RiskUKApril2018
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
April 2018<br />
www.risk-uk.com<br />
Security and Fire Management<br />
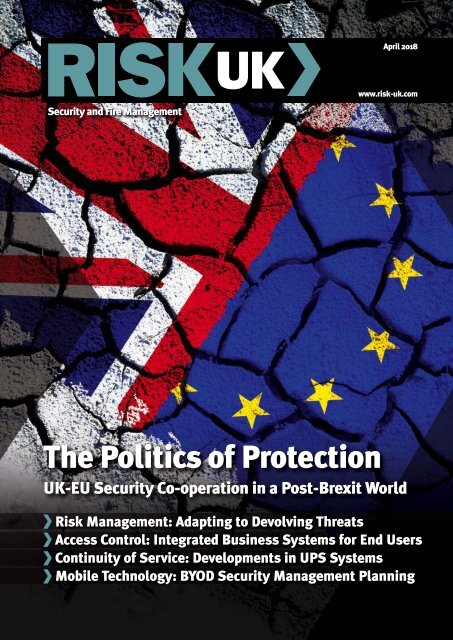
The Politics of Protection<br />
UK-EU Security Co-operation in a Post-Brexit World<br />
Risk Management: Adapting to Devolving Threats<br />
Access Control: Integrated Business Systems for End Users<br />
Continuity of Service: Developments in UPS Systems<br />
Mobile Technology: BYOD Security Management Planning
April 2018<br />
Contents<br />
32 The Voice of Reason<br />
Malcolm Crummey explains why it’s time to take audio solutions<br />
every bit as seriously as the provision of CCTV surveillance<br />
Training and Career Development (pp48-49)<br />
5 Editorial Comment<br />
6 News Update<br />
National Crime Agency Annual Plan 2018-2019. National Security<br />
Capability Review. New Counter-Terrorism Hub for London<br />
8 News Analysis: UK-EU Security Co-operation<br />
The latest Home Affairs Committee report warns of “serious<br />
legal, constitutional and political obstacles” in the way of<br />
achieving close policing and security co-operation post-Brexit<br />
11 News Special: AML Regime Review<br />
With the support of EY, the Lloyds Banking Group and Thomson<br />
Reuters, RUSI is set to conduct a detailed review of the current<br />
anti-money laundering regime. Risk UK delves into the detail<br />
13 Opinion: Access Control and the Equality Act<br />
John Davies examines the importance of effective access control<br />
in making the lives of the less able-bodied that bit easier<br />
16 Opinion: Mind Your Own Business<br />
Daniel Hardy assesses the scale of violence in the workplace<br />
specifically in the retail sector, the reasons behind its growth<br />
and what needs to be done to keep employees safe<br />
19 Adapting to Devolving Threats<br />
Upticks in terrorism and violent crime have occurred in recent<br />
times. Philip Strand and Christine Annerfalk look for a solution<br />
34 Meet The Security Company<br />
In association with the NSI, Risk UK continues its ‘Meet The<br />
Security Company’ series by asking Westgrove Group’s brand<br />
and development director Laurie Barton Wright some questions<br />
37 The Security Institute’s View<br />
Dr Chaditsa Poulatova and Hannah Saunders investigate how<br />
well the Prevent duty is playing out in the education sector<br />
40 In The Spotlight: ASIS International UK Chapter<br />
Nerve Agents and Novichoks... Dan Kaszeta evaluates the impact<br />
of the recent Salisbury attack on Sergei Skripal and his daughter<br />
42 FIA Technical Briefing<br />
The Fire Industry Manufacturers Expo is coming to Ashton Gate<br />
Stadium in Bristol. Ian Moore previews what’s in store<br />
44 Security Services: Best Practice Casebook<br />
As Amanda McCloskey details, investment in security staff<br />
confidence and motivation drivers reaps multiple benefits<br />
46 Mobile Technology: Bring Your Own Device<br />
Jocelyn Krystlik offers some thought-provoking views on Bring<br />
Your Own Device security regimes for today’s organisations<br />
48 Training and Career Development<br />
Charlie Swanson on security training in the retail environment<br />
50 Risk in Action<br />
51 Technology in Focus<br />
53 Appointments<br />
22 Securing Critical Assets<br />
Pip Courcoux discusses integrated access control and the<br />
importance of planned protection regimes for physical assets<br />
24 The Risk Management Journey<br />
Steve Schlarman observes the specific stages involved in<br />
building an integrated risk management programme<br />
27 Fault Intolerance<br />
Risk UK interviews Leo Craig about future developments in the<br />
realm of Uninterruptible Power Supply systems<br />
30 Time for Transformation<br />
Danny Williams tracks the move away from traditional security<br />
guarding towards the delivery of a new style of service<br />
56 The Risk UK Directory<br />
ISSN 1740-3480<br />
Risk UK is published monthly by Pro-Activ Publications<br />
Ltd and specifically aimed at security and risk<br />
management, loss prevention, business continuity and<br />
fire safety professionals operating within the UK’s largest<br />
commercial organisations<br />
© Pro-Activ Publications Ltd 2018<br />
All rights reserved. No part of this publication may be<br />
reproduced or transmitted in any form or by any means<br />
electronic or mechanical (including photocopying, recording<br />
or any information storage and retrieval system) without the<br />
prior written permission of the publisher<br />
The views expressed in Risk UK are not necessarily those of<br />
the publisher<br />
Risk UK is currently available for an annual subscription rate of<br />
£78.00 (UK only)<br />
www.risk-uk.com<br />
Risk UK<br />
PO Box 332<br />
Dartford DA1 9FF<br />
Editor Brian Sims BA (Hons) Hon FSyI<br />
Tel: 0208 295 8304 Mob: 07500 606013<br />
e-mail: brian.sims@risk-uk.com<br />
Design and Production Matt Jarvis<br />
Tel: 0208 295 8310 Fax: 0870 429 2015<br />
e-mail: matt.jarvis@proactivpubs.co.uk<br />
Advertisement Director Paul Amura<br />
Tel: 0208 295 8307 Fax: 01322 292295<br />
e-mail: paul.amura@proactivpubs.co.uk<br />
Administration Tracey Beale<br />
Tel: 0208 295 8306 Fax: 01322 292295<br />
e-mail: tracey.beale@proactivpubs.co.uk<br />
Managing Director Mark Quittenton<br />
Chairman Larry O’Leary<br />
Editorial: 0208 295 8304<br />
Advertising: 0208 295 8307<br />
3<br />
www.risk-uk.com
Add more to your security system<br />
Interact, control and integrate your Texecom security system like never before<br />
<br />
<br />
<br />
www.texe.com<br />
Sales: +44 (0)1706 212524
Editorial Comment<br />
Violent Times<br />
The British Retail Consortium’s (BRC) detailed annual Retail<br />
Crime Survey for 2017 reveals a concerning spike in violence<br />
against shop staff causing injury, with the number of<br />
incidents occurring at twice the rate of the prior survey (which, in<br />
point of fact, held the previous record).<br />
BRC members report that career criminals intentionally use<br />
violence and abuse when challenged over stealing. The<br />
increasingly common requirement for retail colleagues to agecheck<br />
and refuse sales is also triggering an uptick in violence<br />
and threat episodes.<br />
Overall, this year’s survey presents a mixed picture. There have<br />
been noticeable improvements in some areas, such as fraud,<br />
where the cost to retailers has fallen by nearly £30 million as a<br />
result of their significant investment in prevention. Despite that<br />
spending, though, the total direct financial cost of retail crime<br />
has climbed. That represents an increase of 6% from the<br />
previous year. ‘Customer theft’ remains the largest element. This<br />
now weighs in at over half a billion pounds per annum. That’s a<br />
15% increase on the previous results.<br />
The BRC’s Retail Crime Survey covers the period from 1 April<br />
2016 to 31 March last year and encompasses the experiences of<br />
1.1 million employees (accounting for approximately one third of<br />
the retail industry). The total direct cost of retail crime has risen<br />
to just over £700 million. The rate of reported violence with<br />
injury has doubled in a year to six episodes per 1,000 workers. At<br />
that rate, across all roles in retail, an average of 13 individuals<br />
were injured each day of the 12-month period under survey.<br />
The direct cost of customer theft has burgeoned by £65 million<br />
(or nearly 15%), while the direct cost of fraud has reduced by<br />
£27 million (or just under 15%).<br />
On average, retailers spent around the same amount of money<br />
on (non-cyber) crime prevention in 12 weeks as they did in the<br />
whole of the previous year. Nearly half of respondents to the<br />
study have witnessed an increase in the number of cyber attacks<br />
over the last year.<br />
Commenting on the startling findings, Helen Dickinson OBE<br />
(CEO of the BRC) stated: “Retail directly employs nearly one in<br />
every ten workers in the UK, as well as millions more indirectly.<br />
The sector already faces its own challenges, with margins<br />
shrinking. Set against this backdrop, the pressures that retail<br />
crime exerts are having a stronger impact.”<br />
Dickinson went on to observe: “The figures on violence<br />
against staff in particular present a deeply concerning picture.<br />
Attacks on retail workers are intolerable. Retailers are doing<br />
everything possible to ensure that their members of staff and<br />
customers alike are safe and protected, but they’re now having<br />
to spend record amounts on crime prevention in order to do so.<br />
This is a drag on the economic viability of retail outlets and not<br />
infinitely sustainable. It’s clear that a new approach is required.”<br />
Importantly, the BRC is working to build a new model for cooperation<br />
around tackling retail crime and encouraging decisionmakers<br />
throughout the country to apply the priority level the key<br />
issues deserve. This is absolutely the right course of action.<br />
Brian Sims BA (Hons) Hon FSyI<br />
Editor<br />
December 2012<br />
5<br />
www.risk-uk.com
Annual Plan 2018-2019 issued by National<br />
Crime Agency to “deliver step change”<br />
The National Crime Agency (NCA) has published<br />
its Annual Plan for 2018-2019, setting out what<br />
the organisation will do over the coming year to<br />
make itself “leaner and more efficient” and<br />
“deliver a step change” to the way in which it<br />
works with law enforcement and intelligence<br />
partners to fight serious and organised crime.<br />
In the Home Secretary’s foreword to the 19-<br />
page document, Amber Rudd praises the NCA’s<br />
performance, stating that the organisation has<br />
“gone from strength to strength with an<br />
impressive and sustained track record of<br />
disruptions across the full range of serious and<br />
organised crime threats.”<br />
NCA director general Lynne Owens echoes<br />
these sentiments in her own statement,<br />
highlighting that the NCA has delivered “some<br />
outstanding results since its inception”. Owens<br />
added: “We’re not complacent. There’s more to<br />
be done in order to protect the public from the<br />
effects of serious and organised crime, which<br />
continues to grow in complexity and challenge.”<br />
Owens concluded: “Tackling the breadth of<br />
serious and organised crime is beyond the<br />
capacity and capabilities of any one body. It’s<br />
clear that agencies can no longer act in<br />
isolation to protect members of the public, and<br />
nor can any one agency hold all the tools<br />
required for a comprehensive response. This<br />
Annual Plan sets out how we will play our part<br />
in leading that response.”<br />
The NCA’s Annual Plan, which follows on from<br />
the Government’s National Security Capability<br />
Review, is ambitious in its scope, detailing the<br />
concrete steps that the organisation will take<br />
towards transformation over the coming period.<br />
Steps to take in 2018-2019<br />
In 2018-2019, the organisation will:<br />
*Build critical capability through the creation of<br />
the National Assessment Centre, the National<br />
Data Exploitation Capability and the National<br />
Economic Crime Centre<br />
*Continue to demonstrate its leadership role in<br />
tackling serious and organised crime by<br />
embedding a consistent approach towards<br />
threat leadership, including prioritisation and<br />
tasking, in order to become threat agnostic and<br />
intelligence-led in all of its investigations<br />
*Deliver specialist and unique services<br />
designed to support its own operations as well<br />
as those of its partners<br />
*Work with partner organisations to continually<br />
build an evidence base for sustainable funding<br />
*Implement the recommendations of its<br />
international review, ensuring that activity to<br />
tackle serious and organised crime upstream is<br />
driven by agreed national priorities<br />
*Introduce a new streamlined structure that will<br />
also make the NCA a more efficient, agile and<br />
flexible organisation. Savings will be reinvested<br />
to increase the number of frontline officers<br />
“Halfway house” National Security Capability Review “a cause for concern”<br />
The importance of a robust and coherent process in setting the National Security Strategy (NSS)<br />
has been underlined by the Joint Committee on the National Security Strategy (JCNSS) with the<br />
publication of its first report on the National Security Capability Review (NSCR).<br />
Last year, the Government launched the NSCR as a ‘quick refresh’ of national security capabilities<br />
in the light of changing security challenges. The NSCR is still underway, but the Joint Committee’s<br />
report offers preliminary comments on the process and key issues that the review process should<br />
address. The election of the Trump administration in the US, the UK’s decision to leave the EU,<br />
intensifying threats to the UK’s national security and a significant structural hole in the defence<br />
budget have all presented real reasons to revisit the 2015 NSS and Strategic Defence and Security<br />
Review before the next expected review process is conducted during 2020.<br />
However, according to the JCNSS, the decision to focus on capabilities, and not the underlying<br />
strategy, “doesn’t do justice” to the changes to the wider security environment. The announcement<br />
in January of the Modernising Defence Programme puts work on defence on a different basis and<br />
timeline from the rest of the NSCR.<br />
The Joint Committee has stated: “It appears that the NSCR has inadvertently become an<br />
uncomfortable ‘halfway house’ between a ‘quick refresh’ of national security capabilities and a full<br />
review. An honest conversation on defence spending is required if the Government is to match its<br />
ambitions for national security with the realities of the UK’s capabilities and funding. The nation’s<br />
security capabilities are far too important to be allowed to evolve without proper thought or<br />
direction from ministers.”<br />
6<br />
www.risk-uk.com
News Update<br />
Mayor of London confirms<br />
£412 million investment in all-new<br />
counter-terrorism hub<br />
Sadiq Khan, the Mayor of London, and the<br />
Metropolitan Police Service have unveiled the<br />
detail behind a £412 million investment<br />
initiated to create a new counter-terrorism and<br />
organised crime hub in the capital. The major<br />
new investment includes the £250 million<br />
purchase of the Empress State Building in<br />
Hammersmith and Fulham and a “significant<br />
upgrade project” to make the building and its<br />
associated sites secure and fit for purpose.<br />
These plans will bring together for the very<br />
first time under one roof the Metropolitan<br />
Police Service’s Counter-Terrorism Command<br />
and Specialist Crime and Operations in line<br />
with other cities like Manchester and<br />
Birmingham. The move to focus on a single<br />
site, and dispose of other buildings, will also<br />
save on rent, freeing up more money to<br />
support front line policing.<br />
According to a statement issued by the<br />
Mayor’s Office for Policing and Crime, London’s<br />
new counter-terrorism hub will serve to<br />
“streamline operations and capabilities” and<br />
“ensure more effective and efficient working”<br />
in order to keep the capital as safe as possible<br />
from the now constant and ever-evolving<br />
threat of terrorism.<br />
The current threat from international<br />
terrorism in the UK remains at ‘Severe’, which<br />
means an attack is highly likely. The increase<br />
in terrorist activity has been described by<br />
police and security experts as “a shift, not a<br />
spike”. The horrific events that took place in<br />
London and Manchester last year remind us all<br />
that attacks can happen at any time and<br />
without warning.<br />
Until now, a significant proportion of the<br />
Empress State Building has been leased by<br />
the Metropolitan Police Service and used for a<br />
range of purposes including back office and<br />
operational functions. In addition to the<br />
benefits for London’s counter-terror provision,<br />
the purchase of the freehold offers better<br />
value for money than the alternative options<br />
(that include signing another 15-year lease).<br />
Sadiq Khan explained: “Keeping Londoners<br />
safe is my first priority. This means ensuring<br />
that the capital is as protected as possible<br />
from the threat of terrorism and organised<br />
crime. Last year, our city was subjected to four<br />
terrorist attacks. We know that countless more<br />
planned attacks have been thwarted by our<br />
hard-working and dedicated counter-terrorism<br />
officers whose heroism in these times of<br />
adversity we must never take for granted. At a<br />
time when policing budgets continue to be cut<br />
by Government, it’s right for us to prioritise<br />
investment in those areas that matter most.”<br />
Carillion collapse should act as<br />
“wake-up call” for effective risk<br />
management approaches<br />
Public sector officials and the heads of major<br />
corporations must use the collapse of Carillion<br />
as a “wake-up call” and recognise the value of<br />
an effective risk management approach.<br />
Speaking at the recent launch event for the<br />
2018 EURisk Convention, Dr Calie Pistorious<br />
(CEO of technological consultancy firm<br />
DeltaHedron) and international negotiation<br />
trainer Bob Spence implored senior<br />
management figures to recognise the<br />
importance of effective risk management.<br />
Carillion plc is a British multinational FM<br />
and construction services company<br />
headquartered in Wolverhampton. The<br />
business experienced financial difficulties in<br />
2017, and went into compulsory liquidation on<br />
15 January this year, which is the most drastic<br />
procedure in UK insolvency law.<br />
Before its recent liquidation event, Carillion<br />
was the second largest construction company<br />
in the UK, listed on the London Stock<br />
Exchange and an employer of some 43,000<br />
members of staff (around 20,000 of them here<br />
in the UK).<br />
On home shores, the insolvency has caused<br />
project shutdowns, job losses (in Carillion –<br />
1,536 UK redundancies up to 12 March 2018 –<br />
and its suppliers), losses to joint venture<br />
partners and lenders and potential financial<br />
losses to Carillion’s 30,000 suppliers and<br />
28,500 pensioners.<br />
It has led to questions and Parliamentary<br />
enquiries about the conduct of the firm’s<br />
directors and auditors, and about the UK<br />
Government’s relationships with major<br />
suppliers working on PFI schemes and other<br />
privatised provisions of public services.<br />
PFI projects in Ireland have been<br />
suspended, while four of Carillion’s Canadian<br />
businesses have moved to seek legal<br />
bankruptcy protection.<br />
“A lot of companies look at risk as a boxticking<br />
exercise, but that’s a waste of time,”<br />
said Dr Pistorious. “It’s a change of mindset<br />
that’s needed in order to understand the<br />
business value of having an effective risk<br />
approach. The struggles of companies like<br />
Carillion are to do with risk multiplied by<br />
company culture. If those two things work<br />
together then it can be an extremely powerful<br />
force for good. If they’re out of sync, though,<br />
then it’s a nightmare scenario.”<br />
7<br />
www.risk-uk.com
Brexit negotiations “must focus on security<br />
co-operation” urges Home Affairs Committee<br />
A report published by<br />
the Home Affairs<br />
Committee in<br />
Parliament warns of<br />
“serious legal,<br />
constitutional and<br />
political obstacles” in<br />
the way of achieving<br />
continued close<br />
policing and security<br />
co-operation post-<br />
Brexit. Entitled ‘UK-EU<br />
Security Co-operation<br />
After Brexit’, the<br />
document cautions<br />
that these issues need<br />
to be resolved “as a<br />
matter of urgency” or<br />
the UK’s future<br />
policing and security<br />
capabilities risk being<br />
“seriously<br />
undermined”. Brian<br />
Sims analyses the<br />
main talking points<br />
The detailed report welcomes the<br />
Conservative Government’s objectives for a<br />
Security Treaty designed to replicate<br />
current co-operation on Europol, the European<br />
Arrest Warrant and data sharing on criminality,<br />
but at the same time criticises the Conservative<br />
administration for “complacency over the<br />
timetable” and warns about the complexity of<br />
the negotiations.<br />
The Home Affairs Committee is pushing for<br />
security and policing negotiations to begin<br />
immediately, and also calls upon the<br />
Government and the European Commission to<br />
show flexibility. The Committee argues that the<br />
EU should not try to restrict co-operation to<br />
existing third country models, and that the UK<br />
should not be rigid about artificial red lines.<br />
Further, the Committee argues that both<br />
parties should be ready to extend the transition<br />
period, as it’s highly likely to take longer than<br />
two years to resolve new legal arrangements<br />
for extradition and data sharing.<br />
In addition, the Committee warns that the<br />
Government “risks sleepwalking into a crisis”<br />
by appearing to assume that the shared UK-EU<br />
interest in security co-operation will lead to the<br />
swift and easy agreement of complex legal and<br />
constitutional problems.<br />
Yvette Cooper MP, chair of the Home Affairs<br />
Committee. commented: “Given the scale of<br />
cross-border crime, trafficking and terrorism<br />
threats, we need security and policing cooperation<br />
now more than ever, but there’s a<br />
serious risk that we will lose some of the vital<br />
data and extradition arrangements if there isn’t<br />
urgent work conducted by both the UK and the<br />
EU to deal with the trickiest issues.”<br />
Cooper continued: “We agree with the<br />
Government that the European Arrest Warrant,<br />
Europol capabilities and database access<br />
should be replicated in full, and that this is in<br />
Europe’s interests, too, but just because we all<br />
want something, it doesn’t mean that it will<br />
happen unless enough work is put in ahead of<br />
time to overcome the legal, constitutional and<br />
political obstacles we’ve uncovered.”<br />
Embellishing this theme, Cooper went on to<br />
state: “We’re extremely concerned that neither<br />
the Government nor the European Commission<br />
is focusing enough attention on this area of<br />
Brexit in order to sort these problems out in<br />
time. Yet the consequences of running out of<br />
transition time before the Security Treaty is in<br />
place are immensely serious, both for the UK<br />
and Europe. Losing or weakening extradition<br />
arrangements could mean being unable to<br />
extradite rapists like Zdenko Turtak, who fled<br />
back to Slovakia but, using the European Arrest<br />
Warrant, was returned to face a long prison<br />
sentence. Losing or weakening data access<br />
could prevent the police service from gaining<br />
the vital information they need to catch<br />
dangerous criminals or keep victims safe.”<br />
Easing the red line<br />
Cooper asserted that Prime Minister Theresa<br />
May appears to have eased the Court of Justice<br />
of the European Union’s (CJEU) red line when it<br />
comes to security co-operation. “That’s<br />
welcome and essential if we’re to be able to<br />
replicate current co-operation after Brexit,”<br />
outlined Cooper, “but other tricky problems<br />
remain unresolved. We need much more detail<br />
and flexibility from both the Government and<br />
the European Commission.”<br />
According to Cooper and her colleagues on<br />
the Home Affairs Committee, much more<br />
urgency needs to be given to this whole area.<br />
“Otherwise, we risk sleepwalking into a crisis.<br />
That’s why the Committee is ringing the alarm<br />
bell before it’s too late. Policing co-operation,<br />
extradition arrangements and data sharing are<br />
too important to either lose or diminish. The<br />
costs of failure are unthinkable.”<br />
The Home Affairs Committee concludes that<br />
the UK should seek to maintain its security<br />
capabilities in full after Brexit – including<br />
8<br />
www.risk-uk.com
News Analysis: UK-EU Security Co-operation Post-Brexit<br />
Europol membership, replicating the provisions<br />
of the European Arrest Warrant and retaining<br />
full access to EU data sharing mechanisms –<br />
and that the Government is right to aim to<br />
secure those in a Security Treaty separate from<br />
the other negotiations.<br />
The Committee asserts that the Government<br />
should be honest about the complex technical<br />
and legal obstacles to achieving such a close<br />
degree of co-operation as a third country. As far<br />
as the Home Affairs Committee’s concerned, it’s<br />
crucial that the negotiations in this area begin<br />
imminently. The Government and the EU must<br />
be ready to extend the transition period for<br />
security arrangements beyond the proposed<br />
end date of December 2020.<br />
Cross-border crime<br />
With the growing prevalence of cross-border<br />
crime, there can be no substitute for UK access<br />
to Europol’s capabilities and services.<br />
Maintaining this access should be a key priority<br />
in the Brexit negotiations.<br />
Current EU proposals for the UK to lose its<br />
role on the Europol Board during the transition<br />
period are a real concern. Disrupting Europol’s<br />
governance arrangements next March, in<br />
advance of a wider negotiation for the new<br />
relationship, would not benefit anyone’s<br />
security or safety.<br />
The UK and the EU should work to negotiate<br />
a bespoke relationship. Existing Europol<br />
models for co-operation with non-EU countries<br />
would involve a reduction of security<br />
capabilities. The Prime Minister’s willingness to<br />
accept the CJEU is “welcome and essential”<br />
towards securing the closest partnership.<br />
The efficiency and effectiveness of the<br />
European Arrest Warrant is “beyond doubt”.<br />
Being forced to fall back on the 1957 European<br />
Convention on Extradition after Brexit would be<br />
a “catastrophic outcome”.<br />
Establishing a new extradition agreement is<br />
vital, but that process faces serious legal and<br />
constitutional obstacles. For example, Germany<br />
and Slovakia currently have constitutional bars<br />
against extraditing their own citizens to a non-<br />
EU country. That would have shielded Zdenko<br />
Turtak from extradition from Slovakia to face<br />
trial and imprisonment for a violent rape that<br />
occurred in Leeds two years ago.<br />
Data gathering and sharing<br />
The Home Affairs Committee agrees with the<br />
Government that the sharing of criminal data,<br />
including full access to the Second Generation<br />
Schengen Information System (SIS II) and other<br />
EU databases, must continue after the Brexit<br />
process has reached its conclusion.<br />
“Policing co-operation, extradition arrangements and data<br />
sharing are too important to either lose or diminish. The<br />
costs of failure are unthinkable”<br />
However, the Committee is concerned that<br />
there are likely to be significant judicial and<br />
legal obstacles and delays to securing a data<br />
adequacy agreement and reaching the data<br />
protection standards needed to maintain<br />
access to those databases. This could include<br />
increased examination by the EU of the UK’s<br />
surveillance and interception regime as we will<br />
no longer benefit from the national security<br />
exemption for Member States.<br />
The Government could also encounter<br />
problems because of its decision not to<br />
incorporate Article 8 of the EU Charter of<br />
Fundamental Rights into UK law to exempt<br />
immigration cases from the Data Protection Bill.<br />
In summary, then, the Home Affairs<br />
Committee is concerned that the Government is<br />
“worryingly complacent” about the UK’s future<br />
access to EU data.<br />
Given the uncertain prospects for a<br />
comprehensive deal on law enforcement cooperation,<br />
there’s no alternative to contingency<br />
planning for the loss of some or all EU security<br />
measures. The Home Affairs Committee feels<br />
that the Government should dedicate a<br />
substantial proportion of the £3 billion Brexit<br />
planning fund to policing and security cooperation,<br />
including publishing detailed impact<br />
assessments of different scenarios, along with<br />
fully-costed contingency arrangement plans.<br />
Pragmatism on both sides<br />
The Home Affairs Committee argues that<br />
success in this area of Brexit will require<br />
pragmatism on both sides. The EU should not<br />
be so inflexible that it confines co-operation to<br />
existing models, but the UK should not be rigid<br />
about its own red lines, including the future<br />
jurisdiction of the CJEU.<br />
The Committee agrees with Home Secretary<br />
Amber Rudd that a ‘no deal’ outcome in the<br />
sphere of security should be unthinkable, but<br />
isn’t convinced that the Government has a clear<br />
strategy to prevent the unthinkable from<br />
becoming a reality. Indeed, the Committee has<br />
moved to express “serious concerns” about the<br />
apparent lack of investment and interest in<br />
contingency planning in this area.<br />
The detailed Home Affairs Committee report<br />
concludes by stating that it’s time for the<br />
Conservative Government to flesh out the<br />
