Pareekshavijayi e-Book
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
R<br />
12 Veto<br />
follow us: facebook.com/vetotrivandrum 23<br />
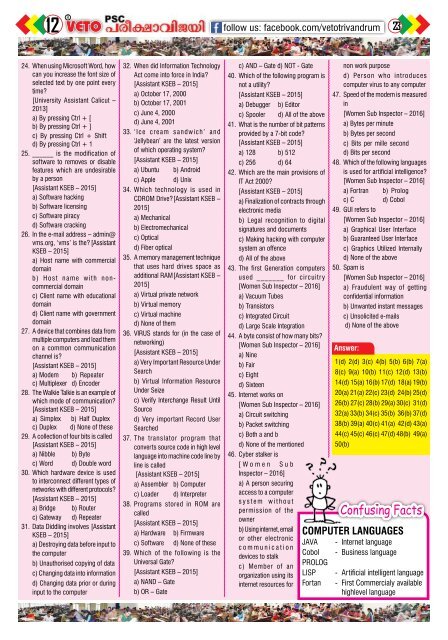
24. When using Microsoft Word, how<br />
can you increase the font size of<br />
selected text by one point every<br />
time?<br />
[University Assistant Calicut –<br />
2013]<br />
a) By pressing Ctrl + [<br />
b) By pressing Ctrl + ]<br />
c) By pressing Ctrl + Shift<br />
d) By pressing Ctrl + 1<br />
25. ______ is the modification of<br />
software to removes or disable<br />
features which are undesirable<br />
by a person<br />
[Assistant KSEB – 2015]<br />
a) Software hacking<br />
b) Software licensing<br />
c) Software piracy<br />
d) Software cracking<br />
26. In the e-mail address – admin@<br />
vms.org, ‘vms’ is the? [Assistant<br />
KSEB – 2015]<br />
a) Host name with commercial<br />
domain<br />
b) Host name with noncommercial<br />
domain<br />
c) Client name with educational<br />
domain<br />
d) Client name with government<br />
domain<br />
27. A device that combines data from<br />
multiple computers and load them<br />
on a common communication<br />
channel is?<br />
[Assistant KSEB – 2015]<br />
a) Modem b) Repeater<br />
c) Multiplexer d) Encoder<br />
28. The Walkie Talkie is an example of<br />
which mode of communication?<br />
[Assistant KSEB – 2015]<br />
a) Simplex b) Half Duplex<br />
c) Duplex d) None of these<br />
29. A collection of four bits is called<br />
[Assistant KSEB – 2015]<br />
a) Nibble b) Byte<br />
c) Word d) Double word<br />
30. Which hardware device is used<br />
to interconnect different types of<br />
networks with different protocols?<br />
[Assistant KSEB – 2015]<br />
a) Bridge b) Router<br />
c) Gateway d) Repeater<br />
31. Data Diddling involves [Assistant<br />
KSEB – 2015]<br />
a) Destroying data before input to<br />
the computer<br />
b) Unauthorised copying of data<br />
c) Changing data into information<br />
d) Changing data prior or during<br />
input to the computer<br />
32. When did Information Technology<br />
Act come into force in India?<br />
[Assistant KSEB – 2015]<br />
a) October 17, 2000<br />
b) October 17, 2001<br />
c) June 4, 2000<br />
d) June 4, 2001<br />
33. ‘Ice cream sandwich’ and<br />
‘Jellybean’ are the latest version<br />
of which operating system?<br />
[Assistant KSEB – 2015]<br />
a) Ubuntu b) Android<br />
c) Apple d) Unix<br />
34. Which technology is used in<br />
CDROM Drive? [Assistant KSEB –<br />
2015]<br />
a) Mechanical<br />
b) Electromechanical<br />
c) Optical<br />
d) Fiber optical<br />
35. A memory management technique<br />
that uses hard drives space as<br />
additional RAM [Assistant KSEB –<br />
2015]<br />
a) Virtual private network<br />
b) Virtual memory<br />
c) Virtual machine<br />
d) None of them<br />
36. VIRUS stands for (in the case of<br />
networking)<br />
[Assistant KSEB – 2015]<br />
a) Very Important Resource Under<br />
Search<br />
b) Virtual Information Resource<br />
Under Seize<br />
c) Verify Interchange Result Until<br />
Source<br />
d) Very important Record User<br />
Searched<br />
37. The translator program that<br />
converts source code in high level<br />
language into machine code line by<br />
line is called<br />
[Assistant KSEB – 2015]<br />
