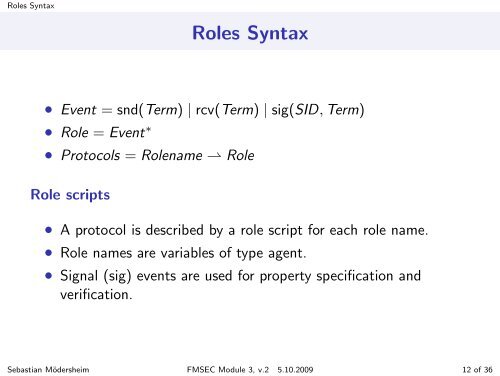
Roles <strong>Syntax</strong>Roles <strong>Syntax</strong>• Event = snd(Term) | rcv(Term) | sig(SID, Term)• Role = Event ∗• <strong>Protocols</strong> = Rolename ⇀ RoleRole scripts• A protocol is described by a role script for each role name.• Role names are variables of type agent.• Signal (sig) events are used for property specification <strong>and</strong>verification.Sebastian Mödersheim FMSEC Module 3, v.2 5.10.2009 12 of 36