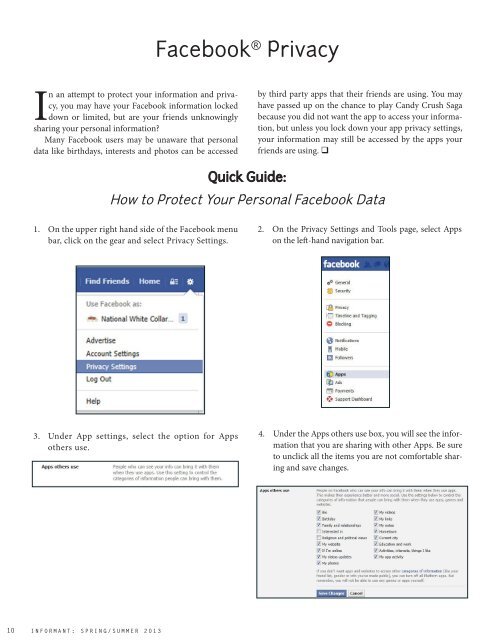
Facebook ® PrivacyIn an attempt to protect your information and privacy,you may have your Facebook information lockeddown or limited, but are your friends unknowinglysharing your personal information?Many Facebook users may be unaware that personaldata like birthdays, interests and photos can be accessedby third party apps that their friends are using. You mayhave passed up on the chance to play Candy Crush Sagabecause you did not want the app to access your information,but unless you lock down your app privacy settings,your information may still be accessed by the apps yourfriends are using. Quick Guide:How to Protect Your Personal Facebook Data1. On the upper right hand side of the Facebook menubar, click on the gear and select Privacy Settings.2. On the Privacy Settings and Tools page, select Appson the left-hand navigation bar.3. Under App settings, select the option for Appsothers use.4. Under the Apps others use box, you will see the informationthat you are sharing with other Apps. Be sureto unclick all the items you are not comfortable sharingand save changes.<strong>10</strong>INFORMANT: SPRING/SUMMER <strong>2013</strong>
Sneak PeakGaming System ResearchBy Elizabeth SingerThe days of simply playing QBert on Atari® are gone.Today’s gaming systems allow users to do muchmore than chomp through a maze. The top gamingsystems, Xbox®, Wii® and Playstation®, continue to evolveto enhance the gaming experience while integrating interactivecapabilities.These systems have memory capacity to store games,images and videos, while also connecting to the Internet.The Wii, for example, allows the user to download appsthat bring them to YouTube®, Netflix® and other websiteswith ease. Handheld gaming devices also offer WiFi connectivity.NW3C computer forensiccourses teach investigatorsabout wheredigital evidence may bestored on various gamingdevices. An Internet<strong>Crime</strong>s Against ChildrenTask Force may investigatea suspected childpornographer, and uponsearching the house failto find a computer. However,the suspect has agaming device, whichcould hold important informationrelated to the case.These systems also helped create a sub-culture of “secondlife” gamers. Multi-player, online games allow theplayers to enter a fantasy realm, where they can becomeogres, super heroes or other imaginary people. While inthese games, the players take on the personas of theircharacters and easily interact with others from aroundthe world.This gaming world is vast, and many take their secondlife personas very seriously. They spend hours on queststo gather riches or swords endowed with powers that holdvalue to the players. Even in a virtual world, crime exists.Reports of these objects stolen from gamers have emerged,and court systems in other countries have even looked athow to handle this type of crime.Police departments in the U.S. cannot investigate thetheft of a virtual sword, but online gaming is also a popularactivity for real-world criminals like hackers and gangmembers. It provides a place to meet to discuss activitiesand share information.Because these systems can hold essential digital evidence,NW3C computer crime specialists are tearingapart various gaming systems for a better understandingof how data can be retrieved. This team of specialists hasXbox 360®’s, PS3®’s, PSVita®’s, Wii®’s and Nintendo 3DS®’s.In a controlled environment they use testers to “play”with the devices andsearch the Internet tocreate a trail of evidence.Once this phase is complete,the specialistswork with the systems tosee if they can extract thedata for forensic analysis.The initial testingshowed that data fromthe two Sony® productsis encrypted, which maymake it unviewable. TheWii has flash memorywhich means that screencaptures may be necessaryto view information. The 3DS has a memory cardthat stores data in an easy-to-read format. It may also beeasy-to-extract data from the Xbox360, but with the needto sign into Xbox servers (where most of the informationis stored, i.e. chat messages, friends list, etc.), the data maybe limited.These findings are preliminary and offer just a snapshotof the beginning of this research. The next step willinclude a meeting with law enforcement subject matterexperts who will provide their ideas, expertise and experiencewith these systems. The Bureau of Justice Assistanceis supporting this research and, once completed,the specialists will produce a white paper outlining theirfindings. This white paper will be featured on the NW3Cwebsite as a resource for investigators. WWW.NW3C.ORG 11