MOC 6232A: Implementing a Microsoft SQL Server 2008 Database ...
MOC 6232A: Implementing a Microsoft SQL Server 2008 Database ...
MOC 6232A: Implementing a Microsoft SQL Server 2008 Database ...
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
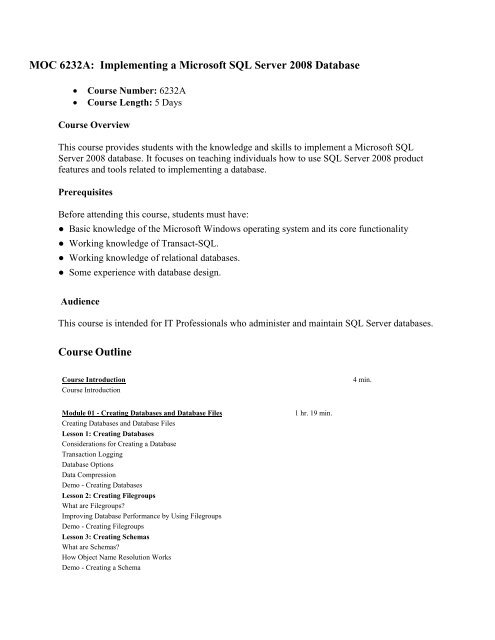
<strong>MOC</strong> <strong>6232A</strong>: <strong>Implementing</strong> a <strong>Microsoft</strong> <strong>SQL</strong> <strong>Server</strong> <strong>2008</strong> <strong>Database</strong><br />
• Course Number: <strong>6232A</strong><br />
• Course Length: 5 Days<br />
Course Overview<br />
This course provides students with the knowledge and skills to implement a <strong>Microsoft</strong> <strong>SQL</strong><br />
<strong>Server</strong> <strong>2008</strong> database. It focuses on teaching individuals how to use <strong>SQL</strong> <strong>Server</strong> <strong>2008</strong> product<br />
features and tools related to implementing a database.<br />
Prerequisites<br />
Before attending this course, students must have:<br />
● Basic knowledge of the <strong>Microsoft</strong> Windows operating system and its core functionality<br />
● Working knowledge of Transact-<strong>SQL</strong>.<br />
● Working knowledge of relational databases.<br />
● Some experience with database design.<br />
Audience<br />
This course is intended for IT Professionals who administer and maintain <strong>SQL</strong> <strong>Server</strong> databases.<br />
Course Outline<br />
Course Introduction<br />
Course Introduction<br />
Module 01 - Creating <strong>Database</strong>s and <strong>Database</strong> Files<br />
Creating <strong>Database</strong>s and <strong>Database</strong> Files<br />
Lesson 1: Creating <strong>Database</strong>s<br />
Considerations for Creating a <strong>Database</strong><br />
Transaction Logging<br />
<strong>Database</strong> Options<br />
Data Compression<br />
Demo - Creating <strong>Database</strong>s<br />
Lesson 2: Creating Filegroups<br />
What are Filegroups?<br />
Improving <strong>Database</strong> Performance by Using Filegroups<br />
Demo - Creating Filegroups<br />
Lesson 3: Creating Schemas<br />
What are Schemas?<br />
How Object Name Resolution Works<br />
Demo - Creating a Schema<br />
1 hr. 19 min.<br />
4 min.
Lesson 4: Creating <strong>Database</strong> Snapshots<br />
How <strong>Database</strong> Snapshots Work<br />
When to Use <strong>Database</strong> Snapshots<br />
Demo - Creating <strong>Database</strong> Snapshots<br />
Lab: Creating <strong>Database</strong>s and <strong>Database</strong> Files<br />
Module 01 Review<br />
Module 02 - Creating Data Types and Tables<br />
Creating Data Types and Tables<br />
Lesson 1: Creating Data Types<br />
What Are System-Supplied Data Types?<br />
Using System-Supplied Data Types<br />
What Are Alias Data Types?<br />
Demo - Creating Data Types<br />
Lesson 2: Creating Tables<br />
How <strong>SQL</strong> <strong>Server</strong> Organizes Data in Rows<br />
How <strong>SQL</strong> <strong>Server</strong> Organizes Large Data Values<br />
Types of Tables<br />
Considerations for Creating Tables<br />
Generating Transact-<strong>SQL</strong> Scripts<br />
Demo - Creating Tables<br />
Lesson 3: Creating Partitioned Tables<br />
What Are Partitioned Tables?<br />
What Are Partition Functions?<br />
What Is a Partition Scheme?<br />
What Operations Can Be Performed on Partitioned Data?<br />
Demo - Creating a Partitioned Table<br />
Lab: Creating Data Types and Tables<br />
Module 02 Review<br />
Module 03 - Creating and Tuning Indexes<br />
Creating and Tuning Indexes<br />
Lesson 1: Planning Indexes<br />
How <strong>SQL</strong> <strong>Server</strong> Accesses Data<br />
What Is a Heap?<br />
What Is a Clustered Index?<br />
What Is a Nonclustered Index?<br />
<strong>SQL</strong> <strong>Server</strong> Storage Allocation<br />
Simple B-Tree Index Structure (Balanced)<br />
Complex B-Tree Index Structure (Balanced)<br />
Lesson 2: Creating Indexes<br />
Overview of Creating Indexes<br />
What Are Unique Indexes?<br />
Considerations for Creating Indexes with Multiple Columns<br />
When to Create Indexes on Computed Columns<br />
What Are Partitioned Indexes?<br />
Options for Incorporating Free Space in Indexes<br />
Methods for Obtaining Index Information<br />
1 hr. 14 min.<br />
1 hr. 9 min.
