Configuring, Managing and Maintaining Windows Server 2008
Configuring, Managing and Maintaining Windows Server 2008
Configuring, Managing and Maintaining Windows Server 2008
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
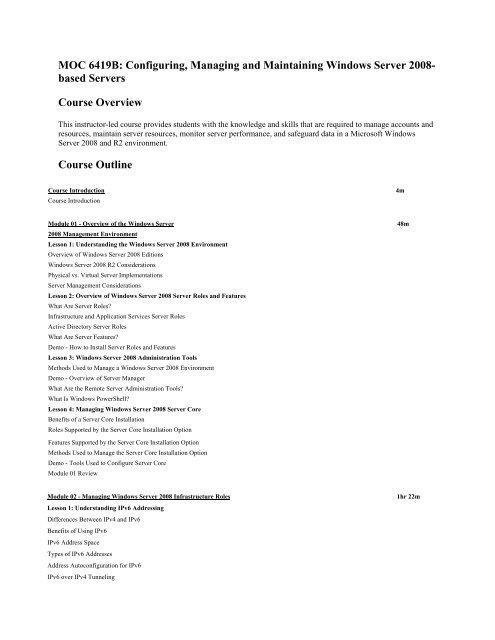
MOC 6419B: <strong>Configuring</strong>, <strong>Managing</strong> <strong>and</strong> <strong>Maintaining</strong> <strong>Windows</strong> <strong>Server</strong> <strong>2008</strong>based<br />
<strong>Server</strong>s<br />
Course Overview<br />
This instructor-led course provides students with the knowledge <strong>and</strong> skills that are required to manage accounts <strong>and</strong><br />
resources, maintain server resources, monitor server performance, <strong>and</strong> safeguard data in a Microsoft <strong>Windows</strong><br />
<strong>Server</strong> <strong>2008</strong> <strong>and</strong> R2 environment.<br />
Course Outline<br />
Course Introduction 4m<br />
Course Introduction<br />
Module 01 - Overview of the <strong>Windows</strong> <strong>Server</strong> 48m<br />
<strong>2008</strong> Management Environment<br />
Lesson 1: Underst<strong>and</strong>ing the <strong>Windows</strong> <strong>Server</strong> <strong>2008</strong> Environment<br />
Overview of <strong>Windows</strong> <strong>Server</strong> <strong>2008</strong> Editions<br />
<strong>Windows</strong> <strong>Server</strong> <strong>2008</strong> R2 Considerations<br />
Physical vs. Virtual <strong>Server</strong> Implementations<br />
<strong>Server</strong> Management Considerations<br />
Lesson 2: Overview of <strong>Windows</strong> <strong>Server</strong> <strong>2008</strong> <strong>Server</strong> Roles <strong>and</strong> Features<br />
What Are <strong>Server</strong> Roles?<br />
Infrastructure <strong>and</strong> Application Services <strong>Server</strong> Roles<br />
Active Directory <strong>Server</strong> Roles<br />
What Are <strong>Server</strong> Features?<br />
Demo - How to Install <strong>Server</strong> Roles <strong>and</strong> Features<br />
Lesson 3: <strong>Windows</strong> <strong>Server</strong> <strong>2008</strong> Administration Tools<br />
Methods Used to Manage a <strong>Windows</strong> <strong>Server</strong> <strong>2008</strong> Environment<br />
Demo - Overview of <strong>Server</strong> Manager<br />
What Are the Remote <strong>Server</strong> Administration Tools?<br />
What Is <strong>Windows</strong> PowerShell?<br />
Lesson 4: <strong>Managing</strong> <strong>Windows</strong> <strong>Server</strong> <strong>2008</strong> <strong>Server</strong> Core<br />
Benefits of a <strong>Server</strong> Core Installation<br />
Roles Supported by the <strong>Server</strong> Core Installation Option<br />
Features Supported by the <strong>Server</strong> Core Installation Option<br />
Methods Used to Manage the <strong>Server</strong> Core Installation Option<br />
Demo - Tools Used to Configure <strong>Server</strong> Core<br />
Module 01 Review<br />
Module 02 - <strong>Managing</strong> <strong>Windows</strong> <strong>Server</strong> <strong>2008</strong> Infrastructure Roles 1hr 22m<br />
Lesson 1: Underst<strong>and</strong>ing IPv6 Addressing<br />
Differences Between IPv4 <strong>and</strong> IPv6<br />
Benefits of Using IPv6<br />
IPv6 Address Space<br />
Types of IPv6 Addresses<br />
Address Autoconfiguration for IPv6<br />
IPv6 over IPv4 Tunneling
Overview of IPv6 Tunneling Technologies<br />
Lesson 2: Overview of the DNS <strong>Server</strong> Role<br />
DNS Enhancements in <strong>Windows</strong> <strong>Server</strong> <strong>2008</strong><br />
