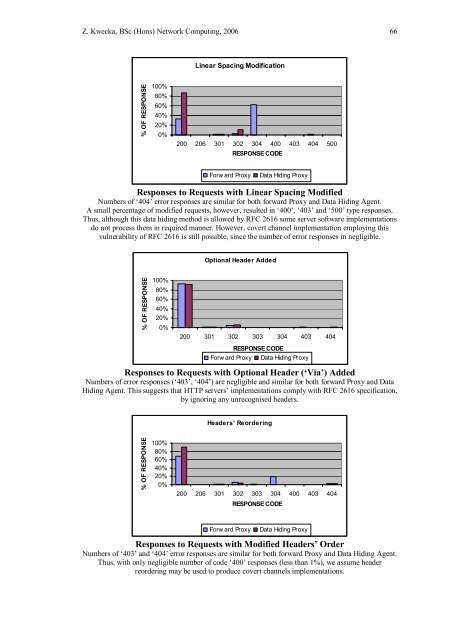
Z. Kwecka, BSc (Hons) Network Computing, 2006 66Linear Spacing Modification% OF RESPONSES100%80%60%40%20%0%200 206 301 302 304 400 403 404 500RESPONSE CODEForw ard ProxyData Hiding ProxyResponses to Requests with Linear Spacing ModifiedNumbers of ‘404’ error responses are similar for both forward Proxy <strong>and</strong> Data Hiding Agent.A small percentage of modified requests, however, resulted in ‘400’, ‘403’ <strong>and</strong> ‘500’ type responses.Thus, although this data hiding method is allowed by RFC 2616 some server software implementationsdo not process them in required manner. However, covert channel implementation employing thisvulnerability of RFC 2616 is still possible, since the number of error responses in negligible.Optional Header Added% OF RESPONSES100%80%60%40%20%0%200 301 302 303 304 403 404RESPONSE CODEForw ard Proxy Data Hiding ProxyResponses to Requests with Optional Header (‘Via’) AddedNumbers of error responses (‘403’, ‘404’) are negligible <strong>and</strong> similar for both forward Proxy <strong>and</strong> DataHiding Agent. This suggests that HTTP servers’ implementations comply with RFC 2616 specification,by ignoring any unrecognised headers.Headers' Reordering% OF RESPONSES100%80%60%40%20%0%200 206 301 302 303 304 400 403 404RESPONSE CODEForw ard ProxyData Hiding ProxyResponses to Requests with Modified Headers’ OrderNumbers of ‘403’ <strong>and</strong> ‘404’ error responses are similar for both forward Proxy <strong>and</strong> Data Hiding Agent.Thus, with only negligible number of code ‘400’ responses (less than 1%), we assume headerreordering may be used to produce covert channels implementations.
Z. Kwecka, BSc (Hons) Network Computing, 2006 67Appendix 3 - HTTP ProtocolDefinition, purpose <strong>and</strong> usageThe application layer protocol called HTTP is often perceived as very basic protocolfor distribution of World Wide Web pages. We could say that even its nameHypertext Transfer Protocol is very suggestive <strong>and</strong> implies that the purpose of thisprotocol is to transfer hypertext, where hypertext is defined as textual data “linked”across many documents or locations. It makes no wonder then, that some networkadministrators do not consider HTTP as a threat or think that as long as only outgoingestablished connections are permitted <strong>and</strong> every machine in the network uses somekind of firewall <strong>and</strong> antivirus software, they network is secure. However the true faceof the protocol is different. The most recent specification of HTTP is RFC 2616 <strong>and</strong>the purpose of the protocol is described as follows:The Hypertext Transfer Protocol (HTTP) is an application-levelprotocol for distributed, collaborative, hypermedia informationsystems. HTTP has been in use by the World-Wide Web globalinformation initiative since 1990. The first version of HTTP, referredto as HTTP/0.9, was a simple protocol for raw data transfer across theInternet. HTTP/1.0, as defined by RFC 1945, improved the protocol byallowing messages to be in the format of MIME-like messages,containing metainformation about the data transferred <strong>and</strong> modifierson the request/response semantics. (Fielding, et al, 1999, pp. 7)HTTP is now well established protocol <strong>and</strong> the current version is 1.1, however theidea of the protocol stayed the same. Through employing a simple human readable(MIME-like) syntax <strong>and</strong> allowing transfer of virtually any kind of data, HTTPbecome a preferred protocol in development of “on-line” applications. Furthermorethe fact that a large group of network administrators allowed almost any outgoingconnections of HTTP either directly or through proxies contributed strongly to thistrend. Nowadays almost any software application, which requires communicationover the Internet, employs HTTP or has a build in functionality allowing itsapplication layer protocol to be tunnelled in HTTP. Example of the first kind could beantivirus software that uses HTTP for downloading signatures of the newest threatsfrom the central server, or an update agent for an application like internet messenger.The implementations of the remote method invocation or remote procedure call are,thus, common examples of the second kind of the applications.HTTP was identified as one of three protocols, which