FortiDDos DDoS Attack Mitigation Guide - Fortinet
FortiDDos DDoS Attack Mitigation Guide - Fortinet
FortiDDos DDoS Attack Mitigation Guide - Fortinet
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
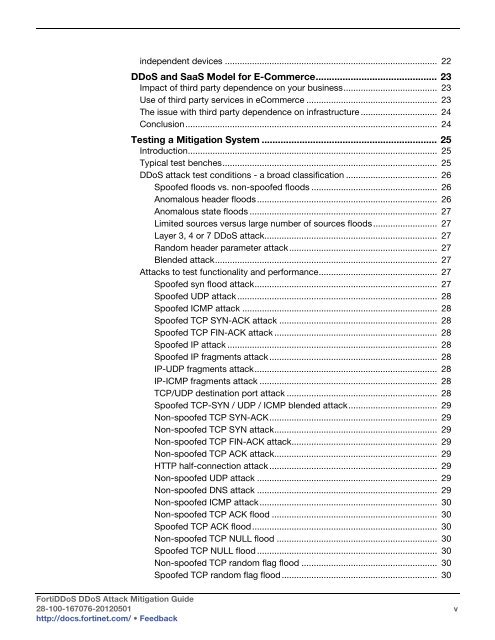
independent devices ...................................................................................... 22<br />
<strong>DDoS</strong> and SaaS Model for E-Commerce............................................. 23<br />
Impact of third party dependence on your business...................................... 23<br />
Use of third party services in eCommerce ..................................................... 23<br />
The issue with third party dependence on infrastructure ............................... 24<br />
Conclusion...................................................................................................... 24<br />
Testing a <strong>Mitigation</strong> System ................................................................. 25<br />
Introduction..................................................................................................... 25<br />
Typical test benches....................................................................................... 25<br />
<strong>DDoS</strong> attack test conditions - a broad classification ..................................... 26<br />
Spoofed floods vs. non-spoofed floods ................................................... 26<br />
Anomalous header floods......................................................................... 26<br />
Anomalous state floods ............................................................................ 27<br />
Limited sources versus large number of sources floods.......................... 27<br />
Layer 3, 4 or 7 <strong>DDoS</strong> attack...................................................................... 27<br />
Random header parameter attack............................................................ 27<br />
Blended attack.......................................................................................... 27<br />
<strong>Attack</strong>s to test functionality and performance................................................ 27<br />
Spoofed syn flood attack.......................................................................... 27<br />
Spoofed UDP attack................................................................................. 28<br />
Spoofed ICMP attack ............................................................................... 28<br />
Spoofed TCP SYN-ACK attack ................................................................ 28<br />
Spoofed TCP FIN-ACK attack .................................................................. 28<br />
Spoofed IP attack ..................................................................................... 28<br />
Spoofed IP fragments attack.................................................................... 28<br />
IP-UDP fragments attack.......................................................................... 28<br />
IP-ICMP fragments attack ........................................................................ 28<br />
TCP/UDP destination port attack ............................................................. 28<br />
Spoofed TCP-SYN / UDP / ICMP blended attack.................................... 29<br />
Non-spoofed TCP SYN-ACK.................................................................... 29<br />
Non-spoofed TCP SYN attack.................................................................. 29<br />
Non-spoofed TCP FIN-ACK attack........................................................... 29<br />
Non-spoofed TCP ACK attack.................................................................. 29<br />
HTTP half-connection attack .................................................................... 29<br />
Non-spoofed UDP attack ......................................................................... 29<br />
Non-spoofed DNS attack ......................................................................... 29<br />
Non-spoofed ICMP attack........................................................................ 30<br />
Non-spoofed TCP ACK flood ................................................................... 30<br />
Spoofed TCP ACK flood........................................................................... 30<br />
Non-spoofed TCP NULL flood ................................................................. 30<br />
Spoofed TCP NULL flood ......................................................................... 30<br />
Non-spoofed TCP random flag flood ....................................................... 30<br />
Spoofed TCP random flag flood............................................................... 30<br />
Forti<strong>DDoS</strong> <strong>DDoS</strong> <strong>Attack</strong> <strong>Mitigation</strong> <strong>Guide</strong><br />
28-100-167076-20120501 v<br />
http://docs.fortinet.com/ • Feedback