Demo - Creating Indexes<br />
Lesson 3: Optimizing Indexes<br />
What Is the <strong>Database</strong> Engine Tuning Advisor?<br />
Demo - Using the <strong>Database</strong> Engine Tuning Advisor<br />
Index Fragmentation<br />
Options for Defragmenting Indexes<br />
Demo - Defragmenting Indexes<br />
Lab: Creating and Optimizing Indexes<br />
Module 03 Review<br />
Module 04 - <strong>Implementing</strong> Data Integrity<br />
by Using Constraints and Triggers<br />
<strong>Implementing</strong> Data Integrity by Using Constraints and Triggers<br />
Lesson 1: Data Integrity Overview<br />
Types of Data Integrity<br />
Options for Enforcing Data Integrity<br />
Lesson 2: <strong>Implementing</strong> Constraints<br />
What Are Constraints?<br />
Key Constraints<br />
Other Constraints<br />
Cascading Referential Integrity<br />
Considerations for Constraint Checking<br />
Demo - Creating Constraints<br />
Lesson 3: <strong>Implementing</strong> Triggers<br />
What Are Triggers?<br />
How an INSERT Trigger Works<br />
How a DELETE Trigger Works<br />
How an UPDATE Trigger Works<br />
How an INSTEAD OF Trigger Works<br />
How Nested Triggers Work<br />
Considerations for Recursive Triggers<br />
Demo - Creating Triggers<br />
Lab: <strong>Implementing</strong> Data Integrity by Using Constraints and Triggers<br />
Module 04 Review<br />
Module 05 - Using XML<br />
Using XML<br />
Lesson 1: Using the XML Data Type<br />
What Is XML?<br />
What Is the XML Data Type?<br />
The Query, Value, and Exist Methods<br />
The Modify Method<br />
The Nodes Method<br />
Demo - Using the XML Data Type<br />
Lesson 2: Retrieving XML by Using FOR XML<br />
Introduction to the FOR XML Clause<br />
What Are RAW Mode Queries?<br />
1 hr. 10 min.<br />
3 hr. 19 min.
What Are AUTO Mode Queries?<br />
What Are EXPLICIT Mode Queries?<br />
What Are PATH Mode Queries?<br />
Syntax for Retrieving Nested XML<br />
Demo - Using FOR XML<br />
Lesson 3: Shredding XML by Using OPENXML<br />
Overview of Shredding XML Data<br />
Stored Procedures for Managing In-Memory Node Trees<br />
OPENXML Syntax<br />
Syntax for Working with XML Namespaces<br />
Demo - Using OPENXML to Shred XML<br />
Lesson 4: Introducing XQuery<br />
What Is XQuery?<br />
XQuery Basics<br />
XQuery Expressions<br />
Demo - Using XQuery Expressions<br />
Lesson 5: Creating XML Indexes<br />
What Are XML Indexes?<br />
What Are the Benefits of XML Indexes?<br />
Types of XML Indexes<br />
Demo - Creating XML Indexes<br />
Lesson 6: <strong>Implementing</strong> XML Schemas<br />
What Are XML Schemas?<br />
XML Schema Validation<br />
What Is an XML Schema Collection?<br />
What Is Typed and Untyped XML<br />
Demo - Using Typed XML<br />
Lab: Using XML<br />
Module 05 Review<br />
Module 06 - <strong>Implementing</strong> Views<br />
<strong>Implementing</strong> Views<br />
Lesson 1: Introduction to Views<br />
What Is a View?<br />
Types of Views<br />
Advantages of Views<br />
Lesson 2: Creating and Managing Views<br />
Syntax for Creating Views<br />
Demo - Creating a View<br />
Syntax for Altering and Dropping Views<br />
View Encryption<br />
How Ownership Chains Affect Views<br />
Sources of Information About Views<br />
Considerations for Modifying Data in a View<br />
Demo - Creating Views with Transact <strong>SQL</strong><br />
Demo - Creating a View with Schema Binding<br />
Lesson 3: Optimizing Performance by Using Views<br />
Performance Considerations for Views<br />
Performance Considerations for Indexed Views<br />
What Is a Partitioned View?<br />
1 hr. 5 min.
Lab: <strong>Implementing</strong> Views<br />
Module 06 Review<br />
Module 07 - <strong>Implementing</strong> Stored Procedures<br />
<strong>Implementing</strong> Stored Procedures<br />
Lesson 1: Using Stored Procedures<br />
Discussion: What Is a Stored Procedure<br />
Syntax for Creating Stored Procedures<br />
Guidelines for Creating Stored Procedures<br />
Demo - Creating Stored Procedures<br />
Syntax for Altering Stored Procedures<br />
Syntax for Dropping Stored Procedures<br />
Demo - Altering and Dropping Stored Procedures<br />
Demo - Switching Execution Context<br />
Lesson 2: Creating Parameterized Stored Procedures<br />
Stored Procedure Parameters<br />
Demo - Creating a Parameterized Stored Procedure<br />
Table-valued Parameters<br />
Demo - Using Table Value Parameters<br />
Lesson 3: Working With Execution Plans<br />
What Is an Execution Plan?<br />
Viewing an Execution Plan<br />
Execution Plan Caching<br />
Query Compilation<br />
Forced Stored Procedure Recompilation<br />
Demo - Using Execution Plans<br />
Lesson 4: Handling Exceptions<br />
Syntax for Structured Exception Handling<br />
Guidelines for Handling Exceptions<br />
Demo - Handling Exceptions<br />
Lab: <strong>Implementing</strong> Stored Procedures<br />
Module 07 Review<br />
Module 08 - <strong>Implementing</strong> Functions<br />
<strong>Implementing</strong> Functions<br />
Lesson 1: Introducing Functions<br />
Types of Functions<br />
What Is a Scalar Function?<br />
Scalar Function Example<br />
What Is an Inline Table-Valued Function?<br />
Inline Table-Valued Function Example<br />
What Is a Multi-Statement Table-Valued Function?<br />
Multi-Statement Table-Valued Function Example<br />
Demo - Creating Functions<br />
Demo - Creating Inline Table-Valued Functions<br />
Demo - Creating Multi-Statement Table-Valued Functions<br />
Lesson 2: Working with Functions<br />
Deterministic and Nondeterministic Functions<br />
Guidelines for Creating Functions<br />
Rewriting Stored Procedures as Functions<br />
1 hr. 55 min.<br />
1 hr. 11 min.