can be employed to createcovert channels for sending data in <strong>and</strong> out of networks commonly considered to besecure. Thus the following section will identify, where RFC 2616 as the documentwhich defines the current version of HTTP in use, gives hackers an open field forhiding data.HTTP Syntax <strong>and</strong> <strong>Covert</strong> <strong>Channel</strong>sRFC 2616 was created to clear up some hard to underst<strong>and</strong> statements from theprevious documentations of HTTP (namely 1.0 <strong>and</strong> 0.9) <strong>and</strong> to introduce few optionalfeatures of HTTP/1.0 as st<strong>and</strong>ard in the new protocol HTTP/1.1. In the time when thisspecification was written the biggest concern of the creators was interoperability
- Page 1 and 2:
Application Layer Covert ChannelAna
- Page 3 and 4:
Z. Kwecka, BSc (Hons) Network Compu
- Page 5 and 6:
Z. Kwecka, BSc (Hons) Network Compu
- Page 7 and 8:
Z. Kwecka, BSc (Hons) Network Compu
- Page 9 and 10:
Z. Kwecka, BSc (Hons) Network Compu
- Page 11:
Z. Kwecka, BSc (Hons) Network Compu
- Page 14:
Z. Kwecka, BSc (Hons) Network Compu
- Page 17 and 18: Z. Kwecka, BSc (Hons) Network Compu
- Page 19 and 20: Z. Kwecka, BSc (Hons) Network Compu
- Page 21 and 22: Z. Kwecka, BSc (Hons) Network Compu
- Page 23 and 24: Z. Kwecka, BSc (Hons) Network Compu
- Page 25: Z. Kwecka, BSc (Hons) Network Compu
- Page 28 and 29: Z. Kwecka, BSc (Hons) Network Compu
- Page 30 and 31: Z. Kwecka, BSc (Hons) Network Compu
- Page 32 and 33: Z. Kwecka, BSc (Hons) Network Compu
- Page 34 and 35: Z. Kwecka, BSc (Hons) Network Compu
- Page 36 and 37: Z. Kwecka, BSc (Hons) Network Compu
- Page 38 and 39: Z. Kwecka, BSc (Hons) Network Compu
- Page 40 and 41: Z. Kwecka, BSc (Hons) Network Compu
- Page 42 and 43: Z. Kwecka, BSc (Hons) Network Compu
- Page 44 and 45: Z. Kwecka, BSc (Hons) Network Compu
- Page 46 and 47: Z. Kwecka, BSc (Hons) Network Compu
- Page 48 and 49: Z. Kwecka, BSc (Hons) Network Compu
- Page 50 and 51: Z. Kwecka, BSc (Hons) Network Compu
- Page 52 and 53: Z. Kwecka, BSc (Hons) Network Compu
- Page 54 and 55: Z. Kwecka, BSc (Hons) Network Compu
- Page 56: Z. Kwecka, BSc (Hons) Network Compu
- Page 60 and 61: Z. Kwecka, BSc (Hons) Network Compu
- Page 63 and 64: Z. Kwecka, BSc (Hons) Network Compu
- Page 65: Z. Kwecka, BSc (Hons) Network Compu
- Page 69 and 70: Z. Kwecka, BSc (Hons) Network Compu
- Page 71 and 72: Z. Kwecka, BSc (Hons) Network Compu
- Page 73 and 74: Z. Kwecka, BSc (Hons) Network Compu
- Page 75 and 76: Z. Kwecka, BSc (Hons) Network Compu
- Page 77 and 78: Z. Kwecka, BSc (Hons) Network Compu
- Page 79 and 80: Z. Kwecka, BSc (Hons) Network Compu
- Page 81 and 82: Z. Kwecka, BSc (Hons) Network Compu
- Page 83 and 84: Z. Kwecka, BSc (Hons) Network Compu
- Page 85 and 86: Z. Kwecka, BSc (Hons) Network Compu
- Page 87 and 88: Z. Kwecka, BSc (Hons) Network Compu
- Page 89 and 90: Z. Kwecka, BSc (Hons) Network Compu
- Page 91 and 92: Z. Kwecka, BSc (Hons) Network Compu
- Page 93 and 94: Z. Kwecka, BSc (Hons) Network Compu
- Page 95 and 96: Z. Kwecka, BSc (Hons) Network Compu
- Page 97 and 98: Z. Kwecka, BSc (Hons) Network Compu
- Page 99 and 100: Z. Kwecka, BSc (Hons) Network Compu
- Page 101 and 102: Z. Kwecka, BSc (Hons) Network Compu
- Page 103 and 104: Z. Kwecka, BSc (Hons) Network Compu
- Page 105 and 106: Z. Kwecka, BSc (Hons) Network Compu
- Page 107 and 108: Z. Kwecka, BSc (Hons) Network Compu
- Page 109 and 110: Z. Kwecka, BSc (Hons) Network Compu
- Page 111 and 112: Z. Kwecka, BSc (Hons) Network Compu
- Page 113: Z. Kwecka, BSc (Hons) Network Compu
- Page 116 and 117:
Z. Kwecka, BSc (Hons) Network Compu
- Page 118 and 119:
Z. Kwecka, BSc (Hons) Network Compu
- Page 120 and 121:
Z. Kwecka, BSc (Hons) Network Compu
- Page 122 and 123:
Z. Kwecka, BSc (Hons) Network Compu
- Page 124 and 125:
Z. Kwecka, BSc (Hons) Network Compu
- Page 126 and 127:
Z. Kwecka, BSc (Hons) Network Compu
- Page 128 and 129:
Z. Kwecka, BSc (Hons) Network Compu
- Page 130 and 131:
Z. Kwecka, BSc (Hons) Network Compu
- Page 132 and 133:
Z. Kwecka, BSc (Hons) Network Compu
- Page 134 and 135:
Z. Kwecka, BSc (Hons) Network Compu
- Page 136 and 137:
Z. Kwecka, BSc (Hons) Network Compu
- Page 138:
Z. Kwecka, BSc (Hons) Network Compu








![Unit 5. Switches and VLANs [PDF]](https://img.yumpu.com/34422504/1/184x260/unit-5-switches-and-vlans-pdf.jpg?quality=85)






