CS1907
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
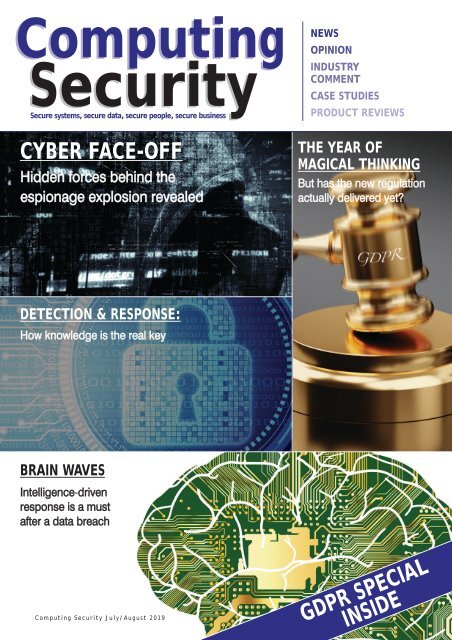
Computing<br />
Security<br />
Secure systems, secure data, secure people, secure business<br />
CYBER FACE-OFF<br />
Hidden forces behind the<br />
espionage explosion revealed<br />
NEWS<br />
OPINION<br />
INDUSTRY<br />
COMMENT<br />
CASE STUDIES<br />
PRODUCT REVIEWS<br />
THE YEAR OF<br />
MAGICAL THINKING<br />
But has the new regulation<br />
actually delivered yet?<br />
DETECTION & RESPONSE:<br />
How knowledge is the real key<br />
BRAIN WAVES<br />
Intelligence-driven<br />
response is a must<br />
after a data breach<br />
Computing Security July/August 2019<br />
GDPR SPECIAL<br />
INSIDE
On-site Media Destruction<br />
Security-savvy businesses don’t think twice about having paper records securely<br />
shredded, but many fail to apply the same philosophy when it comes to hard disk and<br />
media sanitization.<br />
CDL offer a full range of data sanitization services, culminating with our on-site media<br />
destruction vehicle, where clients can witness their data being destroyed on their on<br />
their premises. Our vehicle is equipped to destroy all forms of media to the highest<br />
recognized standards.<br />
For a competitive quote from an award winning business, please contact our sales<br />
team on 01925 730033.<br />
www.computerdisposals.com<br />
T: 01925 730033<br />
CDL House, Davy Road, Runcorn, Cheshire, WA7 1PZ.
comment<br />
NATION IN TRANSFORMATION<br />
Inote that a new report (yes, I know - how many more can there be!) is claiming to serve as<br />
a reality check on digital transformation by outlining where organisations actually are in<br />
the process. It must be said this is a topic that's both timely and 'of the moment', as many<br />
enterprises are either already submerged in digital or building up to embrace it.<br />
"So ubiquitous is digital technology in enterprises, that some commentators think the initial<br />
process of digital transformation is nearing fulfilment," says Nominet, which has published the<br />
report, 'Cyber Security in the Age of Digital Transformation' - https://bit.ly/2O99TO2. However,<br />
the digital transformation of industry and enterprises also brings major challenges with it, one<br />
of the most pressing being security.<br />
States Nominet: "A greater exposure to digital technology means a greater exposure to<br />
system vulnerabilities, as the tools being used by businesses to innovate, like AI and machine<br />
learning, could be vulnerable to attack and are also being used by hackers."<br />
Key findings to emerge from the survey of more than 270 CISOs, CTOs, CIOs - and other<br />
professionals with the responsibility for overseeing the cyber security of their organisation -<br />
include acknowledgement that cyber security is the top 'threat' to digital transformation (53%),<br />
while also confirming that many businesses were leaving it to the pre-implementation stage<br />
(28%), implementation stage (27%) or even post-implementation of the digital transformation<br />
strategy (9%) - suggesting a perception gap of when 'early enough' actually is.<br />
Commenting on the report, Cath Goulding, CISO, Nominet, points out the following: "With<br />
digital transformation, you have to be sure that, when you're bringing in new applications,<br />
security is considered from the outset. More than this, though, in a digital transformation<br />
project the real trick is to manage the security considerations of legacy and new applications<br />
simultaneously."<br />
What's most worrying, however, is this other stat: 85% said their security was highly effective,<br />
despite the fact that 86% had experienced a breach in the past 12 months. How blinkered can<br />
an organisation be to see itself as both breached and safe? I 've never been a great fan of the<br />
much overused cliché, which states: 'It's not a matter of if, but when'. Yet I'm beginning to feel<br />
anyone in so much denial deserves to see that mantra carved on their corporate door.<br />
Brian Wall<br />
Editor<br />
Computing Security<br />
brian.wall@btc.co.uk<br />
EDITOR: Brian Wall<br />
(brian.wall@btc.co.uk)<br />
PRODUCTION: Abby Penn<br />
(abby.penn@btc.co.uk)<br />
LAYOUT/DESIGN: Ian Collis<br />
(ian.collis@btc.co.uk)<br />
SALES:<br />
Edward O’Connor<br />
(edward.oconnor@btc.co.uk)<br />
+ 44 (0)1689 616 000<br />
Louise Hollingdale<br />
(louise.hollingdale@btc.co.uk)<br />
+ 44 (0)1689 616 000<br />
PUBLISHER: John Jageurs<br />
(john.jageurs@btc.co.uk)<br />
Published by Barrow & Thompkins<br />
Connexions Ltd (BTC)<br />
35 Station Square,<br />
Petts Wood, Kent, BR5 1LZ<br />
Tel: +44 (0)1689 616 000<br />
Fax: +44 (0)1689 82 66 22<br />
SUBSCRIPTIONS:<br />
UK: £35/year, £60/two years,<br />
£80/three years;<br />
Europe: £48/year, £85/two years,<br />
£127/three years<br />
R.O.W:£62/year, £115/two years,<br />
£168/three years<br />
Single copies can be bought for<br />
£8.50 (includes postage & packaging).<br />
Published 6 times a year.<br />
© 2019 Barrow & Thompkins<br />
Connexions Ltd. All rights reserved.<br />
No part of the magazine may be<br />
reproduced without prior consent,<br />
in writing, from the publisher.<br />
www.computingsecurity.co.uk July/August 2019 computing security<br />
@CSMagAndAwards<br />
3
Secure systems, secure data, secure people, secure business<br />
Computing Security July/August 2019<br />
contents<br />
CONTENTS<br />
Computing<br />
Security<br />
NEWS<br />
OPINION<br />
INDUSTRY<br />
COMMENT<br />
CASE STUDIES<br />
PRODUCT REVIEWS<br />
CYBER FACE-OFF<br />
THE YEAR OF<br />
MAGICAL THINKING<br />
Hidden forces behind the<br />
But has the new regulation<br />
espionage explosion revealed<br />
actually delivered yet?<br />
DETECTION & RESPONSE:<br />
How knowledge is the real key<br />
BRAIN WAVES<br />
Intelligence-driven<br />
response is a must<br />
after a data breach<br />
COMMENT 3<br />
Nation in transformation<br />
GDPR SPECIAL<br />
INSIDE<br />
EDITOR’S FOCUS 6-7<br />
Twenty fast-growth cyber scale-ups have<br />
been accepted onto their first national<br />
cyber security growth programme<br />
ARTICLES<br />
FULLY IN THE FLOW 8<br />
Document Logistix uses DAST to ensure<br />
security of sensitive customer data<br />
GDPR BARES ITS TEETH 10<br />
With the one-year anniversary of GDPR<br />
having come and gone and the first few<br />
hefty fines now imposed on organisations<br />
by the regulators, we look at what it all<br />
means for the future of the industry<br />
WHO CAN YOU REALLY BANK ON? 16<br />
Those who rely on their online bank to<br />
keep their money safe might be alarmed<br />
to hear that last year 54% of these<br />
institutions allowed attackers to steal<br />
THREAT OR TREAT? 22<br />
money. And their customer data may<br />
be equally at risk<br />
How organisations should set about the<br />
management, detection and response to<br />
EDUCATION, EDUCATION,<br />
a data breach is proving to be an on-going<br />
EDUCATION! 19<br />
question. But whatever the approach<br />
Cybersecurity needs to be a priority for<br />
taken, an intelligence-driven strategy is<br />
the education sector, argues Adrian Jones,<br />
CEO of Swivel Secure<br />
an essential part of that process<br />
GDPR: OPPORTUNITY, NOT THREAT 22<br />
GDPR has increased demand for data<br />
protection processes that are flexible,<br />
autonomous and easy to use. Debbie<br />
Garside, Group Chief Innovation Scientist<br />
at Shearwater Group and CEO of Geolang,<br />
THE STATE WE’RE IN 26<br />
explains how the regulation is helping<br />
The energy sector, communications and<br />
industrial organisations are all at risk of<br />
MASTERCLASS 28<br />
attack from nation states and other<br />
The spotlight this issue falls on Paul Harris,<br />
malicious actors. But it goes much deeper<br />
CEO, Pentest Ltd, A Shearwater Group plc<br />
company, who explains the many benefits<br />
than that. The economy itself is vulnerable,<br />
that Open Source Intelligence (OSINT) can<br />
with UK banks right in the firing line<br />
deliver in the on-going battle against<br />
cyber attacks<br />
ENDPOINT DETECTION & RESPONSE 33<br />
Keith Maskell, Titan Data Solutions, takes<br />
a close-up look at what he sees as an<br />
CRITICAL MASS 30<br />
important new concept in distribution -<br />
Critical asset owners increasingly have to<br />
EDR and Packaged SOC Services<br />
protect their ICT infrastructures against<br />
cyber attacks. It's no longer enough for the<br />
supplier of a single machine component or<br />
PRODUCT REVIEWS<br />
subcomponent to claim it is cyber-secure -<br />
Webroot Business Endpoint Protection 15<br />
the entire machine must be so<br />
Safetica Data Loss Prevention 18<br />
computing security July/August 2019 @CSMagAndAwards www.computingsecurity.co.uk<br />
4
p ent est<br />
INFORMATION SECURITY ASSURANCE<br />
think outside<br />
the tick box<br />
Information security professionals know that a tick box<br />
approach isn’t going to keep their organisation safe.<br />
The job of protecting an organisation is never done and<br />
it requires long-term strategies, as well as constant<br />
improvement efforts.<br />
At Pentest we think outside the tick box, that’s why our<br />
services are designed to not only uncover your IT security<br />
vulnerabilities, but to support ongoing information security<br />
efforts, to pass on our years of expertise and ultimately<br />
to increase the digital resilience of your organisation.<br />
So, are you looking for more than just a tick in the box<br />
when it comes to your information security?<br />
./penetration_testing<br />
./red_teaming<br />
./security_consultancy<br />
call us today on 0161 233 0100<br />
or email contact@pentest.co.uk<br />
www.pentest.co.uk
editor's focus<br />
LEADING SCALE-UPS BOOST CYBER SECURITY FUTURE<br />
TWENTY FAST-GROWTH CYBER SCALE-UPS HAVE BEEN ACCEPTED ON TO THEIR FIRST<br />
NATIONAL CYBER SECURITY GROWTH PROGRAMME - AND THEY MEAN BUSINESS<br />
Funded by the Department for<br />
Digital, Culture, Media and Sport<br />
(DCMS) and supported by global<br />
cyber security market-leaders Tessian,<br />
Digital Shadows, Darktrace and<br />
CensorNet, the newly launched 'Tech<br />
Nation Cyber' project is aimed at<br />
helping to accelerate the growth of the<br />
UK's most promising cyber security<br />
businesses.<br />
Jeremy Hendy, RepKnight.<br />
Andrew Martin, Dynarisk.<br />
It must be said that the breadth of<br />
innovation and application amongst<br />
the 20-strong cohort is testament to<br />
the UK's cyber security and broader<br />
technology sectors. From machine<br />
learning and blockchain, to biometrics<br />
and cloud solutions, these companies<br />
are utilising advanced technologies to<br />
offer clients what they regard as<br />
important new ways to improve<br />
security, and protect businesses and<br />
individuals online.<br />
The companies will benefit from a<br />
series of workshops held across the UK,<br />
led by industry leaders such as Digital<br />
Shadows co-founder James Chappell,<br />
Darktrace co-founders Emily Orton and<br />
Dave Palmer, and Deep3 co-founder<br />
and CEO Richard Yorke. The six-month<br />
programme will also include meet-ups<br />
and networking support to help the<br />
scale-ups navigate common barriers to<br />
growth, with guidance on everything<br />
from how to recruit the right talent<br />
to meeting goals for international<br />
expansion. It will also provide them<br />
with a powerful network of peers,<br />
investors and potential clients.<br />
Ollie Bone, Tech Nation.<br />
Joe Boyle, Salt DNA co-founder and CEO.<br />
Following the call for applications<br />
earlier this year, the successful cohort<br />
was chosen by a panel of expert judges<br />
06<br />
computing security July/August 2019 @CSMagAndAwards www.computingsecurity.co.uk
editor's focus<br />
from the public and private sector. The<br />
judges assessed applicants against their<br />
growth record to date, current scaling<br />
plans and expertise, and long-term<br />
business potential (both nationally and<br />
internationally).<br />
Of the 20 businesses joining the<br />
programme, 45% are based outside of<br />
London, with cohort headquarters<br />
located in nine different cities across the<br />
UK. Kicking off at the Farncombe Estate<br />
in the Cotswolds from 2-3 May, the<br />
programme was launched by marketleading<br />
experts within the cyber security<br />
space, with speakers including Dave<br />
Palmer, director of technology at<br />
Darktrace, James Chappell, founder<br />
and chief innovation officer at Digital<br />
Shadows, and James Hadley, CEO of<br />
Immersive Labs.<br />
Margot James, Minister for Digital and<br />
the Creative Industries, points to the<br />
depth of tech talent right across the<br />
country represented by this select group.<br />
"This important scheme will not only<br />
allow promising cyber security start-ups<br />
to access world-class expert advice, but<br />
also help us achieve our aim of making<br />
Britain the safest place in the world to<br />
be online."<br />
Karen Bradley MP, Secretary of State<br />
for Northern Ireland, comments: "I am<br />
delighted that Belfast-based companies<br />
SaltDNA and RepKnight will be joining<br />
the Tech Nation Cyber programme.<br />
Cyber security is one of the fastestgrowing<br />
digital tech sectors in Northern<br />
Ireland and attracts record levels of<br />
global investment. There is tremendous<br />
talent on offer and world-class<br />
universities, which make Northern<br />
Ireland the ideal location for fast-growth<br />
tech companies. I look forward to seeing<br />
SaltDNA and RepKnight go from<br />
strength to strength and help cement<br />
the UK as a world leader in<br />
cybersecurity."<br />
David Mundell, Secretary of State for<br />
Scotland, has this to say: "Scotland's<br />
reputation as an innovator in technology<br />
is world renowned and I'm delighted to<br />
see us leading the way in cyber security.<br />
Finding ways to fight cyber threats<br />
is one of the world's most pressing<br />
problems and Glasgow's tech sector has<br />
the innovation and experience to be on<br />
the front line. The UK Government has<br />
even chosen the city to host its CyberUK<br />
2019 conference. I am pleased to see<br />
this recognised by Tech Nation and<br />
I offer my congratulations to My1Login<br />
on being chosen to join their first<br />
national cyber security growth<br />
programme."<br />
Kevin Foster, UK Government Minister<br />
for Wales, states: "Cyber security<br />
represents an increasingly important<br />
part of our daily lives, and Wales already<br />
plays a leading role in keeping our data<br />
and systems safe while training up<br />
the next generation of experts. This<br />
programme will initially support two<br />
Welsh companies in Caerphilly and<br />
