Cyber Attack Task Force - Final Report - NERC
Cyber Attack Task Force - Final Report - NERC
Cyber Attack Task Force - Final Report - NERC
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
Executive Summary<br />
identify the point at which current transmission planning criteria is exceeded and allow<br />
for dynamic resilience and mitigation exercise.<br />
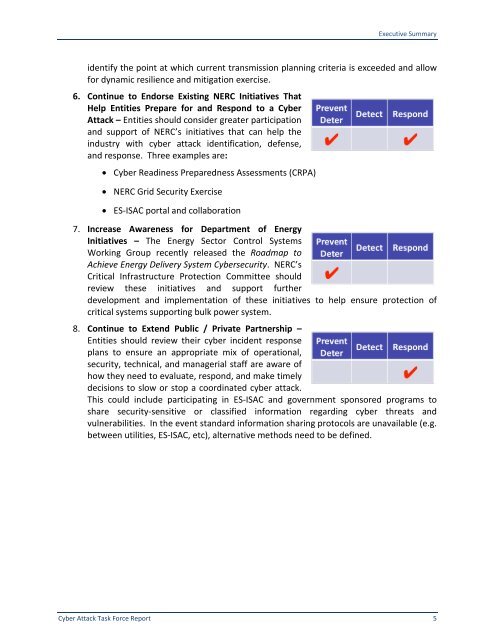
6. Continue to Endorse Existing <strong>NERC</strong> Initiatives That<br />
Help Entities Prepare for and Respond to a <strong>Cyber</strong><br />
<strong>Attack</strong> – Entities should consider greater participation<br />
and support of <strong>NERC</strong>’s initiatives that can help the<br />
industry with cyber attack identification, defense,<br />
and response. Three examples are:<br />
• <strong>Cyber</strong> Readiness Preparedness Assessments (CRPA)<br />
• <strong>NERC</strong> Grid Security Exercise<br />
• ES-ISAC portal and collaboration<br />
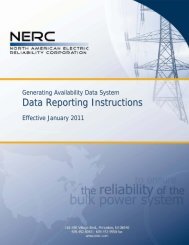
7. Increase Awareness for Department of Energy<br />
Initiatives – The Energy Sector Control Systems<br />
Working Group recently released the Roadmap to<br />
Achieve Energy Delivery System <strong>Cyber</strong>security. <strong>NERC</strong>’s<br />
Critical Infrastructure Protection Committee should<br />
review these initiatives and support further<br />
development and implementation of these initiatives to help ensure protection of<br />
critical systems supporting bulk power system.<br />
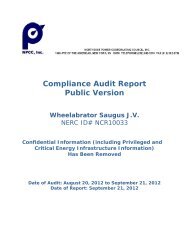
8. Continue to Extend Public / Private Partnership –<br />
Entities should review their cyber incident response<br />
plans to ensure an appropriate mix of operational,<br />
security, technical, and managerial staff are aware of<br />
how they need to evaluate, respond, and make timely<br />
decisions to slow or stop a coordinated cyber attack.<br />
This could include participating in ES-ISAC and government sponsored programs to<br />
share security-sensitive or classified information regarding cyber threats and<br />
vulnerabilities. In the event standard information sharing protocols are unavailable (e.g.<br />
between utilities, ES-ISAC, etc), alternative methods need to be defined.<br />
<strong>Cyber</strong> <strong>Attack</strong> <strong>Task</strong> <strong>Force</strong> <strong>Report</strong> 5