details of the ‘bespoke deal’ it says it hopes to<br />
secure in this area.<br />
Yvette Cooper: Chair of the<br />
Home Affairs Select Committee<br />
in Parliament<br />
Prime Minister Theresa May<br />
9<br />
www.risk-uk.com
TCP/IP<br />
network<br />
PAVIRO<br />
Public Address and Voice Evacuation System<br />
with Professional Sound Quality<br />
Flexibility from the start<br />
PAVIRO offers you smart features making system specification and installation faster, simpler<br />
and more efficient than ever before. Design a complete system with just a few parameters. Avoid<br />
unexpected costs thanks to the system’s extreme flexibility and low operational costs. What‘s<br />
more? The new Dante network interface module ensures IP networking functionality allowing<br />
larger areas with more audio channels with up to four decentralized controllers.<br />
Find out more at boschsecurity.com
News Special: Anti-Money Laundering Regime Review<br />
EY, Lloyds Banking Group and Thomson<br />
Reuters support RUSI review of AML regime<br />
Money laundering threats and<br />
vulnerabilities have radically changed<br />
since the fundamental architecture of<br />
the international AML regime was designed<br />
back in the 1990s. Technological developments<br />
have enabled criminals to become increasingly<br />
sophisticated and evade traditional methods of<br />
detection. The range of available responses has<br />
also evolved. By allowing financial institutions<br />
and supervisors to harness larger amounts of<br />
data, advanced analytics have the potential to<br />
really increase the impact of AML efforts across<br />
sectors and within individual organisations.<br />
Over the next two years, the Financial Crime<br />
2.0 programme will determine how the AML<br />
regime could be updated in order to be more<br />
effective and reflect today’s technological<br />
landscape. The research will be carried out by<br />
RUSI, supported by partners from EY, the<br />
Lloyds Banking Group and Thomson Reuters.<br />
The programme recognises that better<br />
information sharing has enhanced the<br />
effectiveness of AML in recent years. Beyond<br />
these initiatives, however, wider changes are<br />
required in order to allow stakeholders to make<br />
the most effective use of this information and<br />
respond to new challenges.<br />
To inform this discussion, the programme will<br />
combine two concurrent initiatives. The first<br />
initiative is policy-focused and will identify how<br />
core elements of the AML regime could be<br />
improved to create an enabling environment for<br />
the use of technology. In a report to be<br />
published at the end of 2018, it will establish<br />
what reporting requirements provide the most<br />
effective and proportionate basis for the use of<br />
advanced analytics by AML supervisors.<br />
By mid-2019, it will also assess to what<br />
extent the current compliance framework<br />
supports the effective prevention of money<br />
laundering in the private sector. This research<br />
will be informed by the growing role of Artificial<br />
Intelligence and also by developments in data<br />
protection, particularly the European Union’s<br />
General Data Protection Regulation.<br />
The second initiative focuses on the effective<br />
mitigation of new money laundering risks that<br />
are not fully addressed by the existing AML<br />
regime. This will include the threat stemming<br />
from the proceeds of emerging crimes such as<br />
ransomware, as well as the vulnerabilities of<br />
sectors like virtual currencies and e-commerce<br />
that call for an innovative AML response.<br />
Throughout this two-year period, the<br />
programme will engage with a wide range of<br />
stakeholders in the UK and globally through<br />
interviews and workshops, building on the<br />
desire to increase the impact of AML efforts.<br />
Today’s technology<br />
Tom Keatinge, director of the Centre for<br />
Financial Crime and Security Studies at RUSI,<br />
explained: “Designing an AML regime that<br />
harnesses the opportunities presented by<br />
technology is one of the programme’s key<br />
objectives. We need to make sure that new<br />
technologies are not simply used to make the<br />
current system work more efficiently. Rather,<br />
they have the potential to make a real<br />
difference in terms of how effectively we tackle<br />
ill-gotten gains. The Financial Crime 2.0<br />
programme will help realise that potential.”<br />
Patrick Craig, EY’s financial crime leader for<br />
the EMEIA region, observed: “We recognise<br />
that co-ordinated action by financial<br />
institutions, regulators, Governments and<br />
international bodies is needed, and we’re<br />
pleased to be a part of the co-operation that’s<br />
being launched. Taking an intelligence-led<br />
approach, enabled by technological innovation<br />
and behavioural science, is critical to the<br />
effectiveness of financial crime management.<br />
We want to help the industry to innovate.”<br />
Brian Dilley, director for fraud and financial<br />
crime prevention at the Lloyds Banking Group,<br />
added: “The world has changed since many of<br />
the AML regimes were put in place and we need<br />
to ensure that we keep pace with the criminals<br />
to reduce the harm they do to society. It’s no<br />
longer effective to consider different types of<br />
financial crime separately as the criminals don’t<br />
do so. Cyber crime, fraud and money laundering<br />
are all part of the same process for them and,<br />
unless we look at these issues collectively, the<br />
criminals will hide in the gaps. It’s time to use<br />
innovation as a tool to fight crime rather than<br />
seeing it as a threat.”<br />
Phil Cotter, managing director of risk at<br />
Thomson Reuters, concluded: “Despite<br />
considerable efforts and resources devoted to<br />
anti-money laundering, we only detect and<br />
recover around 1% of the more than $2.4 trillion<br />
of money laundering and other criminal activity<br />
estimated to be flowing through the<br />
international financial system. More needs to<br />
be done in both the private and public sectors.”<br />
With the support of EY,<br />
the Lloyds Banking<br />
Group and Thomson<br />
Reuters, the Royal<br />
United Services<br />
Institute (RUSI) is set<br />
to conduct a detailed<br />
review of the current<br />
anti-money laundering<br />
(AML) regime in order<br />
to assess what<br />
reforms are required<br />
to tackle financial<br />
crime in the modern<br />
age. Risk UK reports<br />
11<br />
www.risk-uk.com
Nedap’s Global Client Programme<br />
Standardise your security worldwide<br />
<br />
always up to date?<br />
The Global Client Programme by Nedap Security Management supports you in implementing,<br />
maintaining and updating AEOS – the leading access control system – across multiple<br />
international sites.<br />
We’ll be at ASIS Europe 2018 in Rotterdam from Wednesday 18 to Friday 20 April. Call by to<br />
<br />
As an ASIS member, you’re welcome to join us at our ASIS welcome party on 18 April.<br />
www.nedapsecurity.com/how-we-help/global-client
Opinion: Access Control and the Equality Act 2010<br />
As professionals operating in the security<br />
industry, we have strict obligations to help<br />
our customers enforce the protection of<br />
people and assets, but equally so to assist<br />
authorised users in using security systems on a<br />
regular basis. Unfortunately, it can be all-tooeasy<br />
to overlook features or specific designs<br />
which can make all the difference to those<br />
people with a whole range of disabilities and<br />
specific needs.<br />
It’s vital that everyone is supported by<br />
effective access control. This goes beyond the<br />
obvious moral obligations and is rightly<br />
enshrined in law in many parts of the world.<br />
A key piece of UK legislation here is the<br />
Equality Act 2010, which applies to England,<br />
Scotland and Wales. According to the Act, a<br />
given individual has a disability if they have a<br />
physical or mental impairment and that<br />
impairment exerts a substantial and long-term<br />
adverse effect on their ability to carry out<br />
normal day-to-day activities.<br />
The Equality Act 2010 specifically stipulates<br />
that discrimination occurs if a person treats<br />
another unfavourably because of something<br />
arising in consequence of their disability, and it<br />
cannot be shown that the treatment is a<br />
proportionate means of achieving a legitimate<br />
aim. This doesn’t apply if it can be shown that<br />
the person didn’t know – and could not<br />
reasonably have been expected to know – that<br />
the other had the disability.<br />
Beyond this careful wording, the key<br />
message to remember is that no person with a<br />
disability should be placed at a<br />
disproportionate disadvantage by the facilities<br />
they use. This simple and fair assessment does,<br />
however, mean that security solution providers<br />
need to understand the full range of<br />
requirements and the best ways of catering for<br />
all security system end users.<br />
Broad range of needs<br />
The blanket term ‘disabilities’ covers a very<br />
broad range of additional needs, so careful<br />
consideration is required to ensure that secure<br />
access control systems best cater for everyone<br />
needing to use them. Disabilities can be<br />
physical or learning-related difficulties, as well<br />
as a combination of both. They may be just as<br />
unique as the individual themselves.<br />
Difficulty of movement and interaction are<br />
obvious challenges for those with disabilities<br />
when it comes to using access control. Equally,<br />
those who are registered blind (or have varying<br />
degrees of sight impairment and/or hearing<br />
difficulties) can also struggle with security<br />
systems if they’re not installed in a way that’s<br />
mindful of varying needs.<br />
Access Control:<br />
Designing for All<br />
In our everyday world, it can sometimes be far too easy for us<br />
to forget the obstacles many people with disabilities face<br />
when it comes to just living their daily lives. Here, John<br />
Davies examines the importance of effective access control in<br />
making their lives that bit easier<br />
Individuals with learning difficulties may also<br />
require additional assistance with access<br />
control systems. For instance, biometric readers<br />
may be far more suitable than a PIN code<br />
reader as they’re particularly intuitive and<br />
straightforward for individuals to use, without<br />
any requirement for reading or memorising any<br />
kind of information.<br />
The Equality Act 2010 isn’t prescriptive with<br />
regards to ‘reasonable adjustments’, but suffice<br />
to say these will vary depending on the facility<br />
where the access control solution is being<br />
installed, the specifics of the building(s)<br />
involved and the collective needs of the people<br />
using the location(s).<br />
It’s fair to say that common sense is a key<br />
part of any security installation and this is no<br />
different when it comes to systems that will<br />
support people with additional needs. The<br />
starting point is to examine the physical<br />
features of the installation facility and the<br />
needs of the individuals and groups who make<br />
use of it. This isn’t just the people who<br />
currently use a given location. Ideally, it needs<br />
to include anyone who could use the location in<br />
the future as well.<br />
John Davies:<br />
Managing Director of TDSi<br />
13<br />
www.risk-uk.com
Opinion: Access Control and the Equality Act 2010<br />
Building features<br />
Building features can be numerous. They could<br />
be features arising from the design or<br />
construction of a building, an approach to/exit<br />
from or access to a building, fixtures or<br />
fittings/furniture/furnishings/materials or<br />
indeed any other physical element or quality.<br />
Again, common sense is demanded here to<br />
assess these against the requirements of<br />
security and people.<br />
Obvious adjustments include improved<br />
physical accessibility, such as using barriers<br />
instead of traditional turnstiles and adding<br />
handrails, ramps or lifts where required. It<br />
could also be about using braille, audio<br />
announcements or voice recognition to<br />
overcome visual impairments, or equally visual<br />
announcements to help those individuals who<br />
are hearing-impaired. People with arthritis may<br />
benefit from specially-designed security<br />
keyboards/touchscreens or displays. Readers<br />
may need to be positioned such that those with<br />
wheelchairs and movement aids can more<br />
easily use them.<br />
The question of if an improvement is<br />
reasonable must be addressed. Does it work<br />
and successfully help people to overcome a<br />
difficulty? Is it practical to install and use, and<br />
will it cause significant disruption in doing so?<br />
Is there a financial impact and a possibility of<br />
financial or other assistance to help (such as a<br />
grant)? Every case is individual and needs<br />
careful consideration in its own right.<br />
Different organisations and projects will<br />
inevitably require different solutions. For<br />
example, a school for children with special<br />
needs may need a completely different access<br />
control approach to an office facility. The school<br />
may cater for pupils with specific disabilities<br />
and will therefore require specific systems<br />
designed to actively assist both them and the<br />
teaching/care staff.<br />
It’s also dangerous to make generalised<br />
assumptions with regards to access needs.<br />
With the special needs school, for example,<br />
new pupils may be enrolled who require<br />
additional support over current facilities. It’s<br />
also important that people don’t feel excluded<br />
or segregated because of their needs. For most<br />
installations it makes perfect sense to design<br />
an access control solution that can be used by<br />
anyone and everyone.<br />
“The Equality Act isn’t prescriptive with regards to<br />
‘reasonable adjustments’, but suffice to say these will vary<br />
depending on the facility where the access control solution<br />
is being installed and the specifics of the building(s)”<br />
Ensuring that access control is easy to locate<br />
and use (even for first-time users) is also key.<br />
Signage or instructions is a vital part of these<br />
systems and needs to cater for everyone.<br />
Written instructions may be fine for some, but<br />
those with sight impairment or learning<br />
difficulties may struggle. Audio or pictorial<br />
alternatives offer options that can be<br />
understood by a greater percentage of people.<br />
Always safety first<br />
Naturally, access control isn’t just about<br />
security. It also has a vital role to play in safety,<br />
and there’s no room for error when it comes to<br />
ensuring everyone’s protected. As well as<br />
protecting from intruders or attacks, access<br />
control is often central to evacuation in the<br />
event of a fire or other emergency.<br />
Undoubtedly, safety comes first and is about<br />
far more than just a ‘reasonable adjustment’<br />
being made. If access control systems could<br />
impede anyone’s safety in any way, then they’re<br />
not doing their job properly. BS 8300 outlines<br />
recommendations for the design of new<br />
buildings and their approaches to meet the<br />
needs of people with disabilities, while BS<br />
9999 outlines specific recommendations on<br />
means of escape.<br />
While the legalisation is in place to provide<br />
guidance on safe access and evacuation, these<br />
considerations also need to be at the heart of<br />
any access control planning.<br />
In an ideal world, access control facilities<br />
would have a highly prescriptive set of rules<br />
with regards to catering for anyone with<br />
disabilities. In the real world, of course, there<br />
are any number of variables that can complicate<br />
the situation. Many facilities were designed and<br />
built in less enlightened times, when<br />
practicality for the majority of users and cost<br />
were still considered overriding considerations.<br />
Legislation such as the Equality Act 2010 is<br />
necessarily open to interpretation to address<br />
the reality of an imperfect world. However,<br />
security experts are well placed to ensure that<br />
systems and installations meet the needs of as<br />
many people as possible, while also preserving<br />
the overall integrity of protection.<br />
The PyeongChang Paralympic Winter Games<br />
2018 took place last month. Watching the<br />
competitors perform was even more profound<br />
when you consider the additional challenges<br />
they face compared to many other athletes and<br />
sporting competitors around the globe. The<br />
Paralympics served as a timely reminder of the<br />
endurance and ability of the human spirit to<br />
overcome adversity. This is something that<br />
secure access control solutions can positively<br />
help people with in their everyday lives.<br />
14<br />
www.risk-uk.com
Advertisement Feature<br />
Redefining Critical Communications<br />
As is the case each year, Critical<br />
Communications World (CCW) will<br />
highlight the latest innovations that<br />
advance the state-of-the-art in mission-critical<br />
communications. Celebrating its 20th<br />
Anniversary in 2018, CCW is the ‘must attend’<br />
event for critical communications professionals,<br />
bringing the whole industry together under one<br />
roof to drive innovation and knowledge<br />
exchange. CCW is the largest exhibition of its<br />
kind, gathering critical communications<br />
professionals from all around the world.<br />
Over the 20-year history of CCW, much of the<br />
focus has been on establishing TETRA as the<br />
professional mobile radio (PMR) technology of<br />
choice for mission-critical voice and data<br />
communications. This year, however, marks a<br />
turning point for CCW’s parent as The Critical<br />
Communications Association (TCCA) moves to<br />
supplement TETRA communications with highcapacity<br />
mobile broadband data capabilities<br />
solidly built on LTE networking.<br />
While debates continue to rage about the<br />
potential of shifting mission-critical voice<br />
communications to LTE, the benefits of<br />
incorporating robust mobile broadband<br />
networking into the communications toolkit are<br />
certainly well-understood by stakeholders in<br />
Government. CCW 2018 will bring these<br />
stakeholders as well as supporting ecosystem<br />
partners from across industry together for indepth<br />
discussions on the future of public safety<br />
communications around the globe.<br />
Mobile network operators<br />
The timing of CCW 2018 is particularly<br />
important for mobile network operators. Terror<br />
attacks and natural disasters have prompted<br />
security officials worldwide to look aggressively<br />
at LTE technology. By augmenting voice-centric<br />
TETRA communications with mobile broadband<br />
networks, these officials can deliver better<br />
incident command tools that increase<br />
situational awareness. Mobile network<br />
operators need to take advantage of CCW 2018<br />
in order to engage with these potential<br />
customers and explore their requirements.<br />
Today, mobile networks offer IP data services<br />
designed to serve both consumer and<br />
enterprise customers. Fortunately, the<br />
continued evolution of LTE technology provides<br />
quality of service and access barring tools that<br />
serve to protect select traffic streams during<br />
times of network congestion.<br />
CCW 2018 is an ideal opportunity for strategy<br />
planners to explore future opportunities in<br />
depth. Aside from myriad conference sessions<br />
featuring Governmental leaders, the exhibition<br />
floor hosts a wide range of vendors ready to<br />
add different perspectives on the opportunities<br />
and challenges ahead. Just as important, the<br />
one-on-one networking that’s possible at<br />
conference assists in opening direct lines of<br />
communication between MNO planners and<br />
Government agency officials.<br />
Masterclasses and conference<br />
The ‘Pushing The Boundaries of Innovation’<br />
Masterclass runs on 15 May from 9.30 am to<br />
4.30 pm. Do you want to derive more from your<br />
PMR system? Do you wish to migrate to<br />
broadband, but are not sure what else you<br />
could connect to it? Could your business<br />
benefit from the IoT revolution?<br />
On the same day, the ‘How To Manage Large-<br />
Scale Events’ Masterclass is hosted by the<br />
Federal Agency for Public Safety Digital Radio<br />
(BDBOS) and targets the critical communication<br />
community in general, but addresses especially<br />
end users and practitioners. Those who attend<br />
will enjoy thought-provoking and first-hand<br />
reports on how to manage large-scale events.<br />
The first part of the ‘BDBOS Tactical Day’<br />
examines international experiences. Users,<br />
operators and experts will share their<br />
knowledge gathered in a variety of international<br />
mission-critical events. In the afternoon,<br />
technical solutions are to emphasise both the<br />
technical and tactical challenges faced when<br />
managing operations.<br />
The conference programme running on 16<br />
and 17 May is split into three streams of<br />
content. On 16 May, topics covered are<br />
scheduled to include a presentation and<br />
discussion on 5G and critical communications,<br />
the new possibilities to be realised by<br />
combining critical comms with the IoT and Big<br />
Data analysis and how end users can overcome<br />
the challenges presented by TETRA and LTE<br />
interconnection. Using IP networks as a secure<br />
platform for critical comms is the subject of<br />
Peter Cox’s presentation in Stream B. Cox is the<br />
CEO and Founder of UM Labs.<br />
Paul Steinberg (senior vice-president and<br />
CTO at Motorola Solutions) is speaking on Day<br />
Three at conference and will observe how<br />
technology is going to actively support first<br />
responders in the field going forward.<br />
There’s also a detailed delivery on LTE<br />
devices in critical communications and how to<br />
ensure a reliable ecosystem. The speaker here<br />
is Bittium director Markku Korkiakosi.<br />
The Critical<br />
Communications<br />
Association is set to<br />
run its flagship<br />
industry event, Critical<br />
Communications<br />
World 2018, at Messe<br />
Berlin from 15-17 May.<br />
Event organiser MA<br />
Exhibitions (the Mark<br />
Allen Group) offers the<br />
readers of Risk UK a<br />
preview of the content<br />
lined up for delegates<br />
attending the various<br />
conference sessions,<br />
the Masterclass<br />
Programme and, of<br />
course, the exhibition<br />
Register online for CCW 2018<br />
www.critical-communicationsworld.com
Quelling Those Aggressive Streaks<br />
Violence in the<br />
workplace includes<br />
everything from verbal<br />
abuse, pushing and<br />
punching to spitting,<br />
sexual assault and<br />
even stabbing. While<br />
stabbings and sexual<br />
assaults are not an<br />
everyday occurrence,<br />
the other incidents are<br />
more common than<br />
you might wish to<br />
believe. Daniel Hardy<br />
examines the scale of<br />
the problem<br />
specifically in the<br />
retail sector, the<br />
reasons behind its<br />
growth and what<br />
needs to be done to<br />
keep employees safe<br />
The Health and Safety Executive (HSE)<br />
defines work-related violence as “any<br />
incident in which an employee is abused,<br />
threatened or assaulted by a member of the<br />
public in circumstances arising out of the<br />
course of his/her employment”. The<br />
repercussions of such violence can have<br />
devastating consequences on the physical and<br />
psychological health of those affected.<br />
Although the Health and Safety at Work etc<br />
Act 1974 states that employers have a legal<br />
Duty of Care to ensure (so far as is practicable)<br />
the health, safety and welfare at work of their<br />
employees, the measures implemented can<br />
often fall very short of what’s required.<br />
The 2015-2016 Crime Survey for England and<br />
Wales found that an estimated 1.4% of working<br />
adults have been the victims of one or more<br />
violent incidents at work, with 350,000 adults<br />
having experienced an event of this nature.<br />
During this period, there were an estimated<br />
698,000 incidents of violence comprising<br />
329,000 assaults and 369,000 threats.<br />
Employees in the protective service<br />
occupations are at highest risk, with healthcare<br />
professionals and health and social care<br />
specialists also regularly affected. However,<br />
those working in the retail sector are<br />
increasingly in danger, with the British Retail<br />
Consortium’s (BRC) just published 2017 Retail<br />
Crime Survey figures highlighting the fact that<br />
the rate of incidents of violence with injury has<br />
doubled since the previous year to total six per<br />
1,000 members of staff.<br />
While these statistics identify a clear and<br />
worrying trend, what’s just as concerning is the<br />
lack of conversation relating to what’s causing<br />
these figures. First of all, shopping habits have<br />
changed. Shopping is now a daily occurrence<br />
and, therefore, footfall across the retail sector<br />
is up which, in turn, means that the volume of<br />
crime has risen. Second, the operating model of<br />
retail businesses has changed, with the number<br />
of colleagues working in stores diminishing due<br />
to the use of technology such as self-serve tills.<br />
While stores working smarter and using<br />
technology is, in many ways, very much a good<br />
thing, the big downside to all of this is that<br />
there’s less customer engagement.<br />
Better customer service prevents violence<br />
and, as anyone who has had to stand in a long<br />
queue will recognise, avoids customers’<br />
patience wearing thin. However, the prevalence<br />
of defensive merchandising and planograms<br />
means that high risk or high value items are<br />
locked in a cabinet or kept behind the checkout<br />
counter. This can frustrate the shopper, may<br />
lead to lost sales and could be a contributing<br />
driver for acts of violence.<br />
Retailers have a responsibility to comply with<br />
age-related sales legislation relating to<br />
products such as alcohol, knives and cigarettes,<br />
but criminals are increasingly using violence<br />
and abuse when challenged, in turn triggering<br />
enhanced threats. If these points are combined<br />
with poor or non-existent confrontation<br />
management training, some colleagues could<br />
inadvertently exacerbate a problem still further<br />
and actually serve to inflame potentially<br />
volatile situations through a lack of what’s best<br />
described as emotional intelligence.<br />
Such a ‘perfect storm’ means that violence is<br />
becoming more commonplace and, when it<br />
does occur, there are too few colleagues on<br />
hand who are able to deal with the problem in a<br />
swift and efficient manner.<br />
Time isn’t a healer<br />
Reporting crime takes time and, therefore, an<br />
increasing number of retail staff are opting not<br />
to do so, as it usually requires internal<br />
documentation, dealing with the police and<br />
perhaps liaison with local crime partnerships.<br />
In addition, given that the Anti-Social<br />
Behaviour, Crime and Policing Act 2014 makes<br />
theft from a shop of goods worth £200 or less a<br />
summary-only offence, it seems that retailers<br />
are simply not bothering to pursue some cases.<br />
The same often goes for acts of verbal and<br />
physical aggression. The former have become<br />
so normalised that they’re often not considered<br />
a violent act, just ‘par for the course’. There’s<br />
16<br />
www.risk-uk.com
Opinion: Mind Your Own Business<br />
also the lack of respect that some people have<br />
for authority and this is combined with an<br />
awareness that police services are under so<br />
much resource pressure that they will probably<br />
not attend the scene of anything but the most<br />
serious of incidents.<br />
The issue of inefficient reporting shouldn’t be<br />
underestimated or ignored, as it creates a<br />
situation wherein the scale of the problem is<br />
unclear, so sufficient law enforcement or<br />
security resources cannot be allocated to deal<br />
with it. Worryingly, on the subject of reporting<br />
incidents, the BRC’s 2016 Retail Crime Survey<br />
stated that 56% of retailers questioned thought<br />
that the police service’s performance was either<br />
‘Poor’ or ‘Very poor’.<br />
Taking action<br />
With the rising crime figures and falling police<br />
numbers, the frontline of retail clearly has the<br />
potential to be a dangerous environment for<br />
many shop workers. There’s still a lot to do to<br />
help protect them. Employers should do all they<br />
can to prevent attacks occurring in the first<br />
place and, if an event does occur, provide their<br />
employees with all the support they need.<br />
Health and Safety law applies to risks from<br />
violence, just as it does to other risks from<br />
work. In parallel with the Health and Safety at<br />
Work etc Act 1974, the Management of Health<br />
and Safety at Work Regulations 1999 state that<br />
employers must consider all risks to employees<br />
(including the possibility of reasonably<br />
foreseeable violence), decide how significant<br />