Cardiff in developing their potential<br />
and I look forward to seeing other<br />
companies from across Wales getting<br />
involved in the future."<br />
Ollie Bone, cyber programme lead at<br />
Tech Nation: "In recent years, the success<br />
for a handful of UK Cyber Security<br />
innovators is more than could be<br />
imagined. They have enhanced the<br />
nation's reputation for producing worldclass<br />
technology, while also helping to<br />
pave the way for many more start-ups<br />
hoping to follow suit. Concurrently, the<br />
market for cyber security is continuing to<br />
grow at a rapid pace and this conspires<br />
to make our cohort of scaleups exciting<br />
ones to watch."<br />
Poppy Gustafsson, CEO and cofounder,<br />
Darktrace, states: "Cyber<br />
security is one of the biggest challenges<br />
facing modern society. Cutting-edge<br />
innovations are the only way to protect<br />
our digital infrastructures and safeguard<br />
the services we rely on."<br />
Tim Sadler, CEO, Tessian: "There is a<br />
tremendous amount of cyber talent in<br />
the UK - made clear by the breadth of<br />
innovation represented in this cohort.<br />
The cyber industry is, however, a noisy,<br />
competitive space. To stand out and<br />
succeed, cybersecurity start-ups need<br />
to demonstrate credibility and clearly<br />
communicate the problem their<br />
technology solves."<br />
Alastair Paterson, co-founder and CEO,<br />
Digital Shadows: "Cyber security is<br />
critical to the UK's future success and<br />
prosperity and an area we can excel in<br />
as a country. As such, I'm proud to<br />
be using my experience with Digital<br />
Shadows to help others to scale up<br />
globally."<br />
Douglas Orr, CEO and founder,<br />
Novastone Media, comments: "The<br />
opportunity for Novastone to scale up<br />
and become a future leader in UK Cyber<br />
Security with the support of Tech Nation<br />
is absolutely fantastic. We're looking<br />
forward to building relationships and<br />
learning from other experts that will<br />
no doubt be crucial to our success."<br />
Jonathan Pope, CEO and co-founder,<br />
Corax, states: "As a UK cyber security<br />
start-up seeking to scale, the timing and<br />
intent of the programme is perfect for<br />
Corax and we're looking to benefit from<br />
the advice and reach of Tech Nation and<br />
fellow programme participants."<br />
Peter Szyszko, CEO and founder, White<br />
Bullet Solutions, also chips in: "Following<br />
a strong start-up period, we are ready<br />
to scale, and excited to take advantage<br />
of the vast opportunities that the<br />
programme offers for growth and access<br />
to investment, as well as to learn from<br />
experts and peers."<br />
www.computingsecurity.co.uk @CSMagAndAwards July/August 2019 computing security<br />
07
industry leaders<br />
FULLY IN THE FLOW<br />
DOCUMENT LOGISTIX USES DAST TO ENSURE<br />
SECURITY OF SENSITIVE CUSTOMER DATA<br />
Tim Cowell, Document Logistix:<br />
customers understand we are serious<br />
about protecting their data.<br />
Document Logistix provides awardwinning<br />
workflow software that<br />
manages the lifecycle of<br />
information from capture, through rulesbased<br />
workflow, retention automation<br />
and, finally, destruction.<br />
Historically, software security was not a<br />
topic that was often raised by potential<br />
purchasers. However, today enterprises<br />
and compliance-conscious buyers are<br />
asking for detailed testing information in<br />
their RFTs.<br />
Tim Cowell, Document Logistix CTO, says:<br />
"We invested in dynamic testing to give us<br />
added credibility with customers by raising<br />
the question of security first. It becomes<br />
a non-issue, because they understand<br />
we're serious about our duty to protect<br />
their data."<br />
Document Logistix document<br />
management software powers the<br />
operations of some of the world's most<br />
demanding, high-volume businesses,<br />
including major logistics companies like<br />
DHL, CEVA and Fedex/TNT. Customers<br />
entrust Document Logistix with handling<br />
their sensitive information, so security is<br />
a high priority.<br />
Document Logistix looked for a higher<br />
level of confidence in its application<br />
security testing, and appointed WhiteHat<br />
Security to secure its DevOps environment<br />
and automate its processes. Document<br />
Logistix uses WhiteHat for static<br />
application security testing (SAST) and<br />
dynamic application security testing<br />
(DAST). Cowell explains: "Our application is<br />
basically a portal for sharing documents.<br />
It's not a banking application - we don't<br />
store credit card information - but<br />
document management can be equally, if<br />
not more, vulnerable to people trying to<br />
gain access to things they shouldn't see."<br />
Document Manager is highly<br />
customisable for a large range of business<br />
processes. This could be for something<br />
as simple as proof of delivery or for more<br />
sensitive information, like HR records,<br />
where there is potential for people to see<br />
records they should not be viewing. The<br />
issue has been heightened since the EU's<br />
General Data Protection Regulation (GDPR)<br />
came into effect.<br />
While protecting customers' data has<br />
always been a priority for Document<br />
Logistix, through encryption, permissions<br />
and redaction, it has now implemented<br />
a true solution for testing its application's<br />
security. In the past, some clients<br />
performed their own penetration testing<br />
and submitted any issues to Document<br />
Logistix. The company also did manual<br />
code checks for security vulnerabilities,<br />
which was intensive and costly.<br />
"The biggest problem was the huge<br />
unknown. Our customers are high profile<br />
and high risk. We needed a solution that<br />
gave us a better process," says Cowell.<br />
"With DAST, we have confidence in saying<br />
to our customers: 'This is what was done<br />
to make your information more secure,'<br />
and they know that, every time there's a<br />
new application build, it gets a new test.<br />
We do three to four releases a year and<br />
testing is very expensive, so performing<br />
testing on each release isn't practicable.<br />
This is a cost-effective solution, because<br />
the testing process is ongoing."<br />
ABOUT DOCUMENT LOGISTIX<br />
Document Logistix won the prestigious Document Manager publication's award for the 2018 Product of the Year: Workflow and<br />
BPM. Since 1996, Document Logistix has supplied its uniquely flexible and scalable Document Manager software to diverse SMEs<br />
and blue-chip clients around the globe. The company's UK and EMEA operations are headquartered in Milton Keynes, UK, which<br />
is also the central point of product development, technical support and training. The US branch of the company is headquartered<br />
in Austin, Texas, and has major contracts with the Texas Department of Public Safety, the Virginia State Police, attorneys and<br />
various agencies in other states.<br />
Tel: 01908 366 388 www.document-logistix.com<br />
08<br />
computing security July/August 2019 @CSMagAndAwards www.computingsecurity.co.uk
True multi-factor authentication<br />
with AuthControl Sentry ®<br />
A choice of ten methods of authenticating<br />
Single sign-on and risk-based authentication<br />
as standard<br />
Scan the QR code<br />
to see how easy it is<br />
to create a custom<br />
MFA chain.<br />
Available for on-premise or cloud environments<br />
Uses patented PINsafe ® technology for unparalleled<br />
security<br />
Deployed in over 52 countries and implemented across enterprises including finance, government, healthcare, education, and<br />
manufacturing, AuthControl Sentry ® provides organisations with true multi-factor authentication, delivering an intelligent<br />
solution to prevent unauthorised access to applications and data. swivelsecure.com
GDPR<br />
GDPR BARES ITS TEETH<br />
WITH THE ONE-YEAR ANNIVERSARY OF GDPR COME AND GONE - AND THE FIRST FEW HEFTY FINES NOW<br />
IMPOSED BY THE REGULATORS - WE LOOK AT WHAT IT ALL MEANS FOR THE FUTURE OF THE INDUSTRY<br />
The General Data Protection Regulation<br />
(GDPR) shook things up in a way that<br />
hadn't been seen in a long time. More<br />
specifically, it signalled the biggest overhaul of<br />
EU data protection law in more than 20 years.<br />
The GDPR replaced what had been the current<br />
EU Data Protection Directive to create a unified<br />
data protection legislation covering all<br />
individuals in the European Union. It affected<br />
any business which had access to, or<br />
processed, the personal data of an EU<br />
resident, regardless of where the business<br />
was located, inside or outside the EU.<br />
It arrived more 'softly, softly' than with a snarl,<br />
perhaps suggesting that its teeth had been<br />
pulled before it was ever liberated from the<br />
cage. Indeed, many thought the GDPR was<br />
more about handbags at dawn, rather than<br />
real action. Administrative fines for companies<br />
may, in the most serious cases, go up to a<br />
maximum of 20 million or 4% of annual<br />
global turnover (whichever is greater), which<br />
may amount to billions of euros for the tech<br />
giants, in addition to other sanctions such as<br />
orders to halt data processing.<br />
"While the fines issued during the GDPR's<br />
first year have been much less than such<br />
maximum amounts - for example, Google was<br />
fined 50 million by the French CNIL, far<br />
below the maximum of approximately 3<br />
billion - data protection authorities, such as<br />
that of Ireland, have warned of fines to come<br />
being "substantial," says TBS Business School<br />
Law Professor Gregory Voss. "That we haven't<br />
seen more large fines to date is due in part<br />
to the GDPR fines only applying to data<br />
protection violations since May 25, 2018,<br />
and the fact that it takes time to conduct<br />
investigations." However, with a couple of big<br />
hitters now in the stocks over breaches of<br />
GDPR, the tide may be turning. First up to be<br />
targeted was British Airways. The ICO's<br />
announcement on 8 July that it plans to fine<br />
the company £183.39m in relation to its<br />
high-profile data breach has sent a very clear<br />
message that the data enforcement landscape<br />
has well and truly changed. The fine relates to<br />
a cyber incident notified to the ICO by British<br />
Airways in September 2018 - and would be by<br />
far and away the largest fine handed out by a<br />
European data protection authority (at least as<br />
I write now! - Ed).<br />
HITTING THE SPOT<br />
"It is interesting to note that British Airways<br />
owner IAG released an announcement to<br />
the market and the ICO has issued its press<br />
release, despite the fact the ICO's intention to<br />
10<br />
computing security July/August 2019 @CSMagAndAwards www.computingsecurity.co.uk
GDPR<br />
fine is preliminary," states Ashley Hurst, partner<br />
and head of tech, media and comms at<br />
international legal practice Osborne Clarke.<br />
"Historically, fines were announced once the<br />
final decision regarding the amount of that<br />
fine was reached. It may be that the size of<br />
the proposed fine and the listed status of<br />
British Airways was such that there was no<br />
choice but for IAG to publicly announce the<br />
size of the intended fine."<br />
The proposed fine will also provide<br />
encouragement for a rapidly growing group<br />
of claimant personal injury lawyers looking<br />
to bring post-data breach claims for<br />
compensation, he adds. "It is often difficult to<br />
attribute a data breach to a breach of the<br />
GDPR and even more difficult to prove that<br />
such a breach has led to damage and distress,<br />
so it will be interesting to see whether the ICO<br />
will make any comment about this."<br />
Over the last year, speculation has been rife<br />
regarding the approach that the ICO will take<br />
to fines. "It is now clear that the ICO will not<br />
be gradually scaling up from its previous<br />
£500,000 maximum: the proposed<br />
£183.39m penalty is equal to 1.5% of British<br />
Airways' worldwide turnover of £12,226m in<br />
2017," adds Hurst. "This is substantially less<br />
than the possible maximum GDPR fine of 4%<br />
of worldwide annual turnover, but still<br />
startling and demonstrates more than ever<br />
that cybersecurity needs to stay on the board<br />
agenda." Prior to this announcement, the total<br />
value of all fines issued under the GDPR across<br />
all EU member states had amounted to 56<br />
million euros. This includes a 50 million euro<br />
fine by the French DPA (CNIL) against Google<br />
for what the CNIL considered to be a lack of<br />
transparency, inadequate information and<br />
lack of valid consent, in relation to Google's<br />
use of personal data for the purposes of<br />
personalising advertisements.<br />
And Osborne Clarke’s Hurst adds: "When the<br />
decision is finally published, this case should<br />
provide some long-awaited clarity regarding<br />
the ICO's exercise of its enforcement powers<br />
and, in particular, what it considers to be<br />
'appropriate technical and organisational<br />
measures' to protect personal data, which is<br />
the key technical standard littered throughout<br />
the GDPR."<br />
ANOTHER BIG TARGET<br />
Following on from the BA debacle, Marriott is<br />
next up, as it also faces a huge data fine: £99<br />
million for allegedly failing to protect customer<br />
data. The hotel chain acknowledged in a<br />
regulatory filing in July this year that Britain's<br />
Information Commissioner's Office intends to<br />
impose the fine under the GDPR.<br />
Jake Moore, Cybersecurity Specialist at ESET,<br />
had this to say in the wake of the news<br />
breaking: "Well, the snowball has surely<br />
started to gain momentum now and this just<br />
highlights that it's not just UK companies at<br />
risk of eye-watering fines either. Other firms<br />
who suffered from large breaches post-May<br />
25, 2018, better start saving, because the ICO<br />
Gregory Voss, TBS Business School: the<br />
relatively low levels of GDPR fines is a<br />
reflection of the time it takes to conduct<br />
investigations.<br />
Jake Moore, ESET: other firms who suffered<br />
from large breaches post-May 25, 2018,<br />
better start saving, because the ICO clearly<br />
means business.<br />
FALLING SHORT<br />
For Jason Hart, cybersecurity evangelist, Thales, GDPR hasn't improved data<br />
protection to the extent many in the industry had hoped. "With the number of<br />
breaches being reported dramatically increasing, it's clear the threat of fines and<br />
a potential hit to their reputation is only having a small impact on how seriously<br />
