Security Protocols II: Syntax and Operational Semantics (Part 1)
Security Protocols II: Syntax and Operational Semantics (Part 1)
Security Protocols II: Syntax and Operational Semantics (Part 1)
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
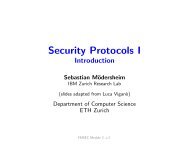
Roles <strong>Semantics</strong><strong>Operational</strong> <strong>Semantics</strong>Definition (State)• State = Trace × IntruderKnowledge × Threads.• Trace = (TID × Event) ∗• IntruderKnowledge = P(Term)• Threads = TID ⇀ Rolewhere the trace <strong>and</strong> the intruder knowledge are ground <strong>and</strong> thethreads are closed.• The TID are Thread IDs for each honest agent playing a role.Sebastian Mödersheim FMSEC Module 3, v.2 5.10.2009 32 of 36