DNS Resource Records<br />
How DNS Name Resolution Works<br />
DNS Forwarding<br />
What Is Conditional Forwarding?<br />
Demo - How to Configure DNS Forwarding<br />
Lesson 3: <strong>Configuring</strong> DNS Zones<br />
What Are Forward <strong>and</strong> Reverse Lookup Zones?<br />
What Are DNS Zone Types?<br />
What Is an Active Directory-Integrated Zone?<br />
Demo - How to Create Forward <strong>and</strong> Reverse Lookup Zones<br />
Overview of DNS Zone Transfer<br />
What Is Time Stamping, Aging, <strong>and</strong> Scavenging<br />
Tools Used to Troubleshoot DNS<br />
Demo - Monitoring DNS<br />
Lesson 4: Overview of DHCP <strong>Server</strong> Roles<br />
New DHCP Features in <strong>Windows</strong> <strong>Server</strong> <strong>2008</strong><br />
DHCP <strong>Server</strong> Authorization<br />
How DHCP Lease Generation Works<br />
How DHCP Lease Renewal Works<br />
Demo - Adding <strong>and</strong> Authorizing the DHCP <strong>Server</strong> Role<br />
Lesson 5: <strong>Configuring</strong> DHCP Scopes <strong>and</strong> Options<br />
What Are DHCP Scopes?<br />
Demo - <strong>Configuring</strong> a DHCPv4 Scope<br />
What Are DHCP Options?<br />
What Are DHCP Class-Level Options?<br />
What Is a DHCP Reservation?<br />
Demo - <strong>Configuring</strong> DHCP Options <strong>and</strong> Reservations<br />
How DHCP Options Are Applied<br />
Common DHCP Issues<br />
Module 02 Review<br />
Module 03 - <strong>Configuring</strong> Access to File Services 1hr 0m<br />
Lesson 1: Overview of Access Control<br />
What Are Security Principals?<br />
What Are Access Tokens?<br />
What Are Permissions?<br />
How Access Control Works<br />
What Is Access-Based Enumeration?<br />
Lesson 2: <strong>Managing</strong> NTFS File <strong>and</strong> Folder Permissions<br />
What Are NTFS Permissions?<br />
What Are St<strong>and</strong>ard <strong>and</strong> Advanced Permissions?<br />
What Is NTFS Permissions Inheritance?<br />
Effects on NTFS Permissions when Copying or Moving Files <strong>and</strong> Folders
Demo - Copying <strong>and</strong> Moving Files on NTFS<br />
Lesson 3: <strong>Managing</strong> Permissions for Shared Resources<br />
Overview of the File Services Role in <strong>Windows</strong> <strong>Server</strong> <strong>2008</strong><br />
What Are Shared Folders?<br />
Shared Folder Permissions<br />
Demo - Creating Shared Folders<br />
Offline File Configuration<br />
Offline File Enhancements in <strong>Windows</strong> <strong>Server</strong> <strong>2008</strong> R2<br />
Demo - <strong>Configuring</strong> Offline File Access<br />
Lesson 4: Determining Effective Permissions<br />
What Are Effective NTFS Permissions?<br />
Discussion: Determining Effective NTFS Permissions<br />
Effects of Combining Shared Folder <strong>and</strong> NTFS Permissions<br />
Discussion: Determining Effective NTFS <strong>and</strong> Shared Folder Permissions<br />
Considerations for Implementing NTFS <strong>and</strong> Shared Folder Permissions<br />
Module 03 Review<br />
Module 04 - <strong>Configuring</strong> <strong>and</strong> <strong>Managing</strong> Distributed File System 51m<br />
Lesson 1: Distributed File System Overview<br />
What Is the Distributed File System?<br />
How DFS Namespaces <strong>and</strong> DFS Replication Work<br />
DFS Scenarios<br />
Types of DFS Namespaces<br />
What Are Folders <strong>and</strong> Folder Targets?<br />
Demo - Installing the Distributed File System Role Service<br />
DFS Enhancements in <strong>Windows</strong> <strong>Server</strong> <strong>2008</strong> R2<br />