businesses take their cybersecurity. Worse, just a tiny percentage of the attacks can<br />
be considered 'secure breaches', where the stolen data is encrypted, rendering<br />
it useless to cybercriminals. Unless businesses are made to adhere to GDPR<br />
recommendations such as encrypting data directly it will continue to have minimal<br />
impact in the UK."<br />
www.computingsecurity.co.uk @CSMagAndAwards July/August 2019 computing security<br />
11
GDPR<br />
clearly means business." Interestingly, these<br />
firms' attacks were by no means the largest, in<br />
terms of numbers for 2018. "This could, in<br />
fact, be the tip of the iceberg of what is to<br />
come," he warns, "but let's hope others are<br />
taking copious amounts of notes as to how to<br />
handle a breach or, better still, evade the<br />
attacks as best they can in the first place."<br />
ENSURING CONSENT<br />
As Rob Allen, director marketing & technical<br />
services at Kingston Technology Europe, rightly<br />
points out, the only noticeable effect of the<br />
EU's General Data Protection Regulation<br />
(GDPR) legislation for most people has been<br />
having to click through tedious popups about<br />
data sharing and cookies on just about every<br />
website. "There's a good reason why they're<br />
appearing," he says.<br />
"One aspect of GDPR is that it compels<br />
organisations to notify users about how their<br />
personal data is handled, which very much<br />
includes all the information that modern web<br />
browsers hoover up. Consent is required for<br />
that data to be shared externally, and all<br />
possible technical measures must be otherwise<br />
taken to safeguard personal information<br />
stored on the organisation's network - or<br />
there's the potential for extremely strong<br />
financial penalties."<br />
So, the news that British Airways was hit by<br />
a potential £183 million fine by the ICO<br />
comes as a sharp reminder that GDPR will be<br />
enforced and failure to comply does have<br />
consequences. "So far, this is the largest GDPR<br />
fine that a UK company has faced. But<br />
although the fine is bad news for BA,<br />
the managers and bosses of other UK<br />
organisations that have been scrambling to<br />
meet the requirements of the legislation may<br />
breathe a little easier, knowing that the time,<br />
effort and cost they have invested into data<br />
security has been done for a good reason," he<br />
states. "And, let's face it, before the changes to<br />
GDPR, many of us had acquired some dreadful<br />
habits when it came to handling data, and<br />
tightening things up wasn't exactly a priority<br />
for many firms."<br />
If you're not paying attention, it's all too easy<br />
for data to end up in the wrong hands,<br />
perhaps because a device is lost or a third<br />
party gets unrestricted access to it, Allen<br />
adds. "Any improvement requires both<br />
organisational and technical changes to keep<br />
data secure. Improving company mindset by<br />
educating a workforce, better information<br />
management and risk management play as<br />
much of a part in secure handling of data as<br />
technological solutions. Ultimately, though,<br />
the use of strong encryption is the foundation<br />
that ensures data is always protected, whether<br />
it's stored on the firm's own devices or<br />
otherwise. That applies to business networks,<br />
company servers, removable devices, and all<br />
internal storage on company laptops."<br />
For an IT manager to sleep well at night,<br />
suggests Allen, they need to be certain that<br />
the next time a company laptop is inevitably<br />
left in a hotel, or a USB stick is misplaced,<br />
it's near impossible that mission-critical<br />
information can be prised from it. "They need<br />
to know that no passwords are stored<br />
anywhere in plain text. They need to know<br />
that employees understand not to email<br />
company documents back home using<br />
personal email accounts, store them on an<br />
unencrypted laptop or rely on unsanctioned<br />
third-party cloud services.<br />
"These examples of changes to business<br />
behaviour aren't necessarily complicated, so<br />
complying with GDPR doesn't have to require<br />
moving heaven and earth. Arguably, the<br />
examples we've suggested are merely good<br />
practice anyway and GDPR is rewarding<br />
organisations that already had solid data<br />
management measures in place, before it<br />
became law to do so," he concludes.<br />
BREACHES RACKING UP<br />
"Hefty fines and reputational damage haunted<br />
businesses in the build-up to the passing of<br />
the General Data Protection Regulation,"<br />
recalls Martin Warren, cloud solutions<br />
manager, EMEA at NetApp. "We all know by<br />
now that data security and privacy are, in fact,<br />
two different, complementary issues and, with<br />
the number of data breaches racking up this<br />
year, we are facing the evolving reality of data<br />
security in a world where we essentially live<br />
digital-first lives.<br />
"In a world in which our data and its privacy<br />
are paramount, data security ensures the front<br />
door is bolted shut; data privacy, meanwhile,<br />
requires data management processes with<br />
privacy-by-design at its core." While data<br />
security is certainly important for businesses,<br />
encryption and data masking will not help a<br />
business become GDPR compliant, he adds.<br />
CULTURE CHANGE<br />
"GDPR has succeeded in increasing the profile of data protection within most organisations," says Robert O'Brien,<br />
CEO MetaCompliance. "Changing the culture of privacy by design and privacy by default will take organisations<br />
a significant time to deploy. There is still a long way to go for most companies.<br />
"It's still early to comment on the impact of GDPR in delivering enforcement. There has not yet been the flurry of<br />
financial sanctions that many people feared. The ability of the regulator to stop an organisation processing data might<br />
become a more powerful and effective tool than fines in the future." However, he does see GDPR as the gold standard<br />
for privacy worldwide. "This can be seen in the construction of the Brazilian and the Californian privacy directives."<br />
12<br />
computing security July/August 2019 @CSMagAndAwards www.computingsecurity.co.uk
case study<br />
"Equally, it does not help companies if they<br />
secure data they are not legally allowed to<br />
have. Therefore, GDPR is not just an IT issue.<br />
The compliance process needs to be led from<br />
the C-suite down, as a legal and business<br />
concern before a technology one - we might<br />
have hoped that this massive shift in mindset<br />
would be more evident almost a year on."<br />
Large-scale data breaches from trusted<br />
companies are now perceived with more<br />
clarity by consumers, who are awake and<br />
more aware of their data rights, suggests<br />
Warren. "This only makes the reputational risks<br />
of non-compliance more significant."<br />
WIDER IMPACT<br />
What is happening with GDPR and its<br />
growing influence though punitive action in<br />
Europe is one thing - but how has it impacted<br />
other national data protection regulations?<br />
"GDPR has emerged as the new standard for<br />
data privacy and has directly influenced similar<br />
regulations in other parts of the world, such as<br />
LGPD in Brazil and CCPA in the State of<br />
California," says Jonathan Deveaux, comforte<br />
AG. "In addition, the European Commission<br />
has reached an agreement of reciprocal<br />
adequacy with Japan, meaning that data<br />
subjects in the EU enjoy the same protections<br />
in Japan and vice versa.<br />
"Most recently, Thailand passed their own<br />
Personal Data Protection Act, which will go<br />
into effect in May 2020. "As this global trend<br />
continues, more and more organisations will<br />
be looking into cross-regulatory compliance<br />
strategies, in order to synergise their<br />
investments into complying with overlapping<br />
data privacy laws around the globe."<br />
RULES OF THE GAME<br />
It's a theme that Wim Nauwelaerts, privacy<br />
and cybersecurity partner at Sidley Austin,<br />
expands on. "Under the GDPR, EU data<br />
protection law applies when personal data<br />
is processed in the context of the (business)<br />
activities of a controller's or processor's<br />
establishment in the European Union (EU).<br />
This rule applies, regardless of whether or not<br />
the data processing takes place in the EU. For<br />
example, a pharmaceutical company with<br />
headquarters in France sponsors a clinical trial<br />
in Bangladesh and receives (coded) study data<br />
from the Bangladeshi site. Although the data<br />
processing takes place in Bangladesh, it is<br />
carried out in the context of the activities of<br />
the sponsor/controller established in France.<br />
Therefore, the provisions of the GDPR apply<br />
to such processing."<br />
Even if a company is not established in the<br />
EU, the GDPR can still apply, if the company<br />
(a) 'targets' individuals in the EU by offering<br />
them products or services; or (b) 'monitors'<br />
their behaviour, in as much as that behaviour<br />
takes place in the EU.<br />
TARGETING AND MONITORING<br />
"Since the GDPR came into effect last year,<br />
there has been confusion around the<br />
targeting and monitoring criteria, and how to<br />
apply them in practice. For companies that<br />
have no physical presence in the EU, but are<br />
receiving personal data relating to individuals<br />
in the EU, it is not always clear whether their<br />
data processing activities fall within the ambit<br />
of the GDPR," Nauwelaerts states.<br />
"On November 23, 2018, the European Data<br />
Protection Board (EDPB) published draft<br />
guidelines, with a view towards addressing<br />
the lack of clarity around the territorial scope<br />
of the GDPR (Guidelines). The guidelines<br />
explain, for instance, that a key element for<br />
the application of the targeting criterion is<br />
whether the conduct of the controller or<br />
processor demonstrates its intention to offer<br />
goods or services to an individual located in<br />
the EU. In other words, the targeting criterion<br />
can only apply, if controllers/processors outside<br />
of the EU have manifested their intention to<br />
establish (commercial) relations with<br />
individuals - mostly consumers - in the EU."<br />
Regarding the monitoring criterion, the<br />
guidelines consider that a broad range of<br />
monitoring activities through various types of<br />
Jonathan Deveaux, comforte AG: GDPR<br />
has emerged as the new standard for data<br />
privacy and has directly influenced similar<br />
regulations in other parts of the world<br />
Martin Warren, NetApp: data security<br />
ensures the front door is bolted shut.<br />
www.computingsecurity.co.uk @CSMagAndAwards July/August 2019 computing security<br />
13
GDPR<br />
Rob Allen, Kingston Technology Europe:<br />
GDPR is rewarding organisations that<br />
already had solid data management<br />
measures in place.<br />
Wim Nauwelaerts, Sidley Austin: even if<br />
a company is not established in the EU,<br />
the GDPR can still apply.<br />
networks and technologies could bring data<br />
processing under the scope of the GDPR, as<br />
long as the monitored behaviour takes place<br />
within EU territory. "The guidelines provide the<br />
example of an Indian pharmaceutical<br />
company without a business presence or<br />
establishment in the EU, which sponsors<br />
clinical trials carried out by sites in Belgium,<br />
Luxembourg, and the Netherlands. Since trial<br />
participants in these EU countries are being<br />
'monitored', the sponsor in India is arguably<br />
subject to the GDPR."<br />
It's a highly complex issue, no better<br />
demonstrated than by the fact that the<br />
guidelines were open for public consultation<br />
until January 18, 2019 and expected to be<br />
finalised shortly afterwards. "However, during<br />
the public consultation, many stakeholders<br />
raised questions about the interaction<br />
between the provisions in the GDPR around<br />
territorial scope and Chapter V of the GDPR,<br />
which deals with data transfers outside of the<br />
EU," explains Nauwelaerts.<br />
"For instance, whether data transfer<br />
safeguards, such as model contracts that have<br />
been pre-approved by the European<br />
Commission, should be put in place vis-à-vis<br />
controllers/processors outside the EU that are<br />
subject to the GDPR, because the targeting or<br />
monitoring criterion is met. The guidelines<br />
currently fail to address these questions. At<br />
this point, it is still unclear when the EDPB will<br />
publish its finalised guidelines and to what<br />
extent they will include guidance on the<br />
GDPR's data transfer restrictions."<br />
ABOVE AND BEYOND<br />
GDPR alone will not keep personal data<br />
secure, of course, as Richard Blanford, chief<br />
executive, Fordway, emphasises. "GDPR<br />
may be part of every organisation's business<br />
practices, but has it really made personal data<br />
more secure? In my view, the answer is no.<br />
I believe GDPR is a business issue. It has<br />
ensured organisations know where they hold<br />
Personally Identifiable Information (PII), and<br />
have controls in place for how they store, use<br />
and delete that data through what should be<br />
a clearly defined and well-understood policy,<br />
with appropriate business processes to ensure<br />
compliance.<br />
"However, GDPR does not address the actual<br />
security of an organisation's networks and the<br />
devices on which they store and access PII. So,<br />
if their perimeter is breached, GDPR is<br />
meaningless. And with data increasingly going<br />
outside an organisation as employees and<br />
partners tunnel through or bypass network<br />
perimeters, good cyber security discipline is<br />
more vital than ever."<br />
KEY DISCIPLINES<br />
According to Blanford, data security really<br />
requires four key disciplines: identity and<br />
authentication management; information<br />
lifecycle management; network security; and<br />
business continuity planning. "To develop an<br />
effective data security policy, organisations<br />
need to take a holistic look at their entire<br />
infrastructure, from how data is created or<br />
acquired to how it is valued, stored, accessed<br />
and disposed of," he advises.<br />
"This includes data that comes in from<br />
customers, partners and suppliers as well as<br />
data created internally. They also need to<br />
consider their users. No technology or<br />
regulation will be effective, unless all<br />
employees adhere to security procedures.<br />
"This means educating users on why security<br />
matters, the consequences of getting it wrong<br />