Lesson 3: Controlling Execution Context<br />
What Is Execution Context?<br />
The EXECUTE AS Clause<br />
Extending Impersonation Context<br />
Lab: <strong>Implementing</strong> Functions<br />
Module 08 Review<br />
Module 09 - <strong>Implementing</strong> Managed Code in a <strong>Database</strong><br />
<strong>Implementing</strong> Managed Code in a <strong>Database</strong><br />
Lesson 1: Introduction to the <strong>SQL</strong> <strong>Server</strong> Common Language Runtime<br />
Introduction to the .NET Framework<br />
What Is the .NET Common Language Runtime?<br />
Advantages of Managed Code<br />
CLR Managed Code <strong>Database</strong> Objects<br />
Managed Code vs. Transact <strong>SQL</strong><br />
Lesson 2: Importing and Configuring Assemblies<br />
What Is an Assembly?<br />
Assembly Trust Levels<br />
Syntax for Importing an Assembly<br />
Demo - Importing and Configuring an Assembly<br />
Lesson 3: Creating Managed <strong>Database</strong> Objects<br />
Overview of Managed <strong>Database</strong> Objects<br />
Managed Stored Procedures, Triggers and Functions<br />
Managed Aggregates and User-Defined Types<br />
Demo - Creating Managed <strong>Database</strong> Objects<br />
Lab: <strong>Implementing</strong> Managed Code in a <strong>Database</strong><br />
Module 09 Review<br />
Module 10 - Managing Transactions and Locks<br />
Managing Transactions and Locks<br />
Lesson 1: Overview of Transactions and Locks<br />
What Are Transactions?<br />
What Are Locks?<br />
What Is Concurrency Control?<br />
Demo - Introducing Transactions<br />
Lesson 2: Managing Transactions<br />
Autocommit Transactions<br />
Explicit Transactions<br />
Implicit Transactions<br />
Transaction Recovery<br />
Considerations for Using Transactions<br />
Restricted Statements<br />
Lesson 3: Understanding <strong>SQL</strong> <strong>Server</strong> Locking Architecture<br />
What Concurrency Problems Are Prevented by Locking?<br />
Lockable Resources<br />
Types of Locks<br />
Lock Compatibility<br />
Locking Compatibility Matrix<br />
Lesson 4: Managing Locks<br />
Session-Level Locking Options<br />
1 hr. 10 min.<br />
2 hr. 2 min.
Locking Isolation Level Options<br />
Setting ISOLATION for Session<br />
Lock Escalation<br />
Dynamic Locking<br />
What Are Deadlocks?<br />
Avoiding Deadlocks<br />
Methods to View Locking Information<br />
Demo - Viewing Locking Information<br />
Lab: Managing Transactions and Locks<br />
Module 10 Review<br />
Module 11 - Using Service Broker<br />
Using Service Broker<br />
Lesson 1: Service Broker Overview<br />
What Is Service Broker?<br />
Service Broker System Architecture<br />
Service Broker Conversation Architecture<br />
Service Broker Conversation Process<br />
Service Broker Conversation Priority<br />
Syntax for Creating Conversation Broker Priority<br />
Service Broker Security Architecture<br />
Management Studio Enhancements<br />
Lesson 2: Creating Service Broker Objects<br />
Enabling Service Broker<br />
External Activation Support<br />
Syntax for Creating Message Types<br />
Syntax for Creating Contracts<br />
Syntax for Creating Queues<br />
Syntax for Creating Services<br />
Demo - Creating Service Broker Objects<br />
Lesson 3: Sending and Receiving Messages<br />
Syntax for Sending Messages<br />
Syntax for Receiving Messages<br />
Demo - Sending and Receiving Messages<br />
Diagnostic Tools for Sending\Receiving Messages<br />
Lab: Using Service Broker<br />
Module 11 Review<br />
Course Closure<br />
Course Introduction<br />
Module 1 - Designing an AD Forest Infrastructure<br />
Designing an Active Directory Forest Infrastructure in Windows <strong>Server</strong> <strong>2008</strong><br />
Overview of AD DS Forest Design Requirements<br />
Design Requirements – AD DS Forest<br />
Business Requirements for an AD DS Forest Design<br />
AD Forest Design<br />
Administrative and Security Requirements<br />
Technical Requirements for an AD DS Forest Design<br />
Types of AD DS Forests<br />
1 hr. 20 min.<br />
1h7m<br />
8m
Benefits of a Single Forest Model<br />
Disadvantages of Single Forest Model<br />
Reasons for <strong>Implementing</strong> Multiple Forests<br />
Benefits of <strong>Implementing</strong> Forest Root Domains<br />
Types of Forest Functional Levels<br />
Forest Functional Levels<br />
Windows <strong>Server</strong> 2003 Forest Functional Level<br />
Guidelines for Designing an AD DS Forest<br />
Types of Trusts<br />
What Is UPN Suffix Routing?<br />
Guidelines for Designing Forest Trusts<br />
Demo: <strong>Implementing</strong> an AD Forest Trust Design<br />
Modifications to AD DS Schema<br />
Guidelines for AD DS Schema Modifications<br />
Demo: Schema Changes<br />
How Does Windows Time Service Work?<br />
Considerations for Configuring Windows Time Service<br />
Member <strong>Server</strong>s and Workstations<br />
Domain Controllers<br />
Considerations<br />
Module 1 Review<br />
Module 2 - Designing an AD Domain Infrastructure<br />
Designing an Active Directory Domain Infrastructure in Windows <strong>Server</strong> <strong>2008</strong><br />
AD DS Domain Design Models<br />
AD DS Domain Models<br />
Factors to Consider When Accessing Domain Models<br />
Reasons for Deploying Multiple AD DS Domains<br />
AD DS Domain Functional Levels<br />
Supported Domain Controller Operating Systems<br />
Considerations for Configuring and Placing the Domain Controllers<br />
Considerations for Deploying Domain Controllers in Branch Offices<br />
Read Only Domain Controller (RODC)<br />
Guidelines for Designing AD DS Domains<br />
Choosing an AD DS Namespace Strategy<br />
Guidelines for Integrating the Public and Private DNS Namespaces<br />
Guidelines for Integrating Multiple Internal DNS Namespaces<br />
Guidelines for <strong>Implementing</strong> DNS <strong>Server</strong>s<br />
Demo: Configuring Forwarders and Delegation Records<br />
Windows <strong>2008</strong> Domain Controllers<br />
Domain Controller on a <strong>Server</strong> Core<br />
Deploying Domain Controllers in Windows <strong>Server</strong> <strong>2008</strong><br />
Deploying Domain Controllers in Windows <strong>Server</strong> <strong>2008</strong> - RODC<br />
Why Deploy RODC?<br />