Lesson 2: <strong>Configuring</strong> DFS Namespaces<br />
Deploying Namespaces for Publishing Content<br />
Permissions Required to Create <strong>and</strong> Manage a Namespace<br />
Demo - How to Create Namespaces<br />
Lesson 3: <strong>Configuring</strong> DFS Replication<br />
What Is DFS Replication?<br />
What Are Replication Groups <strong>and</strong> Replicated Folders?<br />
DFS-R Requirements<br />
Demo - How to Deploy a Replication Group<br />
Tools Used to Troubleshoot DFS-R<br />
Demo - How to Generate Diagnostic Reports <strong>and</strong> Propagation Tests<br />
Module 04 Review<br />
Module 05 - <strong>Managing</strong> File Resources Using 1hr 11m<br />
File <strong>Server</strong> Resource Manager<br />
Lesson 1: Overview of File <strong>Server</strong> Resource Manager<br />
Capacity Management Challenges<br />
What Is File <strong>Server</strong> Resource Manager?<br />
FSRM Configuration Options<br />
Demo - Installing <strong>and</strong> <strong>Configuring</strong> FSRM<br />
Lesson 2: <strong>Configuring</strong> Quota Management<br />
What Is Quota Management?<br />
FSRM Quotas vs. NTFS Disk Quotas<br />
What Are Quota Templates?
Demo - Creating <strong>and</strong> <strong>Configuring</strong> a Quota<br />
Monitoring Quota Usage<br />
Lesson 3: Implementing File Screening<br />
What is File Screening Management?<br />
What Are File Groups?<br />
What Is a File Screen Template?<br />
Demo - How to Implement File Screening<br />
What Is a File Screen Exception?<br />
Lesson 4: <strong>Managing</strong> Storage Reports<br />
What Are Storage Reports?<br />
What Is a Report Task?<br />
Generating On-Dem<strong>and</strong> Reports<br />
Lesson 5: Implementing Classification Management <strong>and</strong> File Management Tasks<br />
What Is Classification Management?<br />
What Are Classification Properties?<br />
What Is a Classification Rule?<br />
Demo - How to Configure Classification Management<br />
Considerations for Using File Classification<br />
What Are File Management Tasks?<br />
Demo - How to Configure File Management Tasks<br />
Module 05 Review<br />
Module 06 - <strong>Configuring</strong> <strong>and</strong> Securing Remote Access 1hr 36m<br />
Lesson 1: <strong>Configuring</strong> a Virtual Private Network Connection<br />
What Is Virtual Private Networking?<br />
Types of VPN Authentication Methods<br />
Tunneling Protocols for a VPN Connection<br />
Considerations for Installing a VPN <strong>Server</strong><br />
Demo - <strong>Configuring</strong> a VPN <strong>Server</strong><br />
Additional Configuration Tasks for VPN <strong>Server</strong>s<br />
What Is VPN Reconnect?<br />
Lesson 2: Overview of Network Policies<br />
What Is the Network Policy <strong>and</strong> Access Services Role?<br />
What Is a Network Policy?<br />
Process for Creating <strong>and</strong> <strong>Configuring</strong> a Network Policy<br />
Demo - How to Create a Network Policy<br />
How Network Policies are Processed<br />
Lesson 3: Integrating Network Access Protection with VPNs<br />
What Is Network Access Protection?<br />
Advantages of Implementing VPN Enforcement<br />
Components of a VPN Enforcement Solution<br />
How VPN Enforcement Determines Remote Access<br />
Lesson 4: <strong>Configuring</strong> VPN Enforcement Using NAP<br />
What Is a System Health Validator?<br />
Demo - What is a System Health Validator?<br />
What Is a Health Policy?<br />
What Is a Remediation <strong>Server</strong> Group?<br />
Overview of VPN NAP Enforcement Configuration<br />