and what to do, if the worst happens. They<br />
are much more likely to comply, if they<br />
understand the risks, rather than simply seeing<br />
security as a set of annoying rules which<br />
prevent them working as they wish. Achieving<br />
recognised security standards such as Cyber<br />
Essentials, ISO27001 and ISO20000, will help<br />
an organisation improve its security and,<br />
importantly, reassure its customers that it has<br />
done so."<br />
See page 20 for another expert take on GDPR<br />
and its impact.<br />
14<br />
computing security July/August 2019 @CSMagAndAwards www.computingsecurity.co.uk
product review<br />
WEBROOT BUSINESS ENDPOINT PROTECTION<br />
Webroot takes data security to<br />
the next level, as its Business<br />
Endpoint Protection teams up<br />
multi-vector protection with cloud-based<br />
machine learning. It delivers real-time<br />
threat detection and prevention for<br />
physical and virtual endpoints, while its<br />
SaaS (software as a service) model allows<br />
multiple sites to be cloud managed from<br />
a single pane of glass.<br />
Deployed as a small-footprint agent, it<br />
uses embedded deep learning intelligence<br />
to analyse end user activity to detect<br />
threats and block them. The agent<br />
functions as a sensor and sends back all<br />
information to the cloud service as data<br />
points, allowing it to adapt instantly to<br />
zero-day threats.<br />
It's very easy to install and we had<br />
no problem deploying it in the lab on<br />
our physical and virtual Windows<br />
workstations and Windows Server<br />
systems. The agent is preconfigured for<br />
your account and we found it could be<br />
installed and providing full protection<br />
in minutes.<br />
The agent runs an initial endpoint scan,<br />
links up with your cloud account and<br />
takes its settings from the default policy,<br />
so there's nothing more to do on each<br />
one. Other features we like are that the<br />
agent can be run transparently and it<br />
won't conflict with other endpoint security<br />
solutions - many competing products<br />
insist on uninstalling them before their<br />
agent can run.<br />
The cloud console is well designed and<br />
MSPs will approve of its site view, as they<br />
can manage all their customers from one<br />
console. It provides a complete overview<br />
of all detected threats, along with direct<br />
access to Webroot's optional DNS<br />
protection and security awareness training<br />
services.<br />
The endpoint protection console is<br />
equally informative and presents a status<br />
overview, clearly showing detected threats<br />
and the affected endpoints where you can<br />
drill down deeper for more information.<br />
The left pane provides a quick link to all<br />
current threats where we could view<br />
associated endpoints and run quick<br />
one-click clean up jobs.<br />
If the agent detects a new executable,<br />
it'll class it as unknown, track all the<br />
changes it makes and send back data<br />
points to the cloud where the results are<br />
analysed in real-time. A valuable feature is<br />
Webroot's journaling as, if it determines<br />
the threat is real, it'll roll back all changes<br />
made on the endpoints automatically.<br />
Custom polices can be easily created<br />
and even a quick glance at their features<br />
shows where Webroot's strengths are, as<br />
they offer remarkable levels of protection.<br />
Along with setting agent behaviour and<br />
self-protection, these provide access to<br />
scan schedules, automatic remediation,<br />
threat analysis heuristics, real-time,<br />
behaviour and core system shields, and<br />
much more.<br />
The web shield protects against<br />
malicious and phishing web sites, while<br />
the identity shield offers features such as<br />
denial of malicious tracking cookies,<br />
DNS verification to prevent man-in-the<br />
middle attacks and even screen capture<br />
prevention. We created custom policies<br />
for our Windows workstations and an<br />
agent is also available for Mac systems,<br />
which uses the same policies, so there's<br />
no need to create separate ones. Groups<br />
allowed us to organise our various<br />
endpoints for easier management, and<br />
policies can be assigned to groups or<br />
individual endpoints on-demand.<br />
Threat detection alerts are assigned<br />
to email distribution lists, which can<br />
also be used to send out regular threat<br />
summaries.<br />
Webroot provides a good range of<br />
reporting tools and MSPs will love its<br />
web-based API, as they can<br />
extract endpoint protection information<br />
and use it in other third-party remote<br />
management tools.<br />
Webroot's Business Endpoint Protection<br />
gets our vote of confidence, as it is easy<br />
to deploy and delivers the toughest<br />
of security measures. Its slick cloud<br />
management console is perfect for<br />
MSPs and SMEs alike, while its flexible<br />
per-device monthly and yearly<br />
subscriptions offer unbeatable value.<br />
Product: Business Endpoint Protection<br />
Supplier: Webroot<br />
Website: webroot.com/ComputingSecurity<br />
Tel: +44 (0)800 804 7016<br />
www.computingsecurity.co.uk @CSMagAndAwards July/August 2019 computing security<br />
15
financial focus<br />
WHO CAN YOU REALLY BANK ON?<br />
THOSE WHO RELY ON THEIR ONLINE BANK TO KEEP THEIR MONEY SAFE MIGHT BE ALARMED<br />
TO HEAR THAT LAST YEAR 54% OF THESE INSTITUTIONS ALLOWED ATTACKERS TO STEAL MONEY.<br />
AND THEIR CUSTOMER DATA MAY BE EQUALLY AT RISK<br />
In its recent report, 'Vulnerabilities in<br />
online banking applications', Positive<br />
Technologies experts assessed the<br />
security levels of online banks in 2018<br />
and found that 54% allowed attackers<br />
to steal money. Equally concerning is<br />
that all online banks carry the risk of<br />
unauthorised access to personal data<br />
and other sensitive information,<br />
according to the findings.<br />
The analysis shows that most online<br />
banks are worryingly exposed. "A security<br />
assessment of online banks revealed<br />
that every reviewed system contained<br />
vulnerabilities that could have major<br />
consequences if exploited. For instance,<br />
fraudulent transactions and theft of<br />
funds were possible in 54 per cent of<br />
applications," says the company.<br />
Threat of unauthorised access to client<br />
information and company sensitive<br />
information, such as account statements<br />
or the payment orders of other users,<br />
was present in every studied online<br />
bank, and, in some cases, vulnerabilities<br />
allowed hackers to attack the bank's<br />
corporate network.<br />
According to Positive Technologies'<br />
experts, the average cost of the data of<br />
16<br />
computing security July/August 2019 @CSMagAndAwards www.computingsecurity.co.uk
financial focus<br />
an online banking user on the darkweb<br />
is $22. Additionally, analysis showed that<br />
77% of online banks had security flaws<br />
in their two-factor authentication<br />
mechanisms.<br />
Positive Technologies' cybersecurity<br />
resilience lead Leigh-Anne Galloway<br />
comments that some online banks do<br />
not use one-time passwords for critical<br />
operations (such as authentication) or<br />
allow old passwords, which are more<br />
likely to be compromised. Experts believe<br />
this is because banks want to strike the<br />
right balance between security and<br />
comfort of use.<br />
"Foregoing security measures in favour<br />
of customer convenience increases the<br />
risk of fraud," she states. "If there's no<br />
need to confirm a transaction with a<br />
one-time password, the attacker no<br />
longer requires access to the victim's<br />
smartphone, and an old password<br />
increases the chances of it being brute<br />
forced. With no limit applied to it,<br />
a one-time password of four symbols<br />
can be cracked within two minutes."<br />
READY-MADE PROVES UNREADY<br />
As well as issues of authentication,<br />
comparative analysis showed that readymade<br />
solutions developed by vendors<br />
had three times fewer vulnerabilities<br />
than those developed in-house. The<br />
number of vulnerabilities in the test<br />
and production systems, on the other<br />
hand, is equal.<br />
Statistics suggest that, in 2018, both<br />
types of systems in most cases contained<br />
at least one critical vulnerability. Experts<br />
think that, after developers have tested<br />
a security system once, they tend to<br />
postpone further analysis once changes<br />
hve been made to the code, causing<br />
vulnerabilities to 'accumulate'. This<br />
means that, before long, the number of<br />
flaws is the same as that found during<br />
initial testing.<br />
The main positive trend to emerge<br />
regarding the security of online financial<br />
applications in 2018 was the reduction<br />
of high-risk vulnerabilities in the total<br />
number of all flaws identified. According<br />
to Positive Technologies' specialists, "the<br />
percentage of critical vulnerabilities<br />
dropped by more than half, compared<br />
to the previous year - from 32% in 2017<br />
to 15% in 2018". However, the overall<br />
security level of online banks remains low<br />
- and that has to change fast.<br />
Solutions have a platform<br />
At the leading international trade fair for<br />
IT security, experts will answer all questions on<br />
artificial intelligence and IT security.<br />
Get your free ticket for it-sa 2019!<br />
it-sa.de/it-security4U<br />
Nuremberg, Germany 8 -10 October 2019
product review<br />
SAFETICA DATA LOSS PREVENTION<br />
Data leak prevention (DLP) is now<br />
an essential security measure for<br />
businesses, but a major concern<br />
for many is the lengthy deployment<br />
processes for some products. Safetica's<br />
DLP solution avoids these problems, as<br />
it's designed to be easily installed and<br />
fully operational in as little as one day.<br />
Safetica generates detailed security<br />
audit reports, revealing potentially<br />
unwanted or unsafe activities, who is<br />
accessing sensitive data and what they<br />
are doing with it. You can see how and<br />
where files are being transferred, the<br />
most active apps and users, potentially<br />
risky apps, IT resource usage and an<br />
analysis of web activity, all accompanied<br />
by security advisories.<br />
It uses a client-server architecture<br />
where the backend management<br />
services can be installed on a Windows<br />
Server host in less than an hour. These<br />
services are resource light, so Safetica<br />
doesn't require a dedicated host system<br />
and, once up and running, you can go<br />
straight to endpoint agent service and<br />
client deployment.<br />
Active Directory (AD) structures are<br />
imported into Safetica and Group Policy<br />
can be used to push the agent service to<br />
endpoints, after which they'll appear in<br />
the main console, ready to receive the<br />
client software. Once loaded, the clients<br />
passively monitor endpoints and send<br />
back information about user activity to<br />
the Safetica server.<br />
The amount of detail is remarkable, as<br />
the Safetica Auditor can show storage<br />
and removable device usage, active<br />
applications and their traffic, web site<br />
accesses, along with data usage and<br />
visit durations, plus all printing jobs.<br />
Trends show areas such as web<br />
browsing and social network habits,<br />
while advanced monitoring reveals all<br />
email and file activity.<br />
Two consoles are provided where the<br />
WebSafetica browser version displays<br />
daily overviews of activity and provides<br />
basic admin access. The desktop console<br />
facilitates access to advanced settings,<br />
the Auditor, DLP policy creation and the<br />
Supervisor access controls.<br />
The Supervisor module manages user<br />
activity and allows you to decide<br />
precisely what they can and can't do.<br />
Policies control areas such as removable<br />
device access permissions or web<br />
content filtering where you can choose<br />
from a range of URL categories, block<br />
or allow them and add multiple rules<br />
for more granular browsing controls.<br />
Data access is controlled by the DLP<br />
module where you create policies<br />
to protect sensitive data against<br />
unauthorised access and ensure users<br />
with access granted don't abuse their<br />
privileges. Along with context-based<br />
rules, the module offers content rules,<br />
which are easy to use as they identify<br />
sensitive data using algorithms,<br />
dictionaries, keywords and regular<br />
expressions.<br />
Content rules dynamically detect<br />
specific information inside files, emails,<br />
attachments, within apps such as IM<br />
and more. These are applied in data DLP<br />
policies, but you can also use others to<br />
define applications and communication<br />
channels, such as email.<br />
Zones group resources together, which<br />
can be external devices, storage areas,<br />
emails, network paths or a list of IP<br />
addresses, and are referenced by a<br />
policy as a single entity, so you can<br />
easily define trusted and untrusted<br />
zones. Disk Guard controls read and<br />
write access to local, network, plus<br />
cloud storage, and Safetica has<br />
management of Windows BitLocker<br />
for encrypting USB flash drives.<br />
Templates streamline DLP policy<br />
creation, so it's possible to create one<br />
and deploy it in as few as three clicks.<br />
Controls are highly granular, as you<br />
can even stop users taking screenshots<br />
of an application, if the view contains<br />
confidential information or using<br />
keyboard cut and paste commands.<br />
Safetica shows that implementing and<br />
enforcing DLP doesn't need to be timeconsuming<br />
or complex. It can show you<br />
everything you need to know about your<br />
data security posture in a few hours and<br />
easily achieve regulatory compliance.<br />
Product: Data Loss Prevention<br />
Supplier: Safetica Technologies<br />
Web site: www.safetica.com<br />
Tel: +44 (0)203 846 8416<br />
Sales: safetica@datasolutions.co.uk<br />
18<br />
computing security July/August 2019 @CSMagAndAwards www.computingsecurity.co.uk
inside track<br />
EDUCATION, EDUCATION, EDUCATION!<br />
CYBERSECURITY NEEDS TO BE A PRIORITY FOR THE EDUCATION SECTOR,<br />
ARGUES ADRIAN JONES, CEO OF SWIVEL SECURE<br />
Adrian Jones, CEO of Swivel Secure.<br />
Education institutions need to make<br />
cybersecurity a priority. Despite the<br />
sector facing major challenges,<br />
such as a lack of staffing, funding and<br />
resources, cyberattacks are no less<br />
frequent or less severe in education. In<br />
fact, they seem to be gaining ground in<br />
prevalence year-on-year, as instances of<br />
breaches in schools and higher education<br />