Considerations When Deploying Domain Controllers<br />
Demo: Configuring an RODC Replication Policy<br />
Types of AD DS Domain Trusts<br />
Security Considerations for Trusts<br />
Demo: Trust Design<br />
Module 02 Review<br />
1h11m
Module 03 - Designing AD Sites and Replication<br />
Designing Active Directory Sites and Replication in Windows <strong>Server</strong> <strong>2008</strong><br />
Things to Document Before the AD Site Design<br />
Network Information for an AD DS Site Design<br />
Location Data for an AD DS Site Design<br />
AD DS Site Models<br />
Guidelines for Creating Additional AD DS Sites<br />
Demo: <strong>Implementing</strong> AD DS Site Design<br />
Locations<br />
How Does Automatic Site Coverage Work?<br />
Types of Replication Topologies<br />
Considerations for Choosing a Replication Protocol<br />
Levels of Connectivity<br />
Choosing Replication Protocols<br />
Demo: <strong>Implementing</strong> AD DS Replication<br />
Replication of Global Catalog, RODC, and SYSVOL<br />
Knowledge Consistency Checker<br />
Inter Site Topology Generator<br />
Using Site Links to Manage Replication<br />
Considerations for Designing Site Links and Bridgehead <strong>Server</strong>s<br />
Considerations for Designing Site-Link Bridging<br />
Considerations for Site Link Bridging<br />
Options for Configuring AD DS Replication<br />
Guidelines for Configuring AD DS Replication<br />
Guidelines for Placing Domain Controllers<br />
Guidelines for Placing RODCs<br />
Guidelines for Placing Global Catalog <strong>Server</strong>s<br />
Guidelines for Placing Operations Master <strong>Server</strong>s<br />
Module 03 Review<br />
Module 04 - Designing AD Domain Administrative Structures<br />
Designing Active Directory Domain Administrative Structures in Windows <strong>Server</strong> <strong>2008</strong><br />
Types of IT Administrative Models<br />
Guidelines for Gathering Information on the Current Administrative Structures<br />
Business Requirements for Existing Structure<br />
Legal Requirements<br />
Guidelines for Gathering Information on Organizational Resources<br />
Guidelines for Gathering Information on Administrative Processes<br />
Strategies for Designing Organizational Units<br />
Strategies for Delegating Administrative Control<br />
Strategies for Designing Group Policy Structures<br />
Considerations for Designing Organizational Unit Hierarchies<br />
Guidelines for Designing an Organizational Unit Structure<br />
Demo: Creating an AD OU Design<br />
AD DS Groups in Windows <strong>Server</strong> <strong>2008</strong><br />
Group Scope<br />
Guidelines for Developing a Group Naming Strategy<br />
Considerations for Group Nesting<br />
Group Nesting<br />
1h20m<br />
56m
Strategies for Using Groups to Access Resources<br />
Strategies for Placing Group Objects<br />
Guidelines for Designing an AD DS Group Strategy<br />
Guidelines for Designing a User Account Strategy<br />
Guidelines for Designing a Computer Account Strategy<br />
Naming Strategies for Computer Accounts<br />
Guidelines for Securing User and Computer Account Management<br />
Demo: Automating User Account Management<br />
Tools for Automating User and Computer Account Management<br />
Module 04 Review<br />
Module 05 - Designing AD Group Policy<br />
Designing Active Directory Group Policy in Windows <strong>Server</strong> <strong>2008</strong><br />
Gathering Organizational Information<br />
Gathering Information on Security Requirements<br />
Gathering Information on Desktop Management Requirements<br />
Gathering Information on Desktop Management<br />
Gathering Information on Administrative Processes<br />
Configuring Group Policy Settings<br />
Demo: Designing AD Group Policy<br />
Applying Group Policy Settings<br />
Demo: <strong>Implementing</strong> AD Group Policy<br />
Group Policy Storage Locations<br />
ADMX Format for Administrative Template<br />
Guidelines for Designing Administrative Templates<br />
Slow Link Detection<br />
Best Practices for Group Policy Model Design<br />
Guidelines for Designing Group Policy Inheritance<br />
Guidelines for Designing Group Policy Filtering<br />
Guidelines for Designing Group Policy Application<br />
GPO Backup and Recovery Strategy<br />
GPO Migration Strategy<br />
Delegating GPO Administration<br />
GPO Administration<br />
Module 05 Review<br />
Module 06 - Designing AD Security<br />
Designing Active Directory Security in Windows <strong>Server</strong> <strong>2008</strong><br />
Gathering Information for Designing Account Security Policies<br />
Key Components for Designing Account Security Policies<br />
Guidelines for Designing Account and Password Policy<br />
Guidelines for Designing Secure Account Management<br />
Fine-Grained Password Policies<br />
What Are Fine-Grained Password Policies?<br />
Storing Fine-Grained Password Policies<br />
Demo: Designing AD DS Security<br />
Password Setting Object Attributes<br />
How PSOs Are Processed and Applied<br />
Guidelines for Designing Fine-Grained<br />
Key Components that Affect Domain Controller Security<br />
1h21m<br />
1h52m
Why Modify the Default Domain Controller Security Policy?<br />
<strong>Server</strong> Core <strong>Server</strong> Roles<br />
<strong>Server</strong> Core as a Solution for Domain Controller Deployment<br />
What is the Security Configuration Wizard?<br />
Scenarios for Using the Security Configuration Wizard<br />
What Are Read-Only Domain Controllers?<br />
Prerequisites for Deploying RODCs<br />
Administrator Role Separation on RODCs<br />
Demo: Domain Controller/RODC Security Policies<br />
Administrator Responsibilities<br />
Service Administrator and Service Management<br />
Data Administrators and Data Management<br />
What Are Administrative Autonomy<br />
Delegation of Administrative Permission<br />
Attributes of a Good Delegation Model<br />
Guidelines for Creating a Delegation Model<br />
Guidelines for Using and Securing Administrator Accounts<br />
Demo: Restricted Groups<br />
Auditing Administrative Access<br />
Module 06 Review<br />
Module 07 - Designing AD High Availability<br />
Designing Active Directory High Availability in Windows <strong>Server</strong> <strong>2008</strong><br />
What is High Availability?<br />
