- Page 3 and 4: Trend Micro Incorporated reserves t
- Page 5 and 6: Contents Preface Contents ScanMail
- Page 7 and 8: Contents Understanding the Server M
- Page 9 and 10: Chapter 8: Performing Administrativ
- Page 11 and 12: Contents Before Contacting Technica
- Page 13 and 14: Contents Example 9: Get Virus Types
- Page 15 and 16: Preface Preface Welcome to the Tren
- Page 17 and 18: Document Conventions To help you lo
- Page 19 and 20: Chapter 1 Introducing Trend Micro S
- Page 21 and 22: Introducing Trend Micro ScanMail fo
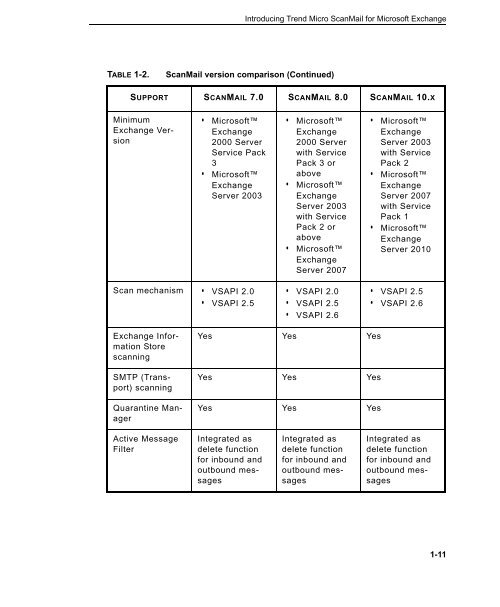
- Page 23 and 24: Introducing Trend Micro ScanMail fo
- Page 25 and 26: Introducing Trend Micro ScanMail fo
- Page 27: Cluster Support ScanMail supports c
- Page 31 and 32: Introducing Trend Micro ScanMail fo
- Page 33 and 34: Introducing Trend Micro ScanMail fo
- Page 35 and 36: About Uncleanable Files Introducing
- Page 37 and 38: Introducing Trend Micro ScanMail fo
- Page 39 and 40: Smart Protection Sources Introducin
- Page 41 and 42: Introducing Trend Micro ScanMail fo
- Page 43 and 44: The Trend Micro Pattern Files Intro
- Page 45 and 46: Manual Scan Introducing Trend Micro
- Page 47 and 48: Introducing Trend Micro ScanMail fo
- Page 49 and 50: Introducing Trend Micro ScanMail fo
- Page 51 and 52: About Attachment Blocking Introduci
- Page 53 and 54: Introducing Trend Micro ScanMail fo
- Page 55 and 56: Introducing Trend Micro ScanMail fo
- Page 57 and 58: Keyword Lists Introducing Trend Mic
- Page 59 and 60: TABLE 1-6. Criteria for a Keyword L
- Page 61 and 62: About Email Reputation Introducing
- Page 63 and 64: Introducing Trend Micro ScanMail fo
- Page 65 and 66: Manage End User Quarantine Introduc
- Page 67 and 68: Renewing a Maintenance Agreement In
- Page 69 and 70: Getting Started with ScanMail Chapt
- Page 71 and 72: To view the product console for a l
- Page 73 and 74: Getting Started with ScanMail • R
- Page 75 and 76: Getting Started with ScanMail Confi
- Page 77 and 78: Getting Started with ScanMail When
- Page 79 and 80:
Activation Codes Getting Started wi
- Page 81 and 82:
Getting Started with ScanMail Suite
- Page 83 and 84:
Reactivating ScanMail Getting Start
- Page 85 and 86:
Updating Components on Clusters Get
- Page 87 and 88:
Getting Started with ScanMail b. Se
- Page 89 and 90:
Getting Started with ScanMail be to
- Page 91 and 92:
Chapter 3 Establishing and Maintain
- Page 93 and 94:
Maintaining Security Establishing a
- Page 95 and 96:
Managing Outbreak Situations Establ
- Page 97 and 98:
Managing ScanMail Chapter 4 This ch
- Page 99 and 100:
Understanding the Server Management
- Page 101 and 102:
Using the Server Management Console
- Page 103 and 104:
Viewing Servers from the Product Co
- Page 105 and 106:
Managing ScanMail 5. Select the che
- Page 107 and 108:
Managing ScanMail 3. Once the resou
- Page 109 and 110:
Starting and Stopping the Services
- Page 111 and 112:
TABLE 4-2. ScanMail icons (Continue
- Page 113 and 114:
Configuring Scanning Chapter 5 This
- Page 115 and 116:
Configuring Scanning Tip: You can l
- Page 117 and 118:
Compression Types Configuring Scann
- Page 119 and 120:
TABLE 5-1. ScanMail Actions (Contin
- Page 121 and 122:
Configuring Scanning For correct re
- Page 123 and 124:
TABLE 5-2. Notification settings (C
- Page 125 and 126:
The following describes the key cha
- Page 127 and 128:
Configuring Scanning • When you w
- Page 129 and 130:
Configuring Scanning • Select Do
- Page 131 and 132:
Configuring Scanning 3. Select Enab
- Page 133 and 134:
Configuring Attachment Blocking Not
- Page 135 and 136:
Content Filtering Configuring Scann
- Page 137 and 138:
Configuring Scanning • Click Expo
- Page 139 and 140:
Step 4: Specify Notifications To co
- Page 141 and 142:
Configuring Scanning 5. Type a desc
- Page 143 and 144:
Configuring Scanning a. Type a keyw
- Page 145 and 146:
Modifying Data Loss Prevention Temp
- Page 147 and 148:
4. Click Import to import the templ
