Cyber Attack Task Force - Final Report - NERC
Cyber Attack Task Force - Final Report - NERC
Cyber Attack Task Force - Final Report - NERC
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
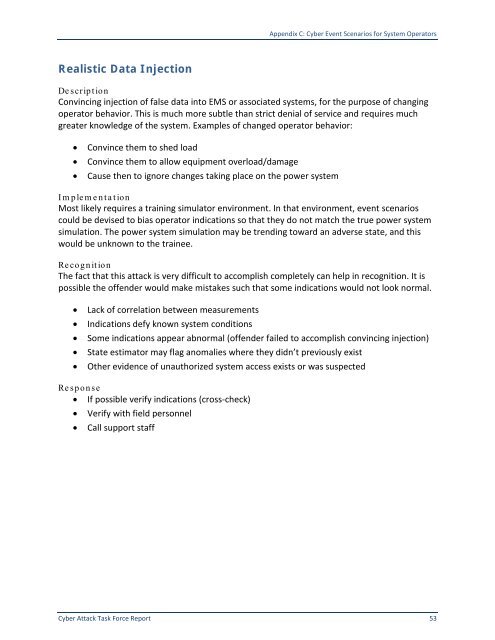
Realistic Data Injection<br />
Appendix C: <strong>Cyber</strong> Event Scenarios for System Operators<br />
De scription<br />
Convincing injection of false data into EMS or associated systems, for the purpose of changing<br />
operator behavior. This is much more subtle than strict denial of service and requires much<br />
greater knowledge of the system. Examples of changed operator behavior:<br />
• Convince them to shed load<br />
• Convince them to allow equipment overload/damage<br />
• Cause then to ignore changes taking place on the power system<br />
Im plem e nta tion<br />
Most likely requires a training simulator environment. In that environment, event scenarios<br />
could be devised to bias operator indications so that they do not match the true power system<br />
simulation. The power system simulation may be trending toward an adverse state, and this<br />
would be unknown to the trainee.<br />
Recognition<br />
The fact that this attack is very difficult to accomplish completely can help in recognition. It is<br />
possible the offender would make mistakes such that some indications would not look normal.<br />
• Lack of correlation between measurements<br />
• Indications defy known system conditions<br />
• Some indications appear abnormal (offender failed to accomplish convincing injection)<br />
• State estimator may flag anomalies where they didn’t previously exist<br />
• Other evidence of unauthorized system access exists or was suspected<br />
Response<br />
• If possible verify indications (cross-check)<br />
• Verify with field personnel<br />
• Call support staff<br />
<strong>Cyber</strong> <strong>Attack</strong> <strong>Task</strong> <strong>Force</strong> <strong>Report</strong> 53