Security Profile for Advanced Metering Infrastructure - Open Smart ...
Security Profile for Advanced Metering Infrastructure - Open Smart ...
Security Profile for Advanced Metering Infrastructure - Open Smart ...
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
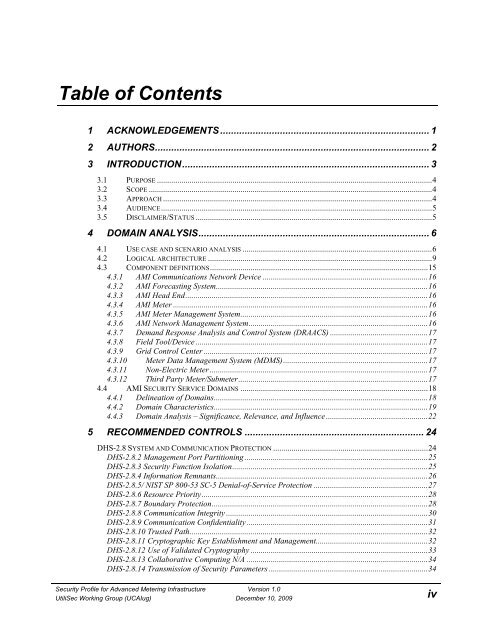
Table of Contents<br />
1 ACKNOWLEDGEMENTS ............................................................................. 1<br />
2 AUTHORS ..................................................................................................... 2<br />
3 INTRODUCTION ........................................................................................... 3<br />
3.1 PURPOSE ....................................................................................................................................... 4<br />
3.2 SCOPE ........................................................................................................................................... 4<br />
3.3 APPROACH .................................................................................................................................... 4<br />
3.4 AUDIENCE ..................................................................................................................................... 5<br />
3.5 DISCLAIMER/STATUS .................................................................................................................... 5<br />
4 DOMAIN ANALYSIS ..................................................................................... 6<br />
4.1 USE CASE AND SCENARIO ANALYSIS ............................................................................................. 6<br />
4.2 LOGICAL ARCHITECTURE .............................................................................................................. 9<br />
4.3 COMPONENT DEFINITIONS ........................................................................................................... 15<br />
4.3.1 AMI Communications Network Device ................................................................................. 16<br />
4.3.2 AMI Forecasting System ........................................................................................................ 16<br />
4.3.3 AMI Head End ....................................................................................................................... 16<br />
4.3.4 AMI Meter ............................................................................................................................. 16<br />
4.3.5 AMI Meter Management System ............................................................................................ 16<br />
4.3.6 AMI Network Management System ........................................................................................ 16<br />
4.3.7 Demand Response Analysis and Control System (DRAACS) ................................................ 17<br />
4.3.8 Field Tool/Device .................................................................................................................. 17<br />
4.3.9 Grid Control Center .............................................................................................................. 17<br />
4.3.10 Meter Data Management System (MDMS) ....................................................................... 17<br />
4.3.11 Non-Electric Meter ........................................................................................................... 17<br />
4.3.12 Third Party Meter/Submeter ............................................................................................. 17<br />
4.4 AMI SECURITY SERVICE DOMAINS ............................................................................................ 18<br />
4.4.1 Delineation of Domains ......................................................................................................... 18<br />
4.4.2 Domain Characteristics ......................................................................................................... 19<br />
4.4.3 Domain Analysis – Significance, Relevance, and Influence .................................................. 22<br />
5 RECOMMENDED CONTROLS .................................................................. 24<br />
DHS-2.8 SYSTEM AND COMMUNICATION PROTECTION ............................................................................ 24<br />
DHS-2.8.2 Management Port Partitioning .......................................................................................... 25<br />
DHS-2.8.3 <strong>Security</strong> Function Isolation ................................................................................................ 25<br />
DHS-2.8.4 In<strong>for</strong>mation Remnants ........................................................................................................ 26<br />
DHS-2.8.5/ NIST SP 800-53 SC-5 Denial-of-Service Protection ........................................................ 27<br />
DHS-2.8.6 Resource Priority ............................................................................................................... 28<br />
DHS-2.8.7 Boundary Protection .......................................................................................................... 28<br />
DHS-2.8.8 Communication Integrity ................................................................................................... 30<br />
DHS-2.8.9 Communication Confidentiality ......................................................................................... 31<br />
DHS-2.8.10 Trusted Path ..................................................................................................................... 32<br />
DHS-2.8.11 Cryptographic Key Establishment and Management ....................................................... 32<br />
DHS-2.8.12 Use of Validated Cryptography ....................................................................................... 33<br />
DHS-2.8.13 Collaborative Computing N/A ......................................................................................... 34<br />
DHS-2.8.14 Transmission of <strong>Security</strong> Parameters .............................................................................. 34<br />
<strong>Security</strong> <strong>Profile</strong> <strong>for</strong> <strong>Advanced</strong> <strong>Metering</strong> <strong>Infrastructure</strong> Version 1.0<br />
UtiliSec Working Group (UCAIug) December 10, 2009<br />
iv