- Page 149 and 150:
Step 2: Specify Rule To specify a D
- Page 151 and 152:
Step 4: Specify Notification To con
- Page 153 and 154:
• Type an approved IP address and
- Page 155 and 156:
Configuring Content Scanning Action
- Page 157 and 158:
Configuring Scanning 3. Select Scan
- Page 159 and 160:
Managing the Quarantine Area Chapte
- Page 161 and 162:
Quarantine Query Managing the Quara
- Page 163 and 164:
Managing the Quarantine Area a. Cli
- Page 165 and 166:
Monitoring ScanMail Chapter 7 This
- Page 167 and 168:
Monitoring ScanMail • Smart Prote
- Page 169 and 170:
Monitoring ScanMail • Smart Prote
- Page 171 and 172:
Alert Notification Settings Monitor
- Page 173 and 174:
• Unscannable message report •
- Page 175 and 176:
Report Maintenance Monitoring ScanM
- Page 177 and 178:
TABLE 7-1. Log types (Continued) Lo
- Page 179 and 180:
Log Maintenance Monitoring ScanMail
- Page 181 and 182:
Chapter 8 Performing Administrative
- Page 183 and 184:
• Spam Prevention • Web Reputat
- Page 185 and 186:
About Access Control Performing Adm
- Page 187 and 188:
To configure Access Control: Perfor
- Page 189 and 190:
To configure internal domains: Perf
- Page 191 and 192:
About Trend Micro Control Manager P
- Page 193 and 194:
Performing Administrative Tasks •
- Page 195 and 196:
Understanding Security Risks Chapte
- Page 197 and 198:
TABLE 9-1. Internet Security Risks
- Page 199 and 200:
Understanding Security Risks For ex
- Page 201 and 202:
Joke Programs Understanding Securit
- Page 203 and 204:
Zip of Death Understanding Security
- Page 205 and 206:
Understanding Security Risks • Lo
- Page 207 and 208:
TABLE 9-2. Malware naming (Continue
- Page 209 and 210:
Understanding Security Risks Multip
- Page 211 and 212:
Chapter 10 Getting Support and Cont
- Page 213 and 214:
Getting Support and Contacting Tren
- Page 215 and 216:
Growing Hazard Getting Support and
- Page 217 and 218:
TABLE 10-1. Using Operators with Ke
- Page 219 and 220:
Getting Support and Contacting Tren
- Page 221 and 222:
Getting Support and Contacting Tren
- Page 223 and 224:
Are Some Files Dangerous? Getting S
- Page 225 and 226:
Counting and Grouping TABLE 10-4. C
- Page 227 and 228:
Character Classes (shorthand) TABLE
- Page 229 and 230:
TABLE 10-6. Character classes (Cont
- Page 231 and 232:
Escape Sequences Regular Expression
- Page 233 and 234:
Using Keywords Effectively Getting
- Page 235 and 236:
Troubleshooting Update the Scan Eng
- Page 237 and 238:
Known Issues Getting Support and Co
- Page 239 and 240:
Before Contacting Technical Support
- Page 241 and 242:
Getting Support and Contacting Tren
- Page 243 and 244:
Appendix A Introducing Trend Micro
- Page 245 and 246:
How to Use Control Manager Introduc
- Page 247 and 248:
Control Manager Architecture Introd
- Page 249 and 250:
TABLE A-2. Control Manager Componen
- Page 251 and 252:
Introducing Trend Micro Control Man
- Page 253 and 254:
Introducing Trend Micro Control Man
- Page 255 and 256:
Determining the Right Heartbeat Set
- Page 257 and 258:
TABLE A-5. Product Directory Option
- Page 259 and 260:
A sample Product Directory appears
- Page 261 and 262:
Introducing Trend Micro Control Man
- Page 263 and 264:
Introducing Trend Micro Control Man
- Page 265 and 266:
Introducing Trend Micro Control Man
- Page 267 and 268:
Using the Directory Management Scre
- Page 269 and 270:
Introducing Trend Micro Control Man
- Page 271 and 272:
Introducing Trend Micro Control Man
- Page 273 and 274:
Introducing Trend Micro Control Man
- Page 275 and 276:
To configure manual download settin
- Page 277 and 278:
Introducing Trend Micro Control Man
- Page 279 and 280:
Introducing Trend Micro Control Man
- Page 281 and 282:
Introducing Trend Micro Control Man
- Page 283 and 284:
Introducing Trend Micro Control Man
- Page 285 and 286:
Introducing Trend Micro Control Man
- Page 287 and 288:
Introducing Trend Micro Control Man
- Page 289 and 290:
