CS Jan-Feb 2024
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
phishing<br />
Malicious actors who set up fake websites<br />
are, of course, hoping to catch users off<br />
guard. "The battle against domain phishing<br />
scams demands unwavering vigilance," he<br />
adds, "as most attacks prey on our busy<br />
lifestyles, in the hope we won't notice things<br />
are 'a little off', If something seems a little too<br />
good to be true, or the website perhaps isn't<br />
exactly how you remember it, it's always best<br />
practice to double-check the domain URL or<br />
the email address and language used in any<br />
correspondence."<br />
To be really sure, you can contact the<br />
company independently to enquire about the<br />
communication validity. Legitimate companies<br />
will generally have a website accessible from<br />
a search engine where anyone can find their<br />
details. Taking a proactive approach will stand<br />
you in good stead to pick up on anything<br />
suspicious, says Herbert.<br />
"We would recommend you visit the website<br />
of the company that any questionable email<br />
claims to be from to see if there are any<br />
announce-ments about phishing attempts.<br />
Having said that, just because there hasn't<br />
been one before doesn't mean there won't<br />
be a first!<br />
"For businesses, implementing basic levels<br />
of cyber hygiene, like technical measures of<br />
threat identification and mitigation, is a good<br />
first step, but unfortunately this often isn't<br />
enough," he continues. "For peace of mind,<br />
it's best practice to invest in a positive security<br />
culture, regular security awareness training<br />
and pen testing - these are simulated phishing<br />
attacks that will help you determine the<br />
effectiveness of staff awareness training.<br />
Deficiencies in process or employee blind<br />
spots can then be rectified."<br />
STAY VIGILANT<br />
Durali Cingit, incident response analyst<br />
at Integrity360, states that the important<br />
questions to ask when it comes to accessing<br />
a website and establishing if it is legitimate<br />
or a phishing one are: "How did I get here,<br />
directly or indirectly? Did I click on a link from<br />
an email? Did I use a search engine to get to<br />
this website? Have I been redirected to this<br />
website from a link?" These questions will help<br />
to keep you safe.<br />
"In order to distinguish the real from the<br />
fake, there are a few details to look out for on<br />
websites," he advises. "First, you want to check<br />
the URL of the website; safe and secure websites<br />
all begin with 'HTTPS://' and, depending<br />
on the browser you use, you will see a green<br />
padlock or the URL bar will be green as an<br />
indicator that this website is secure.<br />
However, threat actors have also adapted<br />
and evolved into now making their websites<br />
secure to fool users into thinking that the fake<br />
website is legit, so it's not enough to rely on<br />
this alone." Also, the 'About Us/Contact Us'<br />
page should provide a contact form or an<br />
email address, which can be a key indicator.<br />
"These pages are normally populated with<br />
different ways in which you can contact the<br />
organisation, whereas a phishing website<br />
may only contain one source of contact<br />
information."<br />
Finally, he suggests, you should ask yourself<br />
the 'How did I get here?' question. "The main<br />
tactic threat actors use to get users onto<br />
a phishing website is either through email<br />
or SMS message. Users should be alert and<br />
cautious as to who sent the email. If they<br />
were expecting an email form the sender, is<br />
the email asking them to click on a link or an<br />
attachment, which more often than not will<br />
redirect the user to a phishing website.<br />
"Same procedure with SMS text messages<br />
where users fall prey to fake text messages -<br />
eg, from the bank with a link that will ask the<br />
user to log in, in order to steal their financial<br />
login details."<br />
He also advises organisations to sign up to<br />
programmes that make it mandatory for all<br />
employees to take part in being educated on<br />
phishing and the signs to look out for.<br />
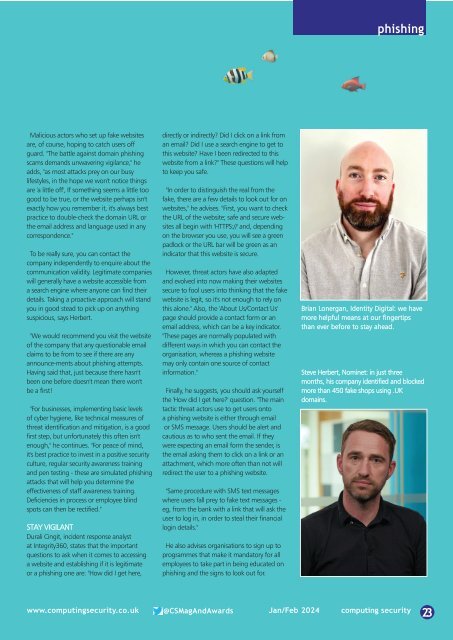
Brian Lonergan, Identity Digital: we have<br />
more helpful means at our fingertips<br />
than ever before to stay ahead.<br />
Steve Herbert, Nominet: in just three<br />
months, his company identified and blocked<br />
more than 450 fake shops using .UK<br />
domains.<br />
www.computingsecurity.co.uk @<strong>CS</strong>MagAndAwards <strong>Jan</strong>/<strong>Feb</strong> <strong>2024</strong> computing security<br />
23