The Dangerous World of Counterfeit and Pirated Software - Microsoft
The Dangerous World of Counterfeit and Pirated Software - Microsoft
The Dangerous World of Counterfeit and Pirated Software - Microsoft
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
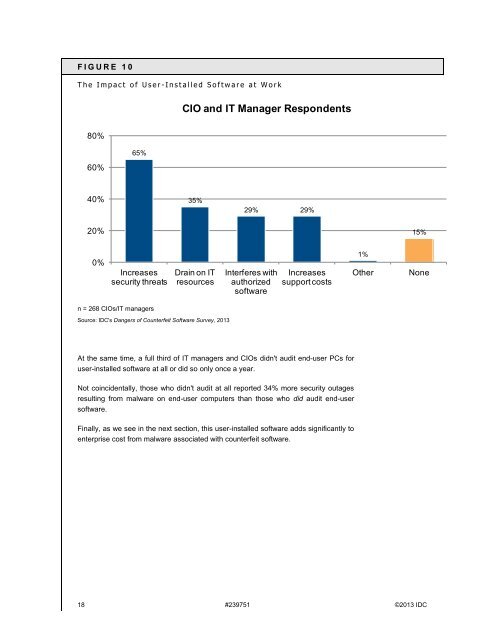
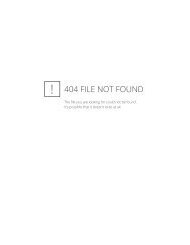
F I G U R E 1 0<br />
T h e I m p a c t o f U s e r - I n s t a l l e d S o f t w a r e a t W o r k<br />
CIO <strong>and</strong> IT Manager Respondents<br />
80%<br />
60%<br />
65%<br />
40%<br />
35%<br />
29% 29%<br />
20%<br />
15%<br />
0%<br />
Increases<br />
security threats<br />
Drain on IT<br />
resources<br />
Interferes with<br />
authorized<br />
s<strong>of</strong>tware<br />
Increases<br />
support costs<br />
1%<br />
Other<br />
None<br />
n = 268 CIOs/IT managers<br />
Source: IDC's Dangers <strong>of</strong> <strong>Counterfeit</strong> S<strong>of</strong>tware Survey, 2013<br />
At the same time, a full third <strong>of</strong> IT managers <strong>and</strong> CIOs didn't audit end-user PCs for<br />
user-installed s<strong>of</strong>tware at all or did so only once a year.<br />
Not coincidentally, those who didn't audit at all reported 34% more security outages<br />
resulting from malware on end-user computers than those who did audit end-user<br />
s<strong>of</strong>tware.<br />
Finally, as we see in the next section, this user-installed s<strong>of</strong>tware adds significantly to<br />
enterprise cost from malware associated with counterfeit s<strong>of</strong>tware.<br />
18 #239751 ©2013 IDC