• Administrator privilege • "Lo
- Page 291 and 292:
Introducing Trend Micro Control Man
- Page 293 and 294:
Introducing Trend Micro Control Man
- Page 295 and 296:
Windows Event Log Codes Appendix B
- Page 297 and 298:
TABLE B-1. ScanMail Windows Event L
- Page 299 and 300:
TABLE B-1. ScanMail Windows Event L
- Page 301 and 302:
TABLE B-1. ScanMail Windows Event L
- Page 303 and 304:
Appendix C Database Schema for 64-b
- Page 305 and 306:
Database Schema for 64-bit Operatin
- Page 307 and 308:
TABLE C-3. Table [tblStorageEntries
- Page 309 and 310:
Database Schema for 64-bit Operatin
- Page 311 and 312:
Database Schema for 64-bit Operatin
- Page 313 and 314:
Table C-10. Table [tblManagementGro
- Page 315 and 316:
Database Schema for 64-bit Operatin
- Page 317 and 318:
Database Schema for 64-bit Operatin
- Page 319 and 320:
TABLE C-16. Possible values of the
- Page 321 and 322:
Database Schema for 64-bit Operatin
- Page 323 and 324:
TABLE C-19. View [vwMsgFilterEntrie
- Page 325 and 326:
TABLE C-20. View [vwMsgFilterEntrie
- Page 327 and 328:
Database Schema for 64-bit Operatin
- Page 329 and 330:
Database Schema for 64-bit Operatin
- Page 331 and 332:
Database Schema for 64-bit Operatin
- Page 333 and 334:
Database Schema for 64-bit Operatin
- Page 335 and 336:
TABLE C-26. View [vwUSLogs] (Contin
- Page 337 and 338:
TABLE C-27. View [vwQuarantineLogs]
- Page 339 and 340:
TABLE C-28. View [vwWTPLogs] (Conti
- Page 341 and 342:
Report Database Schema Database Sch
- Page 343 and 344:
Database Schema for 64-bit Operatin
- Page 345 and 346:
Database Schema for 64-bit Operatin
- Page 347 and 348:
Database Schema for 64-bit Operatin
- Page 349 and 350:
Database Schema for 64-bit Operatin
- Page 351 and 352:
ORDER BY Sum(virusinfo_count) DESC;
- Page 353 and 354:
TABLE C-39. Virus Type Database Sch
- Page 355 and 356:
Appendix D Database Schema for 32-b
- Page 357 and 358:
Database Schema for 32-bit Operatin
- Page 359 and 360:
Database Schema for 32-bit Operatin
- Page 361 and 362:
Database Schema for 32-bit Operatin
- Page 363 and 364:
Database Schema for 32-bit Operatin
- Page 365 and 366:
Database Schema for 32-bit Operatin
- Page 367 and 368:
Database Schema for 32-bit Operatin
- Page 369 and 370:
TABLE D-14. Possible values of the
- Page 371 and 372:
Database Schema for 32-bit Operatin
- Page 373 and 374:
Database Schema for 32-bit Operatin
- Page 375 and 376:
Log View Database Schema Database S
- Page 377 and 378:
TABLE D-20. View [vwMsgFilterEntrie
- Page 379 and 380:
TABLE D-21. View [vwMsgStorageEntri
- Page 381 and 382:
TABLE D-22. View [vwABLogs] (Contin
- Page 383 and 384:
TABLE D-23. View [vwAVLogs] (Contin
- Page 385 and 386:
TABLE D-24. View [vwCFLogs] (Contin
- Page 387 and 388:
TABLE D-25. View [vwDLPLogs] (Conti
- Page 389 and 390:
TABLE D-26. View [vwUSLogs] (Contin
- Page 391 and 392:
TABLE D-28. View [vwWTPLogs] (Conti
- Page 393 and 394:
Report Database Schema Database Sch
- Page 395 and 396:
Database Schema for 32-bit Operatin
- Page 397 and 398:
Database Schema for 32-bit Operatin
- Page 399 and 400:
TABLE D-36. Table [tblReportCollect
- Page 401 and 402:
Database Schema for 32-bit Operatin
- Page 403 and 404:
WHERE virusinfo_cate_id =151 AND vi
- Page 405 and 406:
Database Schema for 32-bit Operatin
- Page 407 and 408:
TABLE D-40. Virus Name String (Cont
- Page 409 and 410:
Best Practices Appendix E This chap
- Page 411 and 412:
Best Practices Note: Exchange 2003
- Page 413 and 414:
Scenario: Best Practices The compan
- Page 415 and 416:
Data Identifiers and Template Creat
- Page 417 and 418:
Best Practices Note: Hidden keys wi
- Page 419 and 420:
• Security Risk Scan: Clean • D
- Page 421 and 422:
Index Symbols 1-36-1-37 A access co
- Page 423 and 424:
Step 2 - Specify Rule 5-37 Step 3 -
- Page 425 and 426:
spam pattern files 1-47 updates 2-1
- Page 427 and 428:
packed files 9-3 phish 9-2, 9-16 sp
- Page 429 and 430:
mail server A-5 Management Communic