Components of an Active Directory High Availability Design<br />
Active Directory High Availability<br />
Business Requirements for AD DS High Availability<br />
Infrastructure Requirements for AD DS High Availability<br />
High Availability Options for Network Infrastructure<br />
Process of Planning for High Availability<br />
Guidelines for Designing Highly Available Domain Controllers<br />
Global Catalog Placement and High Availability<br />
Demo: Designing AD DS Availability<br />
High Availability of DNS<br />
Guidelines for Designing Highly Available Network Infrastructure<br />
Module 07 Review<br />
Module 08 - Designing AD Disaster Recovery<br />
Designing Active Directory Disaster Recovery in Windows <strong>Server</strong> <strong>2008</strong><br />
Overview of <strong>Database</strong> Maintenance<br />
NTDSUtil.exe<br />
Benefits of Restartable AD DS in Windows <strong>Server</strong> <strong>2008</strong><br />
Considerations for Using Restartable AD DS<br />
Overview of AD DS Backup and Recovery<br />
Windows <strong>Server</strong> Backup<br />
AD DS Backup and Recovery in Windows <strong>Server</strong> <strong>2008</strong><br />
Active Directory Domain Services Backup System Components<br />
System State Data<br />
Critical Volumes – Review<br />
Options for Restoring AD DS<br />
57m<br />
27m
Considerations for Restoring AD DS<br />
Guidelines for Designing Backup and Recovery in AD DS<br />
Why Monitor AD DS?<br />
Tools for Monitoring AD DS<br />
Reliability and Performance Monitor<br />
Demo: Disaster Recovery and Monitoring<br />
Guidelines for Monitoring Active Directory Domain Controllers<br />
NTDS Counters – Monitoring AD<br />
Module 08 Review<br />
Module 09 - Designing Public Key Infrastructure<br />
Designing Public Key Infrastructure in Windows <strong>Server</strong> <strong>2008</strong><br />
What is a PKI?<br />
Key Components of a PKI<br />
PKI Solution Requirements<br />
Applications That Use PKI<br />
Certification Authorities and PKI<br />
Comparison of Enterprise and Standalone<br />
Internal and Public Certification Authorities<br />
Using Both Internal and External Public CA’s<br />
Active Directory Certificate Services in Windows <strong>Server</strong> <strong>2008</strong><br />
Features in AD CS<br />
Gathering Information for Designing Certification Authority Hierarchy<br />
Certification Authority Hierarchy Roles<br />
Common Roles in a CA Hierarchy<br />
Demo: Designing PKI for Windows <strong>Server</strong><br />
Options for Designing Certification Authority Hierarchy<br />
Types of CA Hierarchies<br />
Guidelines for Designing a Certification Authority Hierarchy<br />
What Are Certificate Templates?<br />
Certificate Templates in Windows <strong>Server</strong> <strong>2008</strong><br />
Managing Certificate Templates<br />
Superseding Templates Feature<br />
Designing Certificate Templates<br />
Designing Certificate Templates with Customized Add-ons<br />
Demo: Updating Templates<br />
Guidelines for Designing Certificate Templates<br />
Certificate Distribution and Enrollment<br />
Choosing Enrollment Method<br />
Certificate Autoenrollment<br />
Demo: <strong>Implementing</strong> Autoenrollment<br />
What is Certificate Revocation?<br />
Guidelines for Designing Certificate Revocation<br />
Module 09 Review<br />
Module 10 - Designing an AD RMS Infrastructure<br />
Designing an Active Directory RMS Infrastructure in Windows <strong>Server</strong> <strong>2008</strong><br />
What is AD RMS?<br />
Key Components of AD RMS<br />
Scalability Requirements for AD RMS Design<br />
1h29m<br />
45m
Considerations for External Client AD RMS Access<br />
What are AD RMS Rights Policy Templates?<br />
Options for Configuring AD RMS Clusters<br />
Guidelines for Designing AD RMS Clusters<br />
Options for Granting External Users Access to AD RMS<br />
Guidelines for Designing AD RMS Access<br />
AD RMS Backup Components<br />
Options for Restoring AD RMS<br />
Troubleshooting AD RMS Restores – Different Processes<br />
Restoring a Cluster Member<br />
Restoring a Non-Cluster <strong>Server</strong><br />
Demo: Exploring RMS<br />
RMS Root <strong>Server</strong><br />
Guidelines for <strong>Implementing</strong> an AD RMS Backup and Recovery Strategy<br />
Module 10 Review<br />
Module 11 - Designing an AD Federation Services Implementation<br />
54m<br />
Designing an Active Directory Federation Services Implementation in Windows <strong>Server</strong> <strong>2008</strong><br />
What is Active Directory Federation Services?<br />
Key Components of AD FS<br />
Deployment Scenarios for AD FS<br />
AD FS <strong>Server</strong> Roles<br />
AD FS <strong>Server</strong> Placement<br />
AD FS User Account Stores<br />
Components of a B2B Federation Trust<br />
B2B Federation Trust<br />
Demo: Adding the Federation Service Role<br />
Demo: Exporting Certificates<br />
Demo: Importing Certificates<br />
Key Components of B2B Federation Trust<br />
Guidelines for Configuring Certificates and Applications<br />
Guidelines for Designing the Account and Resource Partner Components<br />
Guidelines for Deploying and Securing AD FS <strong>Server</strong>s<br />
Deploy Federation <strong>Server</strong> Proxy In Perimeter Network When…<br />
Additional Guidelines for Deploying and Securing ADFS <strong>Server</strong>s<br />
Options for Configuring AD FS Claims<br />
AD FS Group Claims<br />
Guidelines for Usage of AD FS Claims<br />
Understanding AD FS Applications<br />
Guidelines for Usage of Token-based and Claims-aware Applications<br />
Module 11 Review<br />
Module 12 - Designing an AD LDS Implementation<br />
Designing an Active Directory LDS Implementation<br />
What is AD LDS?<br />
AD LDS Usage<br />
LDAP-Compliant Application Directories<br />
Definitions - LDAP Application Directories<br />
LDAP Compliant Applications - Defined<br />
Extranet Authentication Scenarios<br />
1h
Using AD LDS for Developing Schema Modifications<br />
Key Sizing Factors for AD LDS <strong>Server</strong>s<br />
AD LDS Replication Scenarios<br />
Integration of AD LDS with AD DS<br />
Guidelines for Designing AD LDS Instances and Application Partitions<br />
Schema Changes and AD LDS<br />
Replication of AD LDS Data<br />
Planning AD LDS Replication Traffic across WAN Links<br />