Client Settings to Support NAP<br />
Lesson 5: Overview of DirectAccess
Discussion: Challenges of VPN Connections<br />
What Is DirectAccess?<br />
DirectAccess Infrastructure Components<br />
What Is the Name Resolution Policy Table?<br />
How DirectAccess Works for Internal Clients<br />
How DirectAccess Works for External Clients<br />
How a DirectAccess Client Determines Its Location<br />
<strong>Configuring</strong> DirectAccess<br />
Module 06 Review<br />
Module 07 - <strong>Managing</strong> Active Directory Domain Services 1hr 44m<br />
Lesson 1: Overview of the Active Directory Infrastructure<br />
Components of Active Directory Domain Services<br />
What Are Active Directory Partitions?<br />
What Is Active Directory Replication?<br />
What Are Active Directory Sites?<br />
Demo - Creating an Active Directory Site<br />
Domain <strong>and</strong> Forest Functional Levels<br />
Operations Master Roles<br />
Demo - How to Manage Operations Master Roles<br />
Lesson 2: Working with Active Directory Administration Tools<br />
Overview of the Active Directory Administration Snap-ins<br />
Demo - Active Directory Snap-ins<br />
Active Directory Administrative Center<br />
Demo - How to Manage Active Directory Using Management Tools<br />
Active Directory Module for <strong>Windows</strong> PowerShell<br />
Lesson 3: <strong>Managing</strong> User Accounts<br />
What Is a User Account?<br />
User Account Password Options<br />
User Account Attributes<br />
Demo - <strong>Configuring</strong> User Accounts<br />
What Is a User Account Template?<br />
Lesson 4: <strong>Managing</strong> Computer Accounts<br />
Considerations for Joining a Computer to a Domain<br />
What Is Offline Domain Join?<br />
Tools Used to Automate Computer Account Creation<br />
<strong>Managing</strong> Computer Accounts<br />
Lesson 5: <strong>Managing</strong> Groups<br />
Importance of Groups<br />
Underst<strong>and</strong>ing Role-Based Management Using Groups<br />
Group Types <strong>and</strong> Scope<br />
What Are Global Groups?<br />
What Are Universal Groups?<br />
What Are Domain Local Groups?<br />
Discussion: Identifying Group Usage<br />
What Is Group Nesting?<br />
Lesson 6: Using Queries to Locate Objects in AD DS<br />
Options for Locating Objects in AD DS<br />
Module 07 Review
Module 08 - <strong>Configuring</strong> Active Directory Object 52m<br />
Administration <strong>and</strong> Domain Trust<br />
Lesson 1: <strong>Configuring</strong> Active Directory Object Administration<br />
Active Directory Object Permissions<br />
Determining Effective Permissions<br />
Demo - AD DS Object Permission Inheritance<br />
What Is Delegation of Control?<br />
What Are Managed Service Accounts?<br />
Demo - <strong>Configuring</strong> a Managed Service Account<br />
Lesson 2: <strong>Configuring</strong> Active Directory Trusts<br />
Overview of AD DS Trust Options<br />
How Trusts Work Within a Forest<br />
How Trusts Work Between Forests<br />
Demo - <strong>Configuring</strong> a Forest Trust<br />
Resource Access for Users from Trusted Domains<br />
Module 08 Review<br />
Module 09 - Creating <strong>and</strong> <strong>Managing</strong> Group Policy Objects 1hr 10m<br />
Lesson 1: Overview of Group Policy<br />
What Is Configuration Management?<br />
What Are Group Policy Objects <strong>and</strong> Settings?<br />
How Group Policy Is Applied<br />
Exceptions to Group Policy Processing<br />
Group Policy Components<br />
Demo - <strong>Configuring</strong> Group Policy Objects<br />
Lesson 2: <strong>Configuring</strong> the Scope of Group Policy Objects<br />
