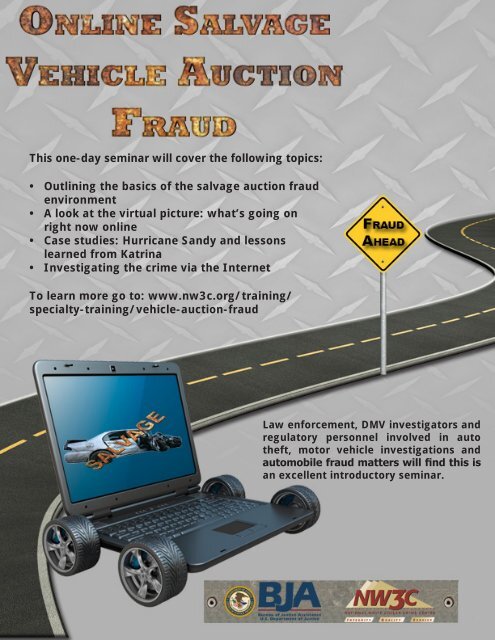
(4))lupea XCV.M , SCTIONMMY D.This one-day seminar will cover the following topics:• Outlining the basics of the salvage auction fraudenvironment• A look at the virtual picture: what’s going onright now online• Case studies: Hurricane Sandy and lessonslearned from Katrina• Investigating the crime via the InternetFRAuoAHEADTo learn more go to: www.nw3c.org/training/specialty-training/vehicle-auction-fraudt .Law enforcement, DMV investigators andregulatory personnel involved in autotheft, motor vehicle investigations andautomobile fraud matters will find this isan excellent introductory seminar.A new C.. .. ..n.. w.... nra4 tr:nunG rir-i2INFORMANT: SPRING/SUMMER <strong>2013</strong>
Table of Contents<strong>Informant</strong> <strong>Spring</strong>/Summer <strong>2013</strong>4 Preventing Online FraudExecutive StaffDon Brackman, DirectorKen Brooks, Deputy DirectorDave Cummings, Deputy DirectorMark Gage, Deputy DirectorMary-Ellen Kendall, General CounselEditorial StaffKim Williams, Communications ManagerElizabeth Singer, Senior Writer and EditorTy Bowers, Print and MultimediaContent CoordinatorLindsey Bousfield, Graphic DesignerContact UsInternet: www.nw3c.orgMember Services: 804-967-62<strong>10</strong>membership@nw3c.orgInvestigative Support: 800-221-4424,ext. 3520Training: 877-628-7674, ext. 2234IC3: www.ic3.gov5 Identifying Electronic Evidence: USB/Flash Drives6 Superstorm Sandy Disaster Fraud Task Force8 Virtual Patrol: Global ‘Tweet-a-thon’ Uses Twitter ® to Pull BackCurtain on Day-t0-Day Police Work<strong>10</strong> Facebook Privacy11 Sneak Peak: Gaming System Research12 Tracking Down Stolen Phones: Law Enforcement, Industry andFCC Work to Curb the Black Market in Stolen Wireless Devices13 Social Media Best Practices: Los Angeles County Sheriff’sDepartment Using Social Media to Prevent <strong>Crime</strong>14 The Salvage Automobile and the <strong>White</strong> <strong>Collar</strong> <strong>Crime</strong> Connection17 Teen Uses Malware to Hack Phones and Obtain ExplicitImages of Children18 Cybercrime Trends: Child Predators Using “Sextortion”19 Cell Phone Thefts Lead to Sextortion<strong>National</strong><strong>White</strong><strong>Collar</strong><strong>Crime</strong>Center@NW3CNewsThis project was supported by Grant <strong>No</strong>. 2011-BE-BX-K002 awarded by the Bureau of Justice Assistance. The Bureau of Justice Assistance is a component of the Office of Justice Programs,which also includes the Bureau of Justice Statistics, the <strong>National</strong> Institute of Justice, the Office of Juvenile Justice and Delinquency Prevention, the Office for Victims of <strong>Crime</strong>, and the Office ofSex Offender Sentencing, Monitoring, Apprehending, Registering, and Tracking. Points of view or opinions in this document are those of the author and do not necessarily represent the officialposition or policies of the U.S. Department of Justice. The <strong>National</strong> <strong>White</strong> <strong>Collar</strong> <strong>Crime</strong> Center (NW3C) is the copyright owner of this document. This information may not be used or reproducedin any form without express written permission of NW3C. For questions or additional information, please contact Kimberly Williams, Communications Manager at 1-800-221-4424 ext. 3320or kwilliams@nw3c.org. NW3C TM and IC3 ® are trademarks of NW3C, Inc. and may not be used without written permission.©<strong>2013</strong>. NW3C, Inc. d/b/a the <strong>National</strong> <strong>White</strong> <strong>Collar</strong> <strong>Crime</strong> Center. All rights reserved. Bureau of Justice AssistanceU.S. Department of JusticeWWW.NW3C.ORG 3