Chapter 3 Time-to-live Covert Channels - CAIA
Chapter 3 Time-to-live Covert Channels - CAIA
Chapter 3 Time-to-live Covert Channels - CAIA
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
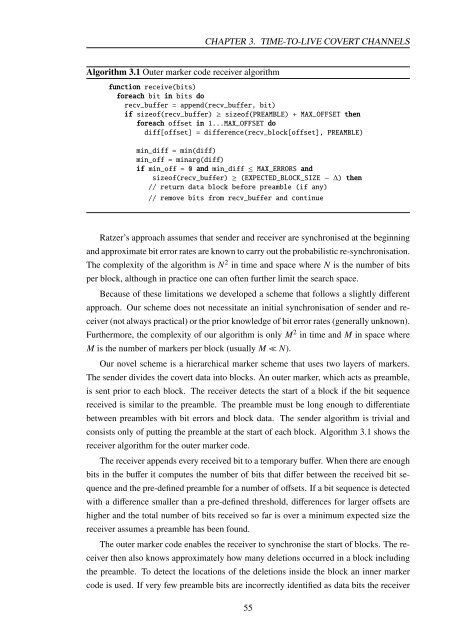
Algorithm 3.1 Outer marker code receiver algorithm<br />
CHAPTER 3. TIME-TO-LIVE COVERT CHANNELS<br />
function receive(bits)<br />
foreach bit in bits do<br />
recv_buffer = append(recv_buffer, bit)<br />
if sizeof(recv_buffer) ≥ sizeof(PREAMBLE) + MAX_OFFSET then<br />
foreach offset in 1...MAX_OFFSET do<br />
diff[offset] = difference(recv_block[offset], PREAMBLE)<br />
min_diff = min(diff)<br />
min_off = minarg(diff)<br />
if min_off = 0 and min_diff ≤ MAX_ERRORS and<br />
sizeof(recv_buffer) ≥ (EXPECTED_BLOCK_SIZE − ∆) then<br />
// return data block before preamble (if any)<br />
// remove bits from recv_buffer and continue<br />
Ratzer’s approach assumes that sender and receiver are synchronised at the beginning<br />
and approximate bit error rates are known <strong>to</strong> carry out the probabilistic re-synchronisation.<br />
The complexity of the algorithm is N 2 in time and space where N is the number of bits<br />
per block, although in practice one can often further limit the search space.<br />
Because of these limitations we developed a scheme that follows a slightly different<br />
approach. Our scheme does not necessitate an initial synchronisation of sender and re-<br />
ceiver (not always practical) or the prior knowledge of bit error rates (generally unknown).<br />
Furthermore, the complexity of our algorithm is only M 2 in time and M in space where<br />
M is the number of markers per block (usually M ≪ N).<br />
Our novel scheme is a hierarchical marker scheme that uses two layers of markers.<br />
The sender divides the covert data in<strong>to</strong> blocks. An outer marker, which acts as preamble,<br />
is sent prior <strong>to</strong> each block. The receiver detects the start of a block if the bit sequence<br />
received is similar <strong>to</strong> the preamble. The preamble must be long enough <strong>to</strong> differentiate<br />
between preambles with bit errors and block data. The sender algorithm is trivial and<br />
consists only of putting the preamble at the start of each block. Algorithm 3.1 shows the<br />
receiver algorithm for the outer marker code.<br />
The receiver appends every received bit <strong>to</strong> a temporary buffer. When there are enough<br />
bits in the buffer it computes the number of bits that differ between the received bit se-<br />
quence and the pre-defined preamble for a number of offsets. If a bit sequence is detected<br />
with a difference smaller than a pre-defined threshold, differences for larger offsets are<br />
higher and the <strong>to</strong>tal number of bits received so far is over a minimum expected size the<br />
receiver assumes a preamble has been found.<br />
The outer marker code enables the receiver <strong>to</strong> synchronise the start of blocks. The re-<br />
ceiver then also knows approximately how many deletions occurred in a block including<br />
the preamble. To detect the locations of the deletions inside the block an inner marker<br />
code is used. If very few preamble bits are incorrectly identified as data bits the receiver<br />
55