are widely reported.<br />
THE CHALLENGES EDUCATION IS<br />
FACING<br />
The JISC report also investigates the<br />
challenges facing IT professionals when it<br />
comes to protecting education networks.<br />
When asked to rate how well their<br />
institution is protected on a scale from 1<br />
(not at all) to 10 (very well), further<br />
education scored lower overall than<br />
higher education. The mean score for<br />
further education institutions was 5.9,<br />
while higher education scored 7.1.<br />
The rationale behind lower scores<br />
included:<br />
A lack of resources and budget -<br />
potentially pointing to the lack of<br />
finances to invest in cybersecurity, be<br />
it software or staff<br />
Cultural issues - a 'Bring Your Own<br />
Device' culture is common in<br />
educational institutions and can<br />
present difficulties in securing the<br />
wider network, particularly with IT<br />
staff already facing stretched resources<br />
An absence of policy - setting out<br />
policies for using the network and<br />
making sure they're adhered to can be<br />
difficult in large institutions with a<br />
dynamic user population.<br />
Despite these challenges, the education<br />
sector is still expected to secure their<br />
networks against unauthorised access and<br />
cyber threats, especially when the<br />
repercussions can be as severe as the<br />
examples discussed earlier.<br />
But there are some critical steps every<br />
institution should undertake to lay the<br />
foundations for a secure IT network.<br />
TOP TIPS FOR SECURING YOUR<br />
EDUCATION IT NETWORK<br />
With the challenges of poor funding and<br />
a lack of resources, the Education sector<br />
should focus their efforts on minimising<br />
the risk of a cyberattack, rather than a<br />
reactive attitude after one has happened.<br />
Training: providing basic training for all<br />
users of your network is one way to<br />
mitigate the effects of a lack of funding<br />
and resource. This can be something as<br />
simple as sharing a handbook with staff<br />
and students, including information about<br />
what to look out for and tips for<br />
practising good cybersecurity hygiene.<br />
Giving people the necessary information<br />
to protect the network at all access points<br />
could reduce the number of incidents<br />
caused by human error.<br />
Authentication: another cost-effective<br />
way to protect the safety of your<br />
institution and its students is to<br />
implement a user-friendly multi-factor<br />
authentication (MFA) tool. Including that<br />
extra security step for users who are<br />
logging onto the network will help<br />
prevent unauthorised access. An easy-touse<br />
platform should be high on your list<br />
of things to look for in an MFA provider.<br />
If users can use a platform self-sufficiently,<br />
there's less likely to be a need for<br />
administrative support, so education<br />
facilities can save on overheads, without<br />
compromising network security.<br />
These are just some of the cost-effective<br />
ways to protect your school, university or<br />
college from any form of unauthorised<br />
access. With the increasing frequency and<br />
potential severity cyberattacks pose to the<br />
education sector, it's crucial that IT<br />
professionals can work to find a solution<br />
to challenges like a lack of funding.<br />
www.computingsecurity.co.uk @CSMagAndAwards July/August 2019 computing security<br />
19
data-centric economy<br />
GDPR - OPPORTUNITY, NOT THREAT<br />
GDPR HAS INCREASED DEMAND FOR DATA PROTECTION PROCESSES THAT ARE FLEXIBLE,<br />
AUTONOMOUS AND EASY TO USE. DEBBIE GARSIDE, GROUP CHIEF INNOVATION SCIENTIST<br />
AT SHEARWATER GROUP AND CEO OF GEOLANG, EXPLAINS<br />
Debbie Garside, Group Chief Innovation<br />
Scientist at Shearwater Group and CEO<br />
of Geolang.<br />
Since GDPR came into force,<br />
businesses handling personal<br />
data have turned their attention<br />
to processes that protect sensitive<br />
information by design and by default.<br />
This was a key innovation in the<br />
legislation and has extended data<br />
protection from a technical issue to<br />
a matter of process and psychology<br />
at all levels of the business; including<br />
every employee by default.<br />
In a data-centric economy, identifying<br />
and categorising different types of data<br />
is an enormous task. The Information<br />
Commissioner's Office (ICO) expects<br />
enterprises to know where sensitive data<br />
is located and to take steps to prevent<br />
its theft, loss or unauthorised access;<br />
yet, over a year on, and still many<br />
organisations are failing to implement<br />
even the simplest 'technologies' to assist<br />
with the task.<br />
Reportedly, 96 per cent of data<br />
breaches are accidental; however,<br />
breach-reporting deadlines and<br />
potential fines apply, regardless. With<br />
the reported £183 million penalty<br />
indication for the BA data breach from<br />
the ICO this week, these penalties are<br />
no longer a figment of what might be,<br />
but indicate, rather, what will be, if<br />
organisations do not take care of<br />
their data - board-level culpability will<br />
undoubtedly ensue. This will serve<br />
as the much-needed catalyst to fully<br />
support those CISOs, CTOs and CIOs<br />
who are still having difficulty persuading<br />
boards of the risk not just to their data,<br />
but to the business as a whole.<br />
As a data discovery and data protection<br />
company, GeoLang has seen increased<br />
demand for our systems, because we find<br />
and categorise data both autonomously<br />
and in real time, with the flexibility to<br />
apply different policies to different data.<br />
This prevents - for example - the emailing<br />
of a client contact list to the wrong<br />
recipient or alerts if any proprietary<br />
information is copied to a USB drive. In<br />
addition, flexibility and ease to search for<br />
personally identifiable information (PII)<br />
across the enterprise is key to servicing<br />
Subject Access Requests (SARs) and we are<br />
seeing a plethora of requests for GeoLang<br />
technologies to assist in such cases.<br />
Each client has a different set of<br />
requirements, with many different<br />
operating systems and repositories making<br />
up the average enterprise. A flexible, agile<br />
approach is a necessity and we work hand<br />
in hand with clients in the development<br />
and deployment of our solutions; there<br />
is no 'one size fits all' or a 'silver bullet'<br />
solution, and our personalised service<br />
is proving to be both an asset to our<br />
customers and to us, as it supports our<br />
product development lifecycle.<br />
One of the fears in the lead-up to GDPR<br />
was that the regulations would decrease<br />
productivity, tying up businesses with<br />
extra administrative work. The reality<br />
is somewhat different. Increased<br />
opportunities for innovations around<br />
technologies that protect sensitive<br />
data and clients' rights are offset by<br />
organisational and digital resilience that<br />
future-proofs the enterprise, leading to<br />
increased competitiveness and growth.<br />
20<br />
computing security July/August 2019 @CSMagAndAwards www.computingsecurity.co.uk
Webroot empowers businesses with predictive technology, and simplifies IT<br />
admin life with single-pane-of-glass management. Our integrated next-gen<br />
cybersecurity solutions cover endpoints, networks, and end user education<br />
to help businesses and MSPs close security gaps, so they can focus on what<br />
they do best: growing profitably.<br />
We can easily manage 5000+ endpoints with<br />
Webroot. The low footprint and cloud-based<br />
management make this our security platform<br />
of choice.<br />
Sam Reed, CTO, Air IT - UK<br />
Visit webroot.com/ComputingSecurity to try next-gen<br />
Webroot ® Business Endpoint Protection free for 30 days.
threat intelligence<br />
THREAT OR TREAT<br />
HOW ORGANISATIONS SHOULD BEST MANAGE,<br />
DETECT AND RESPOND TO A DATA BREACH IS AN<br />
ON-GOING QUESTION. BUT AN INTELLIGENCE-DRIVEN<br />
STRATEGY IS AN ESSENTIAL PART OF THAT<br />
Security vendors should be applauded in<br />
many ways for their ability to take<br />
technology and security best practice<br />
that has been around for a long time, give<br />
it a fancy new name, and sell it as the new<br />
magic bullet, says David Peters, CTO,<br />
ANSecurity.<br />
"Cyber Threat Intelligence is one such<br />
instance that, although it offers some<br />
benefits, is not a new concept and can be<br />
accomplished in more than one fashion.<br />
Even the most basic security controls, such as<br />
desktop anti-virus, use threat intelligence in<br />
the form of signature updates, URL blacklists<br />
are the same, even the regular advisories to<br />
patch applications and operating systems are<br />
effectively threat intelligence messages."<br />
Many of the new breed of cyber threat<br />
intelligence (CTI) offerings are rather<br />
expensive, he adds, but there are alternatives<br />
that are effectively free. "For example,<br />
AlienVault open threat exchange, when<br />
coupled with Palo Alto's Minemeld, can<br />
create a potent threat intelligence platform<br />
that can take both open source alerts and<br />
paid-for services to be fed into an effective<br />
system. This combination can feed dynamic<br />
firewall rules that can block known IP<br />
addresses which are host threat actors.<br />
Building your own is feasible for most IT<br />
professionals and does not need a deep<br />
infosec background."<br />
FIRING ON ALL CYLINDERS<br />
Where some of the CTI systems can shine is<br />
in the more specialist areas, such as Critical<br />
National Infrastructure, very large enterprises<br />
and organisations that use SCADA. "However,<br />
this is a realm where CTI should be used<br />
alongside a dedicated SoC and analyst as an<br />
aid, rather than a replacement for skilled<br />
infosec professionals, Peters advises.<br />
"Even in this space, there are national<br />
resources, such as GCHQ, which do sterling<br />
work in providing threat intelligence that<br />
both these more critical groups and other<br />
enterprises would be wise to regularly<br />
consult."<br />
ATTACK TOOLS AT LARGE<br />
"With the increased availability of highquality,<br />
open-source attack tools, cyber<br />
aggressors can constantly evolve and utilise<br />
automated attack tools, points out Chris<br />
Doman, security researcher at AT&T Alien<br />
Labs. "For an organisation trying to defend<br />
itself from a barrage of these assaults, it can<br />
all become too much to handle, especially<br />
when you consider that security teams are<br />
already understaffed and overstretched.<br />
So, what can security professionals and<br />
organisations alike do to defend against<br />
these attacks?<br />
First, Doman advises, start by fighting<br />
fire with fire. "If cybercriminals are using<br />
automation to their advantage, then so<br />
should organisations. Some tasks remain the<br />
preserve of humans - but there are still many<br />
simple time-consuming tasks that can be<br />
automated. This can alleviate the strain for<br />
security personnel who can fixate their time<br />
on more concerning matters." Secondly, share<br />
threat intelligence. "The last few years, we<br />
22<br />
computing security July/August 2019 @CSMagAndAwards www.computingsecurity.co.uk
threat intelligence<br />
have seen an improvement in governments,<br />
vendors and companies being more open to<br />
sharing threat information. By sharing<br />
intelligence, we are seeing faster detection<br />
and better prevention of known threats.<br />
In addition, for those without the in-house<br />
expertise, seek a dedicated team or a SOC<br />
to continuously monitor the organisation's<br />
environment. This will give the business<br />
insight into what is happening across the<br />
entire network. The threat intelligence<br />
developed with each investigation will assist<br />
the security team in making the correct<br />
decisions when it comes to preventing future<br />
attacks."<br />
By building a united front and utilising near<br />
real-time threat data, he says, "businesses<br />
can strengthen their own defences, while<br />
also helping others to make life more difficult<br />
for hackers, which is what sharing threat<br />
intelligence is all about".<br />
INTELLIGENCE-DRIVEN ACTIONS<br />
Cyber security has certainly become a high<br />
priority for senior management, according to<br />
78% of businesses that responded to the UK<br />
government's 'Cyber Security Breaches Survey<br />
2019'. While it is encouraging that this figure<br />
has risen year on year, generating awareness<br />
of cyber security is only one part of the issue.<br />
"The next step for organisations to take is not<br />
only understanding, but intelligently acting<br />
on the risks presented," argues Andy Pearch,<br />
head of IA Services at CORVID. "Despite the<br />
heightened awareness, many organisations<br />
are still focusing on mitigating assumed risks,<br />
rather than real risks, without a robust<br />
security strategy in place."<br />
The 2019 breaches survey revealed that, in<br />
the last 12 months alone, almost one third<br />
of UK businesses identified cyber security<br />
breaches or attacks. "What's more, the<br />
research also showed that just under half<br />
of these companies identified at least one<br />
breach or attack per month," says Pearch.<br />
"While these figures should be enough to<br />
make a business refocus its strategic security<br />
thinking, it is the use of the word 'identified'<br />
that is significant: many more attacks could<br />
have occurred, but not yet been discovered."<br />
Indeed, global figures reveal that the<br />
median dwell time - the time a criminal can<br />
be on a company's network undetected - is<br />
more than 100 days. "And, in many cases,<br />
the breach is not revealed by the security<br />
team itself; it is a call from a supplier, a<br />
customer or business partner that brings the<br />
problem to light, typically following the<br />
receipt of a diversion fraud email requesting -<br />
for example, that future payments should<br />
be sent to a different bank account."<br />
Such breaches not only have the ability to<br />
undermine business relationships, but, in<br />
some cases, can also incur significant<br />
financial liability. "These frauds usually follow<br />
one of two forms: either impersonation,<br />
where a criminal masquerades as the<br />
business, using a very similar domain name<br />
and email address; or, following a successful<br />
compromise, the email comes from the<br />
company's own system. It is the latter case<br />
that raises the issue of liability for any<br />
financial losses a business partner may have<br />