a) Assembler b) Computer<br />
c) Loader d) Interpreter<br />
38. Programs stored in ROM are<br />
called<br />
[Assistant KSEB – 2015]<br />
a) Hardware b) Firmware<br />
c) Software d) None of these<br />
39. Which of the following is the<br />
Universal Gate?<br />
[Assistant KSEB – 2015]<br />
a) NAND – Gate<br />
b) OR – Gate<br />
c) AND – Gate d) NOT - Gate<br />
40. Which of the following program is<br />
not a utility?<br />
[Assistant KSEB – 2015]<br />
a) Debugger b) Editor<br />
c) Spooler d) All of the above<br />
41. What is the number of bit patterns<br />
provided by a 7-bit code?<br />
[Assistant KSEB – 2015]<br />
a) 128 b) 512<br />
c) 256 d) 64<br />
42. Which are the main provisions of<br />
IT Act 2000?<br />
[Assistant KSEB – 2015]<br />
a) Finalization of contracts through<br />
electronic media<br />
b) Legal recognition to digital<br />
signatures and documents<br />
c) Making hacking with computer<br />
system an offence<br />
d) All of the above<br />
43. The first Generation computers<br />
used _______ for circuitry<br />
[Women Sub Inspector – 2016]<br />
a) Vacuum Tubes<br />
b) Transistors<br />
c) Integrated Circuit<br />
d) Large Scale Integration<br />
44. A byte consist of how many bits?<br />
[Women Sub Inspector – 2016]<br />
a) Nine<br />
b) Fair<br />
c) Eight<br />
d) Sixteen<br />
45. Internet works on<br />
[Women Sub Inspector – 2016]<br />
a) Circuit switching<br />
b) Packet switching<br />
c) Both a and b<br />
d) None of the mentioned<br />
46. Cyber stalker is<br />
[Women Sub<br />
Inspector – 2016]<br />
a) A person securing<br />
access to a computer<br />
system without<br />
permission of the<br />
owner<br />
b) Using internet, email<br />
or other electronic<br />
JAVA<br />
communication<br />
Cobol<br />
devices to stalk<br />
Prolog<br />
c) Member of an<br />
organization using its LISP<br />
internet resources for Fortan<br />
non work purpose<br />
d) Person who introduces<br />
computer virus to any computer<br />
47. Speed of the modem is measured<br />
in<br />
[Women Sub Inspector – 2016]<br />
a) Bytes per minute<br />
b) Bytes per second<br />
c) Bits per mille second<br />
d) Bits per second<br />
48. Which of the following languages<br />
is used for artificial intelligence?<br />
[Women Sub Inspector – 2016]<br />
a) Fortran b) Prolog<br />
c) C d) Cobol<br />
49. GUI refers to<br />
[Women Sub Inspector – 2016]<br />
a) Graphical User Interface<br />
b) Guaranteed User Interface<br />
c) Graphics Utilized Internally<br />
d) None of the above<br />
50. Spam is<br />
[Women Sub Inspector – 2016]<br />
a) Fraudulent way of getting<br />
confidential information<br />
b) Unwanted instant messages<br />
c) Unsolicited e-mails<br />
d) None of the above<br />
Answer:<br />
1(d) 2(d) 3(c) 4(b) 5(b) 6(b) 7(a)<br />
8(c) 9(a) 10(b) 11(c) 12(d) 13(b)<br />
14(d) 15(a) 16(b) 17(d) 18(a) 19(b)<br />
20(a) 21(a) 22(c) 23(d) 24(b) 25(d)<br />
26(b) 27(c) 28(b) 29(a) 30(c) 31(d)<br />
32(a) 33(b) 34(c) 35(b) 36(b) 37(d)<br />
38(b) 39(a) 40(c) 41(a) 42(d) 43(a)<br />
44(c) 45(c) 46(c) 47(d) 48(b) 49(a)<br />
50(b)<br />
Confusing Facts<br />
Computer languages<br />
- Internet language<br />
- Business language<br />
- Artificial intelligent language<br />
- First Commercialy available<br />
highlevel language