Group Policy Processing Order<br />
Options for Modifying Group Policy Processing<br />
Demo - Filtering Group Policy Processing<br />
How Does Loopback Processing Work?<br />
Lesson 3: <strong>Managing</strong> Group Policy Objects<br />
GPO Management Tasks<br />
What Is a Starter GPO?<br />
Using <strong>Windows</strong> PowerShell to Manage GPOs<br />
Options for Delegating Control of GPOs<br />
Lesson 4: Evaluating <strong>and</strong> Troubleshooting Group Policy Processing<br />
What Is Group Policy Reporting?<br />
What Is Group Policy Modeling?<br />
Demo - How to Evaluate Group Policy Processing<br />
Scenarios for Group Policy Troubleshooting<br />
Troubleshooting Group Policy<br />
Tools Used for Troubleshooting Group Policy<br />
Module 09 Review<br />
Module 10 - Using Group Policy to Configure 48m<br />
User <strong>and</strong> Computer Settings<br />
Lesson 1: Using Group Policy to Configure Folder Redirection <strong>and</strong> Scripts<br />
What Is Folder Redirection?<br />
Folder Redirection Configuration Options<br />
Security Settings for Redirected Folders
Demo - <strong>Configuring</strong> Folder Redirection<br />
What Are Group Policy Scripts?<br />
Demo - <strong>Configuring</strong> Scripts with Group Policy<br />
Lesson 2: Using Administrative Templates to Manage Users <strong>and</strong> Computers<br />
Overview of Group Policy Administrative Template Settings<br />
What Are ADM <strong>and</strong> ADMX Files?<br />
What Is the Central Store?<br />
Discussion: Practical Uses of Administrative Templates<br />
Lesson 3: Deploying Software Using Group Policy<br />
How Group Policy Software Distribution Addresses the Software Life Cycle<br />
How <strong>Windows</strong> Installer Enhances Software Distribution<br />
Assigning <strong>and</strong> Publishing Software Applications<br />
<strong>Managing</strong> Software Upgrades Using Group Policy<br />
Comparing Group Policy Software Distribution with System Center Configuration Manager 2007 R3<br />
Lesson 4: Deploying Group Policy Preferences<br />
What Are Group Policy Preferences?<br />
Comparing Group Policy Settings <strong>and</strong> Preferences<br />
Applying <strong>Windows</strong> Settings Using Preferences<br />
Applying Control Panel Settings Using Preferences<br />
Group Policy Preferences Features<br />
Module 10 Review<br />
Module 11 - Implementing Security Settings Using Group Policy 48m<br />
Lesson 1: Overview of Group Policy Security Settings<br />
Overview of Security Settings<br />
What Are Account Policies?<br />
What Are Local Policies?<br />
Advanced Audit Policy Configuration<br />
<strong>Windows</strong> Firewall with Advanced Security<br />
Lesson 2: Implementing Fine-Grained Password Policies<br />
What Are Fine-Grained Password Policies?<br />
How Fine-Grained Password Policies Are Implemented<br />
Considerations for Implementing Fine-Grained Password Policies<br />
Demo - Implementing Fine-Grained Password Policies<br />
Lesson 3: Restricting Group Membership <strong>and</strong> Access to Software<br />
What Are Restricted Groups?<br />
Demo - <strong>Configuring</strong> Restricted Groups<br />
What Is a Software Restriction Policy?<br />
Overview of AppLocker<br />
AppLocker vs. SRPs<br />
Demo - How to Configure Application Control Policies<br />
Module 11 Review<br />
Module 12 - Providing Efficient Network Access for Remote Offices 37m<br />
Lesson 1: Overview of Remote Office Requirements<br />
Discussion: Challenges to <strong>Managing</strong> Remote Office Connectivity<br />