these risks are, determine what to do to<br />
prevent or control them and develop a clear<br />
management plan.<br />
Developing a policy on the management and<br />
prevention of violence can help employers<br />
avoid costs relating to low staff morale, high<br />
absenteeism and staff turnover, expensive<br />
insurance premiums and, possibly,<br />
compensation payments. A policy should<br />
identify how any risk can be controlled and set<br />
out how preventative measures will operate<br />
while detailing training, changing work patterns<br />
or dealing with specific customer groups.<br />
For example, those working in pharmacies<br />
will often have to deal with vulnerable people<br />
such as drug addicts and the mentally ill, while<br />
those in off-licences will sometimes encounter<br />
individuals who abuse alcohol.<br />
Protect and survive<br />
Even though retailers are initiating leaner<br />
operational strategies to protect profit margins,<br />
the BRC claims that they’re also spending<br />
record amounts on crime prevention, security<br />
and other measures to keep staff safe. The<br />
BRC also recognises that this level of financial<br />
investment is, ultimately, unsustainable.<br />
This isn’t really a surprise, as security<br />
guarding can be costly to implement and<br />
maintain, as can remote monitoring. Although<br />
technology such as lone worker devices and<br />
panic buttons have proven to be effective in<br />
other sectors, many retailers question whether<br />
it’s worth investing in them if the police are<br />
unlikely to show up when they’re activated.<br />
Likewise, although civil injunctions and<br />
Banning Orders can be used to address antisocial<br />
behaviour, they can be costly and timeconsuming<br />
to pursue.<br />
There’s certainly a good return on investment<br />
argument to be made for the more widespread<br />
collaboration between retailers to pool<br />
knowledge, share information on Best Practice,<br />
build a safer working community and set up<br />
crime prevention initiatives. The General Data<br />
Protection Regulation isn’t a blocker to<br />
legitimately preventing crime, lowering risks<br />
and protecting staff.<br />
By joining forces, retailers can also use<br />
technology, security guarding, data acquisition,<br />
analytics and information sharing as tools in<br />
the battle against workplace violence. This<br />
reduces expense for retailers and can facilitate<br />
the deployment of a shared resource of highly<br />
trained and skilled personnel who can be<br />
notified about an incident via a smart device as<br />
to where help is needed and provide an<br />
immediate response. Key Performance<br />
Indicators can be agreed in advance and there’s<br />
also the potential for live incident reporting.<br />
This can help to ensure a police response.<br />
On a related subject, the process regarding<br />
the development of Business Improvement<br />
Districts must be enhanced. Charging a levy on<br />
all ratepayers, in addition to the Business Rates<br />
Bill, in order to benefit businesses in a given<br />
local area has seen a certain level of success.<br />
However, as things stand it offers an<br />
inconsistent approach towards delivering real<br />
improvements as safety and security are not<br />
part of the manifesto of a bid. This situation<br />
needs to change and must become part of the<br />
five-yearly renewal process.<br />
Physical violence in retail workplaces is<br />
increasing year on year. Decisive action must be<br />
taken to counter this trend or the consequences<br />
could – quite literally – prove to be fatal.<br />
Daniel Hardy:<br />
Managing Director at the<br />
National Business Crime<br />
Solution (NBCS)<br />
*Mind Your Own Business is the<br />
space where the NBCS examines<br />
current and often key-critical<br />
business crime issues directly<br />
affecting today’s companies. The<br />
thoughts and opinions expressed<br />
here are intended to generate<br />
debate and discussion among<br />
practitioners within the<br />
professional security and risk<br />
management sectors. If you would<br />
like to make comment on the<br />
views outlined, please send an<br />
e-mail to: brian.sims@risk-uk.com<br />
**The NBCS is a ‘Not-for-Profit’<br />
initiative that enables the effective<br />
sharing of appropriate data<br />
between the police service, crime<br />
reduction agencies and the<br />
business community to reduce<br />
crime and risks posed to all. By<br />
providing a central repository<br />
where business crime data is<br />
submitted, shared and analysed,<br />
the NBCS is able to gather the<br />
necessary intelligence and support<br />
to more effectively detect, prevent<br />
and, subsequently, respond to<br />
crimes affecting the UK’s business<br />
community. For further information<br />
access the website at:<br />
www.nationalbusinesscrime<br />
solution.com<br />
“The British Retail Consortium’s 2017 Retail Crime Survey<br />
highlights the fact that the rate of incidents of violence<br />
with injury has doubled since the previous year to total six<br />
such episodes per 1,000 members of staff”<br />
17<br />
www.risk-uk.com
3 July 2018<br />
Hilton London Canary Wharf<br />
ONE DAY DAY – – MULTIPLE SOLUTIONS TO YOUR CHALLENGES<br />
eet Meet with with the the most most trusted solution providers, learn from industry thought leaders and and connect with with<br />
eers peers over over the the course of of the the Summit, which is entirely FREE to attend for for security professionals.<br />
opics Topics covered covered include: include: Access Access Control •• Anti-Virus Browser •• Security Data Data • Theft/Loss • • Malware • Malware<br />
Mobile • Mobile Security Security • Network • Network Security Security Management • Trojan Detection • • UK UK Cyber Cyber Strategy Strategy<br />
For more information and to register, please contact Emily Gallagher<br />
on: 01992 374085 or e.gallagher@forumevents.co.uk.<br />
@SECIT_SUMMIT #SITSUMMIT<br />
SECURITYITSUMMIT.CO.UK<br />
MEDIA & INDUSTRY PARTNER<br />
HOSTED BY
Risk Management Strategy: Adapting to Devolving Threats<br />
Government agencies and, in many cases,<br />
commercial security providers usually<br />
have far more technology, manpower and<br />
purchasing power at their disposal than do<br />
today’s smaller and seemingly weaker threats,<br />
and yet it appears that the whole of the UK’s<br />
security industry remains constantly challenged<br />
to ‘keep up’ with ‘evolving’ threats.<br />
Two types of threat that have recently<br />
(d)evolved to become more problematic than<br />
ever include terrorists who have had a great<br />
deal of success using vehicles as weapons and<br />
street robbers who’ve enjoyed similar levels of<br />
success by using motorbikes as get-away<br />
vehicles throughout London and other major<br />
cities. Each of these threats make for<br />
interesting Case Studies for risk professionals<br />
who should be constantly on the lookout for<br />
‘metrics that matter’ as they conduct their risk,<br />
threat and vulnerability assessments.<br />
While technology, manpower and big budgets<br />
have contributed a great deal towards security<br />
throughout the UK, recent trends have shown<br />
that a great deal of damage can still be done by<br />
‘underdog’ threats operating alone and on<br />
shoestring budgets. It’s imperative that risk<br />
professionals don’t underestimate the value of<br />
key capabilities, like speed and surprise, both<br />
of which have been well-leveraged with<br />
unprecedented effect in recent times.<br />
Evolving Backwards:<br />
Strategies for Adapting<br />
to Devolving Threats<br />
With relatively efficient and professional policing and a<br />
robust private security sector, terrorism and organised crime<br />
have historically been kept to manageable levels. Across the<br />
past few years, though, there have been upticks in terrorism<br />
and violent crime trends as perpetrators have found low-cost<br />
solutions to escape detection and evade arrest. Philip Strand<br />
and Christine Annerfalk search for a solution<br />
Variety of metrics<br />
A wide variety of metrics can be used to assess<br />
the capabilities of threat actors. Technological<br />
capabilities are often measured in terms of<br />
available weaponry, communications<br />
equipment and transport. Total numbers of<br />
threat actors are almost always of interest to<br />
risk analysts, while the ability of a threat actor<br />
or group to secure funding for purchasing<br />
additional supplies and training is normally<br />
factored into risk assessments.<br />
That said, are these metrics always the most<br />
important in comparison to target<br />
organisations’ people and assets? While<br />
criminals, terrorists and other threat actors are<br />
usually fewer in number, lower on funding and<br />
sometimes less well educated than members of<br />
the UK’s public and private security services,<br />
it’s not uncommon for threats to slip by even<br />
sophisticated security systems. It’s arguably<br />
true that the less technology attackers use, the<br />
less effective and capable they are, but their<br />
lack of sophistication can make them extremely<br />
difficult to both detect and disrupt.<br />
It quickly becomes the case that many<br />
successful small-scale attacks can have a<br />
greater effect on a Government, a given<br />
organisation or a population than a few largescale<br />
attacks that never actually make it past<br />
the planning stage.<br />
Islamist-inspired terrorism<br />
One type of threat actor that has ‘devolved’ to<br />
circumvent the strengths and advantages of the<br />
UK’s Security Services is the Islamist-inspired<br />
terrorist. In the wake of several high-profile<br />
terrorist attacks in Belgium and France<br />
involving guns and explosives, law enforcement<br />
agencies throughout Europe took swift action<br />
to stem the spread of high(er)-tech weaponry.<br />
Not to be deterred from their goals, terrorist<br />
leaders re-assessed their followers’ capabilities<br />
and the defences of their primary targets:<br />
citizens in the streets. Calls went out from Al-<br />
Qaeda and ISIS “explicitly… to employ cars as<br />
weapons” to “mow down [their] enemies”.<br />
Terrorist groups’ correct assessments of their<br />
own capabilities compared to those of their<br />
Dr Philip Strand PhD MBA:<br />
Senior Risk Consultant at<br />
CornerStone<br />
19<br />
www.risk-uk.com
Risk Management Strategy: Adapting to Devolving Threats<br />
Christine Annerfalk:<br />
Associate Researcher at<br />
CornerStone<br />
targets resulted in a spate of successful attacks<br />
within technologically-advanced societies.<br />
Vehicle attacks in London, Antwerp and<br />
Stockholm last year left no doubt that a new<br />
trend had emerged in the tactics and modus<br />
operandi of Islamist-inspired terrorism.<br />
Unfortunately, the spread of knowledge<br />
didn’t stop with that particular threat group,<br />
but extended into the ranks of far-right<br />
terrorists, as evidenced by the 2017 Finsbury<br />
Park attack which resulted in one person’s life<br />
being lost and eleven others wounded as they<br />
emerged from a place of worship.<br />
There may once have been a day when the<br />
stereotypical image of a Jihadi terrorist was a<br />
man in a difficult-to-manufacture explosive vest<br />
carrying an expensive-to-procure assault rifle.<br />
Islamist propaganda and magazines succeeded<br />
in making terrorism accessible to everyone and<br />
not necessarily less effective for any lack of<br />
complex weapons, equipment and training. Law<br />
enforcement agencies’ superior training,<br />
weaponry, communications and processes were<br />
enough to limit the attacks, but not enough to<br />
prevent them from occurring in the first place.<br />
Outmanoeuvring technology<br />
A second type of threat actor that has used<br />
simple tactics and tools to outmanoeuvre<br />
technologically-superior security personnel are<br />
the motorbike thieves of London.<br />
Throughout the capital, criminals have<br />
figured out that scooters, mopeds and<br />
motorbikes offer low-cost solutions to mobility<br />
challenges. Historically, the UK’s police have<br />
had the advantage of superior numbers and<br />
command, control and communications (ie C3)<br />
capabilities. In the face of budget cuts, the<br />
police adopted a strategy of intelligence-led<br />
policing, which enabled them to reach crime<br />
scenes before the robbers could move on to<br />
their next victims, effectively limiting the<br />
amount of harm a single robber could cause.<br />
Not to be outdone by superior intelligence<br />
and information capabilities, robbers have now<br />
realised that speed and manoeuvrability are<br />
key when it comes to overmatching the police’s<br />
dwindling numbers. From motorbikes, a pair of<br />
robbers can snatch mobile phones and<br />
handbags throughout a square kilometre area<br />
at a pace of 12 to 15 items within a 30 to 45<br />
minute-long spree.<br />
“It’s arguably true that the less technology attackers use,<br />
the less effective and capable they are, but their lack of<br />
sophistication can make them extremely difficult to both<br />
detect and disrupt”<br />
According to police, a scooter can be stolen<br />
in 30 to 40 seconds by an experienced thief and<br />
that scooter can then become an enabler for a<br />
spate of follow-on crimes. To make matters<br />
worse, scooter gangs can take advantage of UK<br />
laws stating that the police must discontinue<br />
pursuit if that pursuit poses risks to life.<br />
In practice, motorbike-mounted thieves know<br />
that the passenger can simply remove their<br />
helmet and the police will discontinue their<br />
pursuit. The police’s co-ordination, equipment<br />
and ability to rapidly respond becomes useless<br />
when they’re slowed down by traffic.<br />
Low-tech tools in use<br />
While it’s clear that both terrorists and street<br />
criminals have now embraced the use of easyto-obtain<br />
vehicles to carry out their attacks,<br />
they’ve also shown that they realise it’s not just<br />
the vehicles themselves that offer them<br />
advantages. Many of these two types of threat<br />
actors have also employed knives, hammers<br />
and other widely-available and unsophisticated<br />
tools to threaten or harm their victims. The<br />
trend towards low-tech tools suggests a<br />
conscious realisation that ‘gearing up for war’ is<br />
counterproductive in an environment where the<br />
security forces have so many advantages and<br />
the same goals can be achieved with much less.<br />
It’s now time for the UK’s security community<br />
– and the citizens who support it – to make the<br />
next move. Fortunately for tax payers and<br />
businesses alike, levelling the playing field<br />
doesn’t require pouring more money into old<br />
risk management strategies. Motorbike gang<br />
members may be difficult to catch in the<br />
streets, but we can support the police in their<br />
efforts to provide crime prevention advice to<br />
citizens on social media and hold Open Days<br />
with city councils specifically aimed at<br />
combating motorbike-assisted crime.<br />
In the same way that it requires other built-in<br />
safety features on vehicles, the UK Government<br />
can also demand that motorbike manufacturers<br />
take steps to make machines more difficult to<br />
steal. It may also be necessary to fund the<br />
deployment of greater numbers of unmarked<br />
vehicles with highly-trained drivers who will<br />
have greater leeway to pursue moped-riding<br />
robbers if they should spot them in the street.<br />
Preventing vehicle-enabled terrorism is a<br />
more complicated, but not impossible task.<br />
Terrorist leaders who promote low-tech attacks<br />
still rely on high-tech forms of communication<br />
and networking. Terrorists may benefit from<br />
hiding in plain sight, but the Government can<br />
leverage its greater expertise, funding and<br />
access to Big Data in order to identify threats<br />
before they become operational.<br />
20<br />
www.risk-uk.com
www.coie.uk.com<br />
Cortech Open<br />
Innovation Event<br />
IFSEC 2018, ExCel, South Gallery Room 28, E16 1XL<br />
19-21 June 2018<br />
The Mitigation of Risk for Workplace Safety, High Security<br />
<br />
<br />
Be educated, informed and better equipped to manage evolving building needs<br />
<br />
See technology in action as part of the live demonstration<br />
Discover the latest smart integration techniques<br />
Discuss industry challenges with fellow security professionals and technology experts<br />
Learn about GDPR compliance and cyber security resilience<br />
Attending Partners<br />
Cortech<br />
<br />
Media Partner
Securing Critical Assets<br />
various levels of authorisation and needing<br />
access to specific locations at certain times.<br />
Access control<br />
systems have come a<br />
long way since the<br />
invention of the lock<br />
and key.<br />
Advancements in<br />
technology have<br />
realised solutions to<br />
be integrated with<br />
web-based systems,<br />
allowing for<br />
traceability and time<br />
management within<br />
mechanical keys.<br />
Here, Pip Courcoux<br />
discusses integrated<br />
access control and<br />
why the protection<br />
regime enacted for<br />
physical assets is just<br />
as important as that<br />
imparted with data<br />
security in mind<br />
The technological evolution in access control<br />
has created passkeys, cryptographic keys<br />
and encryption keys. Although all of these<br />
new access control products are available,<br />
cyber security often remains the focus of many<br />
organisations’ security concerns, with physical<br />
security an afterthought. For example, you<br />
know to change your e-mail password and web<br />
logins every three months in order to keep your<br />
online information secure, but how often do<br />
you change your keys?<br />
Data and cyber security vigilance is<br />
important, but it’s a futile exercise if someone<br />
can attack your assets through the use of your<br />
keys. In short, organisations shouldn’t become<br />
so focused on cyber security that they’re failing<br />
to protect their premises effectively.<br />
Keys provide physical access to critical<br />
assets, including areas that house servers<br />
holding customer data, and to offices where<br />
customers’ accounts are managed. Despite this,<br />
we often see organisations unsure of how many<br />
keys they have in circulation, or where they are<br />
at any given moment in time.<br />
One of the issues faced by large<br />
organisations, and especially those residing in<br />
the Critical National Infrastructure (CNI) sphere,<br />
is the vast number of key holders accessing<br />
disparate sites. This presents major difficulties<br />
in controlling those keys. Key holders can range<br />
from full-time employees through to temporary<br />
staff members and on to contractors. All of<br />
these key holders will have different and<br />
individual access control requirements, with<br />
Compliance is key<br />
Take contractors as an example. If you have a<br />
data processing contract, they would require<br />
access to data for a period of time to complete<br />
their work, but there would be defined steps in<br />
place to make sure that, once the contract has<br />
finished, they no longer have access to (or any<br />
visibility of) the data involved. If the contractor<br />
has a physical key it’s much harder to restrict<br />
their future access to the system.<br />
When it comes to temporary staff, you may<br />
have new employees joining an organisation,<br />
people moving to different departments and<br />
also members of staff leaving. Once an<br />
employee moves departments, electronic<br />
access to software and systems can be easily<br />
controlled, but physical access restriction is far<br />
trickier. It’s easy to wipe someone’s phone or<br />
laptop if they lose it or leave the business, but<br />
you cannot do this with a mechanical key.<br />
With regards to permanent staff, compliance<br />
is vital. Do they have the permits to work in a<br />
given area and can you control it? Any business<br />
changes such as mergers and acquisitions can<br />
alter a person’s responsibility. In this instance,<br />
data access may be controlled electronically<br />
with ease, but it’s difficult to be so flexible on<br />
physical access with mechanical keys.<br />
Taking control<br />
What, then, is the solution to this issue of key<br />
control to protect critical assets and<br />
information? Electronic key solutions that<br />
feature web-based management can be<br />
integrated with existing telemetry systems to<br />
help control and manage operations. This offers<br />
a high level of both physical and data<br />
protection, given that they only use accredited<br />
software and infrastructure providers. For<br />
example, some systems boast an electronic key<br />
system where all the power is retained by the<br />
key or locks themselves. This means no wiring<br />
is required, whether the system uses door<br />
cylinders, cabinet locks or padlocks.<br />
End users have secure access to an online<br />
management application from anywhere in the<br />
world and can change key access permissions,<br />
profiles, schedules and validity, even revoking<br />
their use virtually at the click of a button. Keys<br />
may be validated daily, weekly or monthly for<br />
continuous security. Users are required to<br />
change their password every three months.<br />
22<br />
www.risk-uk.com
Access Control: Integrated Business Systems for Risk Professionals<br />
This enables an organisation to<br />
comprehensively track and audit who has<br />
access to which locations, when they had<br />
access and on how many occasions. Access can<br />
be granted only at the exact moment it’s<br />
required, thereby mitigating the risks<br />
associated with lost or stolen keys.<br />
Bluetooth 4.0 technology<br />
What’s more, certain advanced systems take<br />
advantage of the latest Bluetooth 4.0<br />
technology, meaning that keys can be activated<br />
through a smart phone and access rights<br />
granted to the user ‘on site’. This revolutionises<br />
remote access control by bringing it firmly and<br />
squarely into the mobile era, subsequently<br />
offering flexibility and time savings as well as<br />
enhancing ease of use.<br />
This offers a solution to the issue of key<br />
control and being able to effectively manage<br />
access rights in organisations where there’s<br />
staff fluidity. If a key should happen to be lost,<br />
or if a contractor or temporary member of staff<br />
needs access revoking, this can all be done<br />
centrally by an administrator, minimising the<br />
risk of a physical security breach.<br />
In addition, if access rights need to be<br />
altered, with a permanent employee being<br />
given permission to enter more areas, this can<br />
be done both quickly and easily, even with the<br />
use of a smart phone.<br />
Operational efficiency<br />
In the case of CNI operations, security is vital to<br />
the continuity of essential services. As well as<br />
minimising the vulnerability of an organisation,<br />
there are many additional benefits to be gained<br />
when installing a solution such as this and<br />
integrating it with other ‘smart’ systems.<br />
Financial savings, CO 2 emissions reduction<br />
and, most importantly, time savings can all be<br />
made with smart infrastructure integration. For<br />
example, access control can be linked with<br />
‘Enterprise Resource Planning’ systems to<br />
identify key holders on shift. ‘Permit to Work’<br />
systems can be linked to ensure that they’re<br />
still compliant for the job at hand and with<br />
telemetry and SCADA systems to ascertain<br />
where they need to be.<br />
The hybrid between mechanical and<br />
electronic technologies is the ‘key’ to success<br />
in this arena, maintaining the strict standards<br />
required for security while also enhancing<br />
operational efficiencies for the future.<br />
Many organisations in the power generation,<br />
water supply, telecoms, financial and<br />
healthcare sectors have witnessed improved<br />
operational control and efficiency when moving<br />
to an integrated web-based access control<br />
“Certain advanced systems take advantage of the latest<br />
Bluetooth 4.0 technology, meaning that keys can be<br />
activated through a smart phone and access rights granted to<br />
the user on site. This revolutionises remote access control”<br />
system. One institution even saw a return on<br />
investment of 600% in the first 12 months<br />
following installation. Most importantly for any<br />
host organisation, when the data’s secure and<br />
managed effectively, the service continuity and<br />
resilience is guaranteed.<br />
Supply chain data<br />
When integrating an access control solution<br />
with other cloud-based systems, it’s inevitable<br />
that the issue of data security does come into<br />
play. Although implementing an access control<br />
system such as the one previously mentioned<br />
offers high security and operational<br />
efficiencies, data security in the supply chain<br />
needs to be considered in detail as well.<br />
Resilience is a key factor. Ensuring a safe<br />
supply chain environment can seem like an<br />
impossible task, but there are ways to minimise<br />
risk. Ask yourself: “How ‘stable’ are my<br />
suppliers?”…“From where do they source their<br />
products?”...”How safe and protected are their<br />
assets?”… and “How robust are their own<br />
relationships with their suppliers?”<br />
To mitigate risk, it’s crucial to identify<br />
dependencies and vulnerabilities that can<br />
impact supply chains. Increasing the visibility of<br />
these areas allows organisations to anticipate<br />
their impact and plan ahead for contingencies.<br />
In a similar vein, in order to ensure the<br />
highest level of access control security, the inhouse<br />
security or risk-focused professional<br />
must select a supplier who uses accredited<br />
software and infrastructure providers that<br />
provide enterprise level Software as a Service<br />
solutions compliant with European and national<br />
standards for physically secure key systems.<br />
Three-factor authentications<br />
Three-factor authentications are also desirable,<br />
including standard 256-bit encryption,<br />
advanced encryption and industry standard<br />
SHA-2 SSL certificates.<br />
When it comes to integrated access control,<br />
then, it’s important for security professionals<br />
not to focus all of their attentions solely on the<br />
safety of data. It’s just as important to<br />
guarantee the physical security of assets.<br />
Covering all bases will ensure resilience and<br />
continuity of essential services, while<br />
organisations can reap the additional benefits<br />
of improved operational control and efficiency.<br />
Pip Courcoux:<br />
Sales and Product Manager<br />
for CLIQ Systems at Abloy UK<br />
23<br />
www.risk-uk.com
The Risk Management Journey<br />
There’s no crystal ball<br />
that will magically<br />
outline opportunities,<br />
map risks and provide<br />
a distinct and<br />
unobstructed path to<br />
success. Nonetheless,<br />
as Steve Schlarman<br />
observes, there are<br />
specific stages that<br />
organisations can<br />
expect to move<br />
through when building<br />
an integrated risk<br />
management<br />
programme<br />
24<br />
www.risk-uk.com<br />
Broadly speaking, there are three distinct<br />
stages of risk management maturity:<br />
siloed, managed and advanced. Before a<br />
business can start to move through its own risk<br />
management journey, it must first work out at<br />
which of the three stages it currently resides.<br />
The most common and most basic form of<br />
risk management is to tackle all of the<br />
individual elements within a vacuum or silo.<br />
Many organisations can become stuck in the<br />
most elementary risk and compliance<br />
approaches, with narrow strategies that lack<br />
the context of wider business objectives and<br />
priorities. This strategy relies on front line<br />
employees being in a constant firefighting<br />
mode and can be effective up to a point.<br />
However, with the focus typically on<br />
compliance and tactical risks, the organisation<br />
cannot see beyond the immediate issue. Risk<br />
managers are hunkered down in the trenches<br />
with little forward movement, relying on oldfashioned<br />
approaches that may see the job<br />
done, but will never truly enable them to keep<br />
pace in today’s market.<br />
These organisations need to prioritise<br />
beyond immediate compliance deadlines and<br />
start addressing regulatory and industry<br />
requirements in the most efficient and effective<br />
manner. This requires automating compliance<br />
and building a cohesive strategy to deal with<br />
the ‘table stakes’ of doing business.<br />
Compliance obligations need to be tackled, but<br />
with an eye towards the future.<br />
Building more silos at this point is futile. Risk<br />
and compliance functions need to focus on<br />
where data and processes can be leveraged, reused<br />
and shared and where the limitations of<br />
niche, operational tools can be overcome. By<br />
transforming compliance, companies can<br />
actively pave the way forward to the next stage<br />
in their risk management journey.<br />
Managed risk<br />
Companies that have moved beyond the silo<br />
and made steps to transform compliance will<br />
have common policies, standards and controls,<br />
