FEDERAL SUPPLY SERVICE Federal Network Systems LLC - Verizon
FEDERAL SUPPLY SERVICE Federal Network Systems LLC - Verizon
FEDERAL SUPPLY SERVICE Federal Network Systems LLC - Verizon
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
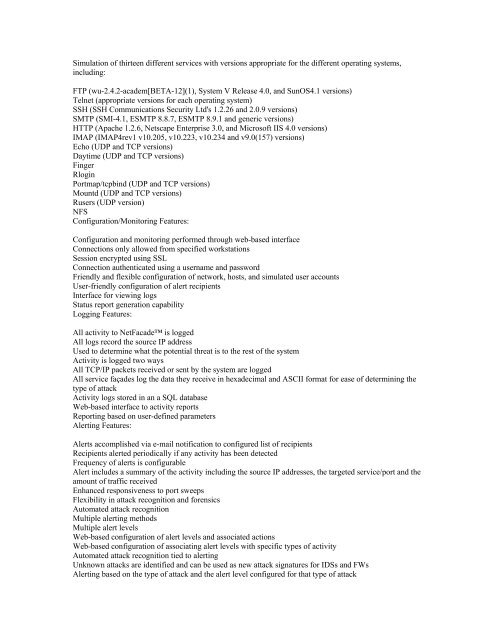
Simulation of thirteen different services with versions appropriate for the different operating systems,<br />
including:<br />
FTP (wu-2.4.2-academ[BETA-12](1), System V Release 4.0, and SunOS4.1 versions)<br />
Telnet (appropriate versions for each operating system)<br />
SSH (SSH Communications Security Ltd's 1.2.26 and 2.0.9 versions)<br />
SMTP (SMI-4.1, ESMTP 8.8.7, ESMTP 8.9.1 and generic versions)<br />
HTTP (Apache 1.2.6, Netscape Enterprise 3.0, and Microsoft IIS 4.0 versions)<br />
IMAP (IMAP4rev1 v10.205, v10.223, v10.234 and v9.0(157) versions)<br />
Echo (UDP and TCP versions)<br />
Daytime (UDP and TCP versions)<br />
Finger<br />
Rlogin<br />
Portmap/tcpbind (UDP and TCP versions)<br />
Mountd (UDP and TCP versions)<br />
Rusers (UDP version)<br />
NFS<br />
Configuration/Monitoring Features:<br />
Configuration and monitoring performed through web-based interface<br />
Connections only allowed from specified workstations<br />
Session encrypted using SSL<br />
Connection authenticated using a username and password<br />
Friendly and flexible configuration of network, hosts, and simulated user accounts<br />
User-friendly configuration of alert recipients<br />
Interface for viewing logs<br />
Status report generation capability<br />
Logging Features:<br />
All activity to NetFacade is logged<br />
All logs record the source IP address<br />
Used to determine what the potential threat is to the rest of the system<br />
Activity is logged two ways<br />
All TCP/IP packets received or sent by the system are logged<br />
All service façades log the data they receive in hexadecimal and ASCII format for ease of determining the<br />
type of attack<br />
Activity logs stored in an a SQL database<br />
Web-based interface to activity reports<br />
Reporting based on user-defined parameters<br />
Alerting Features:<br />
Alerts accomplished via e-mail notification to configured list of recipients<br />
Recipients alerted periodically if any activity has been detected<br />
Frequency of alerts is configurable<br />
Alert includes a summary of the activity including the source IP addresses, the targeted service/port and the<br />
amount of traffic received<br />
Enhanced responsiveness to port sweeps<br />
Flexibility in attack recognition and forensics<br />
Automated attack recognition<br />
Multiple alerting methods<br />
Multiple alert levels<br />
Web-based configuration of alert levels and associated actions<br />
Web-based configuration of associating alert levels with specific types of activity<br />
Automated attack recognition tied to alerting<br />
Unknown attacks are identified and can be used as new attack signatures for IDSs and FWs<br />
Alerting based on the type of attack and the alert level configured for that type of attack