Options for Providing Efficient Access to Network Resources<br />
Lesson 2: Implementing Read-Only Domain Controllers
Read - Only Domain Controller Features<br />
How to Deploy an RODC<br />
What Is a Password Replication Policy?<br />
Demo - How to Configure a Password Replication Policy<br />
Demo - Administering RODC Credentials Caching<br />
Overview of Administrator Role Separation<br />
Lesson 3: Implementing BranchCache<br />
Overview of BranchCache<br />
Multimedia: Compare Hosted Cache Mode with Distributed Cache Mode<br />
BranchCache Requirements<br />
<strong>Server</strong> Configuration for BranchCache<br />
Client Configuration for BranchCache<br />
Demo - <strong>Configuring</strong> BranchCache<br />
BranchCache Monitoring<br />
Module 12 Review<br />
Module 13 - Monitoring <strong>and</strong> <strong>Maintaining</strong> <strong>Windows</strong> <strong>Server</strong> <strong>2008</strong> 52m<br />
Lesson 1: Planning Monitoring Tasks<br />
Reasons for Monitoring <strong>Windows</strong> <strong>Server</strong>s<br />
Types of Monitoring<br />
Planning for Event Monitoring<br />
Lesson 2: Calculating a <strong>Server</strong> Baseline<br />
Strategies for Tuning <strong>and</strong> Testing Performance<br />
Identifying Performance Bottlenecks<br />
Common Performance Metrics<br />
What Is a Performance Trend?<br />
Planning for Future Capacity Requirements<br />
Lesson 3: Interpreting Performance Counters<br />
Primary CPU Performance Counters<br />
Primary Memory Performance Counters<br />
Primary Disk Performance Counters<br />
Primary Network Performance Counters<br />
Identifying Performance Objects by <strong>Server</strong> Role<br />
Lesson 4: Selecting Appropriate Monitoring Tools<br />
Performance Monitor<br />
Reliability Monitor<br />
Resource Monitor<br />
What Are Event Subscriptions?<br />
Demo - Performance Monitor, Reliability Monitor, <strong>and</strong> Resource Monitor<br />
Module 13 Review<br />
Module 14 - <strong>Managing</strong> <strong>Windows</strong> <strong>Server</strong> <strong>2008</strong> Backup <strong>and</strong> Recovery 50m<br />
Lesson 1: Planning <strong>and</strong> Implementing File Backups on <strong>Windows</strong> <strong>Server</strong> <strong>2008</strong><br />
Selecting Backup Software<br />
Changes to <strong>Windows</strong> Backup in <strong>Windows</strong> <strong>Server</strong> <strong>2008</strong> R2<br />
Process for Planning Backup in <strong>Windows</strong> <strong>Server</strong> <strong>2008</strong><br />
Creating the Data Retention Plan<br />
Factors that Affect Backup Policy<br />
Demo - Overview of the <strong>Windows</strong> <strong>Server</strong> Backup Features<br />
Lesson 2: Planning <strong>and</strong> Implementing File Recovery
Considerations for Data Recovery<br />
<strong>Windows</strong> <strong>Server</strong> Backup Recovery Types<br />
<strong>Windows</strong> <strong>Server</strong> Recovery Options<br />
Updating Backup <strong>and</strong> Recovery Policy<br />
Lesson 3: Recovering Active Directory<br />
Methods Used to Recover Active Directory<br />
What Is the Database Mounting Tool?<br />
Recover Objects Using the Active Directory Recycle Bin<br />
Lesson 4: Troubleshooting <strong>Windows</strong> <strong>Server</strong> Startup<br />
Common Causes of Startup Problems<br />
Troubleshooting Startup Before the <strong>Windows</strong> Logo Appears<br />
Troubleshooting Startup After the <strong>Windows</strong> Logo Appears<br />
Troubleshooting Startup Problems After Logon<br />
Module 14 Review<br />
Course Closure<br />
Total Duration: 14hrs 32m