an effective control infrastructure and efficient<br />
methods to measure, monitor and report the<br />
business’ compliance state. Companies in this<br />
stage have solved – or are well on their way<br />
towards solving – the compliance conundrum<br />
and are poised to harness risk.<br />
These organisations need to become aware<br />
of the various risks they’re juggling and put<br />
plans in place to manage these risks within the<br />
context of a broader strategy. A key factor in<br />
this evolution is addressing both<br />
cyber/technical risk and business risk with a<br />
combined strategy. The business needs to<br />
understand the risks in its technology<br />
landscape, while technologists must be active<br />
participants in addressing business risk.<br />
The risk programme should be focused on<br />
affording the business the insight to navigate<br />
major issues. This process is being fuelled<br />
more and more by metrics and analytical<br />
capabilities that provide visibility into risk.<br />
Companies in the managed stage begin<br />
building the bigger picture, shoring up strong<br />
competencies and bringing weaker elements up<br />
to a stable state. As the business risk<br />
management programme matures, effort begins<br />
shifting from compliance as the key driver to<br />
focus more on risk. The organisation eventually<br />
reaches a point whereby the business<br />
objectives take the lead and the company is<br />
then poised to move to the next stage.<br />
Advanced management<br />
When the organisation has mapped out and<br />
conquered the risk landscape, it’s time to begin<br />
exploring the opportunity landscape. The<br />
organisation is now ready to realise the<br />
competitive advantages of harnessing risk:<br />
beating competitors to market, launching new<br />
products and services with calculated<br />
efficiencies and avoiding major issues that can<br />
affect reputation and the bottom line.<br />
The organisation has turned the corner from<br />
managing unrewarded risk to benefiting from<br />
rewarded risk. Companies in this situation<br />
understand that risk and reward are<br />
intrinsically linked and are ready to focus on<br />
the latter having already conquered the former.<br />
How, though, does a business actually go about<br />
reaching this promised land?<br />
Any journey through the three stages of risk<br />
maturity will depend on many things. There’s<br />
no single path to improving risk management in<br />
an organisation. Organisational complexities,<br />
cultural differences, market factors, business<br />
changes, leadership shifts, technology<br />
strategies and other variables will all impact<br />
the journey. While there isn’t a ‘typical’ journey,<br />
then, there are generally four phases involved:<br />
the incline of improvement, the dip of<br />
determination, the ramp of Return on<br />
Investment and the terrain of transformation.<br />
The majority of organisations begin their risk<br />
journey by focusing on individual and tactical
Risk Management: The Three Stages of Maturity<br />
needs. Defined by the organisation’s business<br />
priorities, these use cases should build a<br />
foundation and begin demonstrating quick<br />
wins. This can be called the incline of<br />
improvement as the organisation moves up the<br />
maturity scale. The business will start seeing<br />
some efficiencies immediately, including a<br />
reduction in the time and effort needed to meet<br />
risk management requirements, improved<br />
reporting around those use cases, some data<br />
sharing and other indicators of improvement.<br />
A key turning point for many organisations is<br />
a stronger commitment from senior leadership<br />
to a more enterprise-level approach. While the<br />
initial implementation may be sponsored by<br />
senior leadership, as organisations progress up<br />
the ‘incline’, at some point the wins start<br />
adding up. Executive management sees the<br />
value in the effort expended and issues a<br />
mandate to break down silos, consolidate<br />
platforms, establish common taxonomy and<br />
assessment approaches and streamline<br />
reporting, etc. This is a big step forward as it<br />
gathers more resources and momentum for the<br />
risk management programme itself.<br />
However, most organisations will witness a<br />
dip as processes take one step backward to<br />
take two steps forward. This ‘dip of<br />
determination’ is a positive step, as it sets up a<br />
stronger programme, but you must keep the<br />
focus. As you do, some processes may need to<br />
change in order to break down organisational<br />
barriers (the step backward) and to move on to<br />
the next phase (the two steps forward) that is<br />
the ramp of Return on Investment.<br />
Inflection point<br />
At this point, organisations are in the managed<br />
state of maturity and really starting to connect<br />
the dots. It’s important to keep momentum<br />
going in order to ascend that ramp.<br />
Somewhere along this ramp there’s an<br />
important inflection point. As the risk<br />
programme matures, the goal is to take the<br />
next step towards addressing new and<br />
changing business activities (ie those growth<br />
activities that are fuelling the business).<br />
Organisations are seeking to reach the ‘terrain<br />
of transformation’ whereby risk management is<br />
part of the culture.<br />
At this phase, the discussion is around<br />
business opportunities and the organisation<br />
reaches the advanced stage of maturity. Once<br />
an organisation reaches this terrain, there must<br />
be constant and continuous measurement of<br />
the risk management programme. The<br />
organisation cannot be lulled into a false sense<br />
of security since the business constantly<br />
changes. The good news is that organisations<br />
attaining this level of maturity generally have a<br />
good sense of how to ride through the waves of<br />
change and adjust themselves accordingly.<br />
It’s also vital that organisations are prepared<br />
for challenges and disruptions. For instance,<br />
anywhere along this journey a ‘paused<br />
programme’ can lead to a downward spiral. This<br />
could be triggered by several different factors.<br />
Many times, the loss of a programme<br />
champion, a lack of resources or a general lack<br />
of progress (programme wins or demonstrated<br />
value) can serve to derail the strategic plan.<br />
Imperative to demonstrate progress<br />
If the programme pauses, it will lose<br />
momentum and could end up dissolving to the<br />
point where it has to be reformulated and reestablished.<br />
The process then starts over as the<br />
organisation goes back through the phases.<br />
Given how important risk management is today,<br />
it’s imperative to show progress and keep the<br />
risk management programme on track.<br />
While the risk management journey is rarely<br />
straightforward, organisations need not travel<br />
alone. There are numerous services and<br />
partners who can assist in carrying a company<br />
throughout the process, helping it to make<br />
faster and more informed decisions about risk.<br />
Steve Schlarman:<br />
GRC Strategist at RSA<br />
“The majority of organisations begin their risk journey by<br />
focusing on individual and tactical needs. Defined by the<br />
organisation’s business priorities, these use cases should<br />
build a foundation and begin demonstrating quick wins”<br />
25<br />
www.risk-uk.com
Power Supply Continuity and Management<br />
Risk UK: A continuous power supply is vital<br />
for many businesses with critical operations.<br />
What can you tell us about the current state<br />
of the industry and why UPS is the best<br />
solution for organisations that would suffer<br />
the most from a major power failure?<br />
Leo Craig: A dependable Uninterruptible Power<br />
Supply (UPS) should be seen as a business’<br />
first and foremost line of defence against<br />
potential power outages and disruptions. IT<br />
downtime is catastrophic, not just in terms of<br />
financial losses or drops in productivity, but<br />
also in terms of reputational damage. With a<br />
reliable UPS protecting your critical power<br />
supply, you have that ultimate insurance policy<br />
bridging the gap until your back-up generators<br />
kick-in or letting your computer systems safely<br />
shut down until the power’s back on.<br />
Risk UK: Which business sectors do you<br />
think find a UPS system to be most valuable<br />
and why?<br />
Leo Craig: UPS units are obviously essential in<br />
any Data Centre environment, whether that’s in<br />
the banking or insurance industries, telecoms<br />
and IT or retail. It’s similarly important in<br />
manufacturing, too, where one unplanned<br />
incidence of downtime can cost an average of<br />
£1.6 million in lost productivity.<br />
It’s not just in sectors that prioritise profits<br />
and the interests of shareholders where a UPS<br />
can prove invaluable. It’s not an exaggeration to<br />
suggest that a UPS can sometimes be the<br />
difference between life and death. Hospital<br />
operating theatres and A&E Departments, the<br />
Emergency Services, roads, railways, docks and<br />
airports – all of this critical infrastructure<br />
demands the clean and consistent power<br />
supply that a UPS can provide.<br />
Risk UK: Do you feel that UPS will innovate<br />
or expand in any new or existing sectors in<br />
the near future?<br />
Leo Craig: It’s not so much a case of innovating<br />
or expanding into other sectors. These days,<br />
virtually every industry relies on electricity and<br />
IT in some form or another, so a UPS system is<br />
a valuable safeguard to protect against any<br />
unexpected outages. For example, we’ve<br />
recently secured a number of clients in the<br />
sports stadiums and facilities sectors.<br />
Given the continued growth and popularity of<br />
connected devices, smart industry and the<br />
Internet of Things, our personal and<br />
professional lives are only going to become<br />
more increasingly interconnected and<br />
dependent on a robust and consistent power<br />
supply. That being so, the demand for UPS<br />
protection is only likely to burgeon.<br />
Fault Intolerance:<br />
Future Directions for UPS<br />
Uninterruptible Power Supply systems are typically used to<br />
protect hardware such as computers, telecoms systems or<br />
other electrical equipment where an unexpected power<br />
disruption could cause injuries, fatalities, serious business<br />
disruption or data loss. Risk UK interviews Leo Craig, general<br />
manager at Riello UPS, about future developments in this area<br />
Risk UK: What are the key issues to<br />
remember around ownership of a UPS system<br />
and how can firms avoid potential failures?<br />
Leo Craig: While a UPS is an essential piece of<br />
power protection equipment for businesses of<br />
all shapes and sizes, it’s by no means perfect.<br />
Indeed, no safeguard can ever be 100%<br />
infallible. A UPS unit is a complex machine and,<br />
over time, parts will fail or components such as<br />
batteries or fans will need replacing.<br />
Once a UPS has been installed, it’s the<br />
ongoing monitoring, maintenance and servicing<br />
that keeps it operating at peak performance. A<br />
well-maintained UPS obviously helps to<br />
minimise downtime and promote uptime, which<br />
is the ultimate goal of the host company.<br />
Risk UK: What are the biggest obstructions<br />
to UPS maintenance?<br />
Leo Craig: More than two-thirds of downtime<br />
incidents are actually thought to be preventable<br />
in the first place, with poor maintenance<br />
highlighted as one of the key culprits. Basic<br />
human error is the most common cause. At the<br />
Leo Craig:<br />
General Manager at Riello UPS<br />
27<br />
www.risk-uk.com
Power Supply Continuity and Management<br />
simplest level, ensuring labels are clear and<br />
that switching procedure documentation is<br />
easy to understand can avert possible disaster.<br />
Incorporating castell interlocks into the initial<br />
system design will help to ensure that switches<br />
are thrown in a controlled and safe fashion. In<br />
the most critical environments, a pilot/co-pilot<br />
arrangement (whereby two engineers both<br />
check a procedure before ever carrying out the<br />
action) can reduce the risk of human failure.<br />
The best way to eliminate such a threat is by<br />
making sure you work alongside a dependable<br />
UPS maintenance supplier that only uses fullytrained<br />
and competent field engineers.<br />
Risk UK: What should a business look for in<br />
a UPS maintenance package and what are the<br />
most important issues to bear in mind here?<br />
Leo Craig: Sadly, not all UPS maintenance<br />
agreements are the same. Too many contracts<br />
are full of big promises that, in reality, don’t live<br />
up to expectations. It’s crucial that you clarify<br />
several key issues before signing up.<br />
The first point to cover is emergency<br />
response times – how quickly will you receive<br />
help if disaster strikes? Options tend to range<br />
from 8 or 12 working hours down to four clock<br />
hours. Just as importantly, find out exactly what<br />
that ‘response’ is. Is it an automated message,<br />
a phone call from tech support or a certified<br />
UPS engineer fixing the problem on site?<br />
Availability of replacement parts is also<br />
something to consider. Ask whether your<br />
supplier stores spares in several different<br />
locations such that they can be with you as<br />
quickly as possible. Even better still, do they<br />
provide ‘crash kits’ of the most common spare<br />
parts that you can keep at your location ready<br />
for use in case of an emergency scenario?<br />
Finally, you need to be sure that the person<br />
you’re entrusting to service your UPS unit<br />
knows exactly what they’re doing. Field<br />
engineers should successfully pass a<br />
challenging Certified Engineer training<br />
programme in order to prove their competence.<br />
Risk UK: How about energy wastage through<br />
UPS? Is this a problem and is there a way in<br />
which wastage can be reduced to lower<br />
carbon emissions and cut back on cost?<br />
Leo Craig: The rise in popularity of modular<br />
UPS systems is helping to improve energy<br />
efficiency. Moving away from larger static UPS<br />
to a more modular approach means that loads<br />
can be configured more closely to the business’<br />
actual power requirements, in turn ensuring<br />
there’s less wasted capacity without<br />
compromising on performance or redundancy. If<br />
and when the client needs to scale-up, they can<br />
simply ‘Pay as you Grow’ by adding in extra<br />
modules. Compact modular UPS solutions also<br />
produce far less heat, thereby reducing the<br />
reliance on energy-intensive cooling.<br />
We recently worked on a major Data Centre<br />
upgrade that saw several larger static UPS<br />
replaced with more modern modular units. The<br />
client benefited from a 72% reduction in annual<br />
CO 2 emissions and saved more than £335,000<br />
per annum on its UPS and air conditioning<br />
costs. This is conclusive proof that there are<br />
significant efficiency savings to be made.<br />
Risk UK: Are there any other applications for<br />
UPS that haven’t yet been widely adopted?<br />
Leo Craig: Although it will need something of a<br />
shift in mindset across our industry, there’s<br />
definitely merit in embracing the move towards<br />
demand side response by using the untapped<br />
potential of UPS batteries to store electricity<br />
and feed it into the National Grid.<br />
The move to Lithium-Ion batteries makes this<br />
a real possibility and offers obvious ‘wins’ for<br />
both sides. With demands for electricity only<br />
ever going to increase, energy harnessed from<br />
UPS units could become a valuable additional<br />
source of renewable power to add to the<br />
nation’s energy mix. From the host<br />
organisation’s perspective, it’ll help reduce<br />
their environmental footprint as well as<br />
providing an extra revenue stream.<br />
At present, mission-critical businesses tend<br />
to be risk-averse. UPS resilience is by far and<br />
away their foremost priority. Even something<br />
seemingly straightforward such as harnessing<br />
power from back-up generators hasn’t gained<br />
much traction yet, so asking these businesses<br />
to go beyond that and adopt UPS energy<br />
storage will need a major change in mentality.<br />
It’s up to us as a sector to keep pushing the<br />
environmental and economic benefits.<br />
Risk UK: Where is the industry heading now?<br />
Have there been any recent developments or<br />
technological advances in UPS systems?<br />
Leo Craig: The aforementioned move to<br />
Lithium-Ion batteries has been very positive.<br />
Compared to the more traditional sealed lead<br />
acid (SLA) batteries, they offer several<br />
advantages. Lithium-Ion versions take up half<br />
the space, but provide a much higher power<br />
density. They charge far quicker and can be<br />
recharged many more times than SLA batteries.<br />
Lithium-Ion batteries can operate effectively<br />
at 40 o C, twice the recommendation for SLA<br />
types, which also happens to be closer to the<br />
optimum temperature at which a UPS should<br />
operate. This means there’s less need for costly<br />
air conditioning to keep the unit/batteries cool.<br />
28<br />
www.risk-uk.com
D E S I G N I M A N U F A C T U R E I I N S T A L L<br />
PERIMETER SECURITY<br />
SOLUTIONS<br />
OUR PASSION<br />
IS YOUR SECURITY<br />
High security perimeter and<br />
access solutions, including fence<br />
and gate systems, designed and<br />
built in the UK to answer the needs<br />
of your project, from security<br />
rating of LPS 1175 SR1 to SR5.<br />
Call 0800 408 4749 or visit<br />
www.jacksons-fencing.co.uk/secure
Looking towards the<br />
future roadmap for<br />
private sector security<br />
provision in the UK,<br />
Danny Williams tracks<br />
the move from<br />
traditional security<br />
guarding to the<br />
delivery of a new style<br />
of service that affords<br />
value-driven,<br />
predictive and<br />
intelligent solutions<br />
making use of client<br />
and industry data<br />
while at the same time<br />
encompassing open<br />
source intelligence<br />
Danny Williams:<br />
Managing Director (North,<br />
Midlands and South West) at<br />
Securitas UK<br />
Time for Transformation<br />
Five years ago, although security was<br />
considered to be a necessary purchase, it’s<br />
fair to suggest that many clients had<br />
limited visibility or clarity as to why security<br />
services were required or how they could<br />
proactively protect their assets and people. In<br />
the intervening period, times have most<br />
certainly changed. Clients are now far more<br />
aware of the importance of security and how<br />
effective risk management strategies can serve<br />
to protect their assets, people and property.<br />
In today’s world, the industry is moving away<br />
from the traditional security guarding model,<br />
whereby a physical presence used to be a<br />
standalone feature, and more towards<br />
collaborative partnerships wherein security<br />
providers offer a range of protective services<br />
that realise end-to-end security solutions.<br />
Undoubtedly, the security of today – and,<br />
indeed, the future – will rely heavily on a<br />
combination of people, technology and<br />
knowledge working in unison to ensure that<br />
clients receive value-driven and predictive total<br />
security solutions.<br />
People will continue to play a pivotal role in<br />
security, of course. Given their local knowledge,<br />
experience and personal judgement, security<br />
officers will always be at the very heart of<br />
service delivery and best placed to develop<br />
collaborative relationships and understand<br />
local client needs. As is the case across many<br />
industries, though, the advent of new<br />
technology and digital innovation is certainly<br />
redefining the role of the security officer. It’s a<br />
change pattern that the industry simply must<br />
embrace with open arms.<br />
With increasingly innovative and advanced<br />
technology solutions, one might expect the role<br />
of the security officer to be in some way<br />
diminished going forward. However, the reverse<br />
is true. Innovation and technology is actually<br />
enhancing the value of security officers on the<br />
ground. Clients now expect better qualified and<br />
more highly engaged individuals who possess<br />
core skills and have both the knowledge and<br />
flexibility to deliver the important personal<br />
element of a total security solution.<br />
As the number of tasks an officer is expected<br />
to perform continues to multiply, and clients’<br />
expectations increase in unison, the role of an<br />
officer provides enormous opportunities for<br />
personal growth and development.<br />
From reactive to predictive<br />
If the industry is to make a successful transition<br />
from reactive to predictive security, we must<br />
harness Big Data to provide intelligent security<br />
solutions. Tailored security solutions are<br />
already being devised using detailed databased<br />
risk analyses filtered to specific levels,<br />
and by a variety of parameters, including<br />
geographical areas, site and even type and<br />
propensity of criminality. The intelligence<br />
gleaned then allows security providers to<br />
foresee and proactively mitigate risk to<br />
implement preventative measures.<br />
The ability to proactively mitigate risk,<br />
particularly in today’s climate and with an eye<br />
towards the future, will become the modus<br />
operandi of the security industry going forward.<br />
Proactive data management and the analysis of<br />
real-time and historical data allows us to review<br />
security solutions implemented on a site and<br />
consider: ‘Is the solution still appropriate and is<br />
it fit for purpose?’<br />
For example, does a location need on-site<br />
officers present at all times or would a flexible<br />
allocation of resource to risk in the form of<br />
mobile patrols actually present a more efficient<br />
and appropriate solution? These are questions<br />
that detailed data analysis coupled with<br />
thorough risk assessments can answer.<br />
Security providers boasting an Operations<br />
Centre capability are able to share real-time<br />
information with security officers via a number<br />
of mobile devices, among them smart phones<br />
and PDAs. As necessary, operators liaise with<br />
officers to guide their actions on site or send<br />
out a mobile patrol vehicle if required.<br />
The connection between the Operations<br />
Centre staff and the officer(s) on site helps to<br />
reduce false alarms and ensures that valuable<br />
resources are allocated to those situations<br />
where they’re most needed.<br />
Security in a digital age<br />
Technology is making a breakthrough impact on<br />
the industry, with the onset of virtual reality<br />
training, augmented reality patrol systems and<br />
autonomous robots all now entering the<br />
security space as support tools for the security<br />
officer. Investment in these groundbreaking<br />
technologies is essential and must continue in<br />
order to allow security providers to build those<br />
aforementioned value-driven and predictive<br />
total security solutions for their clients.<br />
In addition, the next generation of monitoring<br />
hardware is evolving. We’re now witnessing a<br />
move away from passive CCTV cameras to a<br />
combination of smart cameras, various types of<br />
sensor and analysis software. These solutions<br />
will not only record and detect incidents, but<br />
30<br />
www.risk-uk.com
Security Management: Transitioning to Predictive Solutions<br />
also analyse, draw conclusions and suggest<br />
appropriate actions.<br />
A much-publicised development is the use of<br />
drone technology. The option to deploy drones<br />
in support of officers is a further example of<br />
people and technology working in unison. One<br />
of the benefits of drones is their ability to scan<br />
and patrol far-reaching areas not usually<br />
accessible to humans.<br />
While this presents an obvious positive,<br />
there’s also an obverse consideration for clients<br />
working in sensitive environments who need to<br />
keep their sites secure from the general public.<br />
However, technology now allows for anti-drone<br />
solutions to combat this risk.<br />
Trusted advisor<br />
As the digital transformation of the industry<br />
continues to gather momentum, we will<br />
increasingly see improvements in efficiencies,<br />
lower costs for customers and an increase in<br />
the safety of security officers. However, it’s also<br />
important to appreciate that the move towards<br />
technology-based security management<br />
solutions may seem intimidating for clients,<br />
and particularly so those who are used to a<br />
physical presence alone.<br />
It’s here that a security provider should<br />
establish itself as a trusted advisor in order to<br />
help the client feel comfortable in making any<br />
transition. The rise in the adoption of mobile,<br />
remote and electronic security solutions over<br />
recent years is a direct reflection of the<br />
changing face of security and demonstrates a<br />
move away from purely on-site or security<br />
guarding solutions.<br />
While innovation and technology are creating<br />
positive changes in this era of digital<br />
transformation, we must also remember that<br />
there’s a flip-side to all of this as more and<br />
more people have access to information and<br />
data widely available through the Internet and<br />
social media channels. A much greater focus on<br />
these platforms is going to be necessary in<br />
order to combat potential security threats.<br />
Law enforcement agencies understand that<br />
intelligence can be gleaned through open<br />
source investigation and this is something that<br />
security providers are now starting to offer their<br />
clients. In the first instance, open source<br />
investigation can begin to combat the insider<br />
threat, providing an enhanced level of vetting<br />
for particular roles that have a heightened<br />
requirement for discretion.<br />
Add to this the ability to offer enhanced<br />
social media screening through the right<br />
monitoring software and you’re then in a<br />
position to mitigate any potential risk at the<br />
very outset.<br />
In countries outside the UK, the role of the<br />
security officer is seen as a career pathway. It’s<br />
a respected profession with long-term career<br />
prospects. Here in the UK, we still have some<br />
work to do. With a greater focus on security as<br />
a specialisation, we must strive to improve the<br />
perception of the security officer’s role.<br />
When you compare security to other<br />
industries in the UK, there’s a misconception<br />
that the industry is unattractive and<br />
unrewarding, but this is changing. Technology<br />
and innovation have paved the way for IT-based<br />
security solutions, and it’s this innovation that<br />
will undoubtedly appeal to the next generation<br />
of security professionals.<br />
Indeed, young people now embarking on a<br />
career in security expect technology and<br />
innovation to play just as important a role in<br />
their working life as it does in their personal<br />
life. The security industry needs to challenge<br />
itself. It must evolve to attract and retain the<br />
best talent. There’s no denying that people<br />
remain at the heart of security, and rightly so,<br />
but it’s important to look beyond traditional<br />
ways of working, embrace change and build<br />
long-term sustainable partnerships with clients.<br />
Security is developing. Technologies and<br />
client needs are changing. Our industry cannot<br />
solve the challenges of an evolving landscape<br />
with traditional approaches from yesterday.<br />
“The connection between the Operations Centre staff and<br />
the officer(s) on site helps to reduce false alarms and<br />
ensures that valuable resources are allocated to those<br />
situations where they’re most needed”<br />
31<br />
www.risk-uk.com
Although HD video<br />
surveillance has<br />
become the norm<br />
when configuring and<br />
implementing a<br />
security strategy, less<br />
attention has been<br />
given to the benefits<br />
of audio. Malcolm<br />
Crummey explains<br />
why it’s time to take<br />
audio seriously and<br />
evaluates how it can<br />
help to prevent<br />
security problems<br />
before they start<br />
The Voice of Reason<br />
All of us have become used to living in a<br />
‘surveillance society’. CCTV cameras are<br />
now part of everyday life, with the average<br />
Londoner caught on camera over 300 times<br />
each day. However, while the visual element of<br />
a security strategy is very much a ‘given’,<br />
what’s far less prevalent is the use of voice<br />
address technology. It’s high time for the<br />
benefits of using audio to be reappraised.<br />
In the majority of cases, CCTV is<br />
retrospectively used to analyse where a crime<br />
took place, establish the events that occurred<br />
and, if necessary, provide prosecution evidence.<br />
A subject of some debate is whether CCTV<br />
alone actually acts as a deterrent or is simply<br />
something of an inconvenience for those with<br />
criminal intent in mind.<br />
Audio technology has some significant<br />