AD LDS Sites and Site Links<br />
Guidelines for Designing AD LDS Schema and Replication<br />
User Proxies in AD LDS<br />
Authentication and Authorization in AD LDS<br />
<strong>Implementing</strong> Synchronization between AD DS and AD LDS<br />
Demo: Working with AD LDS<br />
Module 12 Review<br />
Module 13 - Designing AD Migrations<br />
Designing Active Directory Migrations in Windows <strong>Server</strong> <strong>2008</strong><br />
AD DS Migration Strategies<br />
Domain Upgrade Strategy<br />
Domain Restructure Strategy<br />
Domain Upgrade and Restructure<br />
Criteria for Choosing a Migration Strategy<br />
Guidelines for Choosing the Domain Upgrade Strategy<br />
Guidelines for Choosing the Domain Restructure Strategy<br />
Guidelines for Choosing the Domain Upgrade and Restructure Strategy<br />
Documenting the Current Environment<br />
Active Directory Structure<br />
Current Network Services<br />
Current Domain Controller Hardware and Software<br />
Cleaning Up the Current Active Directory Environment<br />
Hardware and Application Compatibility<br />
Preparing a Domain and Forest for Upgrade<br />
Upgrade Guidelines<br />
Domain Functional Levels in Windows <strong>Server</strong> <strong>2008</strong><br />
Windows 2000 Native Functional Level<br />
Windows <strong>Server</strong> 2003 Functional Level<br />
Windows <strong>Server</strong> <strong>2008</strong> Functional Mode<br />
SID History<br />
Active Directory Migration Tool<br />
ADMT Scenarios<br />
Preparing a Domain to Run ADMT<br />
Demo: Installing ADMT<br />
Intraforest and Interforest Restructuring<br />
Demo: Using ADMT Trusts<br />
59m
Guidelines for Restructuring Domains<br />
Module 13 Review<br />
Course Closure<br />
Course Introduction<br />
Module 1 - Designing an AD Forest Infrastructure<br />
Designing an Active Directory Forest Infrastructure in Windows <strong>Server</strong> <strong>2008</strong><br />
Overview of AD DS Forest Design Requirements<br />
Design Requirements – AD DS Forest<br />
Business Requirements for an AD DS Forest Design<br />
AD Forest Design<br />
Administrative and Security Requirements<br />
Technical Requirements for an AD DS Forest Design<br />
Types of AD DS Forests<br />
Benefits of a Single Forest Model<br />
Disadvantages of Single Forest Model<br />
Reasons for <strong>Implementing</strong> Multiple Forests<br />
Benefits of <strong>Implementing</strong> Forest Root Domains<br />
Types of Forest Functional Levels<br />
Forest Functional Levels<br />
Windows <strong>Server</strong> 2003 Forest Functional Level<br />
Guidelines for Designing an AD DS Forest<br />
Types of Trusts<br />
What Is UPN Suffix Routing?<br />
Guidelines for Designing Forest Trusts<br />
Demo: <strong>Implementing</strong> an AD Forest Trust Design<br />
Modifications to AD DS Schema<br />
Guidelines for AD DS Schema Modifications<br />
Demo: Schema Changes<br />
How Does Windows Time Service Work?<br />
Considerations for Configuring Windows Time Service<br />
Member <strong>Server</strong>s and Workstations<br />
Domain Controllers<br />
Considerations<br />
Module 1 Review<br />
Module 2 - Designing an AD Domain Infrastructure<br />
Designing an Active Directory Domain Infrastructure in Windows <strong>Server</strong> <strong>2008</strong><br />
AD DS Domain Design Models<br />
AD DS Domain Models<br />
Factors to Consider When Accessing Domain Models<br />
Reasons for Deploying Multiple AD DS Domains<br />
AD DS Domain Functional Levels<br />
Supported Domain Controller Operating Systems<br />
Considerations for Configuring and Placing the Domain Controllers<br />
Considerations for Deploying Domain Controllers in Branch Offices<br />
Read Only Domain Controller (RODC)<br />
Guidelines for Designing AD DS Domains<br />
Choosing an AD DS Namespace Strategy<br />
Guidelines for Integrating the Public and Private DNS Namespaces<br />
1h7m<br />
1h11m<br />
8m
Guidelines for Integrating Multiple Internal DNS Namespaces<br />
Guidelines for <strong>Implementing</strong> DNS <strong>Server</strong>s<br />
Demo: Configuring Forwarders and Delegation Records<br />
Windows <strong>2008</strong> Domain Controllers<br />
Domain Controller on a <strong>Server</strong> Core<br />
Deploying Domain Controllers in Windows <strong>Server</strong> <strong>2008</strong><br />
Deploying Domain Controllers in Windows <strong>Server</strong> <strong>2008</strong> - RODC<br />
Why Deploy RODC?<br />
Considerations When Deploying Domain Controllers<br />
Demo: Configuring an RODC Replication Policy<br />
Types of AD DS Domain Trusts<br />
Security Considerations for Trusts<br />
Demo: Trust Design<br />
Module 02 Review<br />
Module 03 - Designing AD Sites and Replication<br />
Designing Active Directory Sites and Replication in Windows <strong>Server</strong> <strong>2008</strong><br />
Things to Document Before the AD Site Design<br />
Network Information for an AD DS Site Design<br />
Location Data for an AD DS Site Design<br />
AD DS Site Models<br />
Guidelines for Creating Additional AD DS Sites<br />
Demo: <strong>Implementing</strong> AD DS Site Design<br />
Locations<br />
How Does Automatic Site Coverage Work?<br />
Types of Replication Topologies<br />
Considerations for Choosing a Replication Protocol<br />
Levels of Connectivity<br />
Choosing Replication Protocols<br />
Demo: <strong>Implementing</strong> AD DS Replication<br />
Replication of Global Catalog, RODC, and SYSVOL<br />
Knowledge Consistency Checker<br />
Inter Site Topology Generator<br />
Using Site Links to Manage Replication<br />
Considerations for Designing Site Links and Bridgehead <strong>Server</strong>s<br />
Considerations for Designing Site-Link Bridging<br />
Considerations for Site Link Bridging<br />
Options for Configuring AD DS Replication<br />
Guidelines for Configuring AD DS Replication<br />
Guidelines for Placing Domain Controllers<br />
Guidelines for Placing RODCs<br />
Guidelines for Placing Global Catalog <strong>Server</strong>s<br />
Guidelines for Placing Operations Master <strong>Server</strong>s<br />
Module 03 Review<br />
Module 04 - Designing AD Domain Administrative Structures<br />
Designing Active Directory Domain Administrative Structures in Windows <strong>Server</strong> <strong>2008</strong><br />
