Space Superiority
Space Superiority
Space Superiority
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
What measures should be in place to make sure America is<br />
able to use space capabilities at any time?<br />
On 2 August 2004, the Air Force Chief of Staff, General<br />
John P. Jumper, issued Air Force Doctrine Document 2-<br />
2.1, Counterspace Operations. In this publication, General<br />
Jumper outlines the role of Air Force space in the conduct of<br />
counterspace operations. General Jumper states, “We must<br />
be prepared to deprive an adversary of the benefits of space<br />
capabilities when American interests and lives are at stake.” 5<br />
This involves America’s use of space during combat operations,<br />
but it also includes everyday uses of space. Protecting<br />
those space capabilities is the hurdle that must be overcome to<br />
ensure uninterrupted use. There are DCS measures that can<br />
be taken to maximize usage of both military and commercial<br />
space systems.<br />
For the most part, protecting our space systems does not<br />
require orbiting space sentinels or the pre-emptive destruction<br />
of enemy capabilities. The effectiveness<br />
of hostile attacks can be limited<br />
with passive techniques. Many of these<br />
techniques can be implemented long before<br />
the systems are launched into space.<br />
Designing satellite command and control<br />
and uplink/downlink facilities to be highly<br />
resistant to physical attack is one passive<br />
technique. This is an easy task when<br />
the ground station is on a military installation,<br />
but becomes difficult for commercial<br />
facilities, which often must be<br />
collocated with customers and employee<br />
populations. Protecting commercial sites<br />
will take more planning, manpower, and<br />
effort. However, the repercussions of an<br />
attack on commercial space systems are<br />
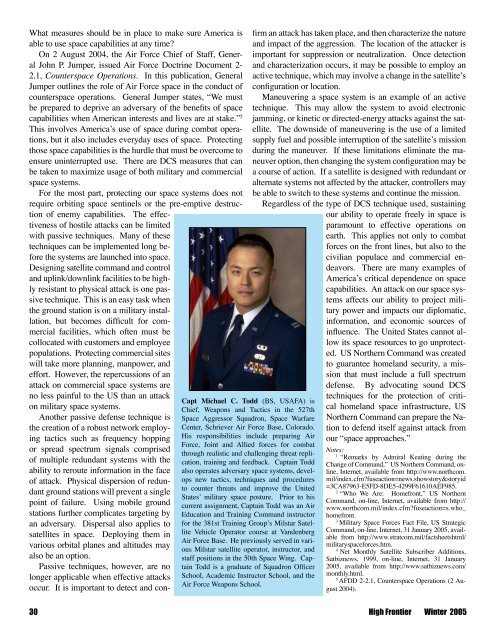
Capt Michael C. Todd (BS, USAFA) is<br />
Chief, Weapons and Tactics in the 527th<br />
<strong>Space</strong> Aggressor Squadron, <strong>Space</strong> Warfare<br />
Center, Schriever Air Force Base, Colorado.<br />
His responsibilities include preparing Air<br />
Force, Joint and Allied forces for combat<br />
through realistic and challenging threat replication,<br />
training and feedback. Captain Todd<br />
also operates adversary space systems, develops<br />
new tactics, techniques and procedures<br />
to counter threats and improve the United<br />
States’ military space posture. Prior to his<br />
current assignment, Captain Todd was an Air<br />
Education and Training Command instructor<br />
for the 381st Training Group’s Milstar Satellite<br />
Vehicle Operator course at Vandenberg<br />
Air Force Base. He previously served in various<br />
Milstar satellite operator, instructor, and<br />
staff positions in the 50th <strong>Space</strong> Wing. Captain<br />
Todd is a graduate of Squadron Officer<br />
School, Academic Instructor School, and the<br />
Air Force Weapons School.<br />
no less painful to the US than an attack<br />
on military space systems.<br />
Another passive defense technique is<br />
the creation of a robust network employing<br />
tactics such as frequency hopping<br />
or spread spectrum signals comprised<br />
of multiple redundant systems with the<br />
ability to reroute information in the face<br />
of attack. Physical dispersion of redundant<br />
ground stations will prevent a single<br />
point of failure. Using mobile ground<br />
stations further complicates targeting by<br />
an adversary. Dispersal also applies to<br />
satellites in space. Deploying them in<br />
various orbital planes and altitudes may<br />
also be an option.<br />
Passive techniques, however, are no<br />
longer applicable when effective attacks<br />
occur. It is important to detect and confirm<br />
an attack has taken place, and then characterize the nature<br />
and impact of the aggression. The location of the attacker is<br />
important for suppression or neutralization. Once detection<br />
and characterization occurs, it may be possible to employ an<br />
active technique, which may involve a change in the satellite’s<br />
configuration or location.<br />
Maneuvering a space system is an example of an active<br />
technique. This may allow the system to avoid electronic<br />
jamming, or kinetic or directed-energy attacks against the satellite.<br />
The downside of maneuvering is the use of a limited<br />
supply fuel and possible interruption of the satellite’s mission<br />
during the maneuver. If these limitations eliminate the maneuver<br />
option, then changing the system configuration may be<br />
a course of action. If a satellite is designed with redundant or<br />
alternate systems not affected by the attacker, controllers may<br />
be able to switch to these systems and continue the mission.<br />
Regardless of the type of DCS technique used, sustaining<br />
our ability to operate freely in space is<br />
paramount to effective operations on<br />
earth. This applies not only to combat<br />
forces on the front lines, but also to the<br />
civilian populace and commercial endeavors.<br />
There are many examples of<br />
America’s critical dependence on space<br />
capabilities. An attack on our space systems<br />
affects our ability to project military<br />
power and impacts our diplomatic,<br />
information, and economic sources of<br />
influence. The United States cannot allow<br />
its space resources to go unprotected.<br />
US Northern Command was created<br />
to guarantee homeland security, a mission<br />
that must include a full spectrum<br />
defense. By advocating sound DCS<br />
techniques for the protection of critical<br />
homeland space infrastructure, US<br />
Northern Command can prepare the Nation<br />
to defend itself against attack from<br />
our “space approaches.”<br />
Notes:<br />
1<br />
“Remarks by Admiral Keating during the<br />
Change of Command,” US Northern Command, online,<br />
Internet, available from http://www.northcom.<br />
mil/index.cfm?fuseaction=news.showstory&storyid<br />
=3CA87963-E5FD-8DE5-4299F61610AEF985.<br />
2<br />
“Who We Are: Homefront,” US Northern<br />
Command, on-line, Internet, available from http://<br />
www.northcom.mil/index.cfm?fuseaction=s.who_<br />
homefront.<br />
3<br />
Military <strong>Space</strong> Forces Fact File, US Strategic<br />
Command, on-line, Internet, 31 January 2005, available<br />
from http://www.stratcom.mil/factsheetshtml/<br />
militaryspaceforces.htm.<br />
4<br />
Net Monthly Satellite Subscriber Additions,<br />
Satbiznews, 1999, on-line, Internet, 31 January<br />
2005, available from http://www.satbiznews.com/<br />
monthly.html.<br />
5<br />
AFDD 2-2.1, Counterspace Operations (2 August<br />
2004).<br />
30 High Frontier Winter 2005