industrial wireless book special edition - Networking ...
industrial wireless book special edition - Networking ...
industrial wireless book special edition - Networking ...
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
<strong>industrial</strong> <strong>wireless</strong><br />
50<br />
Fig. 5. Personnel and tracking applications need a<br />
plantwide Wi-Fi coverage for tracking RFID tags, often<br />
accomplished by external aerial mounting of <strong>wireless</strong><br />
transmitters and receivers.<br />
Protecting networks – Each mesh AP’s digital<br />
certificate authenticates it to the <strong>wireless</strong><br />
controller and allows it to participate in the<br />
secure network, so rogue or perhaps unauthorised<br />
APs cannot mimic genuine APs.<br />
All lawful <strong>wireless</strong> network communications<br />
are encrypted to prevent eavesdropping or<br />
packet manipulation. Rogue APs cannot insert<br />
themselves in the middle of the <strong>wireless</strong> infrastructure<br />
or otherwise compromise the network.<br />
Ideally, <strong>wireless</strong> user access should be deployed<br />
with a <strong>wireless</strong> intrusion prevention system.<br />
Also, scan for rogue clients/APs.<br />
Control access – Every user/device must<br />
authenticate with a centralised network domain<br />
authority. One way is to use an Authentication,<br />
Authorisation, and Accounting (AAA) server<br />
with the RADIUS authentication protocol coordinating<br />
access to the <strong>wireless</strong> network<br />
resources with the existing IT security infrastructure.<br />
Ensure client integrity – Antivirus software<br />
must be installed to prevent any primary<br />
infection of the device. Good security practices<br />
should be in force. Ideally, control devices<br />
(wired or <strong>wireless</strong>) should have no email or<br />
Internet access.<br />
PHOTO: EMERSON PROCESS<br />
WirelessHART field network inherent security<br />
features include:<br />
● AES-128 encryption (NIST/IEEE compliant)<br />
for all communications within the device mesh<br />
network and the gateway;<br />
● Individual device session keys to ensure endto-end<br />
message authenticity, data integrity,<br />
receipt validation, and secrecy through data<br />
encryption;<br />
● Hop-by-hop CRC and MIC calculations to<br />
ensure message authentication and verification<br />
as to communications source/receiver;<br />
● Devices must have a pre-configured ‘join key’;<br />
● White listing (ACL). If individual join keys<br />
are used, devices are explicitly given permission<br />
to join the network through the gateway or<br />
network manager via an ACL entry (also<br />
includes their globally unique HART address).<br />
Internal firewall<br />
The connectivity from the w-HART gateway to<br />
the host system is secured by an easily<br />
configured internal firewall that allows only the<br />
protocols and ports required for the field<br />
solution to be enabled for communication.<br />
Ethernet-based protocols (Modbus, OPC, AMS,<br />
HART Port, https) all support SSL-protected<br />
communications, while the gateway’s internal<br />
bi-directional firewall should default to ‘reject<br />
all’. Note that the firewall needs no active<br />
management.<br />
The above security features provide an easy<br />
to manage yet very robust communications<br />
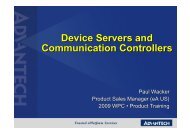
system. Figure 4 shows a table of field <strong>wireless</strong><br />
attacks against mitigating defences.<br />
Some <strong>wireless</strong> solutions use an 802.11-2007-<br />
based Wi-Fi Mesh technology. Note, however,<br />
that 802.11 can be a security risk because<br />
<strong>wireless</strong> signals can be received by any<br />
commercially available 802.11 compliant<br />
device. By authenticating users before allowing<br />
them to access the <strong>wireless</strong> network, most<br />
attackers can be deterred, but it is recommended<br />
that all <strong>wireless</strong> data transmitted<br />
Denial of service<br />
Spoofing<br />
Man-in-the-middle<br />
Replay<br />
HELLO floods<br />
Sinkholes<br />
Eavesdropping<br />
Anti-jamming<br />
Authentication<br />
Verification<br />
Encryption<br />
Key management<br />
Mitigating defences<br />
Attacks<br />
Fig. 4: Plant <strong>wireless</strong> attacks against mitigating<br />
defences. WirelessHART field network inherent security<br />
features include AES-128 encryption, individual device<br />
session keys, hop-by-hop CRC and MIC calculations, a<br />
pre-configured ‘join key’ for devices, and white listing<br />
(ACL).<br />
<strong>industrial</strong> ethernet <strong>book</strong><br />
within the Wi-Fi mesh network, and between<br />
it and all client devices, should be encrypted.<br />
Device diagnostics<br />
The diagnostics information available from a<br />
<strong>wireless</strong> sensor or instrument is similar to that<br />
from a hard-wired fieldbus device or a conventional<br />
HART-based instrument. It is known that<br />
many users installed HART-based instruments<br />
mainly because of the extensive diagnostic<br />
information available, but estimates are that<br />
only 10% of installations actually use this<br />
information to the full extent. Many companies<br />
instead limit their use to handheld devices<br />
employed to manually calibrate and check field<br />
instruments during commissioning and calibration.<br />
Part of the problem with wired HART devices<br />
is they have to communicate over a relatively<br />
slow 4-20mA connection, and <strong>special</strong> software<br />
is involved. However, with w-HART, the full<br />
range of HART diagnostics is available via the<br />
high speed <strong>wireless</strong> connection, and asset<br />
management software can extract the HART<br />
information. Yet w-HART is still familiar to<br />
users, who don’t need to buy new tools or<br />
undertake more training programs.<br />
Older, wired instruments can be added using<br />
a w-HART adapter, opening up a new area for<br />
maintenance and diagnostics. For example,<br />
many <strong>industrial</strong> and process plants have valves<br />
that have to be pulled from the line for an<br />
overhaul on a regular basis.<br />
By adding a <strong>wireless</strong> adapter to a HART-based<br />
valve actuator, users can gain access to all the<br />
details needed to make an informed and<br />
proactive maintenance decision, instead of<br />
running to failure or performing unneeded<br />
maintenance. The same applies to flowmeters<br />
and related instruments.<br />
On the horizon<br />
The HCF continues to develop new technologies<br />
for HART and w-HART. Coming in the near<br />
future is standardisation on HART IP, an abbreviation<br />
for Highway Addressable Remote<br />
Transducer over IP.<br />
HART IP can use both TCP and UDP as the<br />
transport protocol. Typically, most <strong>wireless</strong><br />
gateways are connected to automation and<br />
information systems using Modbus, but the<br />
available bandwidth is low. HCF envisages HART<br />
IP over an Ethernet physical layer, as a better<br />
way of getting data into automation and information<br />
systems.<br />
Being able to obtain information on the<br />
performance and operational state of the mesh<br />
network is also desirable. HCF is responding to<br />
feedback from NAMUR testing to see if this is<br />
possible.<br />
David Walker is Sales Director for Wireless Solutions,<br />
Middle East & Africa at Emerson Process Management.<br />
First published in the <strong>industrial</strong> ethernet <strong>book</strong> May 2012<br />
sponsored by Advantech