Understanding Security APIs - CrySyS Lab
Understanding Security APIs - CrySyS Lab
Understanding Security APIs - CrySyS Lab
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
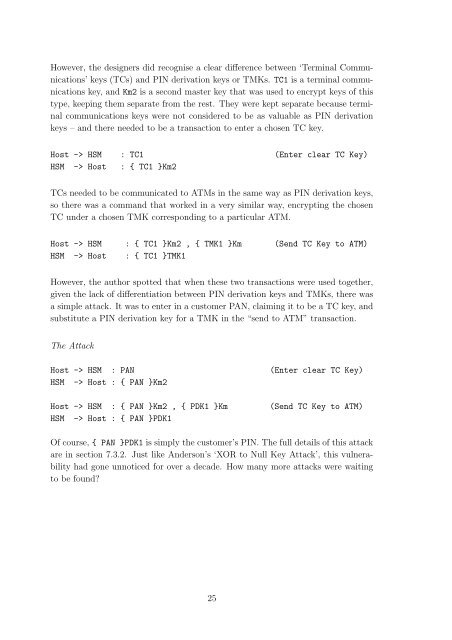
However, the designers did recognise a clear difference between ‘Terminal Communications’<br />
keys (TCs) and PIN derivation keys or TMKs. TC1 is a terminal communications<br />
key, and Km2 is a second master key that was used to encrypt keys of this<br />
type, keeping them separate from the rest. They were kept separate because terminal<br />
communications keys were not considered to be as valuable as PIN derivation<br />
keys – and there needed to be a transaction to enter a chosen TC key.<br />
Host -> HSM : TC1 (Enter clear TC Key)<br />
HSM -> Host : { TC1 }Km2<br />
TCs needed to be communicated to ATMs in the same way as PIN derivation keys,<br />
so there was a command that worked in a very similar way, encrypting the chosen<br />
TC under a chosen TMK corresponding to a particular ATM.<br />
Host -> HSM : { TC1 }Km2 , { TMK1 }Km (Send TC Key to ATM)<br />
HSM -> Host : { TC1 }TMK1<br />
However, the author spotted that when these two transactions were used together,<br />
given the lack of differentiation between PIN derivation keys and TMKs, there was<br />
a simple attack. It was to enter in a customer PAN, claiming it to be a TC key, and<br />
substitute a PIN derivation key for a TMK in the “send to ATM” transaction.<br />
The Attack<br />
Host -> HSM : PAN (Enter clear TC Key)<br />
HSM -> Host : { PAN }Km2<br />
Host -> HSM : { PAN }Km2 , { PDK1 }Km (Send TC Key to ATM)<br />
HSM -> Host : { PAN }PDK1<br />
Of course, { PAN }PDK1 is simply the customer’s PIN. The full details of this attack<br />
are in section 7.3.2. Just like Anderson’s ‘XOR to Null Key Attack’, this vulnerability<br />
had gone unnoticed for over a decade. How many more attacks were waiting<br />
to be found?<br />
25