suffered."<br />
ATTACK MINDED<br />
In the battle against sophisticated<br />
cyberattacks, defenders must innovate, if<br />
they wish to remain one step ahead of the<br />
latest threats. To do so, cybersecurity<br />
professionals need real-time, actionable<br />
intelligence about the threat landscapes they<br />
face, says Nilesh Dherange, CTO of Gurucul.<br />
"Threat intelligence solutions provide data<br />
that lets security personnel make informed<br />
decisions about their defences. With threat<br />
intelligence technology, organisations can<br />
know who is attacking them, what their<br />
motivations are and what they are trying to<br />
accomplish. With this knowledge, they can<br />
remedy the threat."<br />
Moreover, to make informed decisions,<br />
context is key. "Without proper context,<br />
David Peters, ANSecurity: creating<br />
a potent threat intelligence platform<br />
doesn't have to be expensive.<br />
Nilesh Dherange, Gurucul: with threat<br />
intelligence technology, organisations can<br />
know who is attacking them, what their<br />
motivations are and what they are trying<br />
to accomplish.<br />
www.computingsecurity.co.uk @CSMagAndAwards July/August 2019 computing security<br />
23
threat intelligence<br />
threat intelligence is an unruly cascade of<br />
alerts that no human can effectively monitor.<br />
Too many alerts lead to alert fatigue, not<br />
answers. Some conventional threat<br />
intelligence systems, like security incident and<br />
event management (SIEM), don't generate<br />
the data required for delivering actionable<br />
intelligence. The result is too many 'false<br />
positives' - urgent security warnings that turn<br />
out to be empty threats. According to our<br />
survey at RSA Conference 2019, false<br />
positives are the biggest hurdle in maximising<br />
the value of a SIEM solution."<br />
Dherange references a study produced by<br />
Enterprise Management Associates that<br />
revealed 79% of security teams are<br />
overwhelmed by the volume of threat alerts.<br />
"Like the fable about the boy who cried<br />
wolf, too many false positives can result in<br />
warnings simply being ignored. A famous<br />
example of alert fatigue leading to a<br />
cyberattack is the infamous 2013 Target<br />
breach that affected more than 40 million<br />
customers. According to post-breach analysis,<br />
the security group kept seeing the same, false<br />
malware alert before the attack. Eventually,<br />
those warnings were ignored, even as the<br />
real intrusion occurred." To remedy the<br />
situation, he adds, a solution is needed that<br />
can provide the proper context by quickly<br />
analysing new alerts, removing false positives<br />
and generating real-time data about current<br />
threats. "Modern threat intelligence solutions<br />
use behaviour analytics, powered by machine<br />
learning, to automate data collection and<br />
provide risk-prioritised intelligence. Advanced<br />
machine-learning algorithms provide a<br />
holistic view of all log data and expose<br />
suspicious activity.<br />
"These machine-learning models can predict<br />
insider threats, account compromise and<br />
data exfiltration by identifying users and<br />
entities that are acting in risky 'abnormal'<br />
ways, compared to peer-group behaviour.<br />
Most organisations already use multiple<br />
security tools, which produce meaningful log<br />
data. Applying behaviour analytics and data<br />
science to those sources to examine user<br />
access and behaviour is the logical next step."<br />
HUMAN EXPERTISE<br />
To become relevant and actionable,<br />
intelligence must be customised. It's not just a<br />
case of switching on a few threat data feeds.<br />
"Intelligence needs to be developed over time,<br />
with human expertise playing a key role<br />
in this," comments Azeem Aleem, VP<br />
Consulting, NTT Security. "It is an intelligencedriven<br />
holistic security process that may result<br />
in a few mistakes along the way, but that<br />
should not distract you from the ultimate<br />
goal."<br />
The five steps he suggests to attain the Holy<br />
Grail of actionable intelligence are:<br />
Business and risk alignment -<br />
understanding the mission, scope<br />
and authority needed to mitigate risk<br />
Visibility - define the visibility required<br />
to achieve mission readiness<br />
Content - build enablement for detection,<br />
including use cases, situational awareness<br />
and baseline<br />
Security operations - respond, contain<br />
and hunt to achieve the mission of<br />
rooting out known and unknown threats<br />
Applied intelligence and analytics -<br />
analyse, attribute and predict threats to<br />
refocus the mission.<br />
"The key is to first understand what your<br />
organisation's key assets - or 'crown jewels' -<br />
are via a risk analysis," adds Aleem. "Then<br />
filter out the 'noise' to prioritise intelligence<br />
relevant to your business. You can then move<br />
forward to proactively hunt for threats, map<br />
attack patterns and outline the black hats'<br />
tactics, techniques and procedures (TTPs). By<br />
pre-empting the bad guys, you can take the<br />
initiative back to manage cyber and business<br />
risk on your own terms."<br />
MOBILISING YOUR DEFENCES<br />
As more of our daily interactions move to mobile and other handheld devices, our cyber risk is growing exponentially.<br />
"Even Gartner has predicted that, by 2020, 80% of work tasks will take place on mobile devices," points out Tom Davison,<br />
pictured right, EMEA technical director at post-perimeter security companyLookout. "Today, the deployment of mobile<br />
devices, across the enterprise, has introduced a host of new cyber threats and led to the disappearance of the perimeter,<br />
as employees are able to access the corporate network from anywhere."<br />
Threat intelligence is a must for any organisation, of course. "However, to truly have confidence in the defence of the<br />
business, there needs to be visibility across the entire asset base, including mobile devices," argues Davison. "A dedicated<br />
mobile endpoint security solution can contribute directly to the overall threat intelligence picture, while also protecting sensitive<br />
assists when accessed by devices outside the business perimeter. This is particularly crucial in our now post-perimeter security world.<br />
"With humans often regarded as the weak link in security, fortifying technology with education is also paramount to give employees within the<br />
organisation a truer understanding of the mobile threat landscape," he adds. "With a number of hackers and cybercriminals groups operating, its<br />
time businesses upped their resilience levels and post-perimeter security is key to efficiently protect the corporate border, while still giving secure<br />
access to critical data. "<br />
24<br />
computing security July/August 2019 @CSMagAndAwards www.computingsecurity.co.uk
12th edition of the most recognized and influential<br />
cyber security business forum in Scandinavia.<br />
2019 Main Focus Areas<br />
Cybersecurity<br />
Data Protection and GDPR<br />
Identity and Access Management<br />
IoT and Network Security<br />
Mobile and Cloud Protection<br />
Hacking Democracy by Hacking Minds<br />
60 Nordic and international speakers presenting on 5 stages in 9<br />
agenda streams and 5 C-Level industry panel discussions<br />
Is 14th of November 2019 marked in your schedule?<br />
Registration is now open!<br />
For more information, visit our website at www.nordicitsecurity.com<br />
or email us at info@itstechbook.com
cyber espionage<br />
THE STATE WE'RE IN<br />
IT ISN'T JUST THE ENERGY SECTOR, COMMUNICATIONS AND INDUSTRIAL ORGANISATIONS<br />
THAT ARE AT RISK OF ATTACK FROM NATION STATE AND OTHER MALICIOUS ACTORS.<br />
THE ECONOMY ITSELF IS VULNERABLE, WITH UK BANKS RIGHT IN THE FIRING LINE<br />
Malicious actors are targeting critical<br />
national infrastructure (CNI) sites<br />
and energy distribution facilities on<br />
a growing scale. Interconnected systems in<br />
the energy industry are greatly increasing<br />
vulnerabilities, while cyber-attacks often go<br />
undetected for some time.<br />
As energy companies save costs against the<br />
backdrop of lower oil prices, consolidating<br />
operations can weaken business resilience<br />
and redundancy levels. This gives rise to new,<br />
single critical points of failure, with any<br />
disruption across the supply chain potentially<br />
having increased consequences.<br />
"Espionage and sabotage attacks against<br />
CNI organisations have increased over the<br />
years and I don't think we have seen it all<br />
yet," says Sami Ruohonen, labs threat<br />
researcher at Finnish cyber security company<br />
F-Secure.<br />
Connecting Industrial Control Systems (ICS)<br />
to the Internet is increasing, and many CNI<br />
systems in use today were installed and built<br />
before 24/7/365 internet connections were<br />
the norm - and the advent of Stuxnet. Many<br />
Operational Technology (OT) components<br />
have built-in remote operation capabilities,<br />
but are either partly or entirely lacking in<br />
security protocols such as authentication.<br />
Moreover, cyber security was not a realistic<br />
threat when these systems were<br />
manufactured, and legacy protocols and<br />
systems never had the built-in security<br />
controls that we take for granted today.<br />
Transitioning these systems to the Internet<br />
has opened them up to attacks from a<br />
myriad of angles.<br />
"Critical infrastructure, due to its nature, is<br />
an interesting target for a foreign nationstate,<br />
even during peacetime," Ruohonen<br />
adds. F-Secure's report makes the following<br />
points:<br />
A variety of adversaries, each with<br />
their own motivations and tradecraft,<br />
constantly strive to compromise<br />
organisations that operate critical<br />
infrastructure<br />
Attackers have more time than their<br />
targets and will take months to plan<br />
their attack<br />
People are the weakest link in production,<br />
with company employees seemingly<br />
being criminals' go-to target<br />
Attackers continue to succeed, mainly<br />
due to organisations' lack of mature<br />
cyber security practices<br />
Nation-state sponsored Advanced<br />
Persistent Threat (APT) groups are<br />
relentless, and continue to seek network<br />
foothold positions on CNIs and espionage<br />
opportunities, in the interests of<br />
exercising political leverage<br />
Nine attackers/malwares/techniques<br />
targeting the energy industry stand out,<br />
with spear phishing being the most<br />
common initial supply chain attack<br />
technique<br />
Keeping a small attack surface in the<br />
energy industry - while often pitched as<br />
the best way to mitigate the risk of a<br />
cyber-attack - is simply not possible.<br />
While breaches are a certainty, Ruohonen<br />
advises organisations to carefully review their<br />
cyber security posture to implement latest<br />
technologies, such as an endpoint detection<br />
and response (EDR) solution.<br />
"EDR is a quick way to tremendously<br />
increase capabilities to detect and respond to<br />
advanced threats and targeted attacks, which<br />
might bypass traditional endpoint solutions,"<br />
he explains. "Managed EDR solutions can<br />
provide monitoring, alerting, and response<br />
to cover the needs 24/7. This means<br />
organisations' IT teams can operate during<br />
business hours to review the detections,<br />
while a specialised cybersecurity team takes<br />
care of the rest."<br />
IRANIAN CONNECTION<br />
Iran looms large as a source of such attacks,<br />
with a large-scale coordinated cyber assault<br />
on UK infrastructure, which took place in<br />
December last year, attributed to that<br />
country. In the campaign, personal details<br />
were stolen from thousands of employees,<br />
including those working at the Post Office,<br />
major banks and local government.<br />
David Atkinson, CEO of Senseon and ex<br />
cyber operative, describes the incident as<br />
26<br />
computing security July/August 2019 @CSMagAndAwards www.computingsecurity.co.uk
cyber espionage<br />
a "sobering story" that demonstrates how<br />
wide the scope is when we talk about nation<br />
state cyber-attacks. "The temptation is to<br />
think of one government's agency fighting<br />
another," he says. "However, as this story<br />
demonstrates, the reality is that the<br />
battlefield extends beyond that to businesses,<br />
public services and other organisations. In<br />
this case the Post Office, local government<br />
and banks are the victims that were caught<br />
in the crossfire.<br />
"This attack also shows that we need to<br />
change awareness of what constitutes critical<br />
infrastructure. Again, we are not just talking<br />
about the energy sector, communications<br />
and industrial organisations. Threat actors<br />
will also target the economy and, if a largescale<br />
attack is launched against the UK's<br />
banks, you can bet the situation will quickly<br />
become critical. The government has a<br />
responsibility to ensure a good standard of<br />
security and defence across all major<br />
organisations to safeguard the UK."<br />
MASSIVE INVESTMENT<br />
Andy Barratt, UK managing director of<br />
cybersecurity consultancy Coalfire, argues<br />
SOFTWARE: A SOFT TARGET<br />
that Iran's effort to steal sensitive data from<br />
UK public sector organisations "is another<br />
example of a surge in nation-state backed<br />
cyber espionage in recent years". Even a<br />
cursory look at the cyber strategies of<br />
countries around the world - both in Asia<br />
and the West - shows that there is massive<br />
investment in offensive digital capabilities,<br />
he points out.<br />
"It's interesting that Iran is seeking to extract<br />
data, rather than bring down core<br />
infrastructure like other nation-state attacks<br />
have done - North Korea's WannaCry hack,<br />
for example, brought parts of the NHS to a<br />
standstill. It's possible that Iran is being<br />
careful, given the West's penchant for<br />
military activity in the Middle East. But it's<br />
also possible that this was an intelligencegathering<br />
exercise to collect the data needed<br />
for more targeted espionage in the future."<br />
Public sector employees are a good target<br />
for accessing data, if the end goal is to access<br />
government infrastructure, he warns. "The<br />
attack costs are relatively low and a huge<br />
database of potential targets can be built up<br />
quickly."<br />
David Atkinson, Senseon: the battlefield<br />
extends beyond that to businesses, public<br />
services and other organisations.<br />
Andy Barratt, Coalfire: Iran is another<br />
example of a surge in nation-state<br />