advantages in this regard. In the event that an<br />
intruder is identified, an operative at a Remote<br />
Monitoring Centre (RMC) can issue a verbal<br />
warning to that intruder to cease what they’re<br />
doing and disperse – an approach that has<br />
been proven to prevent the majority of<br />
incidents from going any further. If this doesn’t<br />
work then further action can be initiated, such<br />
as deploying security officers or summoning<br />
the police service to the scene.<br />
Furthermore, not all remote monitoring needs<br />
to be carried out on a live basis. For those<br />
customers looking for constant round-the-clock<br />
surveillance of their premises and operations,<br />
alert-based remote monitoring is the perfect<br />
solution. In fact, it’s most effective when linked<br />
to a range of other technology such as intruder<br />
alarms, access control and fire detection<br />
systems. RMC operators can pick up alerts,<br />
which are then visually confirmed, meaning<br />
that the response from the Emergency Services<br />
is taken to an enhanced level.<br />
Sound move<br />
Although video surveillance is the dominant<br />
technology in a security system, the time has<br />
surely now come to recognise audio monitoring<br />
as an equally critical component. Indeed, it<br />
should be part of any remote monitoring<br />
facility’s range of services.<br />
There have been massive developments in<br />
terms of security technology in recent years<br />
thanks to the use of Internet Protocol (IP)-<br />
based systems, and audio is no exception. IP is<br />
a communications mechanism that allows every<br />
computer or other device on a network to have<br />
an individual address, affording the ability to<br />
control and monitor them from anywhere on a<br />
network. What’s more, they can even be<br />
configured and controlled from an off-site<br />
location. That’s part of the reason why a<br />
growing number of organisations are choosing<br />
to use third party RMCs as a way of maximising<br />
the efficiency of their operations.<br />
Thanks to IP, it’s now possible to control a<br />
wide variety of building services over one<br />
infrastructure. From logistical and capital<br />
expenditure points of view, there’s the potential<br />
for substantial savings on cabling installation<br />
costs in that an existing network can be used<br />
instead of installing totally new cables. This is<br />
something that can reduce installation time.<br />
That’s important, as security technology has<br />
traditionally been viewed by corporate<br />
management as a ‘necessary evil’ – something<br />
that doesn’t typically create or generate<br />
revenue for the business in which it’s deployed.<br />
IP-based systems can reduce overheads.<br />
Take, for example, barrier and access control.<br />
Shopping Centres often have one dedicated<br />
person on site to provide access for deliveries,<br />
etc. While this is obviously important from a<br />
security point of view, there may well be long<br />
periods of time where that operative is doing<br />
very little. By using an IP-based video and voice<br />
system, the RMC is able to carry out this<br />
function as part of a broader range of activities.<br />
32<br />
www.risk-uk.com
CCTV and Audio Monitoring<br />
Features and benefits<br />
As part of an IT network infrastructure, IPbased<br />
audio technology is compatible with a<br />
wide range of other security devices, including<br />
cameras, recorders and software. This helps to<br />
ensure full integration.<br />
IP-enabled speakers provide clear, long range<br />
speech for remote speaking in surveillance<br />
applications and, as well as enabling an<br />
operator to remotely address people and deter<br />
unwanted activity, they can also play a prerecorded<br />
message when it’s manually or<br />
automatically activated in response to a<br />
specific event. Alarms can also be triggered<br />
based on audio sounds above a specified<br />
decibel level.<br />
What’s more, IP audio provides real-time<br />
confirmation of an intrusion. That being so,<br />
organisations then have an effective way of<br />
keeping people, property and assets safe, while<br />
also avoiding false alarms and the unnecessary<br />
deployment of personnel.<br />
As each speaker has its own IP address, it<br />
can be isolated. When it’s only necessary to<br />
communicate with a person – or persons – in a<br />
specific area, this can be achieved without<br />
using the entire system. This type of flexibility<br />
serves the security needs of a wide range of<br />
locations including educational establishments,<br />
car parks, building sites, hospitals, car<br />
dealerships, industrial estates, warehouses and<br />
utilities sites, etc.<br />
In addition, IP audio harbours less obvious<br />
benefits in terms of ensuring adequate<br />
standards of Health and Safety. For instance, in<br />
high density locations such as Shopping<br />
Centres and sports stadiums it can be used to<br />
make announcements that avoid the build-up of<br />
dangerous ‘bottlenecks’.<br />
Power over Ethernet<br />
Back in 2003, the IEEE 802.3af standard – more<br />
commonly known to industry professionals as<br />
Power over Ethernet (PoE) – was ratified and<br />
allows surveillance cameras, audio equipment,<br />
access control technology and other embedded<br />
devices to receive power as well as data over<br />
existing cabling.<br />
The original PoE standard was limited to<br />
provide up to 15.4 W of DC power per device,<br />
but in 2009 the higher power IEEE 802.3at<br />
standard – or PoE+ – came into play, enhancing<br />
provision up to 25.5 W of power. Standardscompliant<br />
PoE applications are intended to<br />
operate over twisted pair copper cables from<br />
Category 5 upwards, with a channel distance of<br />
up to 100 metres.<br />
PoE has been an enabler of IP-based<br />
security and the benefits extend to audio. It<br />
eliminates the need for separate data and<br />
power cables, while also simplifying the<br />
installation and maintenance of networked<br />
devices. One of the biggest benefits of PoE is<br />
its ability to simplify the management of the<br />
network. Installation becomes less complex<br />
and the process is also quicker due to the need<br />
for fewer cables and power sockets.<br />
In addition, global organisations can also<br />
deploy PoE everywhere, without concern for<br />
any local variances in AC power standards,<br />
outlets or plugs.<br />
Sound advice<br />
Given its clear advantages, the use of IP-based<br />
audio technology is set to rise in the coming<br />
years. Some systems also have the capability to<br />
operate in a two-way capacity, meaning that<br />
there’s the potential to ‘listen in’ and record<br />
conversations. Those thinking of using audio<br />
for this purpose in a business application need<br />
to be careful, though, as they could be entering<br />
an ethical and legal minefield by doing so.<br />
The Information Commissioner’s Office’s<br />
(ICO) CCTV Code of Practice states that sound<br />
recording is unnecessary and in most cases<br />
intrusive, and could undermine public support<br />
for CCTV. In addition, if used inappropriately it<br />
could be in violation of the ‘Right to Privacy’<br />
section of the Human Rights Act 1998.<br />
Violating privacy laws is considered a serious<br />
crime and the ICO advises that organisations<br />
should choose a system without this facility if<br />
possible. If a system is supplied equipped with<br />
a sound recording facility, then this should be<br />
turned off or otherwise disabled.<br />
Power of audio<br />
Proven to be highly effective at deterring those<br />
individuals about to commit acts of crime, IPbased<br />
audio systems should be considered an<br />
essential part of any remotely monitored CCTV<br />
system. To be frank, more organisations need to<br />
start tapping into the power of audio in order to<br />
meet their security needs.<br />
‘Prevention is better than cure’ is what the<br />
old adage states, so the ability to issue a<br />
warning and stop an incident before it starts<br />
will always be preferable to simply reviewing<br />
footage on a retrospective basis, locating the<br />
culprits and spending precious time and money<br />
dealing with the aftermath.<br />
Malcolm Crummey:<br />
Sales Manager (UK and<br />
Ireland) at TOA Corporation UK<br />
“Although video surveillance is the dominant technology in<br />
a security system, the time has come to recognise audio<br />
monitoring as an equally critical component. Indeed, it<br />
should be part of any remote monitoring facility’s services”<br />
33<br />
www.risk-uk.com
Meet The<br />
Security Company<br />
This is the tenth<br />
instalment in a<br />
monthly series of<br />
articles for the readers<br />
of Risk UK where we<br />
shine the spotlight on<br />
NSI-approved<br />
businesses for the<br />
benefit of risk and<br />
security managers<br />
who purchase security<br />
guarding as well as<br />
systems-focused<br />
solutions. Answering<br />
our key questions on<br />
this occasion is Laurie<br />
Barton Wright, brand<br />
and development<br />
director at the<br />
Westgrove Group<br />
Risk UK: Can you briefly describe your<br />
business’ activities and what you consider to<br />
be your USP as an organisation?<br />
Laurie Barton Wright: Westgrove Group is a<br />
soft services provider specialising in high<br />
footfall destinations such as Shopping Centres<br />
and public realm spaces. We provide security<br />
and cleaning solutions plus customer services<br />
ambassadors on over 70 sites across the UK.<br />
We have a ‘people-centric’ approach to our<br />
business and we believe that this sets us apart<br />
from other providers. We have a number of<br />
USPs: we form partnerships with a long-term<br />
vision, have a willingness to invest in people<br />
through colleague engagement, show flexibility<br />
in problem-solving and provide the drive<br />
needed to support on-site management teams.<br />
Westgrove is a true retail property service<br />
provider. Our portfolio extends to commercial<br />
buildings, but we excel in retail locations where<br />
we can help to deliver a face-to-face guest<br />
experience and add to the customer journey.<br />
Over 90% of our business is within the retail<br />
sector and we plan to increase this even further<br />
through the introduction of ‘Synergy by<br />
Westgrove’ which is our bespoke service<br />
provision for Shopping Centres and retail parks.<br />
About the National Security Inspectorate<br />
The National Security Inspectorate (NSI) is a wholly-independent, not-forprofit<br />
company limited by guarantee and operates as a UKAS-accredited<br />
certification body specialising in the security and fire safety sectors.<br />
For over 40 years, the NSI has served to protect businesses, homeowners<br />
and the general public alike, raising standards by providing robust and high<br />
quality audits of both security and fire safety service providers.<br />
Westgrove Group’s expertise and culture<br />
stems from an independent business which has<br />
grown organically over the past 18 years. The<br />
company boasts a senior management team<br />
offering a wealth of direct retail experience. We<br />
have a dynamic DNA within the business that’s<br />
common to our whole organisation and affords<br />
us a true understanding of our Shopping Centre<br />
management teams.<br />
Risk UK: What do your clients value most<br />
about the services you deliver?<br />
Laurie Barton Wright: We refer to our clients<br />
as partners and our staff as colleagues. This<br />
sets us apart from other providers and is<br />
something that we feel supports our<br />
partnership approach and colleague-centred<br />
DNA. That helps to cement long-term working<br />
relationships as we truly add value to our<br />
partners’ businesses, whether that be through<br />
our innovative ideas or by upskilling on-site<br />
teams to be a greater value asset.<br />
We prioritise our investment in training and<br />
development to ensure that all colleagues are<br />
given the same opportunities to enhance their<br />
knowledge and skills. This extends even further<br />
to customer service training and targeted<br />
service excellence-focused initiatives.<br />
Risk UK: How do you feel accreditations have<br />
assisted your company?<br />
Laurie Barton Wright: Accreditations are very<br />
important to us, and particularly so when<br />
tendering for new business. We can show that<br />
we have the necessary accreditations in place<br />
to afford potential partners confidence.<br />
Accreditations are a benchmark to show that<br />
we’re operating at a defined level of excellence<br />
within our industry. They also assist us<br />
internally by helping to support and develop<br />
processes and procedures which add structure<br />
and robustness to our business.<br />
Risk UK: Specifically, what value does ACS<br />
registration and NSI Guarding Gold approval<br />
bring to your business and its clients?<br />
Laurie Barton Wright: Approved Contractor<br />
Scheme (ACS) registration and NSI Guarding<br />
Gold approval gives us confidence that we’re<br />
operating at a level of excellence which is<br />
recognised externally. The ACS registration and<br />
NSI approval are not always requested by<br />
purchasing customers, but are recognised by<br />
many partners and help us to demonstrate that<br />
34<br />
www.risk-uk.com
Meet The Security Company: Westgrove Group<br />
In association with the<br />
we take our business, its performance and<br />
integrity very seriously indeed.<br />
It’s important for us to be measured and to<br />
think about how we’re operating and how we<br />
can make continuous improvements. We’re an<br />
independent business, but we offer the same<br />
service standards as the major plcs. This is a<br />
real USP for us in the marketplace.<br />
Risk UK: In practice, what are the main<br />
differences between ACS registration and NSI<br />
Guarding Gold approval?<br />
Laurie Barton Wright: The NSI was the first<br />
security industry assessing body that offered<br />
access to the ACS via the Passport route. The<br />
Passport route is open to NSI approved<br />
companies providing services for security<br />
guarding, CCTV, door supervision, close<br />
protection, key holding and Cash-in-Transit.<br />
The Passport route offers qualifying<br />
companies an additional option for access to<br />
the ACS. NSI approved companies achieving<br />
this must meet an NSI Passport Specification,<br />
but will not be required to pass through<br />
separate ACS assessments.<br />
Risk UK: How do you think technology has<br />
changed the industry over the last couple of<br />
years and what do you feel will be the<br />
direction of travel in the future?<br />
Laurie Barton Wright: We use a good deal of<br />
cloud-based technology and this has really<br />
helped us to deliver a better service for our<br />
partners. There are a number of key systems<br />
which we’ve been able to develop and roll out<br />
and which show real benefits for our partners.<br />
Accuracy and collection of data is vital both<br />
in security and cleaning to demonstrate a<br />
number of outcomes and support Key<br />
Performance Indicators around productivity of<br />
the team on site, Health and Safety, customer<br />
feedback and so much more.<br />
All of our systems are cloud-based and<br />
accessible to our partners. This promotes a<br />
greater sense of trust and transparency. The<br />
fact that we’re ‘paperless’ aligns with partners’<br />
Corporate Social Responsibility aspirations.<br />
Going forward, we’re keen to develop our<br />
systems further. We know our partners see the<br />
benefits and we’re continually trying to develop<br />
them further to enhance reporting capabilities<br />
and integration with their own systems on site.<br />
Risk UK: When it comes to negotiating<br />
contracts and responding to tender requests,<br />
what aspects are of most value to customers<br />
and how are these changing?<br />
Laurie Barton Wright: Partners are keen to see<br />
an innovative approach. Of course, cost is<br />
always a factor, but it’s not always the<br />
overriding one. Partners are keen to see a new<br />
way of thinking and innovative solutions.<br />
There’s always the potential for many<br />
contracts to be left to almost ‘stagnate’ which is<br />
why we continue to strategically revisit our<br />
contracts on a regular basis post-mobilisation.<br />
Budgets are always a consideration and,<br />
again, flexibility of approach showing long-term<br />
gain for our partners is the desired route.<br />
Risk UK: How has Government legislation (eg<br />
the National Minimum Wage, the National<br />
Living Wage and holiday pay) affected your<br />
business? Do you believe such legislation is<br />
a good thing?<br />
Laurie Barton Wright: Being a solutions<br />
provider means that we can only recommend<br />
pay rates. Having the National Living Wage in<br />
place is helpful to ensure a consistent level of<br />
approach. It also gives us a better ability to<br />
look at costs for our partners going forward so<br />
that there are no surprises.<br />
We do try and encourage pay rates to go<br />
above the National Living Wage or, in some<br />
cases, consider the same pay rate for cleaning<br />
and security.<br />
On many of our sites we provide a ‘dual’<br />
service and we often ‘de-badge’ our colleagues<br />
from the traditional security/cleaning roles,<br />
instead moving towards a customer service<br />
ambassador-focused structure.<br />
We firmly believe that our internal reward<br />
and recognition scheme and training and<br />
development all help to benefit colleagues.<br />
Importantly, we also factor in the<br />
Apprenticeship Levy at 0.5% of all labour costs<br />
such that partner organisations can take<br />
advantage of this funding stream.<br />
Risk UK: What are the most important<br />
attributes you look for in your security<br />
officers and staff members in general?<br />
Laurie Barton Wright: The answer to this<br />
question differs from site to site depending on<br />
our partners’ needs. Outside of the normal<br />
vetting requirements, we also place a lot of<br />
importance on face-to-face interviews.<br />
As stated, our contracts are mainly within the<br />
retail/property sector so our colleagues are<br />
very ‘front-facing’. This requires them to be<br />
open to the idea of customer service and ‘going<br />
the extra mile’ to support our partners’ own<br />
business objectives.<br />
A willingness to learn and engage is vital. We<br />
have training and development for all levels,<br />
right up from basic job training through to<br />
management training plus developmental<br />
instruction for dementia and autism awareness.<br />
Name<br />
Laurie Barton Wright<br />
Job title<br />
Brand and Development<br />
Director<br />
Time in the security sector<br />
Two years as a contractor and<br />
20 years in property<br />
management (client side)<br />
working for CBRE, Cushman<br />
and Wakefield and Westfield<br />
Location of the business<br />
Warrington, Cheshire<br />
Areas of expertise<br />
Security, cleaning and<br />
customer service<br />
ambassadors for property<br />
partners including retail<br />
(Shopping Centres/retail<br />
parks) and mixed use<br />
destinations<br />
Accreditations<br />
NSI Guarding Gold, FM Gold,<br />
Health and Safety Gold and<br />
EMS Gold, SIA ACS,<br />
SafeContractor, Contractor<br />
Plus, Member of the British<br />
Safety Council, Member of<br />
the British Council of<br />
Shopping Centres, ISO 14001,<br />
ISO 9001 and OHSAS 18001<br />
Laurie Barton Wright Dip SCM:<br />
Brand and Development<br />
Director at Westgrove Group<br />
35<br />
www.risk-uk.com
BENCHMARK<br />
Smart Solutions<br />
BENCHMARK<br />
Innovative and smart solutions can add value and benefits to<br />
modern systems for customers. With the technological landscape<br />
rapidly evolving, the Benchmark Smart Solutions project assesses<br />
the potential on offer from system integration, advanced<br />
connectivity and intelligent technology. Bringing together field trials<br />
and assessments, proof of concept and real-world experience of<br />
implementing smart solutions, it represents an essential resource<br />
for all involved in innovative system design.<br />
Launching in 2017, Benchmark Smart Solutions will be the industry’s only real-world resource for<br />
security professionals who are intent on offering added value through the delivery of smarter solutions.<br />
@Benchmark_Smart<br />
Partner Companies<br />
www.benchmarksmart.com
The Security Institute’s View<br />
The basic aim of the Government’s Prevent<br />
strategy is to reduce the risk to the UK and<br />
its interests overseas from terrorism such<br />
that citizens can go about their daily lives freely<br />
and with confidence. According to the Home<br />
Office’s 2011 policy paper, the key objectives of<br />
Prevent are to respond to the ideological<br />
challenge of terrorism and the threat we face<br />
from those who promote it, prevent people<br />
from being drawn into terrorism and ensure<br />
that they’re given appropriate advice and<br />
support and work with sectors and institutions<br />
where there are risks of radicalisation<br />
demanding to be addressed.<br />
The strategy has evolved to reflect the terror<br />
threat posed to the UK’s national security. The<br />
biggest change came with the passing of the<br />
Counter-Terrorism and Security Act (CTSA) 2015<br />
after the threat level from international<br />
terrorism was raised to ‘Severe’ in 2014 in<br />
response to the increased number of British<br />
nationals travelling to the Middle East in order<br />
to join the ongoing conflicts in Iraq and Syria.<br />
That same year, the Quilliam Foundation<br />
estimated that around 500 foreign terrorist<br />
fighters were British out of approximately 2,600<br />
Western Europeans and 16,000 globally, in turn<br />
raising concerns of battle-hardened extremists<br />
returning to the UK. The main driver for the<br />
CTSA was the prevention of terrorist acts on<br />
British soil perpetrated due to radicalisation.<br />
According to the UK Government, 30% of<br />
convicted terrorists in the UK since 2001 have<br />
attended university or further education, with<br />
examples including Bradford University (three<br />
students were questioned on suspicion of terror<br />
offences in 2006) and Liverpool John Moores<br />
University (two former students have been<br />
killed while fighting for ISIS in Syria, another<br />
has been named as a senior ISIS commander<br />
who left behind a wife and a child to wage Jihad<br />
in the Middle East and a fourth was jailed in the<br />
USA for 40 years for plotting terror attacks<br />
across the globe in 2015).<br />
Further examples are Queen Mary University<br />
in London (a student group called The<br />
Ideological Society was described as being a<br />
front for Hizb ut-Tahrir, the pan-Islamist<br />
movement pressing for restoration of the<br />
caliphate and the introduction of Sharia Law)<br />
and University College London (the Detroit<br />
‘underpants bomber’ of 2009 was allegedly<br />
indoctrinated while studying there).<br />
CTSA 2015 in focus<br />
The CTSA 2015 consists of six main parts and<br />
aims to disrupt the ability of people to travel<br />
abroad to fight in countries like Syria and Iraq,<br />
control their return to the UK, enhance<br />
The Prevent Duty on<br />
Universities: The Right Balance<br />
Prevent is one of the four Ps that make up the pillars of the<br />
UK’s counter-terrorism strategy developed by the Home<br />
Office in early 2003, although it remained secret until 2006.<br />
Its remit was widened in 2011 and it was placed on a<br />
statutory footing in 2015, but how effectively is Prevent<br />
playing out in the education sector? Dr Chaditsa Poulatova<br />
and Hannah Saunders investigate<br />
operational capabilities to monitor and control<br />
the actions of those in the UK who pose a<br />
threat and help to combat the underlying<br />
ideology that supports terrorism.<br />
It enables the seizure of passports and<br />
introduced reforms to the terrorism prevention<br />
and investigation measures which can be<br />
placed on terrorism suspects to restrict their<br />
movements and invoke temporary exclusion<br />
from the UK. This has some far-reaching<br />
implications for UK citizens and visitors.<br />
The core mission of Part V (ie Sections 26 to<br />
41) of the CTSA 2015 is to put Prevent on a<br />
statutory footing, while placing a duty on<br />
“specified authorities” as listed in Schedule 6<br />
of the Act (among them universities) to have<br />
“due regard to the need to prevent people from<br />
being drawn into terrorism”.<br />
Paragraph 9.4 makes Prevent a safeguarding<br />
and student welfare issue “based on the<br />
premise that people being drawn into<br />
radicalisation and recruitment can be identified<br />
and then provided with support”. According to<br />
the Prevent Duty Guidance for Higher Education<br />
Institutions in England and Wales, such<br />
Dr Chaditsa Poulatova MSyI:<br />
Strategic Advisor to the Cyber<br />
Rescue Alliance<br />
37<br />
www.risk-uk.com
The Security Institute’s View<br />
The Security Institute’s View<br />
is compiled and edited by Dr<br />
Alison Wakefield FSyI<br />
(Chairman of The Security<br />
Institute) and Brian Sims BA<br />
(Hons) Hon FSyI (Editor of<br />
Risk UK)<br />
Institutions “are required to provide adequate<br />
training and development for leadership and<br />
staff” to ensure that vulnerability factors are<br />
identified at an early stage and that the<br />
Institution’s Prevent officer, who’s often that<br />
Institution’s safeguarding officer, is informed.<br />
In order to support universities in fulfilling<br />
their Prevent duties, back in 2013 Universities<br />
UK (the representative body for university vicechancellors)<br />
launched the Safe Campus<br />
Communities website in order to facilitate<br />
information sharing on issues such as external<br />
speaker protocols, effective community and<br />
police engagement and inter-faith relations on<br />
campus, in turn enabling the sharing of good<br />
practice. Since 2015, a monitoring framework<br />
has been in place via the UK regions’<br />
appropriate regulatory bodies for higher<br />
education, with the new Office for Students<br />
now fulfilling that role on behalf of English<br />
universities, as set out on its web page entitled<br />
‘Counter-Terrorism: The Prevent Duty’.<br />
Guidance for university governing<br />
bodies/councils to inform their oversight of<br />
senior management in the delivery of the<br />
Prevent requirements, and in accordance with<br />
the Higher Education Code of Governance<br />
which informs the effective governance of<br />
universities, has also been published by the<br />
Leadership Foundation in conjunction with the<br />
Committee of University Chairs.<br />
Challenges of implementation<br />
Re-casting Prevent as “safeguarding” seems to<br />
have allayed some anxieties about the duty, but<br />
the CTSA has not been without controversy.<br />
Frances Webber, vice-chair of the Institute of<br />
Race Relations, stated that it “impinged on<br />
basic freedoms and further alienated the<br />
already under threat Muslim community”, while<br />
Sir Peter Fahy (former chief constable of<br />
Greater Manchester Police) has argued: “The<br />
extension of the Prevent duty to the education<br />
sector was introduced in haste and without the<br />
time for proper training which resulted, in some<br />
cases, in inappropriate referrals.”<br />
The University and College Union has<br />
suggested that Prevent represented a<br />
draconian crackdown on the rights of<br />
academics and students, which would have an<br />
adverse effect on freedom of speech within an<br />
environment where views are routinely<br />
challenged and boundaries tested in the spirit<br />
of academic endeavour. The latter view was<br />
also shared by the Parliamentary Joint<br />
Committee on Human Rights.<br />
It’s inevitable that some terrorists have<br />
attended university: a level of 30% is roughly<br />
what one would expect of a sample of young<br />
people of the right age. The statistic quoted by<br />
the Government fails to distinguish correlation<br />
and causation, however, and in the words of<br />
Lord Andrew Phillips in the House of Lords:<br />
“That seems to me to be an utterly useless<br />
statistic. Were they terrorists before they went<br />
to university? Were they terrorists as a result of<br />
going to university, or were they terrorists as a<br />
result of what happened to them after<br />
university? We have not the slightest idea.”<br />
It’s very difficult to measure the full extent of<br />
the Prevent strategy’s successes and failures.<br />
Out of 7,500 referrals made to the scheme in<br />
2015-2016, no action was taken in 37% of the<br />
cases, while a quarter of individuals referred<br />
were found to be vulnerable, but not at risk of<br />
terrorist involvement. The fact remains that it’s<br />
impossible to know how many people may or<br />
may not have gone on to commit terrorist acts<br />
without coming into contact with Prevent.<br />
Although the core mission of Part V of the<br />
CTSA 2015 is to put Prevent on a statutory<br />
footing, the legislation does so selectively by<br />
way of a basic framework approach.<br />
Universities participate on a voluntary basis<br />
and have no power to refer anyone directly to a<br />
de-radicalisation programme.<br />
