Cyber Security of SCADA Systems test bed - Senior Design - Iowa ...
Cyber Security of SCADA Systems test bed - Senior Design - Iowa ...
Cyber Security of SCADA Systems test bed - Senior Design - Iowa ...
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
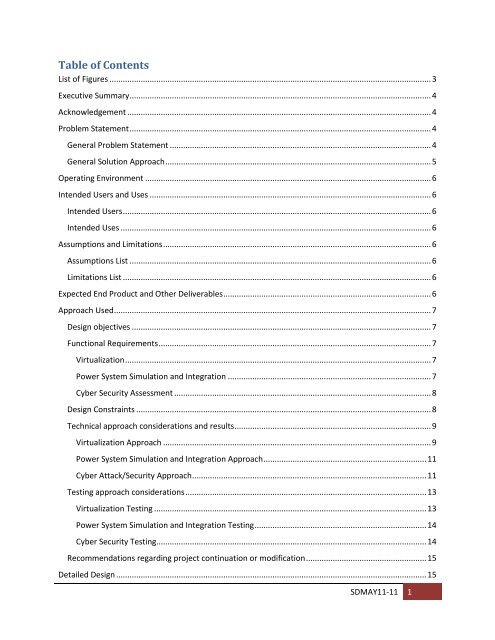
Table <strong>of</strong> Contents<br />
List <strong>of</strong> Figures ................................................................................................................................................ 3<br />
Executive Summary ....................................................................................................................................... 4<br />
Acknowledgement ........................................................................................................................................ 4<br />
Problem Statement ....................................................................................................................................... 4<br />
General Problem Statement ..................................................................................................................... 4<br />
General Solution Approach ....................................................................................................................... 5<br />
Operating Environment ................................................................................................................................ 6<br />
Intended Users and Uses .............................................................................................................................. 6<br />
Intended Users .......................................................................................................................................... 6<br />
Intended Uses ........................................................................................................................................... 6<br />
Assumptions and Limitations ........................................................................................................................ 6<br />
Assumptions List ....................................................................................................................................... 6<br />
Limitations List .......................................................................................................................................... 6<br />
Expected End Product and Other Deliverables ............................................................................................. 6<br />
Approach Used .............................................................................................................................................. 7<br />
<strong>Design</strong> objectives ...................................................................................................................................... 7<br />
Functional Requirements .......................................................................................................................... 7<br />
Virtualization ......................................................................................................................................... 7<br />
Power System Simulation and Integration ........................................................................................... 7<br />
<strong>Cyber</strong> <strong>Security</strong> Assessment ................................................................................................................... 8<br />
<strong>Design</strong> Constraints .................................................................................................................................... 8<br />
Technical approach considerations and results ........................................................................................ 9<br />
Virtualization Approach ........................................................................................................................ 9<br />
Power System Simulation and Integration Approach ......................................................................... 11<br />
<strong>Cyber</strong> Attack/<strong>Security</strong> Approach ......................................................................................................... 11<br />
Testing approach considerations ............................................................................................................ 13<br />
Virtualization Testing .......................................................................................................................... 13<br />
Power System Simulation and Integration Testing ............................................................................. 14<br />
<strong>Cyber</strong> <strong>Security</strong> Testing......................................................................................................................... 14<br />
Recommendations regarding project continuation or modification ...................................................... 15<br />
Detailed <strong>Design</strong> ........................................................................................................................................... 15<br />
SDMAY11-11 1