backed cyber espionage in recent years.<br />
State hacking campaigns, such as Cloudhopper, that target software<br />
supply companies are incredibly dangerous. "By breaching one company,<br />
you can create a backdoor into thousands of others," cautions Simon<br />
Whitburn, SVP Cyber Security Services at Nominet, pictured above. "The<br />
information gathered from these types of attacks can then be used for<br />
spear phishing attacks on high value individuals, which is where serious<br />
damage can be done.<br />
Defending against this type of campaign can be very tough, he adds. "There is a<br />
feeling amongst users that, if lots of people trust and use a service, then it must be secure.<br />
This can result in companies downloading software without checking it themselves first.<br />
Cloudhopper demonstrates that this is a dangerous assumption. Whenever a company uses<br />
an outside service, even from a reputable source, they need to check that there is nothing<br />
malicious lurking in the code. This will add to the deployment time, but could help protect<br />
organisations against this type of malware spreading. One way of noticing if third party<br />
services have been compromised is to measure DNS traffic, which could flag if a programme<br />
is calling out to a command and control centre."<br />
www.computingsecurity.co.uk @CSMagAndAwards July/August 2019 computing security<br />
27
MASTERCLASS<br />
SOCIAL ENGINEERING AND RED TEAMING:<br />
RISKS, REWARDS AND APPROACHES THAT WORK<br />
PAUL HARRIS, CEO, PENTEST LTD, A SHEARWATER GROUP<br />
PLC COMPANY, EXPLAINS THE BENEFITS THAT OPEN SOURCE<br />
INTELLIGENCE (OSINT) CAN DELIVER IN THE ON-GOING<br />
BATTLE AGAINST CYBER ATTACKS<br />
The report is unequivocal: "Cyber<br />
attackers are increasingly focusing<br />
their attention on people, not technical<br />
defences." Automated or AI-driven<br />
technologies are conducting monitoring<br />
and incident-response with unprecedented<br />
power and speed, yet human users remain<br />
the entry point into networks that most<br />
cyber attackers exploit.<br />
The prevalence of malicious social<br />
engineering means that its inclusion in red<br />
teaming exercises is a standard offering.<br />
The objective is to assess the integrity of a<br />
company's defensive mechanisms, and to<br />
then use these findings to improve overall<br />
security culture and incident response.<br />
But what can mock social engineering<br />
actually reveal about a company's staff?<br />
Performed unethically, or without clear<br />
objectives, mock social engineering could<br />
undermine employee confidence or trust in<br />
management. A certain percentage of staff<br />
will consistently click malicious links or install<br />
misrepresented programs; there's nothing<br />
new to learn here.<br />
ALL COMPANIES CAN BE SOCIALLY<br />
ENGINEERED…THE QUESTION IS HOW?<br />
For some companies, revealing the scenarios<br />
a malicious actor could employ may be a<br />
more valuable exercise. A successful social<br />
engineering campaign is, after all, the result<br />
of research conducted by the attacker into<br />
key business partners, technology stacks,<br />
current deals, or staff changes; everything<br />
that could be used to establish a believable<br />
pretext, gain trust or create a sense of<br />
urgency. Open Source Intelligence (OSINT)<br />
replicates this process, and combined with<br />
expert knowledge of active threat groups,<br />
OSINT analysts can specify the ruses that<br />
attackers might present, or the areas of<br />
corporate policy (social media use, for<br />
example), that need to be tightened.<br />
Companies can take these findings and alert<br />
their employees to emails, phone calls, or<br />
network breaches that attackers (may) have<br />
attempted; pre-emptively warning security<br />
teams and keeping good security policy<br />
(eg, do NOT enable macros) at the forefront<br />
of employees' minds, without an unnecessary<br />
game of 'gotcha'.<br />
SIMULATION, NOT HUMILIATION<br />
The inevitability of social engineering prompts<br />
other companies to focus upon the efficacy<br />
of incident response. Pentest (a Shearwater<br />
Group plc company) has conducted<br />
simulations with selected employees<br />
consenting to be mock-phished and<br />
reporting the incident to internal security.<br />
This approach highlights failures in network<br />
segmentation, communication channels,<br />
or technical ability. After conducting such<br />
exercises, Pentest clients have created new<br />
email addresses (suspicious@company.com),<br />
implemented data backup procedures, or<br />
placed assets behind an internal VPN. If the<br />
worst should transpire, the network and its<br />
first-line defenders can contain the impact<br />
of an attack.<br />
Paul Harris, CEO, Pentest.<br />
KNOWLEDGE IS ALWAYS VALUABLE<br />
Standard social engineering tests may reap<br />
valuable data. Identifying the percentage of<br />
vulnerable employees can inform company<br />
training programs - or evaluate previous<br />
security investments. In these circumstances,<br />
anonymising the results of such tests is the<br />
basis of ethical practice. A company like<br />
Pentest has extensive experience in red<br />
teaming and social engineering, while they<br />
are also adept at presenting the results in<br />
such a way as to protect the identity of<br />
affected employees.<br />
Overall, when considering the inclusion of<br />
social engineering in a red teaming exercise,<br />
identifying the informational outcome that<br />
the company is seeking should be the<br />
primary step. A red teaming provider who<br />
seeks to understand the end goal and design<br />
an exercise appropriately is ideally placed to<br />
conduct mock social engineering in an ethical<br />
manner that maximises its rewards.<br />
28<br />
computing security July/August 2019 @CSMagAndAwards www.computingsecurity.co.uk
CYBER<br />
SECURITY<br />
europe<br />
9-10 October 2019,<br />
ExCeL London<br />
PART OF<br />
DIGITALTRANSFORMATION E PO<br />
PROTECT<br />
DETECT<br />
MITIGATE<br />
REGISTRATION IS NOW OPEN<br />
www.dt-x.io
industrial cyber security<br />
CRITICAL MASS<br />
CRITICAL ASSET OWNERS INCREASINGLY HAVE TO PROTECT THEIR ICT INFRASTRUCTURES AGAINST<br />
CYBER ATTACKS. IT'S NO LONGER ENOUGH FOR THE SUPPLIER OF A SINGLE MACHINE COMPONENT<br />
OR SUBCOMPONENT TO CLAIM IT IS CYBER-SECURE - THE ENTIRE MACHINE MUST BE SO<br />
Quite recently, hacking group<br />
Xenotime reportedly started to probe<br />
industrial control systems of power<br />
grids in the US. Xenotime are the group<br />
behind the infamous Triton malware,<br />
designed to disable safety systems at<br />
petrochemical plants. This malware was<br />
used in December 2017 to attack the safety<br />
systems of an unidentified power station in<br />
Saudi Arabia. Dragos, which specialises in<br />
industrial control system (ICS) security, found<br />
evidence of Xenotime collecting open source<br />
research on targeted electric companies,<br />
externally scanning those companies'<br />
networks and attempting to gain access<br />
through either credential stuffing or stolen<br />
credentials.<br />
"The Trisis malware used in the attack on<br />
Saudi Arabian petrochemical plants and now<br />
recurring in probes conducted against US<br />
industrial control systems is just one example<br />
of the increasingly complex threats posed by<br />
modernising legacy software," says John<br />
Titmus, director EMEA, CrowdStrike. "Across<br />
many of these facilities, previously air-gapped<br />
systems are now being connected to public<br />
internet, in order to make use of internet of<br />
things (IoT) technologies.<br />
"This news highlights the critical importance<br />
of leveraging threat intelligence to mount a<br />
proactive, rather than a reactive,<br />
cybersecurity defence. For groups like<br />
Xenotime, who have proven their capability<br />
at acquiring, reverse engineering and<br />
developing attack packages for industrial<br />
control system equipment, reactive measures<br />
are insufficient to address critical<br />
infrastructure threats," he states.<br />
As supply chain attacks from nation-states<br />
and other cybercriminals persist in plaguing<br />
organisations and government agencies,<br />
the effectiveness of current cyber-security<br />
methods is called into question. "While<br />
individual components may be labelled<br />
as cyber-secure, it only takes a single<br />
vulnerability to compromise the entire supply<br />
chain. To remedy this and improve OT<br />
(Operational Technology) hygiene,<br />
continuous monitoring and enhanced<br />
detection below the OS-level is essential.<br />
Today, most security products remain<br />
blind to attacks that attempt to leverage<br />
vulnerabilities in, for instance, BIOS<br />
firmware. Accessing endpoints in this way<br />
compromises the entire system and can even<br />
persist across reboots and reinstallation of<br />
the operating system."<br />
Titmus believes that firmware and<br />
hardware-level visibility into these<br />
vulnerabilities and attacks is the best option<br />
for protecting the supply chain - and can<br />
even prevent attacks before they have a<br />
chance to take off. "Importantly, this level<br />
of visibility allows cyber security teams to<br />
discover dormant threats that have not yet<br />
been detected. Industrial networks are<br />
particularly at risk to these types of attack,<br />
since their security has often been neglected<br />
for years; malware can spread rapidly from<br />
individual infected devices to the whole<br />
office, to plants in other countries."<br />
30<br />
computing security July/August 2019 @CSMagAndAwards www.computingsecurity.co.uk
industrial cyber security<br />
MULTIPLE CHALLENGES<br />
How do you stop a wave of innovation from<br />
becoming a tsunami? Cyber security<br />
specialists will know this dilemma well,<br />
acknowledges Mike Nelson, VP of IoT<br />
Security, DigiCert. "The IoT promises to<br />
revolutionise not just how we live at home,<br />
but how we do business and, more<br />
importantly, how we provide those critical<br />
resources that society runs on: gas, water,<br />
electricity and so on. Given the opportunities<br />
that are being offered to seemingly every<br />
level of society - who could say no? Then<br />
again, a cyberattack on a Fitbit is a very<br />
different thing to a cyberattack on a water<br />
treatment facility."<br />
Securing each, he adds, will take very<br />
different efforts and before we even start<br />
doing that we're presented with several<br />
problems. "First, critical assets were built for<br />
failure, not attack. The legacy systems that<br />
run those facilities have often been doing<br />
so for many years and were never created<br />
to withstand a cyberattack, let alone an<br />
attempt to penetrate their pitiful security by<br />
the concerted effort of a nation state. As we<br />
fill in the decades-old airgap between critical<br />
assets and the internet, we are introducing<br />
them to a whole environment full of threats<br />
that they are largely unprepared for."<br />
Secondly, there’s the simple, well-known<br />
fact that the IoT is insecure. Just behind the<br />
rapturous applause for the IoT's arrival has<br />
been a quieter, but no less impassioned,<br />
warning about its vulnerabilities, Nelson<br />
states. "Throughout this period, there has<br />
been little oversight - government or<br />
otherwise - as manufacturers have produced<br />
insecure devices and retailers have sold them<br />
on to an eager public. That insecurity could<br />
have to do with the whole device or it could<br />
have been inserted along the often long and<br />
labyrinthine supply chain that these devices<br />
are assembled on. Even if a manufacturer<br />
says their product is secure, there are plenty<br />
of potential points of failure from the factory<br />
floor to the customer's hands."<br />
And we are only beginning to address<br />
these problems now, he says. "A variety of<br />
governments and industry bodies are<br />
attempting to introduce regulation and<br />
standards that seek to protect this wave of<br />
innovation. Though these efforts are<br />
encouraging, they are not going to patch<br />
over mistakes already made and they won't<br />
pay the security debts that have already been<br />
racked up by the over-eager adoption of<br />
insecure technology. Hopefully, the<br />
regulation stick will lead to better, more<br />
standardised, approaches to IoT security."<br />
That insecurity is not going to be solved<br />
soon and new vulnerabilities will always crop<br />
up, but device manufacturers can use<br />
technology available now to protect devices,<br />
suggests Nelson. "Public Key Infrastructures<br />
[PKI] with digital certificates, for example,<br />
are already being used to secure IoT<br />
devices from the factory floor to use<br />
across distributed networks. PKIs' ability to<br />
authenticate device identities, protect the<br />
integrity of code and firmware updates, and<br />
encrypt data are proven to be scalable and<br />
are interoperable. Well-run PKIs can police<br />
the connections between large networks of<br />
devices and that makes them a good fit for<br />
industrial IoT."<br />
MULTIPLE CHALLENGES<br />
The supply chain for IoT products is often<br />
so complex that it's hard to trace - let alone<br />
make reasonable security judgements about.<br />
"Just because a vendor can vouch for the<br />
integrity of its supplier and that supplier can<br />
vouch for the integrity of its manufacturers,<br />
it doesn't mean that trust, or even security<br />
considerations, are present at all of the<br />
critical stages of development," says Scott<br />
Gordon, CMO, Pulse Secure. That problem<br />
becomes bigger when we're talking about<br />
the IIoT (Industrial Internet of Things) - "not<br />
because the supply chain is less trustworthy,<br />
but because human safety is inextricably<br />
linked to cyber security".<br />
Defending these often undependable<br />
devices is just as much of a problem for the<br />
Mike Nelson, DigiCert: critical assets were<br />
built for failure, not attack.<br />
John Titmus, CrowdStrike: firmware and<br />
hardware-level visibility is the best option<br />
for protecting the supply chain.<br />
www.computingsecurity.co.uk @CSMagAndAwards July/August 2019 computing security<br />
31
industrial cyber security<br />
supply chain, as it is a more general problem<br />
about our outdated security mindset. "For<br />
years, we've thought that, if we only build<br />
perimeter walls that are strong enough, we'll<br />
be safe. Then again, 12-foot concrete barriers<br />
don't count for much, if they come with an<br />
unlocked door. Considering the herculean<br />
task of trying to police every device, let<br />