There are no legal sanctions under the CTSA<br />
or elsewhere for failures to act upon<br />
information or make a formal Prevent referral,<br />
even when an act of terrorism is committed<br />
which might otherwise have been averted.<br />
Where next for Prevent?<br />
Given the practical challenges underpinning the<br />
Prevent duty in universities, there have been<br />
calls by Parliament’s Joint Committee on Human<br />
Rights, Human Rights organisation Liberty and<br />
the Open Society Justice Initiative for a “full<br />
and transparent review of the application of the<br />
Prevent strategy to the educational setting”.<br />
Certainly, this would give some clarity around<br />
the relevant risks that each university has<br />
faced, the mitigating actions undertaken and<br />
the extent to which the Prevent duty is<br />
effectively integrated into universities’ current<br />
corporate risk assessment strategies.<br />
Hannah Saunders:<br />
Student of Journalism at<br />
Emerson College in Boston,<br />
Massachusetts<br />
“The extension of the Prevent duty to the education sector was<br />
introduced in haste and without the time for proper training which<br />
resulted, in some cases, in inappropriate referrals”<br />
38<br />
www.risk-uk.com
thepaper<br />
Business News for Security Professionals<br />
Pro-Activ Publications is embarking on a revolutionary<br />
launch: a FORTNIGHTLY NEWSPAPER dedicated to the<br />
latest financial and business information for<br />
professionals operating in the security sector<br />
The Paper will bring subscribers (including CEOs,<br />
managing directors and finance directors within the<br />
UK’s major security businesses) all the latest company<br />
and sector financials, details of business re-brands,<br />
market research and trends and M&A activity<br />
FOR FURTHER INFORMATION<br />
ON THE PAPER CONTACT:<br />
Brian Sims BA (Hons) Hon FSyI<br />
(Editor, The Paper and Risk UK)<br />
Telephone: 020 8295 8304<br />
e-mail: brian.sims@risk-uk.com<br />
www.thepaper.uk.com
Accusations and<br />
recriminations<br />
between Britain and<br />
Russia are set to<br />
escalate with the<br />
recent news that<br />
scientists at the<br />
Porton Down military<br />
research facility have<br />
been unable to<br />
establish exactly<br />
where the nerve agent<br />
used to carry out the<br />
attack on former MI6<br />
agent Sergei Skripal<br />
and his daughter Yulia<br />
in Salisbury was<br />
manufactured. Dan<br />
Kaszeta examines the<br />
episode and its<br />
political and security<br />
implications to date<br />
Dan Kaszeta MA:<br />
Founder and Managing Director<br />
of Strongpoint Security<br />
40<br />
www.risk-uk.com<br />
Nerve Agents and Novichoks<br />
The recent Salisbury attack on the Skripals<br />
is, in many ways, part of a broad trend<br />
reaching back decades, but on the other<br />
hand, it could be viewed as a reckless act of<br />
terror due to its prevailing effects on people<br />
and property that were not the evident target.<br />
The revelation that the Salisbury episode was<br />
transacted not just by a nerve agent, but<br />
possibly by a particular nerve agent called a<br />
Novichok, is deemed particularly disturbing.<br />
At the time of writing, it’s theorised that a<br />
nerve agent was applied to the handle on the<br />
door of Sergei Skripal’s car. Nerve agents are a<br />
specific family of chemicals. The term ‘nerve<br />
agent’ has strict definitions in military, scientific<br />
and medical literature. Nerve agents are a<br />
subset of the broader category that we could<br />
call “bad things affecting the nervous system”.<br />
Accepted references define nerve agents as<br />
chemicals that interfere with the normal<br />
operations of the chemicals acetylcholine and<br />
acetylcholinesterase in the human nervous<br />
system. Some sources go as far as to restrict<br />
the definition to those chemicals present in the<br />
organophosphate family. However, there’s a<br />
strong case to be made that chemicals in the<br />
related carbamate family could be considered<br />
nerve agents because their biological action is<br />
similar. All are complex to manufacture and all<br />
are highly dangerous to human beings.<br />
Nerve agents include military chemical<br />
warfare agents and a large range of<br />
insecticides. The better-known military<br />
chemical warfare nerve agents include Tabun,<br />
Sarin, Soman and VX. One should never use the<br />
phrase ‘nerve gas’ here as none of them are<br />
gases in their natural state. Nerve agents are<br />
mostly liquids, while some are even solids.<br />
Many of the insecticides in the nerve agent<br />
category include the now banned Amiton, the<br />
highly restricted Parathion and several others.<br />
Chemical imbalance<br />
Depending on the particular nerve agent and<br />
existing environmental conditions, they can last<br />
in the environment for widely varying lengths of<br />
time. On a warm day, Sarin may only last a few<br />
minutes, whereas VX or one of the pesticides<br />
could last for many months, and particularly so<br />
if soaked into material.<br />
Nerve agents affect the human body by<br />
causing a chemical imbalance called a<br />
cholinergic crisis. They can be inhaled when<br />
you breathe, ingested in food or drink or<br />
absorbed through the skin and eyes. They<br />
usually operate quickly through respiratory and<br />
ocular exposure, with the onset of adverse<br />
effects occurring within a period of a few<br />
seconds to a few minutes depending on dose.<br />
Absorption through the skin is slower (ie<br />
minutes to hours) depending on the dose. The<br />
rate of action for wound exposure is believed to<br />
be intermediate in speed between respiratory<br />
and dermal absorption. Gastrointestinal<br />
absorption isn’t well documented, but is likely<br />
to be fast. It has been theorised that nerve<br />
agents could be engineered to have a delayed<br />
onset of their effects.<br />
The signs and symptoms, and their order of<br />
appearance, vary depending on the route of<br />
exposure. They’re drawn from the Textbook of<br />
Military Medicine volume on chemical warfare<br />
agents. In terms of liquid exposure to skin, the<br />
rate of action is from minutes to hours after<br />
exposure. Mild effects will be muscle twitching<br />
at the site of exposure (fasciculations),<br />
sweating, nausea, vomiting and weakness.<br />
Serious effects would be the mild symptoms<br />
plus difficulty in breathing, generalised muscle<br />
twitching, weakness, paralysis, convulsions and<br />
loss of bladder/bowel control.<br />
Note that miosis (ie ‘pinpointing’ of the eye<br />
pupils) is often a late sign in situations where<br />
the victim is exposed only to liquid.<br />
When it comes to the inhalation of<br />
aerosolised droplets or vapour, the rate of<br />
action is from seconds to minutes after<br />
exposure. Mild effects here will be the<br />
aforementioned miosis, dimness of vision,<br />
headache, runny nose, salivation and a feeling<br />
of tightness in the chest. Serious effects are,<br />
once again, the mild symptoms plus difficulty in<br />
breathing, generalised muscle twitching,<br />
weakness, paralysis, convulsions and loss of<br />
bladder/bowel control.<br />
The phenomenon of ingested nerve agents is<br />
less well-studied, so the exact presentation of<br />
symptoms and the order in which they’re likely<br />
to appear is less certain. Logically,<br />
gastrointestinal effects may present themselves<br />
earlier. The rate of action of nerve agents could<br />
theoretically vary. Some compounds are more<br />
fat soluble than others, and this affects the rate<br />
of absorption through skin.<br />
What are Novichok agents?<br />
Novichok means ‘newcomer’ in Russian. The<br />
Novichok agents were developed by the Soviet<br />
Union in conditions of great secrecy back in the<br />
1980s. For a full background, read the book
In the Spotlight: ASIS International UK Chapter<br />
‘State Secrets’ authored by Vil Mirzayanov, a<br />
defector from Moscow’s chemical warfare<br />
research programme and creator of Novichoks.<br />
The Novichoks were created for several<br />
reasons. First, they would avoid the (then<br />
current) state-of-the-art military chemical<br />
warfare detectors used in the West. Second,<br />
they could be made from precursor chemicals<br />
that were not proscribed or controlled under<br />
the arms control arrangements that were either<br />
in place or under negotiation at the time. It<br />
should be noted that, as Moscow was a party to<br />
the negotiations drawing up lists of specifically<br />
proscribed chemicals, it’s not surprising that<br />
the Novichoks didn’t make these lists.<br />
Third, the agents were more toxic than any of<br />
the nerve agents already in existence, meaning<br />
that a smaller amount of agent could have the<br />
same wide area effects. Fourth, at least one of<br />
the Novichoks was a solid, so it could be<br />
deployed as a dust or a powder. This has<br />
bearings on weapon design, detection and<br />
decontamination. Indeed, a powder would be<br />
absorbed much more slowly in many instances,<br />
which could explain the timeline of the recent<br />
Salisbury case.<br />
Finally, the Novichoks – according to some<br />
scientific literature, at least – have more<br />
potential for causing permanent damage to the<br />
nervous system.<br />
Implications of Salisbury<br />
The implications of the Salisbury attack are<br />
immensely important. There are four aspects of<br />
this attack that are clear to me.<br />
First, nerve agents are, by their very<br />
definition, indiscriminate area weapons rather<br />
than precision weapons. The hazard spreads by<br />
contact. The perpetrators cared not one bit<br />
whether other people were killed or injured in<br />
the attack. It’s akin to burning down an<br />
apartment building to kill one individual.<br />
Second, Novichoks contaminate things. This<br />
leads to extensive property damage of a type<br />
that will not be covered by insurance. It isn’t<br />
just an attack on health. Rather, it’s an area<br />
denial weapon. Third, the injuries produced by<br />
Novichoks may include permanent neurological<br />
damage. It could even be argued that, in this<br />
particular instance, death wasn’t even the<br />
sought after result. Permanent disfigurement is<br />
at least as intimidating as sudden death.<br />
Fourth, as Novichoks are the Intellectual<br />
Property of the Russian State (having been<br />
invented there), if they were used in Salisbury<br />
this means the perpetrators didn’t care about<br />
attribution. In fact, clear attribution to Russia<br />
may be exactly the point of this attack. It’s a<br />
way of saying: “We did it and we don’t care<br />
that you know that we did it.” Putin’s Russia<br />
has had a long history of deliberately provoking<br />
crises in order to suit domestic political goals.<br />
Let’s not forget there was an election on.<br />
Denials and conspiracies<br />
An apocryphal maxim of covert operations is<br />
“admit nothing, deny everything, make counteraccusations.”<br />
It’s clear that the Russian State<br />
takes this expression to heart. If anyone<br />
doubted the existence of Russian ‘troll farms’<br />
and other types of information warfare<br />
apparatus, the speed with which various<br />
conspiracy theories have circulated is evidence.<br />
The full weight of the information operations<br />
establishment seems to be spreading<br />
‘alternative narratives’ to try to explain away<br />
the attempted murders. At the time of writing, I<br />
count at least ten ‘theories’ that point fingers<br />
away from Russia. As is often the case, they’re<br />
generally mutually exclusive from each other,<br />
yet often the same outlets are pushing things<br />
that are exceedingly unlikely to be true and<br />
even contradictory of one another.<br />
It takes an Orwellian degree of doublethink<br />
to believe simultaneously: “There’s no such<br />
thing as a Novichok” and “Someone used a<br />
Novichok as a ‘false flag’ attack”. However,<br />
social media is ablaze with this sort of thing.<br />
For many commentators on the issue, the<br />
existence of such a defiant campaign of denial<br />
and obfuscation represents evidence in itself.<br />
“Nerve agents are, by their very definition, indiscriminate<br />
area weapons rather than precision weapons. It’s akin to<br />
burning down an apartment building to kill one individual”<br />
41<br />
www.risk-uk.com
New Opportunities at FIM Expo 2018<br />
At the end of this<br />
month, the Fire<br />
Industry<br />
Manufacturers Expo is<br />
coming to Ashton Gate<br />
Stadium in Bristol. The<br />
event is organised by<br />
the Fire Industry<br />
Association (FIA) and<br />
helps to build the<br />
bridge between<br />
manufacturers of fire<br />
detection and alarm<br />
products and those in<br />
the services world. Ian<br />
Moore elaborates on<br />
the key detail of the<br />
day for attendees<br />
Ian Moore: CEO of the Fire<br />
Industry Association<br />
For security companies, the Fire Industry<br />
Manufacturers (FIM) Expo is a great place<br />
to meet manufacturers and network with<br />
other service professionals if they’re thinking of<br />
expanding from security service installation and<br />
maintenance into this other somewhat niche,<br />
but still buoyant area of business. It’s a big step<br />
if a company hasn’t yet expanded, but the<br />
Expo’s light and informal atmosphere is<br />
renowned for making those close connections<br />
and business partnerships due to its small size.<br />
Here, instead of wandering aimlessly<br />
between stands for hours, you can easily make<br />
all the connections you need within a relatively<br />
short period of time. A major advantage is that<br />
you can see all the products and glean answers<br />
on how they all work, which is helpful if you’re<br />
unfamiliar with this particular area.<br />
If you’re already operating within fire<br />
detection and alarm services, there’s still plenty<br />
to engage with at the FIM Expo even for a more<br />
seasoned professional. The confirmed<br />
exhibitors will be showcasing a range of<br />
products and, with new ranges being<br />
developed, it’s a good time to find out if there<br />
are any new solutions to be sourced or explore<br />
other manufacturers’ products that you might<br />
not have known much about previously.<br />
For those operating within this specialist<br />
sector, there’s good news in that the market is<br />
continuing to grow. Demand for fire safety<br />
services such as fire detection and alarm<br />
maintenance and installation is ever-present.<br />
The FIA’s Market Conditions Survey, which has<br />
been repeated every six months since 2008,<br />
has shown that, if any industry is relatively<br />
financially fire-proof (if you’ll excuse the pun),<br />
then it’s the fire industry.<br />
Reports spanning the last few years have<br />
continually demonstrated a period of financial<br />
stability and, on the whole, respondents don’t<br />
feel that Brexit is necessarily going to<br />
negatively impact their business (though there<br />
are a few responders to the survey with<br />
understandable concerns at present, such as<br />
the rise in supplier costs).<br />
As such, now might be a good time to start<br />
having those business conversations with a<br />
range of different contacts to look at different<br />
product series and prices. The FIM Expo is a<br />
good opportunity for this. The atmosphere<br />
tends to be relaxed, there’s no pressure and<br />
exhibitors tend to have more time for in-depth<br />
conversations in person than at some of the<br />
larger shows where they simply take your<br />
details down and say they’ll call you back at<br />
some point next week.<br />
If you’re a regular attendee at the FIM Expo,<br />
you’ll know just how valuable those<br />
conversations with others in the business can<br />
be in the real world. It’s a great place to seek<br />
advice and build worthwhile connections with<br />
new people, to meet up or make an<br />
appointment to see a business contact over a<br />
coffee (tea and coffee is provided free of charge<br />
alongside a buffet luncheon).<br />
42<br />
www.risk-uk.com
FIA Technical Briefing: Fire Industry Manufacturers Expo 2018<br />
BS 5839-1: 2017 examined<br />
Alongside the chance to meet with the<br />
exhibitors themselves, there’s the added bonus<br />
of two free seminars at the Expo. Last time out,<br />
the seminars were completely full with standing<br />
room only, so it’s worth arriving early to ensure<br />
you can grab a seat.<br />
The first seminar in 2018, running under the<br />
title ‘BS 5839-1: 2017 – What has changed?’ is<br />
presented by the FIA’s technical manager Will<br />
Lloyd, who also helped to write the materials<br />
for the FIA’s new qualifications in fire detection<br />
and alarms. Will is very well known for his<br />
encyclopaedic knowledge of British Standards,<br />
and can provide expert advice on a wide range<br />
of fire detection and alarm-centric issues.<br />
This seminar covers the latest major revision<br />
of British Standard BS 5839-1, and the<br />
differences between this version and the old<br />
variant. Despite it being 2018, there may still be<br />
some aspects of the 2017 revision of this<br />
document of which you (or indeed your<br />
colleagues) may be unaware.<br />
The update seminar covers a long list of<br />
areas including multi-sensor detectors in<br />
escape routes, L3 and L2 systems, the use of<br />
manual Call Point covers, places of ‘ultimate<br />
safety’, manual Call Point locations,<br />
communications with the Fire and Rescue<br />
Service, staff alarms, video fire detection, types<br />
of fire detectors and their selection, the spacing<br />
and siting of automatic fire detectors, detector<br />
spacing and siting on honeycomb ceilings, the<br />
siting of optical beam smoke detectors, ceiling<br />
height limits, cables, wiring and other<br />
interconnections and inspection and servicing.<br />
This isn’t a full and complete list, but does<br />
afford an indication of the degree of depth of<br />
the seminar. The FIA is committed to improving<br />
levels of professionalism throughout the<br />
industry and this seminar will provide plenty of<br />
insight into what is a complex subject area.<br />
The second seminar running at FIM Expo will<br />
be discussing the future of the fire industry.<br />
What levels of competency will be expected or<br />
needed in 2018 and beyond? In the current<br />
climate, wherein pressures on responsible<br />
persons/duty holders are rising, what will<br />
potential clients be looking for in their chosen<br />
fire detection and alarm service company?<br />
Entitled ‘The Future of Qualifications in Fire<br />
Detection and Alarms’, this is a good<br />
opportunity to hear from industry experts and<br />
ask questions about the movement of the<br />
industry over the next few years. This<br />
presentation will be given by the FIA’s general<br />
manager Martin Duggan who has served the<br />
organisation since 2001 and can offer a high<br />
level of intelligent and comprehensive<br />
observations and answers about the future of<br />
the industry and where it might be heading.<br />
Both seminars at this year’s FIM Expo are<br />
fully Continuing Professional Development<br />
(CPD)-accredited. CPD certificates will be<br />
available to pick up from the registration desk<br />
at the end of the presentations.<br />
Diversifying security businesses<br />
Back to the big question: ‘If you’re in security,<br />
should you diversify your business and move<br />
into fire as well?’ There’s a great deal of<br />
support available should you wish to do so, but<br />
success within the fire industry does come with<br />
a number of hoops to jump through in the first<br />
instance. It’s important to understand that the<br />
fire industry is framed by a large amount of<br />
legislation that the security industry doesn’t<br />
necessarily have, including the need to be<br />
‘competent’ (according to that legislation).<br />
While the legislation doesn’t say how to<br />
show competence, accessing accredited CPD<br />
(such as by attending seminars at FIM Expo)<br />
should help, along with achieving third party<br />
certification through an independent scheme<br />
such as BAFE. This will allow you to become a<br />
member of the FIA, subsequently putting you in<br />
good standing to gain larger contracts from<br />
bigger clients who tend to be more insistent on<br />
third party certification That isn’t always the<br />
case, but it’s most certainly a growing trend.<br />
However, only companies that have third<br />
party certification (such as BAFE SP203,<br />
SP101/ST104 or LPS1014) are eligible for<br />
membership of the FIA, so too manufacturers<br />
that are BS EN ISO 9001 certificated. We’re not<br />
interested in representing contractors who are<br />
not up to the job and who give the industry a<br />
bad name. Credibility and a reputation for high<br />
quality and second-to-none service are what<br />
FIA members are all about.<br />
Becoming certified requires being audited by<br />
a certification body and the process can<br />
certainly be a somewhat long and confusing<br />
one if you’ve never worked within this area.<br />
Thankfully, the FIA enjoys a partnership with<br />
the Security Systems and Alarms Inspection<br />
Board and a wealth of information and help to<br />
ease you through the certification process.<br />
Probationary membership is available for up<br />
to 12 months for any organisation which is on<br />
the way to achieving accreditation.<br />
Logistics for the day<br />
The FIM Expo 2018 takes<br />
place at Ashton Gate Stadium<br />
in Bristol on Wednesday 25<br />
April. The Expo is open from<br />
9.30 am through until 3.30<br />
pm. The first seminar<br />
focusing on BS 5839-1:2017<br />
is being presented at 11.00<br />
am, with the second<br />
concentrating on the<br />
industry’s future roadmap<br />
running at 2.00 pm<br />
Although the event is free to<br />
attend, spaces are limited<br />
and it’s recommended to<br />
register in advance to secure<br />
a space. Full details are<br />
available on the event<br />
website. Visit www.fimexpo.com<br />
to register<br />
“Confirmed exhibitors at the FIM Expo will be showcasing a<br />
range of products and, with new ranges being developed,<br />
it’s a good opportunity to find out if there are any<br />
particular solutions you need to source”<br />
43<br />
www.risk-uk.com
Recognising ‘The Hero Factor’<br />
find it difficult to share positive stories about<br />
themselves and their work with colleagues and<br />
clients, preferring instead to exercise modesty<br />
and humility.<br />
Isn’t that a waste of potentially powerful<br />
content, which could be used in a number of<br />
ways to promote the individual, the company<br />
and the industry?<br />
Showing members of<br />
the security staff that<br />
they’re appreciated<br />
through visible<br />
recognition and<br />
reward is important if<br />
the employer and<br />
service buyer wants to<br />
see the best return<br />
from those on duty. As<br />
Amanda McCloskey<br />
details, investment in<br />
staff confidence and<br />
motivation drivers has<br />
multiple benefits, not<br />
least when it comes to<br />
fostering a culture<br />
built on the desire to<br />
exceed expectations<br />
Hero (Verb): “To treat or honour as a hero”.<br />
The use of the word ‘Hero’ as a verb might<br />
be relatively new, perhaps appearing<br />
more commonly in business speak vernacular<br />
thanks to the advertising industry whose<br />
moguls use it to describe how they want their<br />
product to shine out over everything else. It’s<br />
also an appropriate turn of phrase to enact<br />
when talking about the potential in spotlighting<br />
and delighting valued employees.<br />
On that note, security industry leaders need<br />
to understand what motivates their staff to get<br />
out of bed and go to work in order to prevent<br />
them from being lured away by competitors or<br />
even other industries. Notoriety and rewards<br />
are important, but ideally as part of a broad<br />
and creative approach towards showing<br />
appreciation for employees and respect for<br />
their motivational drivers. Different people are<br />
motivated by different things, but there are a<br />
few elements which are common to all.<br />
Purpose and meaning are increasingly<br />
important to today’s employees. Many value<br />
regular praise from their bosses more highly<br />
than monetary rewards. The security industry<br />
can be said to have purpose in abundance, but<br />
spotlighting and storytelling needs to come<br />
into it to ensure that the value of this purpose<br />
is communicated to all those involved.<br />
Experience tells me that many security<br />
officers are genuinely motivated by the desire<br />
to make the world a fairer and safer place. The<br />
drive to be a ‘Force for Good’ is strong and<br />
many an officer’s raison d’être. Yet some may<br />
Celebrating achievement<br />
When I reflect on the individual and team<br />
success stories that we’ve relied upon as<br />
“reasons to believe” in supporting the<br />
communication of our sales, recruitment and<br />
employee messages, not to mention emotive<br />
Case Studies to back up our industry award<br />
entries, I’m left in no doubt about the<br />
importance of celebrating staff achievements.<br />
Hero-ing people makes them feel like they’re<br />
fulfilling their job role, and we know that job<br />
purpose is inextricably linked to productivity.<br />
According to workplace behaviour expert Hatch,<br />
94% of people it surveyed said the more<br />
meaning their job has, the more likely they are<br />
to be engaged. Hatch also found that<br />
companies who afford their employees greater<br />
control grow four times as fast. Handing over<br />
more control breeds confidence and resilience.<br />
Empowering staff with transparency on<br />
company plans and encouraging the provision<br />
of feedback through focus groups and surveys<br />
cultivates a sense of involvement, while acts of<br />
generosity (to reward loyalty or help given on a<br />
project, etc) and inclusive company events<br />
create a sense of community and belonging.<br />
Among a growing list of skills, qualities and<br />
characteristics that an effective modern security<br />
professional is expected to have, confidence is<br />
an absolute lynchpin. Of course, a certain<br />
amount of self-assurance is essential, and<br />
particularly so for those working in high-profile<br />
security roles. Senior management are missing<br />
an opportunity if they fail to foster and further<br />
develop confidence levels in individuals.<br />
Confidence and competence<br />
A good security officer should project<br />
confidence and competence. Therefore, it’s<br />
important that successes be noted and<br />
celebrated to enable the building of trust in<br />
one’s own abilities and decision-making skills.<br />
Neglecting to hero your most talented and<br />
hardworking staff is a significant business risk.<br />
Anyone who deals regularly with recruitment<br />
agents will be aware of the cost of replacing<br />
44<br />
www.risk-uk.com
Security Services: Best Practice Casebook<br />
staff versus the nurturing of existing<br />
employees. Much better to keep them under<br />
your roof by building them into your succession<br />
plans and allowing them to continue spreading<br />
ripples of inspiration and a positive work ethic.<br />
Platform to self-report<br />
Staff should be given a platform to self-report<br />
their moments of glory through a well-run<br />
recognition programme which is communicated<br />
throughout the business and incentivised with<br />
a mix of rewards that ideally echo the<br />
messages imbued by the company.<br />
World-class customer service is a<br />
prerequisite for CIS Security’s clients. You<br />
simply cannot have happy customers unless<br />
you have loyal and faithful staff who are being<br />
noticed for their good efforts. Security officers<br />
will happily go above and beyond the Call of<br />
Duty if they know they’ll be acknowledged and<br />
praised for doing so, ideally in front of all of<br />
their colleagues and clients.<br />
Awards ceremonies are a great idea to show<br />
appreciation and promote dedication to duty.<br />
Layer up the extravagance according to your<br />
budget, but don’t scrimp and be clear and<br />
consistent in your criteria for qualification and<br />
winning. Honour the most talented staff with all<br />
the pomp and ceremony that they deserve for<br />
their continued hard work and determination.<br />
When it comes to external events, some<br />
managers may be insecure about letting their<br />
best people out into the networking world lest<br />
they be enticed to a competitor. On the<br />
contrary, cultivating their ‘celebrity’ can have<br />
the positive impact of making them appreciate<br />
their role as a valued brand ambassador. Offer<br />
to take a fantastic photo for their LinkedIn<br />
account and highlight them as a Newsletter<br />
columnist with a regular feature on their<br />
industry-related area of interest or expertise.<br />
They’ll appreciate your belief in them as an<br />
individual and reward you with their loyalty.<br />
The ‘War for Talent’<br />
Every conference I attend these days seems to<br />
refer to the “War for Talent”. This isn’t as<br />
simple as offering a good package anymore.<br />
Today’s talented individuals see themselves as<br />
