FortiDDos DDoS Attack Mitigation Guide - Fortinet
FortiDDos DDoS Attack Mitigation Guide - Fortinet
FortiDDos DDoS Attack Mitigation Guide - Fortinet
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
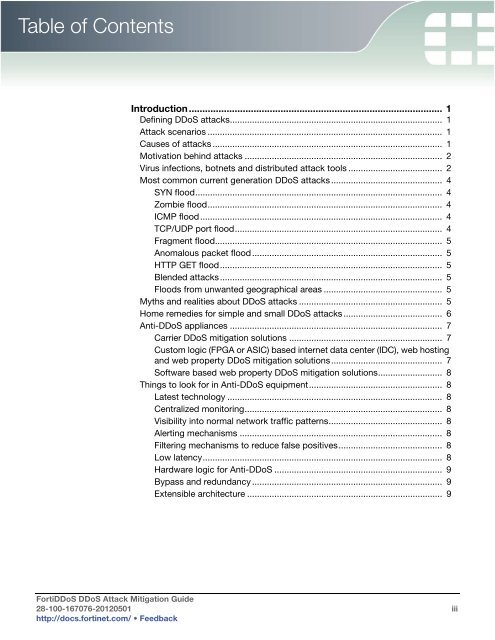
Table of Contents<br />
Introduction.............................................................................................. 1<br />
Defining <strong>DDoS</strong> attacks...................................................................................... 1<br />
<strong>Attack</strong> scenarios ............................................................................................... 1<br />
Causes of attacks ............................................................................................. 1<br />
Motivation behind attacks ................................................................................ 2<br />
Virus infections, botnets and distributed attack tools ...................................... 2<br />
Most common current generation <strong>DDoS</strong> attacks ............................................. 4<br />
SYN flood.................................................................................................... 4<br />
Zombie flood............................................................................................... 4<br />
ICMP flood.................................................................................................. 4<br />
TCP/UDP port flood.................................................................................... 4<br />
Fragment flood............................................................................................ 5<br />
Anomalous packet flood............................................................................. 5<br />
HTTP GET flood.......................................................................................... 5<br />
Blended attacks.......................................................................................... 5<br />
Floods from unwanted geographical areas ................................................ 5<br />
Myths and realities about <strong>DDoS</strong> attacks .......................................................... 5<br />
Home remedies for simple and small <strong>DDoS</strong> attacks ........................................ 6<br />
Anti-<strong>DDoS</strong> appliances ...................................................................................... 7<br />
Carrier <strong>DDoS</strong> mitigation solutions .............................................................. 7<br />
Custom logic (FPGA or ASIC) based internet data center (IDC), web hosting<br />
and web property <strong>DDoS</strong> mitigation solutions............................................. 7<br />
Software based web property <strong>DDoS</strong> mitigation solutions.......................... 8<br />
Things to look for in Anti-<strong>DDoS</strong> equipment...................................................... 8<br />
Latest technology ....................................................................................... 8<br />
Centralized monitoring................................................................................ 8<br />
Visibility into normal network traffic patterns.............................................. 8<br />
Alerting mechanisms .................................................................................. 8<br />
Filtering mechanisms to reduce false positives.......................................... 8<br />
Low latency................................................................................................. 8<br />
Hardware logic for Anti-<strong>DDoS</strong> .................................................................... 9<br />
Bypass and redundancy ............................................................................. 9<br />
Extensible architecture ............................................................................... 9<br />
Forti<strong>DDoS</strong> <strong>DDoS</strong> <strong>Attack</strong> <strong>Mitigation</strong> <strong>Guide</strong><br />
28-100-167076-20120501 iii<br />
http://docs.fortinet.com/ • Feedback