Cyber Attack Task Force - Final Report - NERC
Cyber Attack Task Force - Final Report - NERC
Cyber Attack Task Force - Final Report - NERC
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
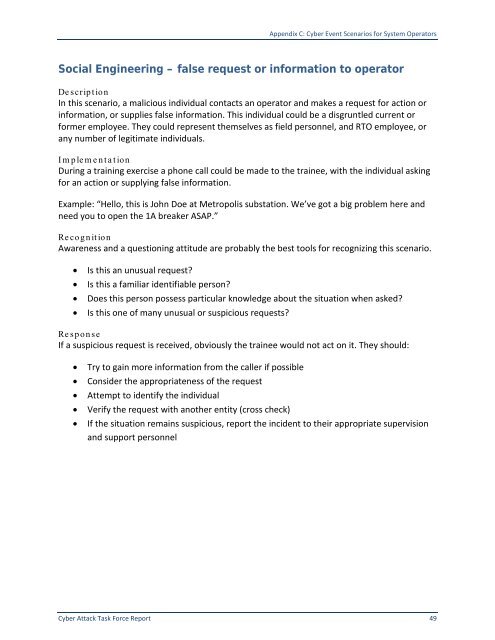
Appendix C: <strong>Cyber</strong> Event Scenarios for System Operators<br />
Social Engineering – false request or information to operator<br />
De scription<br />
In this scenario, a malicious individual contacts an operator and makes a request for action or<br />
information, or supplies false information. This individual could be a disgruntled current or<br />
former employee. They could represent themselves as field personnel, and RTO employee, or<br />
any number of legitimate individuals.<br />
Im plem e nta tion<br />
During a training exercise a phone call could be made to the trainee, with the individual asking<br />
for an action or supplying false information.<br />
Example: “Hello, this is John Doe at Metropolis substation. We’ve got a big problem here and<br />
need you to open the 1A breaker ASAP.”<br />
Recognition<br />
Awareness and a questioning attitude are probably the best tools for recognizing this scenario.<br />
• Is this an unusual request?<br />
• Is this a familiar identifiable person?<br />
• Does this person possess particular knowledge about the situation when asked?<br />
• Is this one of many unusual or suspicious requests?<br />
Response<br />
If a suspicious request is received, obviously the trainee would not act on it. They should:<br />
• Try to gain more information from the caller if possible<br />
• Consider the appropriateness of the request<br />
• Attempt to identify the individual<br />
• Verify the request with another entity (cross check)<br />
• If the situation remains suspicious, report the incident to their appropriate supervision<br />
and support personnel<br />
<strong>Cyber</strong> <strong>Attack</strong> <strong>Task</strong> <strong>Force</strong> <strong>Report</strong> 49