a micro business and, as such, will conduct<br />
thorough due diligence before accepting a role<br />
at any company. This includes searching online<br />
news for any mention of a prospective employer<br />
to ensure they don’t have any form of unfair<br />
treatment of staff being reported.<br />
They will also scan any employer review<br />
websites, taking in any snapshot ‘Star Ratings’<br />
and accompanying comments from current and<br />
past employees to gauge the general<br />
satisfaction levels of those who work within the<br />
business. Any credible negative commenters<br />
should be contacted to find out more so that<br />
lessons can be learned going forward.<br />
What else can you do to keep your best<br />
people performing at the very pinnacle of their<br />
ability? If you were to ask them, more than a<br />
few would say: “It’s the little things that<br />
matter”. For instance, comfortable workplaces<br />
are essential for motivating staff to stay and<br />
finish their work on time. Good ergonomics<br />
such as comfortable, adjustable seats and<br />
considered lighting are a ‘must’. Push your<br />
budget a little further to positively transform<br />
the aesthetic of the workplace.<br />
Mental health policy<br />
Even superheroes have challenging days.<br />
Security life can be stressful and some<br />
experiences can have a lasting impact. Pastoral<br />
support and strong mental health awareness is<br />
important to maintain a healthy workforce, as<br />
detailed by Louise McCree in the Security<br />
Services: Best Practice Casebook article<br />
published in last month’s Risk UK.<br />
A functioning mental health policy, tools and<br />
communication campaign can help mitigate the<br />
risks of the high costs related to employees<br />
who might otherwise become absent from work<br />
for lengthy periods. Home working is now a far<br />
more viable option for some employees due to<br />
advances in remote technology. While not for<br />
everyone, it may be just the right space certain<br />
personality types need in order to transact their<br />
job role with a sense of comfort.<br />
Celebrated individualism and control breeds<br />
confidence and, combined with considered<br />
workspaces and approaches, makes for happy<br />
members of staff who will dutifully remain with<br />
the business through thick and thin.<br />
From my own point of view, I thoroughly<br />
enjoy reading about hero colleagues within the<br />
company, whether they’re enjoying a team night<br />
out as a reward for excellent collaboration in<br />
apprehending a nuisance criminal, receiving a<br />
long service award or even sharing photos of<br />
themselves red-faced from running their charity<br />
marathon in our Newsletter.<br />
Hero-ing individuals feels right for this<br />
industry and allows me to identify and<br />
remember those members of staff both for who<br />
they are and what they’ve achieved inside and<br />
outside of the working environment.<br />
Amanda McCloskey:<br />
Sales and Marketing Director<br />
at CIS Security<br />
“Empowering staff with transparency on company plans and<br />
encouraging the provision of feedback through focus<br />
groups and surveys cultivates a sense of involvement”<br />
45<br />
www.risk-uk.com
Successful Cloud and Mobile<br />
Technology Strategies: Security of Data<br />
malware attacks occur. This isn’t only a problem<br />
faced by large organisations, either. As BYOD<br />
has become more acceptable among SMEs, so<br />
it has created even more challenges because<br />
this size of enterprise simply doesn’t have the<br />
resources needed to manage breaches to the IP<br />
network on a large scale.<br />
Companies have faced<br />
unprecedented<br />
security challenges<br />
and risks to the<br />
integrity of their<br />
networks since cloud<br />
computing, the Bring<br />
Your Own Device<br />
(BYOD) concept and<br />
mobile technology<br />
forged a permanent<br />
place in business IT<br />
strategies. How, then,<br />
might those risks and<br />
challenges be met<br />
head on? Jocelyn<br />
Krystlik offers some<br />
thought-provoking<br />
views on the matter<br />
Today’s security managers and network<br />
administrators fear the cyber security<br />
dangers outside and the dangers lurking<br />
within pretty much in equal measure, knowing<br />
full well that they’re no longer able to rely upon<br />
the existence of a solid and reliable IP<br />
‘perimeter fence’ to defend the business.<br />
Admittedly, ongoing improvements in<br />
connectivity have brought about many benefits,<br />
allowing employees to work remotely on a<br />
much bigger scale, with increased collaboration<br />
and often lower capital expenditures. Whether<br />
from a home office or on the move, employees<br />
want to be able to access vital data from the<br />
corporate network, but the challenge is that the<br />
environments they inhabit are not always safe.<br />
Mobile devices in particular introduce<br />
potential breaches, because in the urgency to<br />
access an important document or update a<br />
calendar, the employee will almost always<br />
choose convenience over security. Access to the<br />
Internet or Wi-Fi means that, as soon as a given<br />
phone is connected to the corporate network, it<br />
creates a two-way bridge from the safety of the<br />
internal zone to the outside world. This is<br />
precisely why businesses need to consider the<br />
cloud very carefully if they’re to manage the<br />
inevitable loss of security control which could<br />
expose their digital assets.<br />
This is all-too-easy to do. While on the one<br />
hand organisations encourage their staff to use<br />
company mobiles or even their own smart<br />
phones and tablets as part of a Bring Your Own<br />
Device (BYOD) policy, primarily because it’s<br />
cost-efficient and easy, on the other hand the<br />
security team has to pick up the pieces and<br />
solve breaches to the network as and when<br />
Start with data<br />
Any discussion around security, the cloud,<br />
BYOD and mobility must beging with the topic<br />
of data. Companies need to adopt a datacentric<br />
approach because of the difficulties in<br />
protecting devices that are being used by<br />
individual employees. One of the main<br />
challenges lies in the inability to keep files<br />
encrypted as they move into and away from the<br />
cloud or are otherwise e-mailed to customers,<br />
colleagues and business partners via cloudbased<br />
services.<br />
Device-based encryption and data loss<br />
prevention technologies do keep files protected<br />
to a certain extent when they remain on the<br />
premises or on devices, but once the files are<br />
uploaded to the cloud, sent via e-mail or shared<br />
on the cloud platform, the encryption is often<br />
removed. As a result, digital assets can become<br />
dangerously exposed.<br />
On premises, sensitive data is the priority of<br />
the company, but for cloud providers, the<br />
priority will always be delivering access to their<br />
cloud platforms 24/7 rather than preventing<br />
access to data. This is why it’s important to<br />
encrypt data end-to-end. It’s the only way that<br />
companies will be able to fully protect their<br />
data from security breaches.<br />
While it’s vital that businesses afford<br />
employees and end users alike the freedom to<br />
collaborate and share files with each other as<br />
well as trusted contractors, service providers<br />
and partners, they have to strike a balance with<br />
protecting their key digital assets.<br />
Battle to remain secure<br />
Encryption is a great – if fallible – weapon to<br />
use in the battle to remain secure. Documents<br />
can be encrypted via certified trust solutions<br />
which provide each file with a unique<br />
encryption key, thereby limiting data leaks in<br />
the event of a compromise. The encryption key<br />
is controlled by the user or the organisation,<br />
removing responsibility from the cloud provider.<br />
46<br />
www.risk-uk.com
Mobile Technology: Security Management for BYOD<br />
Device-based encryption allows embedded<br />
drives or removable drives to be encrypted,<br />
enabling data to be protected. This is great if<br />
the device is lost or stolen, but problems arise<br />
if a user is logged into the device and the data<br />
is unencrypted (allowing it to be used in other<br />
Apps running on the device). To overcome the<br />
encryption gaps, data can be classified by data<br />
loss prevention, but it does present issues<br />
relating to which data files need to be<br />
encrypted and when it comes to configuring the<br />
decryption policies and rules.<br />
There’s also a more personal approach which<br />
can be used by employees and end users to<br />
apply encryption among their own trusted circle<br />
of collaborators with whom they may share<br />
password access keys to view the files.<br />
Combining this approach with centralised<br />
controls and rules creates a powerful security<br />
defence system that may be used to secure<br />
data ranging from video surveillance images<br />
through to employee records on laptops,<br />
desktops, tablets and smart phones.<br />
Even though it’s applied by employees, the IT<br />
Department is in control, defining, managing,<br />
enforcing, tracking, auditing and reporting on<br />
data protection policies for the company.<br />
Encryption limitations<br />
Implementation of end-to-end encryption does<br />
go a long way towards minimising the dangers<br />
that the data itself can find on the path from<br />
the repository to the mobile device or at rest in<br />
the cloud or a third party environment.<br />
However, companies shouldn’t fool<br />
themselves into believing that encryption can<br />
solve all of the challenges. Like many other<br />
solutions, it works for specific cyber security<br />
issues, in particular to protect data that’s being<br />
moved on and off the cloud via different<br />
devices, but it will not stop an attacking virus<br />
from deleting the entire contents of a hard drive<br />
and it doesn’t halt ransomware. Also, it doesn’t<br />
provide protection against unauthorised access<br />
to – and the misuse of – corporate internal<br />
networks. Encryption cannot protect or obscure<br />
metadata, which in some circumstances is as<br />
revealing and valuable as corporate data.<br />
If properly implemented and managed with a<br />
methodology and solution for the creation,<br />
storage, control and distribution of encryption<br />
keys, then encryption is probably the single<br />
biggest improvement that companies can make<br />
to their security, and particularly so when<br />
they’re using the cloud, BYOD and mobiles.<br />
When the IP perimeter was diminished, we<br />
also said goodbye to trust. The only real<br />
solution to this issue is strong authentication.<br />
This isn’t the same as two-factor authentication<br />
“Documents can be encrypted via certified trust solutions<br />
which provide each file with a unique encryption key,<br />
thereby limiting data leaks in the event of a compromise”<br />
or multi-factor authentication, but instead it’s<br />
the underlying basis of both – the method of<br />
verifying the identity of a user or device that’s<br />
intrinsically stringent enough to ensure the<br />
security of the system it protects by<br />
withstanding any attacks it’s likely to encounter<br />
and, by its very nature, creating an element of<br />
trust in the device or system used.<br />
Both two-factor authentication and multifactor<br />
authentication are strong<br />
authentications, but then so are several multichallenge/response<br />
approaches using singlefactor<br />
(although it must be said that these rely<br />
on multiple points of validation of the<br />
knowledge factor).<br />
As we’re now operating in a more open and<br />
collaborative working environment, it would be<br />
to our advantage to shift from the old ‘reside<br />
inside’ mindset and instead establish point-topoint<br />
trust between machines, end users and<br />
applications. Following a policy of<br />
segmentation and separation, whether it’s the<br />
physical separation of networks into data plus<br />
security plus external, or segmenting networks<br />
in application-based geographies or functions,<br />
all provide a fundamental basis for the<br />
implementation of strong authentication. In<br />
fact, it’s the next big step for consideration.<br />
Asking for help<br />
Security and network managers already have<br />
big challenges to oversee. Keeping their arms<br />
around the risks that cloud computing, BYOD<br />
policies and mobility present is becoming more<br />
difficult, not less. The responsibility of network<br />
administration in complex and dangerous<br />
environments has increased exponentially.<br />
The most committed IT security manager is<br />
unlikely to be able to manage it all, even in<br />
smaller-sized companies, so if it’s at all<br />
affordable, it’s always good practice to pull<br />
together a pool of experts with segmented<br />
responsibilities or the services of reputable<br />
security companies. Outsourcing means they<br />
can provide Security Operations Centre services<br />
and a broad range of skills. They will be as<br />
invested and involved in protecting the data of<br />
their client as the company itself, and<br />
particularly so since any issues that do arise<br />
will render them culpable.<br />
Ultimately, iit’s vital to implement encryption<br />
and to ensure that at least primary systems are<br />
protected with strong authentication.<br />
Jocelyn Krystlik:<br />
Product Marketing Manager at<br />
Stormshield<br />
47<br />
www.risk-uk.com
Risk Assessments and Education: Key for<br />
the Safety of Shoppers, Staff and Stock<br />
money makes a strong headline and investing<br />
in the latest security systems may seem like the<br />
right thing to do (and, in some instances, it may<br />
well be), but how much of that investment in<br />
combating retail crime is spent wisely?<br />
Let’s face it, the statistics tell us that such<br />
criminality is continuing to rise.<br />
Tackling the<br />
continuing rise in the<br />
rate of retail crime as<br />
reported by the British<br />
Retail Consortium<br />
means concentrating<br />
heavily on the basics<br />
(and doing them well).<br />
Here, Charlie Swanson<br />
explains in detail why<br />
thorough risk<br />
assessments, careful<br />
systems procurement<br />
and targeted training<br />
for members of staff<br />
form the key<br />
ingredients of a<br />
successful security mix<br />
in the retail arena<br />
Retailers are having a tough time of late,<br />
with Toys R Us, Maplin and Mothercare<br />
(among others) all hitting the headlines in<br />
a negative way. The British Retail Consortium<br />
(BRC) did little to lighten the mood when<br />
recently publishing the findings of its annual<br />
Retail Crime Survey, shining a light on the<br />
increasing levels of violence being experienced<br />
by shop workers and how the industry is<br />
shouldering a burden of £700 million as a<br />
direct cost of retail crime.<br />
While theft represents three-quarters of the<br />
total cost of retail crime, the most worrying<br />
revelation is that escalating rate of reported<br />
violence against employees which has doubled<br />
in a year to number six attacks per thousand<br />
members of staff. This suggests that 13 shop<br />
workers (and that includes security officers)<br />
become victims each and every day.<br />
Thankfully, the retail sector isn’t resting on<br />
its laurels, as the BRC’s CEO Helen Dickinson<br />
states in her Foreword to the 2017 Retail Crime<br />
Survey report. “Our members are fully playing<br />
their part in tackling retail crime, spending in 12<br />
weeks on crime prevention what they did for<br />
the whole of the previous year. However, that<br />
level of spending may not be viable in the<br />
longer-term,” comments Dickinson.<br />
Here, I would argue that there’s a world of<br />
difference between doing things right and<br />
doing the right things. Spending huge sums of<br />
Always risk assess<br />
If we’re going to tackle the rise in retail crime<br />
we need to start at the beginning. That means<br />
making sure we’re doing the basics and doing<br />
them well. This begins with the uncomfortable<br />
acknowledgment that the criminal is always on<br />
the front foot. They are all-too-often successful<br />
because they’re adept at spotting and<br />
exploiting vulnerabilities. Put simply, they do<br />
something many retailers are failing to do<br />
adequately or altogether – they risk assess.<br />
It sounds obvious, but if you can pinpoint<br />
areas of exposure and close them, the risk<br />
posed to the organisation is greatly reduced.<br />
This holds true whether you’re talking about<br />
the physical security of a given store in a<br />
Shopping Centre or an online store seeking to<br />
mitigate the growing threat of cyber crime.<br />
Much of the money spent on securing retail<br />
establishments is dedicated to systems (both<br />
physical and, increasingly, cyber).<br />
Organisations are always being told that there’s<br />
a new solution to their woes, and there are<br />
many excellent examples of where technology<br />
in many different guises is being used to great<br />
effect. Similarly, there are many instances<br />
where what has been specified wasn’t fit for<br />
purpose, installed poorly or used inefficiently.<br />
Many buyers are not clear on what they want<br />
and what they need their security systems to<br />
do, and don’t always understand the limitations<br />
of those systems (which, for obvious reasons,<br />
are rarely explained during the procurement<br />
process). This is just one area where a risk<br />
assessment, conducted by a qualified security<br />
professional, would help to ensure the right<br />
questions are being asked. Any investment not<br />
directly addressing an identified vulnerability<br />
would be ineffective and discounted.<br />
Untrained staff at risk<br />
Of course, the larger retailers such as<br />
supermarkets have dedicated security teams<br />
who tend to understand security systems and<br />
the need for regular risk assessments (albeit<br />
48<br />
www.risk-uk.com
Training and Career Development<br />
perhaps only to a certain degree). For small<br />
independent store owners, though, the whole<br />
process can be a challenge, because they want<br />
to spend as little as possible on security as<br />
such an investment can have an even greater<br />
impact on their bottom line. However, even if<br />
the store with one CCTV camera and monitor<br />
hasn’t undertaken a thorough risk assessment<br />
and trained the operator(s), the system isn’t<br />
then being used to its full potential.<br />
What’s more, some security systems that are<br />
commonplace for larger retail stores have been<br />
installed without adequate training or<br />
processes, and are potentially putting people in<br />
danger. A good example is the electronic<br />
tagging of products. When the alarm sounds as<br />
someone exits the store, it’s likely that<br />
members of staff may not have a full<br />
appreciation of the situation. It could be an<br />
innocent mistake. Perhaps the cashier didn’t<br />
remove the tag from an item of clothing. It may<br />
be an attempted theft. All-too-often, it’s the<br />
nearest member of staff who reacts based on<br />
instinct rather than Best Practice and, again<br />
potentially, places themselves in harm’s way.<br />
To give one example of poor procedural<br />
understanding and communication, I once<br />
spoke with two young shop employees who<br />
chased a thief running out of a store with some<br />
electrical goods. When they caught up with the<br />
male he produced a syringe seemingly filled<br />
with blood and exclaimed that he was HIV<br />
positive. When asked why they ran after him,<br />
they explained that the manager had told them<br />
to do so or else face disciplinary proceedings.<br />
The BRC’s report highlights syringes to be<br />
the second most significant weapon now used<br />
in retail crime. However, the incident to which<br />
I’m referring took place way back in 1994. Such<br />
occurrences may still be happening today and,<br />
if so, this is both wrong and extremely<br />
concerning on so many levels.<br />
Awareness and education<br />
You can conduct a risk assessment and have<br />
the right systems installed in the right way, but<br />
all of this must be accompanied by awareness<br />
and, critically, appropriate training in order for<br />
that risk assessment to be truly effective.<br />
In the previous example, the store manager<br />
clearly acted irresponsibly. However, the two<br />
members of staff on the shop floor should have<br />
been trained to know what response was<br />
required of them, which most certainly would<br />
not be to give chase to the thief.<br />
Lack of training and adherence to Best<br />
Practice is currently a massive problem area in<br />
the retail world. Often, members of staff at all<br />
levels of the business are ill-prepared regarding<br />
“You can conduct a risk assessment and have the right<br />
systems installed in the right way, but all of this must be<br />
accompanied by awareness and appropriate training”<br />
how to mitigate the risks presented to<br />
themselves, customers and merchandise. Every<br />
store manager needs to be aware of their Duty<br />
of Care when it comes to the safety and security<br />
of staff, customers and merchandise. The CEO,<br />
Saturday staff and everyone in-between also<br />
need to be mindful of the risks posed to the<br />
business and the checks and balances in place<br />
to mitigate them. Any organisation is only ever<br />
as strong as its weakest link, and you can be<br />
sure that a criminal – whether they’re physically<br />
entering a store or attacking online – will<br />
always look to exploit this weak point.<br />
Another important factor is ensuring that<br />
those who commit crime are prosecuted. This<br />
means being able to furnish the police with<br />
sufficient evidence that’s admissible in a Court<br />
of Law. With police resources stretched, they<br />
now need all the help they can muster when<br />
investigating an incident.<br />
Basic steps such as ensuring that camera<br />
systems are installed correctly can make a huge<br />
difference. This can be a challenge for smaller<br />
retailers. One shining light is the retailer Card<br />
Factory which has been complimented by the<br />
police service for the phenomenal quality of<br />
CCTV images that it’s able to share with law<br />
enforcers from its estate of 900-plus stores.<br />
Communicating the risk<br />
From my own point of view, I’ve been teaching<br />
risk management for more than 30 years and, in<br />
many respects, my mantra hasn’t changed<br />
when it comes to extolling the virtues of a<br />
thorough risk assessment and communicating<br />
the risk right across the organisation in some<br />
form of training and awareness.<br />
Before another penny is invested, my advice<br />
to you is to start assessing, planning and<br />
preparing today. Whether this is completed inhouse<br />
or with the aid of a specialist consultant,<br />
good security is about nurturing the right blend<br />
of people, process and technology.<br />
At the moment, in many instances this isn’t<br />
happening, and maybe falling down the cracks<br />
somewhere between the CEO and the shop<br />
floor. The bottom line is that, without effective<br />
risk mitigation measures, retailers will continue<br />
to render their business to unnecessary risks<br />
and suffer increasing violence against staff and<br />
shrinkage, which includes the loss of stock<br />
attributed to factors ranging from staff theft<br />
through to shoplifting and vendor fraud.<br />
Charlie Swanson MSc PG Dip<br />
CSyP FSyI SIRM:<br />
Principal Trainer at the Linx<br />
International Group<br />
49<br />
www.risk-uk.com
Risk in Action<br />
Risk in Action<br />
Abloy UK secures O2<br />
Arena thanks to<br />
Hillsborough BR4<br />
ballistic doors<br />
Located in London’s<br />
Docklands, the O2 Arena is a<br />
multi-purpose indoor venue<br />
with the second highest<br />
seating capacity of any such<br />
venue in the UK. In 2015, the<br />
O2 was the busiest music<br />
arena in the world in terms<br />
of ticket sales, handling no less than 1,819,487 tickets for myriad events.<br />
Given the increase in gun crime and terrorist attacks in the UK, high capacity<br />
venues must prepare for emerging threats. Last year, the O2 Arena was faced<br />
with a problem. The venue’s interior doors were no longer fit for purpose due to<br />
wear and damage caused by the constant flow of people entering the site. The<br />
main priority for the venue’s management team was to have doors fitted which<br />
could ensure the safety of visitors and staff from fire or criminal attacks.<br />
Abloy UK had a complete understanding of the security requirements here<br />
thanks to having worked on many Critical National Infrastructure projects<br />
across varied sectors. At the survey stage it was agreed that, in order to ensure<br />
the level of security needed and provide doors that are fire-rated, the most<br />
suitable solution was the Hillsborough BR4 ballistic doors.<br />
These fire-rated ballistic door sets designed by Abloy UK offer protection<br />
from 9 mm handguns through to armour-piercing rounds. All system testing is<br />
to European and British Standards BS EN 1522 and BS EN 1523.<br />
Abloy UK provided a full service for this project covering site survey, supply<br />
and installation and ensured that the job was carried out with one main point of<br />
contact (in this instance Wren Construction Limited, the main contractor on site<br />
throughout the project).<br />
The company was able to adapt to any additional requests during the build<br />
and fit-out process. Furthermore, Abloy UK was also able to produce a bespoke<br />
colour ‘O2 blue’ to guarantee that the door sets are aesthetically pleasing in<br />
terms of matching the O2 Arena’s colour scheme.<br />
£260 million Bradford Broadway<br />
retail complex safeguarded by<br />
Advanced fire panels<br />
The Broadway is the latest UK retail venture for<br />
property investment management business<br />
Meyer Bergman, which also owns The Bentall<br />
Centre in Kingston upon Thames and London’s<br />
iconic Burlington Arcade. It’s home to over<br />
570,000 sq ft of retail and leisure units in<br />
addition to 1,300 parking spaces.<br />
At the heart of The Broadway’s active fire<br />
protection system is a network of ten Advanced<br />
MxPro 5 intelligent multiprotocol panels. This<br />
network is augmented by a TouchControl<br />
touchscreen repeater panel, a special<br />
evacuation zone control package, a BMS<br />
interface and a bespoke PC-based graphical<br />
user interface. The network was designed,<br />
configured and commissioned by Carlton Fire<br />
Systems, a long-time Advanced partner, with<br />
the installation of equipment and cables being<br />
undertaken by Pitts Wilson Electrical.<br />
TouchControl is a fully-functional remote<br />
terminal and repeater with a ten-inch HD<br />
touchscreen that delivers new solutions<br />
including Active Maps and zone plans. These<br />
are easily added to the system from almost any<br />
drawing or image.<br />
The TouchControl interface offers fire panel,<br />
network control and reporting right down to<br />
individual device level.<br />
Nortech’s parking system enhances<br />
risk management efficiencies at<br />
Tewkesbury Community Hospital<br />
Gloucestershire Care Services NHS Trust has<br />
recently updated and improved Tewkesbury<br />
Community Hospital’s car park by using<br />
Nortech’s FeeMaster system. The Feemaster<br />
range was installed by entry control system<br />
specialist ASGuk, who had been appointed to<br />
the project by the NHS Trust to design and<br />
install a parking control system to prevent<br />
visitors from misusing the site’s car park.<br />
ASGuk proposed a time and budget-friendly<br />
solution that fitted the client’s needs now and<br />
into the future, combining both automatic<br />
barriers and parking ticket control. The<br />
company selected Nortech’s FeeMaster<br />
parking system as part of the design, which<br />
includes the FeeMaster Smart Entry Station,<br />
the FeeMaster Smart Exit Station and a<br />
number of FeeMaster Smart Consoles for<br />
inside the building.<br />
The consoles allow members of staff to<br />
control any misuse of the car park and ensure<br />
that there are enough parking spaces for<br />
visitors and patients alike at any given time.<br />
Nortech’s FeeMaster Smart parking<br />
management system is a flexible, simple and<br />
cost-effective way of managing car parking<br />
access and controlling validity periods using<br />
Mifare smart cards. This avoids the need for<br />
expensive cabling between components and<br />
minimises on-site disruption. The Smart Entry<br />
Station is designed to be used to record the<br />
date and time that a vehicle enters a car park.<br />
50<br />
www.risk-uk.com
Technology in Focus<br />
Technology in Focus<br />
Milestone Systems focuses on performance and privacy<br />
issues with XProtect 2018 R1<br />
Milestone Systems, the open<br />
platform company in networked<br />
video management software (VMS),<br />
has released XProtect 2018 R1. The<br />
business is responding to the<br />
market’s rising demands for costeffective<br />
video solutions with its first<br />
VMS update this year.<br />
In this release, Milestone pioneers the use of multiple NVIDIA graphics cards<br />
