Security Protocols II: Syntax and Operational Semantics (Part 1)
Security Protocols II: Syntax and Operational Semantics (Part 1)
Security Protocols II: Syntax and Operational Semantics (Part 1)
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
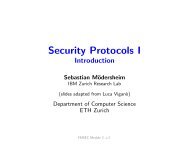
The Dolev-Yao-Style IntruderDolev-Yao ClosureDefinitionGiven a set of terms M we define DY(M) as the least closure of Munder the following rules:Axiom (m ∈ M) sm ∈ DY(M)t 1 ∈ DY(M) . . . t n ∈ DY(M)f (t 1 , . . . , t n ) ∈ DY(M)〈m 1 , m 2 〉 ∈ DY(M)m i ∈ DY(M)∈ DY(M)t ∈ DY(M)Algebra (s ≈ t)Composition (f ∈ Σ p )Proj i{|m|} k ∈ DY(M) k ∈ DY(M)m ∈ DY(M){m} k ∈ DY(M) inv(k) ∈ DY(M)DecAsymm ∈ DY(M)DecSym{m} inv(k) ∈ DY(M)OpenSigm ∈ DY(M)Decidability/complexity: in module 5.Sebastian Mödersheim FMSEC Module 3, v.2 5.10.2009 26 of 36