alone components within that device,<br />
organisations are thinking about defence in<br />
new ways. Zero Trust architecture is just one<br />
of them."<br />
Knocking down the tired inside/outside<br />
dichotomy of traditional network security,<br />
Zero Trust does not automatically trust any<br />
device, system or user, states Gordon. "Any<br />
that want to gain access must be verified<br />
according to the resource they want to use<br />
or communicate with, leveraging factors like<br />
user and location to authenticate.<br />
Instead of one wall around the city, Zero<br />
Trust builds walls - and, perhaps more<br />
importantly, watchtowers - around each<br />
Nigel Stanley, TUV Rheinland: to build<br />
cybersecurity into the supply chain, it needs<br />
to be written into contracts with suppliers.<br />
constituent building, further complicating<br />
an attacker's job, providing visibility and<br />
preventing the lateral movement that is so<br />
critical in the cyber kill chain."<br />
This matters more when we realise how the<br />
perimeter is changing, he continues. "New<br />
ways of working, such as BYoD [Bring Your<br />
own Device] are making the perimeter line<br />
on which older generations of security<br />
depended less and less clear. We can no<br />
longer say that a network perimeter ends at<br />
the office door, so it makes sense to employ<br />
strategies which accommodate these new<br />
realities."<br />
Moreover, he points out, we are just now<br />
getting regulations that will force security<br />
into the design stage for many of these<br />
devices. "The UK government, for example,<br />
will finally make its 2018 IoT guidelines<br />
mandatory. While commendable, they won't<br />
necessarily secure those supply chains<br />
entirely and the insecure components that<br />
are already floating around the IIoT will<br />
continue to pose threats. It will never be<br />
good enough to have insecure components<br />
within a device; but it's almost impossible to<br />
make sure of. Trying to wish away that reality<br />
is another version of the security wall fallacy:<br />
'If I can stop it from getting into my<br />
environment, I'll be safe'."<br />
For the moment, IIoT users simply have to<br />
accept that there will always be a risk with<br />
these devices and start thinking about how<br />
they're going to respond, once that insecure<br />
component is already in their environment.<br />
"Until IoT users can rely on these complex<br />
supply chains, "enterprises can look to<br />
concepts like Zero Trust to tackle these<br />
unfortunate realities within the supply<br />
chain, " Gordon concludes.<br />
SECURITY MYTH<br />
The number of cybersecurity- related<br />
incidents in industrial control networks has<br />
risen in every region in recent years, and<br />
there have been well publicised reports of<br />
sophisticated malware and threat actors<br />
disrupting safety instrumented control<br />
systems. On the back of this, says Nigel<br />
Stanley, CTO - Global OT and Industrial Cyber<br />
Security CoE at TÜV Rheinland Group,<br />
organisations operating industrial facilities<br />
have a responsibility to "monitor, detect and<br />
mitigate cybersecurity attacks in order to<br />
maintain the safety, integrity and availability<br />
of their site which, if compromised, may<br />
have a severe and detrimental impact on<br />
society".<br />
HOW SAFE IS ‘SAFE’?<br />
But this is no straightforward task, he<br />
concedes, given that safety-critical systems<br />
can contain thousands of hardware<br />
components and millions of lines of software<br />
code. "When it comes to securing individual<br />
components, there is no such thing as<br />
absolute security. In terms of cybersecurity,<br />
products cannot be proven to be secure, or<br />
measured against an industry accepted<br />
Safety Integrity Level (SIL). Therefore, if<br />
a manufacturer claims their product is<br />
'cybersecure', this should be taken with<br />
a large pinch of salt.<br />
"To satisfy cybersecurity concerns, the most<br />
astute manufacturers or operators tend to<br />
seek security assurance - for example, three<br />
levels down their supply chain. While a good<br />
idea on paper, in reality this is a complex and<br />
time-consuming process for all parties. A<br />
detailed questionnaire can confirm whether<br />
suppliers are compliant with cybersecurity<br />
guidelines, but this is never the full picture."<br />
To really build cybersecurity into the supply<br />
chain, it needs to be written into contracts<br />
with suppliers, states Stanley. "Obliging<br />
software code or a piece of hardware to<br />
undergo official certification against an<br />
accepted standard - such as IEC 62443 - can<br />
be helpful. However, this still doesn't<br />
guarantee that a product is secure; just that<br />
it has met the requirements of a particular<br />
standard at a particular time."<br />
32<br />
computing security July/August 2019 @CSMagAndAwards www.computingsecurity.co.uk
endpoint detection and response<br />
GETTING TO GRIPS WITH ENDPOINT<br />
DETECTION AND RESPONSE<br />
KEITH MASKELL, HEAD OF CYBERSECURITY, TITAN DATA SOLUTIONS,<br />
TAKES A CLOSE-UP LOOK AT WHAT HE SEES AS AN IMPORTANT NEW<br />
CONCEPT IN DISTRIBUTION - EDR AND PACKAGED SOC SERVICES<br />
As companies of all sizes come to<br />
grips with the responsibilities<br />
defined by GDPR, as well as the everworsening<br />
threat landscape in IT security,<br />
the conversation inevitably moves to<br />
'EDR' - endpoint detection and response.<br />
No longer can antivirus protection be<br />
considered a sufficient solution on the<br />
endpoint - on workstations, servers, mobile<br />
devices. When a company realises it is time<br />
to be able to detect the IT security breaches<br />
which may happen at any time, regardless<br />
of the layers of defence implemented,<br />
then it is time for them to consider an<br />
EDR solution. For very many companies, of<br />
many different sizes, that time is right now.<br />
But the world of EDR is not simple to get<br />
to grips with. At the heart of the problem<br />
is the fact that EDR is often dealing with<br />
complicated technical situations which may<br />
be the work of very capable individuals<br />
who have possibly, so far, outwitted the<br />
network and endpoint defences that were<br />
put in place. An EDR solution typically<br />
gathers large amount of highly detailed<br />
event data from the monitored endpoints<br />
and uses analytic processes to extract<br />
combinations of events that, when taken<br />
together, are suspicious. Then the race<br />
is on, to determine whether this particular<br />
alert is really an attack, or perhaps else<br />
a 'false-positive'. No-one wants to be<br />
responsible for shutting down services<br />
or raising alarms, which may cause the<br />
business substantial cost, based on<br />
a false-positive alarm.<br />
ISSUES IN EDR MONITORING<br />
So, there are two tough requirements for<br />
EDR monitoring: firstly, having the right<br />
technical expertise available at the right<br />
time, to make the right decision based on<br />
the EDR alert, and secondly, having people<br />
with the courage to take responsibility for<br />
making the decision, within a suitable work<br />
process framework. Especially taking into<br />
account that this cover has to be on<br />
a 24/7/365 basis to be effective, this<br />
challenge is one step too far for the vast<br />
majority of companies to solve in-house.<br />
If these problems are not truly solved, then<br />
EDR is relegated from being a monitored<br />
alarm system that can help see off attacks,<br />
possibly before any real damage is done, to<br />
being a forensics tool that can help analyse<br />
what happened weeks or months ago,<br />
when an attack took place that was missed<br />
at the time. This is the difference between<br />
stopping the burglar before he can open<br />
the office safe and arriving after the event<br />
to take fingerprints.<br />
One potential solution is the use of<br />
managed services of an external,<br />
independent 'SOC' - security operations<br />
centre. Experts at the SOC can monitor<br />
your EDR system and alert you when<br />
potential breaches are detected.<br />
This may solve the monitoring problem,<br />
but there are three questions: how do you<br />
select the SOC, is it too expensive, and how<br />
do you manage incident response activity<br />
when an alert is received?<br />
www.computingsecurity.co.uk @CSMagAndAwards July/August 2019 computing security<br />
33
endpoint detection and response<br />
MANAGING THE COST<br />
The key to obtaining SOC services at the<br />
right price is to have the choice between<br />
alternative suppliers, or MSSPs - managed<br />
security service suppliers. If an EDR solution<br />
does not provide the possibility of this<br />
customer choice for SOC services, then the<br />
element of competition for the services<br />
element may be lost.<br />
Titan Data Solutions is an IT security<br />
distributor with a difference, because it<br />
believes that its key role is to take the hard<br />
work out of sourcing SOC services for EDR.<br />
Titan Data Solutions works with multiple<br />
SOCs and selects the best options, to<br />
supply Titan packaged SOC services via<br />
its partner base to all types of end-user<br />
organisation. These SOC services include<br />
threat monitoring, remote incident<br />
response by SOC experts, and on-site<br />
incident response.<br />
By sourcing and integrating SOC<br />
packaged services with EDR solutions at the<br />
distributor level, and taking responsibility<br />
for them under its own brand, Titan Data<br />
Solutions provides unique added value.<br />
This translates to affordable pricing for<br />
end users.<br />
For resellers, it is easy to sell these<br />
advanced services like other types of<br />
product, and let Titan Data Solutions, with<br />
its SOC provider, implement the standard<br />
service packages. For 'MSPs' - IT managed<br />
service providers - it can be an impossible<br />
challenge to upskill and increase resources<br />
to provide SOC services on a 24/7 basis,<br />
to meet customer requirements. So,<br />
MSPs can also find Titan Data Solutions'<br />
packaged SOC services an invaluable asset,<br />
to enable them to supply a working EDR<br />
with affordable services, increase their<br />
footprint in the customer and increase<br />
customer loyalty.<br />
AN INTEGRATED FUTURE<br />
Titan Data Solutions believes that, as a<br />
distributor, it is in the perfect position to<br />
source and supply these SOC services. Both<br />
MSPs and resellers may fear that, if they<br />
bring in an MSSP with a SOC directly to<br />
provide these services, then the MSSP may<br />
take over their relationship with their enduser<br />
customer. Titan Data Solutions, on the<br />
other hand, is a distributor and is 100%<br />
committed to its relationships with its<br />
partners - it uses carefully selected SOCs to<br />
provide the services under its own brand,<br />
but Titan Data Solutions will be the supplier<br />
of the services.<br />
So, with the emergence of affordable<br />
packaged SOC services, companies of all<br />
sizes can look afresh at the possibility of<br />
implementing an EDR solution that will<br />
function as a monitored alarm with timely<br />
alerts - including a packaged incident<br />
response service, to assist in analysing<br />
and countering any detected threats.<br />
The future direction of EDR will be for<br />
increased integration with other layers of<br />
IT Security defences, such as antivirus, so<br />
that automated responses to suspected<br />
breaches can become more commonplace.<br />
While many triggered responses are already<br />
available, this can only deal with a limited<br />
subset of use cases for the foreseeable<br />
future. The ingenuity and creativity of<br />
human attackers will require the ingenuity<br />
of human defenders for a significant time<br />
yet to come. Nevertheless, the drive for<br />
cost-competitiveness is likely to strengthen<br />
the trend to increased automated response.<br />
DRIVING FORCE<br />
Consequently, any strategy for EDR should<br />
embrace the future requirement for<br />
increased real-time automated incident<br />
response, driven by the EDR system.<br />
This implies that the EDR system which is<br />
selected should be capable of triggering<br />
defensive responses in the antivirus<br />
endpoint threat prevention system and on<br />
other security layers in the network, to<br />
demonstrate that this facility exists and<br />
can be developed further for the future.<br />
Titan Data Solutions addresses this need<br />
by offering the 'Enterprise Inspector' EDR<br />
system from ESET, together with Dynamic<br />
Threat Defence, to its partners and their<br />
end-users. This EDR system works in<br />
concert with the ESET antivirus system for<br />
endpoint threat prevention. Titan Data<br />
Solutions' packaged SOC services are<br />
supplied for this ESET platform. By tuning<br />
the SOC services to this platform, Titan<br />
Data Solutions can ensure the SOC services<br />
have optimum efficiency and affordability.<br />
EDR is a chameleon: either it is a<br />
monitored alarm that can save your<br />
company, or it is a post-event forensics<br />
tool. Affordable packaged SOC services,<br />
that meet your specific requirements, could<br />
make the difference.<br />
With the right strategy, this will be the<br />
gateway to a future of increased<br />
integration and automated response.<br />
34<br />
computing security July/August 2019 @CSMagAndAwards www.computingsecurity.co.uk
Brookcourt Solutions (A Shearwater Group plc Company) delivers<br />
cyber security, network monitoring technologies and managed<br />
security services to help secure and protect your organisation’s<br />
critical infrastructure.<br />
Brookcourt sell leading high-end technology and services to leading<br />
Fortune 250 companies – including the largest telecommunications<br />
providers within the UK, high street banks, global retail enterprises<br />
and the largest oil companies across the world.<br />
Brookcourt can help defend your business against todays advisories<br />
and cyber threats whilst helping you with your data protection and<br />
control. Our leading-edge cyber threat intelligence technologies are<br />
provided to leading global institutions as well as smaller enterprises<br />
as a complete managed service.<br />
Get in touch today: contact@brookcourtsolutions.com<br />
C y b e r S u r v e i l l a n c e • S e c u r i t y • N e t w o r k i n g • C o n s u l t a n c y • M a n a g e d S e r v i c e s<br />
A Shearwater Group plc Company - Multi Award Winning - shearwatergroup.com<br />
For more information contact Brookcourt Solutions t: +44 (0) 1737 886 111 www.brookcourtsolutions.com