GSN_Nov-Dec_FINAL_Yumpu
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
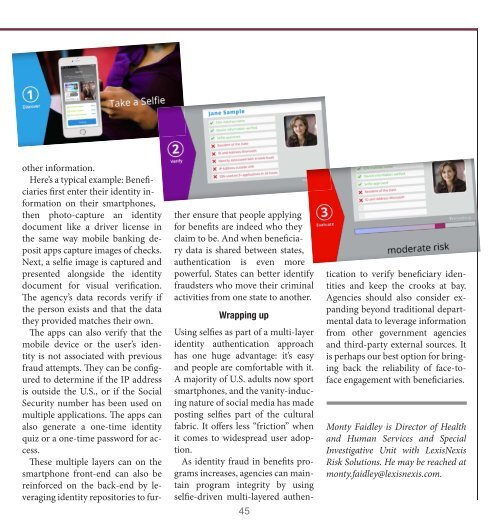
other information.<br />
Here’s a typical example: Beneficiaries<br />
first enter their identity information<br />
on their smartphones,<br />
then photo-capture an identity<br />
document like a driver license in<br />
the same way mobile banking deposit<br />
apps capture images of checks.<br />
Next, a selfie image is captured and<br />
presented alongside the identity<br />
document for visual verification.<br />
The agency’s data records verify if<br />
the person exists and that the data<br />
they provided matches their own.<br />
The apps can also verify that the<br />
mobile device or the user’s identity<br />
is not associated with previous<br />
fraud attempts. They can be configured<br />
to determine if the IP address<br />
is outside the U.S., or if the Social<br />
Security number has been used on<br />
multiple applications. The apps can<br />
also generate a one-time identity<br />
quiz or a one-time password for access.<br />
These multiple layers can on the<br />
smartphone front-end can also be<br />
reinforced on the back-end by leveraging<br />
identity repositories to further<br />
ensure that people applying<br />
for benefits are indeed who they<br />
claim to be. And when beneficiary<br />
data is shared between states,<br />
authentication is even more<br />
powerful. States can better identify<br />
fraudsters who move their criminal<br />
activities from one state to another.<br />
Wrapping up<br />
Using selfies as part of a multi-layer<br />
identity authentication approach<br />
has one huge advantage: it’s easy<br />
and people are comfortable with it.<br />
A majority of U.S. adults now sport<br />
smartphones, and the vanity-inducing<br />
nature of social media has made<br />
posting selfies part of the cultural<br />
fabric. It offers less “friction” when<br />
it comes to widespread user adoption.<br />
As identity fraud in benefits programs<br />
increases, agencies can maintain<br />
program integrity by using<br />
selfie-driven multi-layered authen-<br />
45<br />
tication to verify beneficiary identities<br />
and keep the crooks at bay.<br />
Agencies should also consider expanding<br />
beyond traditional departmental<br />
data to leverage information<br />
from other government agencies<br />
and third-party external sources. It<br />
is perhaps our best option for bringing<br />
back the reliability of face-toface<br />
engagement with beneficiaries.<br />
Monty Faidley is Director of Health<br />
and Human Services and Special<br />
Investigative Unit with LexisNexis<br />
Risk Solutions. He may be reached at<br />
monty.faidley@lexisnexis.com.