Types of IT Administrative Models<br />
Guidelines for Gathering Information on the Current Administrative Structures<br />
Business Requirements for Existing Structure<br />
1h20m<br />
56m
Legal Requirements<br />
Guidelines for Gathering Information on Organizational Resources<br />
Guidelines for Gathering Information on Administrative Processes<br />
Strategies for Designing Organizational Units<br />
Strategies for Delegating Administrative Control<br />
Strategies for Designing Group Policy Structures<br />
Considerations for Designing Organizational Unit Hierarchies<br />
Guidelines for Designing an Organizational Unit Structure<br />
Demo: Creating an AD OU Design<br />
AD DS Groups in Windows <strong>Server</strong> <strong>2008</strong><br />
Group Scope<br />
Guidelines for Developing a Group Naming Strategy<br />
Considerations for Group Nesting<br />
Group Nesting<br />
Strategies for Using Groups to Access Resources<br />
Strategies for Placing Group Objects<br />
Guidelines for Designing an AD DS Group Strategy<br />
Guidelines for Designing a User Account Strategy<br />
Guidelines for Designing a Computer Account Strategy<br />
Naming Strategies for Computer Accounts<br />
Guidelines for Securing User and Computer Account Management<br />
Demo: Automating User Account Management<br />
Tools for Automating User and Computer Account Management<br />
Module 04 Review<br />
Module 05 - Designing AD Group Policy<br />
Designing Active Directory Group Policy in Windows <strong>Server</strong> <strong>2008</strong><br />
Gathering Organizational Information<br />
Gathering Information on Security Requirements<br />
Gathering Information on Desktop Management Requirements<br />
Gathering Information on Desktop Management<br />
Gathering Information on Administrative Processes<br />
Configuring Group Policy Settings<br />
Demo: Designing AD Group Policy<br />
Applying Group Policy Settings<br />
Demo: <strong>Implementing</strong> AD Group Policy<br />
Group Policy Storage Locations<br />
ADMX Format for Administrative Template<br />
Guidelines for Designing Administrative Templates<br />
Slow Link Detection<br />
Best Practices for Group Policy Model Design<br />
Guidelines for Designing Group Policy Inheritance<br />
Guidelines for Designing Group Policy Filtering<br />
Guidelines for Designing Group Policy Application<br />
GPO Backup and Recovery Strategy<br />
GPO Migration Strategy<br />
Delegating GPO Administration<br />
GPO Administration<br />
Module 05 Review<br />
1h21m
Module 06 - Designing AD Security<br />
Designing Active Directory Security in Windows <strong>Server</strong> <strong>2008</strong><br />
Gathering Information for Designing Account Security Policies<br />
Key Components for Designing Account Security Policies<br />
Guidelines for Designing Account and Password Policy<br />
Guidelines for Designing Secure Account Management<br />
Fine-Grained Password Policies<br />
What Are Fine-Grained Password Policies?<br />
Storing Fine-Grained Password Policies<br />
Demo: Designing AD DS Security<br />
Password Setting Object Attributes<br />
How PSOs Are Processed and Applied<br />
Guidelines for Designing Fine-Grained<br />
Key Components that Affect Domain Controller Security<br />
Why Modify the Default Domain Controller Security Policy?<br />
<strong>Server</strong> Core <strong>Server</strong> Roles<br />
<strong>Server</strong> Core as a Solution for Domain Controller Deployment<br />
What is the Security Configuration Wizard?<br />
Scenarios for Using the Security Configuration Wizard<br />
What Are Read-Only Domain Controllers?<br />
Prerequisites for Deploying RODCs<br />
Administrator Role Separation on RODCs<br />
Demo: Domain Controller/RODC Security Policies<br />
Administrator Responsibilities<br />
Service Administrator and Service Management<br />
Data Administrators and Data Management<br />
What Are Administrative Autonomy<br />
Delegation of Administrative Permission<br />
Attributes of a Good Delegation Model<br />
Guidelines for Creating a Delegation Model<br />
Guidelines for Using and Securing Administrator Accounts<br />
Demo: Restricted Groups<br />
Auditing Administrative Access<br />
Module 06 Review<br />
Module 07 - Designing AD High Availability<br />
Designing Active Directory High Availability in Windows <strong>Server</strong> <strong>2008</strong><br />
What is High Availability?<br />
Components of an Active Directory High Availability Design<br />
Active Directory High Availability<br />
Business Requirements for AD DS High Availability<br />
Infrastructure Requirements for AD DS High Availability<br />
High Availability Options for Network Infrastructure<br />
Process of Planning for High Availability<br />
Guidelines for Designing Highly Available Domain Controllers<br />
Global Catalog Placement and High Availability<br />
Demo: Designing AD DS Availability<br />
High Availability of DNS<br />
Guidelines for Designing Highly Available Network Infrastructure<br />
Module 07 Review<br />
1h52m<br />
27m
Module 08 - Designing AD Disaster Recovery<br />
Designing Active Directory Disaster Recovery in Windows <strong>Server</strong> <strong>2008</strong><br />
Overview of <strong>Database</strong> Maintenance<br />
NTDSUtil.exe<br />
Benefits of Restartable AD DS in Windows <strong>Server</strong> <strong>2008</strong><br />
Considerations for Using Restartable AD DS<br />
Overview of AD DS Backup and Recovery<br />
Windows <strong>Server</strong> Backup<br />
AD DS Backup and Recovery in Windows <strong>Server</strong> <strong>2008</strong><br />
Active Directory Domain Services Backup System Components<br />
System State Data<br />
Critical Volumes – Review<br />
Options for Restoring AD DS<br />
Considerations for Restoring AD DS<br />
Guidelines for Designing Backup and Recovery in AD DS<br />
Why Monitor AD DS?<br />
Tools for Monitoring AD DS<br />
Reliability and Performance Monitor<br />
Demo: Disaster Recovery and Monitoring<br />
Guidelines for Monitoring Active Directory Domain Controllers<br />
NTDS Counters – Monitoring AD<br />
Module 08 Review<br />
Module 09 - Designing Public Key Infrastructure<br />
Designing Public Key Infrastructure in Windows <strong>Server</strong> <strong>2008</strong><br />