on top of Intel GPU acceleration to achieve “ultra-high performance”.<br />
The XProtect Smart Client 2018 R1 and Smart Wall are now specifically<br />
configured to actively support hardware acceleration, whereby system<br />
performance can be boosted by adding a supported graphics card to take over<br />
the ‘heavy lifting’ when it comes to decoding video, in turn leaving room for the<br />
system to handle other key tasks.<br />
This means that the end user can view more HD or Ultra HD streams just by<br />
adding one or more supported graphics cards to the computer running the<br />
XProtect Smart Client or Smart Wall.<br />
www.milestonesys.com<br />
Commend partners with<br />
TeleData UK to deliver hosted<br />
intercom platform<br />
Commend (the provider of integrated<br />
security communication systems) and<br />
TeleData UK (a highly secure Data Centre<br />
operator and cloud hosting provider)<br />
have announced details of a partnership<br />
which has enabled the former to bring a<br />
“groundbreaking” hosted security<br />
communication solution to market.<br />
The latest solution from Commend is<br />
based on a hosted platform enabling<br />
customers to gain all the advantages of a secure communication system<br />
without the need for on-site server hardware. Hugely scalable, this hosted<br />
solution enables end user customers to start small and grow on a subscription<br />
basis over a period of time.<br />
Although Commend has developed and owns the intercom platform, the<br />
company required a specialist partner to deliver the cloud infrastructure on<br />
which the application would reside. It was vital that this partner was able to<br />
offer huge scalability, immediately available technical support and a committed<br />
quality of service to guarantee the continued availability of Commend<br />
customers’ service. It was also critical to ensure that the chosen partner met<br />
Commend’s commitment to both physical and virtual security.<br />
TeleData operates some of the most secure Data Centre facilities in Europe<br />
and offers customers a range of cloud, IaaS, co-location and resilient network<br />
services. The company was able to offer Commend a cloud-based Data Centre<br />
product delivering scalability and usability and a commercial model to assist in<br />
the whole product lifecycle, from proof of concept to final product delivery.<br />
Matthew Edgley, TeleData UK’s commercial director, commented: “Commend<br />
and TeleData have some key synergies, with a real focus on physical and virtual<br />
security, application performance and service stability.”<br />
www.commend.co.uk<br />
ASSA ABLOY introduces eCLIQ<br />
electronic locking system to<br />
security market<br />
ASSA ABLOY, the<br />
door opening<br />
solutions specialist,<br />
has launched its<br />
eCLIQ electronic<br />
locking system<br />
through ASSA<br />
ABLOY Security<br />
Solutions, offering end users “reliable<br />
protection and maximum flexibility” for a<br />
wide range of buildings and facilities.<br />
Featuring what ASSA ABLOY describes as a<br />
“pioneering” chip and 128-bit AES<br />
encryption, the system has been developed<br />
to offer high security and resistance to<br />
electronic attack. Proven technology and<br />
advanced microelectronics ensure quick and<br />
secure communication between lock and<br />
key, while the eCLIQ cylinders and<br />
programmable keys are robust enough to<br />
withstand the harshest of weather.<br />
Security managers can easily update<br />
access authorisations when required. Lost<br />
eCLIQ keys may be quickly revoked, thus<br />
eliminating the time and money spent on<br />
changing lock cylinders and re-cutting keys.<br />
www.assaabloy.co.uk<br />
Herongrange integrates ievo’s<br />
biometric fingerprint readers<br />
Security system provider Herongrange has<br />
become the latest organisation to integrate<br />
biometric fingerprint readers designed and<br />
manufactured by Newcastle-based ievo with its<br />
own security access system.<br />
The integration with Herongrange’s system<br />
offers clients multi-layer security services to<br />
meet the changing needs of site access and<br />
workforce management. The biometric lead<br />
solution can reduce the risk of unauthorised<br />
access to sites and the fraudulent access and<br />
time recording commonly associated with<br />
traditional PIN or card-controlled systems.<br />
www.ievoreader.com<br />
51<br />
www.risk-uk.com
“<br />
You have to be here if you want<br />
to be regarded as a key player<br />
in the security market.<br />
“<br />
27,658<br />
visitors from<br />
116 countries<br />
79%<br />
of visitors come to<br />
source new products<br />
£20.7bn<br />
total budget of<br />
visitors to IFSEC 2017<br />
Enquire about exhibiting at IFSEC 2018: ifsec.events/international<br />
Proud to be supported by:
Appointments<br />
Socrates Coudounaris<br />
The Institute of Risk<br />
Management (IRM) has<br />
announced that Socrates<br />
Coudounaris CFIRM will<br />
step up from his position of<br />
deputy chair of the<br />
organisation’s Board when<br />
current chair Nicola<br />
Crawford CFIRM steps down<br />
in early May. Coudounaris is the executive<br />
director of risk for the EMEA region at the<br />
Reinsurance Group of America.<br />
Crawford is stepping down to pursue<br />
business opportunities having devoted a<br />
considerable amount of her professional time to<br />
the Institute with a hugely positive impact.<br />
“It’s with significant regret that I’m stepping<br />
down as the IRM’s chair,” explained Crawford in<br />
conversation with Risk UK. “I have enjoyed the<br />
role and will continue to remain involved with<br />
the IRM when it comes to supporting various<br />
initiatives, as well as being an advisory member<br />
of the Enterprise Risk Management in Banking<br />
and Financial Services Special Interest Group<br />
and the IRM Turkey Regional Group.”<br />
Coudounaris and Crawford are currently<br />
working through their transition plan to ensure<br />
that there’s a smooth handover period.<br />
On behalf of the IRM’s Board and senior<br />
management team, Coudounaris has thanked<br />
Crawford for her “dedication and contribution”<br />
to the organisation and now looks forward to<br />
taking on the vitally important role of chair.<br />
An independent, not-for-profit organisation<br />
that champions excellence in managing risk to<br />
improve organisational performance, the IRM is<br />
the leading international professional body for<br />
risk management. The Institute provides<br />
internationally-recognised qualifications and<br />
training for practising professionals.<br />
Rob Wainwright<br />
Deloitte has announced the appointment of<br />
Rob Wainwright as a senior partner in its<br />
European cyber security practice to help lead<br />
and grow the team and energise business with<br />
clients. In his new role, Wainwright will also be<br />
engaged in areas of related risk, such as<br />
financial crime and fraud prevention.<br />
Wainwright joins Deloitte from Europol, the<br />
European Union (EU) law enforcement agency,<br />
where he has served as executive director for<br />
the past nine years. As a high-level executive<br />
in the EU and the leading voice in European<br />
policing, Wainwright managed the agency that<br />
harbours 1,000 members of staff and boasts<br />
an operational network spanning 40 countries.<br />
Appointments<br />
Risk UK keeps you up-to-date with all the latest people<br />
moves in the security, fire, IT and Government sectors<br />
Mike Haley<br />
The Board of Cifas, the UK’s fraud prevention<br />
agency, has just announced the selection of<br />
Mike Haley as the new CEO for the organisation<br />
when current chief executive Simon Dukes steps<br />
down this month.<br />
Haley harbours over 30 years’ experience of<br />
tackling and preventing fraud across the public,<br />
private and not-for-profit sectors, leading<br />
investigative teams and directing fraud strategy<br />
at organisations including the NHS, the Ministry<br />
of Defence, the Office of Fair Trading, the<br />
National Fraud Authority, Her Majesty’s Revenue<br />
and Customs and the Solicitors Regulation<br />
Authority. Haley joined Cifas back in 2015 in the<br />
role of deputy CEO.<br />
Commenting on Haley’s appointment, Simon<br />
Dukes stated: “Mike has already contributed a<br />
wealth of experience and expertise to Cifas. I’m<br />
very pleased that he has been chosen by the<br />
Board to bring these skills to the role of chief<br />
executive and I wish him every success.”<br />
Dukes is set to leave Cifas on Monday 30<br />
April after nearly five years of dedicated service<br />
to the organisation in order to take up the<br />
position of CEO of the Pharmaceutical Services<br />
Negotiating Committee.<br />
For his part, Mike Haley said: “I’m delighted<br />
to be taking up this role. I look forward to<br />
continuing to develop Cifas as an innovative and<br />
authoritative leader in the field of fraud<br />
prevention as we navigate the challenges and<br />
opportunities of the coming years.”<br />
Wainwright has enjoyed a 25-year career in<br />
the spheres of intelligence, policing,<br />
Government, EU and international affairs,<br />
including posts with the Serious Organised<br />
Crime Agency, the National Criminal<br />
Intelligence Service and the British Security<br />
Service. Wainwright is an honorary fellow at<br />
the University of Exeter and Cardiff University<br />
and a member of Prime Minister Theresa May’s<br />
Task Force on Modern Slavery.<br />
Speaking about his new role, Wainwright<br />
observed: “I fully intend to bring the<br />
experience I’ve gained at Europol to the<br />
private sector, working with a wide range of<br />
clients in multiple industry sectors as part of<br />
what is undoubtedly a highly enterprising and<br />
professional team at Deloitte.”<br />
53<br />
www.risk-uk.com
Appointments<br />
Ciaran Barry<br />
The Linx International Group has appointed Ciaran Barry<br />
as director of Group operations to oversee all parts of the<br />
business, including the Linx International Consultancy,<br />
Tavcom Training, ARC Training International and<br />
Perpetuity Training.<br />
Barry has an experienced and varied background in<br />
both security and business. Following the attainment of<br />
his BA (Honours) degree in Business and French, he held<br />
a number of commercial roles before serving in the<br />
British Army for nine years and then the Hertfordshire Constabulary for over<br />
eight years in the role of detective.<br />
In 2015, Barry joined the Linx International Group as a senior consultant. He<br />
studied for a Diploma in Security Management (achieved with Distinction) and<br />
recently attained the prestigious Certified Protection Professional (CPP)<br />
qualification from ASIS International. Indeed, as an avid supporter of<br />
professionalism within the industry, Barry is actively involved with not just ASIS<br />
International, but also The Security Institute.<br />
Commenting on his appointment, Barry told Risk UK: “I’m delighted and<br />
honoured to be taking on this new and pivotal role. I’ll be taking the lead in<br />
ensuring that the market is fully aware of all services the Group has to offer.”<br />
Emma Walker<br />
Emma Walker has stepped<br />
up to the role of managing<br />
director at security<br />
specialist Ashridge Group.<br />
Ashridge Group Ltd was<br />
founded back in 2012 and<br />
is comprised of Ashridge<br />
Security Management,<br />
Ashridge Facilities<br />
Management and consultancy firm Cognitious.<br />
As the company enhances its senior<br />
capabilities, it’s also looking to build on the<br />
value of its ‘People First, Security Second’<br />
ethos, which focuses on prioritising its own<br />
employees’ needs in order to deliver customer<br />
service excellence.<br />
Given her strong people management skills<br />
and depth of understanding of the industry,<br />
Walker is set to redress the gender divide in<br />
this traditionally male-dominated sector.<br />
“Broadly speaking, the business case for<br />
parity is understood, and those in pursuit of it<br />
are very much on the right path to success,”<br />
explained Walker.<br />
Previously working as the company’s<br />
operations director, Walker’s track record<br />
combines achievements in security and<br />
business continuity planning with expertise in<br />
managing a range of resilience, major site and<br />
asset protection-focused operations.<br />
As chair of Herts Crimestoppers, Walker is<br />
also involved in driving forward various<br />
community safety projects, including work for<br />
the charity’s ‘Fearless’ dedicated youth service,<br />
whereby she has led on various safety training<br />
and awareness initiatives.<br />
Vince Bell<br />
Securitas has appointed<br />
Vince Bell in the role of<br />
fire and safety service<br />
delivery manager. With a<br />
remit to cover the South<br />
of the UK, Bell joins<br />
Securitas after 32 years<br />
of service with the<br />
London Fire Brigade.<br />
During the course of his successful career in<br />
the Fire and Rescue Service, Bell has<br />
undertaken a number of diverse roles. The first<br />
of these focused on the development, testing<br />
and delivery of tactical plans for the Control of<br />
Major Accident Hazards sites for operational<br />
and strategic management teams.<br />
Bell was also instrumental in the design and<br />
development of bespoke Health and Safety<br />
assurance audits on transport and<br />
infrastructure projects worth billions of pounds.<br />
These projects have included the Thames<br />
Tideway and Crossrail.<br />
Event operations formed a significant part of<br />
Bell’s remit during his time with the London Fire<br />
Brigade, including the development of plans for<br />
major London-based events. This involved close<br />
collaboration with Police Gold Commanders.<br />
Tony Aston FSyI<br />
The Security Institute is<br />
pleased to announce<br />
the co-option to its<br />
Board of Directors of<br />
the Institute’s Validation<br />
Board vice-chairman<br />
Tony Aston FSyI.<br />
Institute chairman Dr<br />
Alison Wakefield FSyI<br />
said: “I’m delighted to welcome Tony to the<br />
Institute’s Board of Directors. He has been an<br />
active Institute member for over ten years,<br />
having served on the Validation Board since<br />
2010 and becoming vice-chairman in 2012.<br />
Tony is also chairman of the Validation<br />
Board’s Working Group, which was<br />
established to continually review and<br />
improve the Board’s process in order to<br />
ensure that it’s fit for purpose and in line<br />
with the Institute’s long-term objectives.”<br />
Having been a career police officer for 27<br />
years, Aston then moved into the UK defence<br />
industry in 1996, joining the Government<br />
defence contractor (now known as Thales<br />
UK) under the ‘List X’ umbrella.<br />
The Security Institute’s vice-chairman Paul<br />
Drury FSyI said: “Tony has a great attention<br />
to detail and always puts the membership<br />
first in his decision-making processes.”<br />
54<br />
www.risk-uk.com
SECURITY WORKFORCE<br />
MANAGEMENT PLATFORM<br />
One platform providing actionable insights in real-time, from anywhere.<br />
160 000 +<br />
FACILITIES<br />
200 000 +<br />
USERS<br />
35<br />
COUNTRIES<br />
DRIVE OPTIMAL<br />
SECURITY DECISIONS<br />
SAVE MONEY<br />
IMPROVE PRODUCTIVITY<br />
& GROW REVENUE<br />
GAIN TIME<br />
INCREASE MOBILE<br />
OPERATIONAL PERFORMANCE<br />
OPTIMIZE SECURITY<br />
OPERATIONS<br />
LIMIT OVERTIME<br />
OUR CLIENTS<br />
“Digital transformation<br />
for security services? Not<br />
without TrackTik.”<br />
Matthieu Leroy, CEO<br />
“The very best<br />
in<br />
guard management<br />
software”<br />
Bill Barthelemy, COO<br />
“Enables data-driven drive<br />
security decisions”<br />
Luc Dupont, VP<br />
CONNECT WITH US<br />
+44 808 178 5442 TRACKTIK.COM DEMO@TRACKTIK.COM
Best Value Security Products from Insight Security<br />
www.insight-security.com Tel: +44 (0)1273 475500<br />
...and<br />
lots<br />
more<br />
Computer<br />
Security<br />
Anti-Climb Paints<br />
& Barriers<br />
Metal Detectors<br />
(inc. Walkthru)<br />
Security, Search<br />
& Safety Mirrors<br />
Security Screws &<br />
Fastenings<br />
Padlocks, Hasps<br />
& Security Chains<br />
Key Safes & Key<br />
Control Products<br />
Traffic Flow &<br />
Management<br />
see our<br />
website<br />
ACCESS CONTROL<br />
KERI SYSTEMS UK LTD<br />
Tel: + 44 (0) 1763 273 243<br />
Fax: + 44 (0) 1763 274 106<br />
Email: sales@kerisystems.co.uk<br />
www.kerisystems.co.uk<br />
ACCESS CONTROL<br />
ACCESS CONTROL & DOOR HARDWARE<br />
ALPRO ARCHITECTURAL HARDWARE<br />
Products include Electric Strikes, Deadlocking Bolts, Compact Shearlocks,<br />
Waterproof Keypads, Door Closers, Deadlocks plus many more<br />
T: 01202 676262 Fax: 01202 680101<br />
E: info@alpro.co.uk<br />
Web: www.alpro.co.uk<br />
ACCESS CONTROL – SPEED GATES, BI-FOLD GATES<br />
HTC PARKING AND SECURITY LIMITED<br />
St. James’ Bus. Centre, Wilderspool Causeway,<br />
Warrington Cheshire WA4 6PS<br />
Tel 01925 552740 M: 07969 650 394<br />
info@htcparkingandsecurity.co.uk<br />
www.htcparkingandsecurity.co.uk<br />
ACCESS CONTROL<br />
COVA SECURITY GATES LTD<br />
Bi-Folding Speed Gates, Sliding Cantilevered Gates, Road Blockers & Bollards<br />
Consultancy, Design, Installation & Maintenance - UK Manufacturer - PAS 68<br />
Tel: 01293 553888 Fax: 01293 611007<br />
Email: sales@covasecuritygates.com<br />
Web: www.covasecuritygates.com<br />
ACCESS CONTROL<br />
INTEGRATED DESIGN LIMITED<br />
Integrated Design Limited, Feltham Point,<br />
Air Park Way, Feltham, Middlesex. TW13 7EQ<br />
Tel: +44 (0) 208 890 5550<br />
sales@idl.co.uk<br />
www.fastlane-turnstiles.com<br />
ACCESS CONTROL<br />
SECURE ACCESS TECHNOLOGY LIMITED<br />
Authorised Dealer<br />
ACCESS CONTROL MANUFACTURER<br />
NORTECH CONTROL SYSTEMS LTD.<br />
Nortech House, William Brown Close<br />
Llantarnam Park, Cwmbran NP44 3AB<br />
Tel: 01633 485533<br />
Email: sales@nortechcontrol.com<br />
www.nortechcontrol.com<br />
ACCESS CONTROL – BIOMETRICS, BARRIERS, CCTV, TURNSTILES<br />
UKB INTERNATIONAL LTD<br />
Planet Place, Newcastle upon Tyne<br />
Tyne and Wear NE12 6RD<br />
Tel: 0845 643 2122<br />
Email: sales@ukbinternational.com<br />
Web: www.ukbinternational.com<br />
Tel: 0845 1 300 855 Fax: 0845 1 300 866<br />
Email: info@secure-access.co.uk<br />
Website: www.secure-access.co.uk<br />
Custom Designed Equipment<br />
• Indicator Panels<br />
• Complex Door Interlocking<br />
• Sequence Control<br />
• Door Status Systems<br />
• Panic Alarms<br />
<br />
• Bespoke Products<br />
Hoyles are the UK’s leading supplier of<br />
custom designed equipment for the<br />
security and access control industry.<br />
From simple indicator panels to<br />
complex door interlock systems.<br />
www.hoyles.com<br />
sales@hoyles.com<br />
Tel: +44 (0)1744 886600<br />
BUSINESS CONTINUITY<br />
TO ADVERTISE HERE CONTACT:<br />
Paul Amura<br />
Tel: 020 8295 8307<br />
Email: paul.amura@proactivpubs.co.uk<br />
BUSINESS CONTINUITY MANAGEMENT<br />
CONTINUITY FORUM<br />
Creating Continuity ....... Building Resilience<br />
A not-for-profit organisation providing help and support<br />
Tel: +44(0)208 993 1599 Fax: +44(0)1886 833845<br />
Email: membership@continuityforum.org<br />
Web: www.continuityforum.org<br />
www.insight-security.com Tel: +44 (0)1273 475500
CCTV<br />
CCTV<br />
Rapid Deployment Digital IP High Resolution CCTV<br />
40 hour battery, Solar, Wind Turbine and Thermal Imaging<br />
Wired or wireless communication fixed IP<br />
CE Certified<br />
Modicam Europe, 5 Station Road, Shepreth,<br />
Cambridgeshire SG8 6PZ<br />
www.modicam.com sales@modicameurope.com<br />
CCTV SPECIALISTS<br />
PLETTAC SECURITY LTD<br />
Unit 39 Sir Frank Whittle Business Centre,<br />
Great Central Way, Rugby, Warwickshire CV21 3XH<br />
Tel: 01788 567811 Fax: 01788 544 549<br />
Email: jackie@plettac.co.uk<br />
www.plettac.co.uk<br />
CONTROL ROOM & MONITORING SERVICES<br />
CCTV POLES, COLUMNS, TOWERS AND MOUNTING PRODUCTS<br />
ALTRON COMMUNICATIONS EQUIPMENT LTD<br />
Tower House, Parc Hendre, Capel Hendre, Carms. SA18 3SJ<br />
Tel: +44 (0) 1269 831431<br />
Email: cctvsales@altron.co.uk<br />
Web: www.altron.co.uk<br />
ADVANCED MONITORING SERVICES<br />
EUROTECH MONITORING SERVICES LTD.<br />
Specialist in:- Outsourced Control Room Facilities • Lone Worker Monitoring<br />
• Vehicle Tracking • Message Handling<br />
• Help Desk Facilities • Keyholding/Alarm Response<br />
Tel: 0208 889 0475 Fax: 0208 889 6679<br />
E-MAIL eurotech@eurotechmonitoring.net<br />
Web: www.eurotechmonitoring.net<br />
DISTRIBUTORS<br />
CCTV<br />
G-TEC DISTRIBUTION<br />
Gtec House, 35-37 Whitton Dene<br />
Hounslow, Middlesex TW3 2JN<br />
Tel: 0208 898 9500<br />
www.gtecsecurity.co.uk<br />
sales@gtecsecurity.co.uk<br />
SPECIALISTS IN HD CCTV<br />
MaxxOne<br />
Unit A10 Pear Mill, Lower Bredbury, Stockport. SK6 2BP<br />
Tel +44 (0)161 430 3849<br />
www.maxxone.com<br />
sales@onlinesecurityproducts.co.uk<br />
www.onlinesecurityproducts.co.uk<br />
AWARD-WINNING, LEADING GLOBAL WHOLESALE<br />
DISTRIBUTOR OF SECURITY AND LOW VOLTAGE PRODUCTS.<br />
ADI GLOBAL DISTRIBUTION<br />
Distributor of electronic security systems and solutions for over 250 leading manufacturers, the company<br />
also offers an internal technical support team, dedicated field support engineers along with a suite of<br />
training courses and services. ADI also offers a variety of fast, reliable delivery options, including specified<br />
time delivery, next day or collection from any one of 28 branches nationwide. Plus, with an ADI online<br />
account, installers can order up to 7pm for next day delivery.<br />
Tel: 0161 767 2990 Fax: 0161 767 2999 Email: sales.uk@adiglobal.com www.adiglobal.com/uk<br />
CCTV & IP SECURITY SOLUTIONS<br />
PANASONIC SYSTEM COMMUNICATIONS COMPANY<br />
EUROPE<br />
Panasonic House, Willoughby Road<br />
Bracknell, Berkshire RG12 8FP UK<br />
Tel: 0207 0226530<br />
Email: info@business.panasonic.co.uk<br />
TO ADVERTISE HERE CONTACT:<br />
Paul Amura<br />
Tel: 020 8295 8307<br />
Email: paul.amura@proactivpubs.co.uk<br />
DIGITAL IP CCTV<br />
SESYS LTD<br />
High resolution ATEX certified cameras, rapid deployment<br />
cameras and fixed IP CCTV surveillance solutions available with<br />
wired or wireless communications.<br />
1 Rotherbrook Court, Bedford Road, Petersfield, Hampshire, GU32 3QG<br />
Tel +44 (0) 1730 230530 Fax +44 (0) 1730 262333<br />
Email: info@sesys.co.uk www.sesys.co.uk<br />
www.insight-security.com Tel: +44 (0)1273 475500
THE UK’S MOST SUCCESSFUL DISTRIBUTOR OF IP, CCTV, ACCESS<br />
CONTROL AND INTRUDER DETECTION SOLUTIONS<br />
NORBAIN SD LTD<br />
210 Wharfedale Road, IQ Winnersh, Wokingham, Berkshire, RG41 5TP<br />
Tel: 0118 912 5000 Fax: 0118 912 5001<br />
www.norbain.com<br />
Email: info@norbain.com<br />
INTEGRATED SECURITY SOLUTIONS<br />
INNER RANGE EUROPE LTD<br />
Units 10 - 11, Theale Lakes Business Park, Moulden Way, Sulhampstead,<br />
Reading, Berkshire RG74GB, United Kingdom<br />
Tel: +44(0) 845 470 5000 Fax: +44(0) 845 470 5001<br />
Email: ireurope@innerrange.co.uk<br />
www.innerrange.com<br />
UK LEADERS IN BIG BRAND CCTV DISTRIBUTION<br />
SATSECURE<br />
Hikivision & MaxxOne (logos) Authorised Dealer<br />
Unit A10 Pear Mill, Lower Bredbury,<br />
Stockport. SK6 2BP<br />
Tel +44 (0)161 430 3849<br />
www.satsecure.uk<br />
PERIMETER PROTECTION<br />
IDENTIFICATION<br />
PERIMETER PROTECTION<br />
GPS PERIMETER SYSTEMS LTD<br />
14 Low Farm Place, Moulton Park<br />
Northampton, NN3 6HY UK<br />
Tel: +44(0)1604 648344 Fax: +44(0)1604 646097<br />
E-mail: info@gpsperimeter.co.uk<br />
Web site: www.gpsperimeter.co.uk<br />
POWER<br />
COMPLETE SOLUTIONS FOR IDENTIFICATION<br />
DATABAC GROUP LIMITED<br />
1 The Ashway Centre, Elm Crescent,<br />
Kingston upon Thames, Surrey KT2 6HH<br />
Tel: +44 (0)20 8546 9826<br />
Fax:+44 (0)20 8547 1026<br />
enquiries@databac.com<br />
INDUSTRY ORGANISATIONS<br />
POWER SUPPLIES – DC SWITCH MODE AND AC<br />
DYCON LTD<br />
Unit A, Cwm Cynon Business Park, Mountain Ash, CF45 4ER<br />
Tel: 01443 471900 Fax: 01443 479 374<br />
Email: sales@dyconpower.com<br />
www.dyconpower.com<br />
TRADE ASSOCIATION FOR THE PRIVATE SECURITY INDUSTRY<br />
BRITISH SECURITY INDUSTRY ASSOCIATION<br />
Tel: 0845 389 3889<br />
Email: info@bsia.co.uk<br />
Website: www.bsia.co.uk<br />
Twitter: @thebsia<br />
UPS - UNINTERRUPTIBLE POWER SUPPLIES<br />
ADEPT POWER SOLUTIONS LTD<br />
Adept House, 65 South Way, Walworth Business Park<br />
Andover, Hants SP10 5AF<br />
Tel: 01264 351415 Fax: 01264 351217<br />
Web: www.adeptpower.co.uk<br />
E-mail: sales@adeptpower.co.uk<br />
INTEGRATED SECURITY SOLUTIONS<br />
SECURITY PRODUCTS AND INTEGRATED SOLUTIONS<br />
HONEYWELL SECURITY AND FIRE<br />
Tel: +44 (0) 844 8000 235<br />
E-mail: securitysales@honeywell.com<br />
UPS - UNINTERRUPTIBLE POWER SUPPLIES<br />
UNINTERRUPTIBLE POWER SUPPLIES LTD<br />
Woodgate, Bartley Wood Business Park<br />
Hook, Hampshire RG27 9XA<br />
Tel: 01256 386700 5152 e-mail:<br />
sales@upspower.co.uk<br />
www.upspower.co.uk<br />
www.insight-security.com Tel: +44 (0)1273 475500
SECURITY<br />
ANTI-CLIMB SOLUTIONS & SECURITY PRODUCT SPECIALISTS<br />
INSIGHT SECURITY<br />
Units 1 & 2 Cliffe Industrial Estate<br />
Lewes, East Sussex BN8 6JL<br />
Tel: 01273 475500<br />
Email:info@insight-security.com<br />
www.insight-security.com<br />
CASH & VALUABLES IN TRANSIT<br />
CONTRACT SECURITY SERVICES LTD<br />
Challenger House, 125 Gunnersbury Lane, London W3 8LH<br />
Tel: 020 8752 0160 Fax: 020 8992 9536<br />
E: info@contractsecurity.co.uk<br />
E: sales@contractsecurity.co.uk<br />
Web: www.contractsecurity.co.uk<br />
EXPERTS IN X-RAY SCANNING SECURITY EQUIPMENT SINCE 1950<br />
TODD RESEARCH<br />
1 Stirling Way, Papworth Business Park<br />
Papworth Everard, Cambridgeshire CB23 3GY<br />
United Kingdom<br />
Tel: 01480 832202<br />
Email: xray@toddresearch.co.uk<br />
FENCING SPECIALISTS<br />
J B CORRIE & CO LTD<br />
Frenchmans Road<br />
Petersfield, Hampshire GU32 3AP<br />
Tel: 01730 237100<br />
Fax: 01730 264915<br />
email: fencing@jbcorrie.co.uk<br />
INTRUSION DETECTION AND PERIMETER PROTECTION<br />
OPTEX (EUROPE) LTD<br />
Redwall® infrared and laser detectors for CCTV applications and Fiber SenSys® fibre<br />
optic perimeter security solutions are owned by Optex. Platinum House, Unit 32B<br />
Clivemont Road, Cordwallis Industrial Estate, Maidenhead, Berkshire, SL6 7BZ<br />
Tel: +44 (0) 1628 631000 Fax: +44 (0) 1628 636311<br />
Email: sales@optex-europe.com<br />
www.optex-europe.com<br />
ONLINE SECURITY SUPERMARKET<br />
EBUYELECTRICAL.COM<br />
Lincoln House,<br />
Malcolm Street<br />
Derby DE23 8LT<br />
Tel: 0871 208 1187<br />
www.ebuyelectrical.com<br />
LIFE SAFETY EQUIPMENT<br />
C-TEC<br />
Challenge Way, Martland Park,<br />
Wigan WN5 OLD United Kingdom<br />
Tel: +44 (0) 1942 322744<br />
Fax: +44 (0) 1942 829867<br />
Website: www.c-tec.com<br />
PERIMETER SECURITY<br />
TAKEX EUROPE LTD<br />
Aviary Court, Wade Road, Basingstoke<br />
Hampshire RG24 8PE<br />
Tel: +44 (0) 1256 475555<br />
Fax: +44 (0) 1256 466268<br />
Email: sales@takex.com<br />
Web: www.takex.com<br />
SECURITY EQUIPMENT<br />
PYRONIX LIMITED<br />
Secure House, Braithwell Way, Hellaby,<br />
Rotherham, South Yorkshire, S66 8QY.<br />
Tel: +44 (0) 1709 700 100 Fax: +44 (0) 1709 701 042<br />
www.facebook.com/Pyronix<br />
www.linkedin.com/company/pyronix www.twitter.com/pyronix<br />
SECURITY SYSTEMS<br />
BOSCH SECURITY SYSTEMS LTD<br />
PO Box 750, Uxbridge, Middlesex UB9 5ZJ<br />
Tel: 0330 1239979<br />
E-mail: uk.securitysystems@bosch.com<br />
Web: uk.boschsecurity.com<br />
INTRUDER AND FIRE PRODUCTS<br />
CQR SECURITY<br />
125 Pasture road, Moreton, Wirral UK CH46 4 TH<br />
Tel: 0151 606 1000<br />
Fax: 0151 606 1122<br />
Email: andyw@cqr.co.uk<br />
www.cqr.co.uk<br />
SECURITY EQUIPMENT<br />
CASTLE<br />
Secure House, Braithwell Way, Hellaby,<br />
Rotherham, South Yorkshire, S66 8QY<br />
TEL +44 (0) 1709 700 100 FAX +44 (0) 1709 701 042<br />
www.facebook.com/castlesecurity www.linkedin.com/company/castlesecurity<br />
www.twitter.com/castlesecurity<br />
QUALITY SECURITY AND SUPPORT SERVICES<br />
CONSTANT SECURITY SERVICES<br />
Cliff Street, Rotherham, South Yorkshire S64 9HU<br />
Tel: 0845 330 4400<br />
Email: contact@constant-services.com<br />
www.constant-services.com<br />
SECURITY PRODUCTS<br />
EATON<br />
Eaton is one of the world’s leading manufacturers of security equipment<br />
its Scantronic and Menvier product lines are suitable for all types of<br />
commercial and residential installations.<br />
Tel: 01594 545 400 Email: securitysales@eaton.com<br />
Web: www.uk.eaton.com Twitter: @securityTP<br />
SECURE CONNECTIVITY PROVIDERS<br />
CSL<br />
T: +44 (0)1895 474 474<br />
sales@csldual.com<br />
@CSLDualCom<br />
www.csldual.com<br />
SECURITY SYSTEMS<br />
VICON INDUSTRIES LTD.<br />
Brunel Way, Fareham<br />
Hampshire, PO15 5TX<br />
United Kingdom<br />
www.vicon.com<br />
www.insight-security.com Tel: +44 (0)1273 475500
Inner Range’s Integriti<br />
High Security System is<br />
a complete Hardware/<br />
Software solution designed<br />
specifically for High Security<br />
installations.<br />
Our range includes:<br />
All Software<br />
Hardware Controllers<br />
End of Line Modules<br />
Power Supplies<br />
Keypads<br />
Enclosures<br />
Communications Devices<br />
Access Control Readers<br />
Credentials<br />
WHY TAKE CHANCES?<br />
FULL END TO END DATA ENCRYPTION EXTERNALLY CERTIFIED<br />
T: +44 845 470 5000 | E: ireurope@innerrange.co.uk innerrange.com