What is a PKI?<br />
Key Components of a PKI<br />
PKI Solution Requirements<br />
Applications That Use PKI<br />
Certification Authorities and PKI<br />
Comparison of Enterprise and Standalone<br />
Internal and Public Certification Authorities<br />
Using Both Internal and External Public CA’s<br />
Active Directory Certificate Services in Windows <strong>Server</strong> <strong>2008</strong><br />
Features in AD CS<br />
Gathering Information for Designing Certification Authority Hierarchy<br />
Certification Authority Hierarchy Roles<br />
Common Roles in a CA Hierarchy<br />
Demo: Designing PKI for Windows <strong>Server</strong><br />
Options for Designing Certification Authority Hierarchy<br />
Types of CA Hierarchies<br />
Guidelines for Designing a Certification Authority Hierarchy<br />
What Are Certificate Templates?<br />
Certificate Templates in Windows <strong>Server</strong> <strong>2008</strong><br />
Managing Certificate Templates<br />
Superseding Templates Feature<br />
Designing Certificate Templates<br />
Designing Certificate Templates with Customized Add-ons<br />
Demo: Updating Templates<br />
57m<br />
1h29m
Guidelines for Designing Certificate Templates<br />
Certificate Distribution and Enrollment<br />
Choosing Enrollment Method<br />
Certificate Autoenrollment<br />
Demo: <strong>Implementing</strong> Autoenrollment<br />
What is Certificate Revocation?<br />
Guidelines for Designing Certificate Revocation<br />
Module 09 Review<br />
Module 10 - Designing an AD RMS Infrastructure<br />
Designing an Active Directory RMS Infrastructure in Windows <strong>Server</strong> <strong>2008</strong><br />
What is AD RMS?<br />
Key Components of AD RMS<br />
Scalability Requirements for AD RMS Design<br />
Considerations for External Client AD RMS Access<br />
What are AD RMS Rights Policy Templates?<br />
Options for Configuring AD RMS Clusters<br />
Guidelines for Designing AD RMS Clusters<br />
Options for Granting External Users Access to AD RMS<br />
Guidelines for Designing AD RMS Access<br />
AD RMS Backup Components<br />
Options for Restoring AD RMS<br />
Troubleshooting AD RMS Restores – Different Processes<br />
Restoring a Cluster Member<br />
Restoring a Non-Cluster <strong>Server</strong><br />
Demo: Exploring RMS<br />
RMS Root <strong>Server</strong><br />
Guidelines for <strong>Implementing</strong> an AD RMS Backup and Recovery Strategy<br />
Module 10 Review<br />
Module 11 - Designing an AD Federation Services Implementation<br />
Designing an Active Directory Federation Services Implementation in Windows <strong>Server</strong> <strong>2008</strong><br />
54m<br />
What is Active Directory Federation Services?<br />
Key Components of AD FS<br />
Deployment Scenarios for AD FS<br />
AD FS <strong>Server</strong> Roles<br />
AD FS <strong>Server</strong> Placement<br />
AD FS User Account Stores<br />
Components of a B2B Federation Trust<br />
B2B Federation Trust<br />
Demo: Adding the Federation Service Role<br />
Demo: Exporting Certificates<br />
Demo: Importing Certificates<br />
Key Components of B2B Federation Trust<br />
Guidelines for Configuring Certificates and Applications<br />
Guidelines for Designing the Account and Resource Partner Components<br />
Guidelines for Deploying and Securing AD FS <strong>Server</strong>s<br />
Deploy Federation <strong>Server</strong> Proxy In Perimeter Network When…<br />
Additional Guidelines for Deploying and Securing ADFS <strong>Server</strong>s<br />
Options for Configuring AD FS Claims<br />
45m
AD FS Group Claims<br />
Guidelines for Usage of AD FS Claims<br />
Understanding AD FS Applications<br />
Guidelines for Usage of Token-based and Claims-aware Applications<br />
Module 11 Review<br />
Module 12 - Designing an AD LDS Implementation<br />
Designing an Active Directory LDS Implementation<br />
What is AD LDS?<br />
AD LDS Usage<br />
LDAP-Compliant Application Directories<br />
Definitions - LDAP Application Directories<br />
LDAP Compliant Applications - Defined<br />
Extranet Authentication Scenarios<br />
Using AD LDS for Developing Schema Modifications<br />
Key Sizing Factors for AD LDS <strong>Server</strong>s<br />
AD LDS Replication Scenarios<br />
Integration of AD LDS with AD DS<br />
Guidelines for Designing AD LDS Instances and Application Partitions<br />
Schema Changes and AD LDS<br />
Replication of AD LDS Data<br />
Planning AD LDS Replication Traffic across WAN Links<br />
AD LDS Sites and Site Links<br />
Guidelines for Designing AD LDS Schema and Replication<br />
User Proxies in AD LDS<br />
Authentication and Authorization in AD LDS<br />
<strong>Implementing</strong> Synchronization between AD DS and AD LDS<br />
Demo: Working with AD LDS<br />
Module 12 Review<br />
Module 13 - Designing AD Migrations<br />
Designing Active Directory Migrations in Windows <strong>Server</strong> <strong>2008</strong><br />
AD DS Migration Strategies<br />
Domain Upgrade Strategy<br />
Domain Restructure Strategy<br />
Domain Upgrade and Restructure<br />
Criteria for Choosing a Migration Strategy<br />
Guidelines for Choosing the Domain Upgrade Strategy<br />
Guidelines for Choosing the Domain Restructure Strategy<br />
Guidelines for Choosing the Domain Upgrade and Restructure Strategy<br />
Documenting the Current Environment<br />
Active Directory Structure<br />
Current Network Services<br />
Current Domain Controller Hardware and Software<br />
Cleaning Up the Current Active Directory Environment<br />
1h<br />
59m
Hardware and Application Compatibility<br />
Preparing a Domain and Forest for Upgrade<br />
Upgrade Guidelines<br />
Domain Functional Levels in Windows <strong>Server</strong> <strong>2008</strong><br />
Windows 2000 Native Functional Level<br />
Windows <strong>Server</strong> 2003 Functional Level<br />
Windows <strong>Server</strong> <strong>2008</strong> Functional Mode<br />
SID History<br />
Active Directory Migration Tool<br />
ADMT Scenarios<br />
Preparing a Domain to Run ADMT<br />
Demo: Installing ADMT<br />
Intraforest and Interforest Restructuring<br />
Demo: Using ADMT Trusts<br />
Guidelines for Restructuring Domains<br />
Module 13 Review<br />
Course Closure<br />
Total Duration: 16 hrs 57 min