Evaluation of Department of State Information Security Program ...
Evaluation of Department of State Information Security Program ...
Evaluation of Department of State Information Security Program ...
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
UNCLASSIFIED<br />
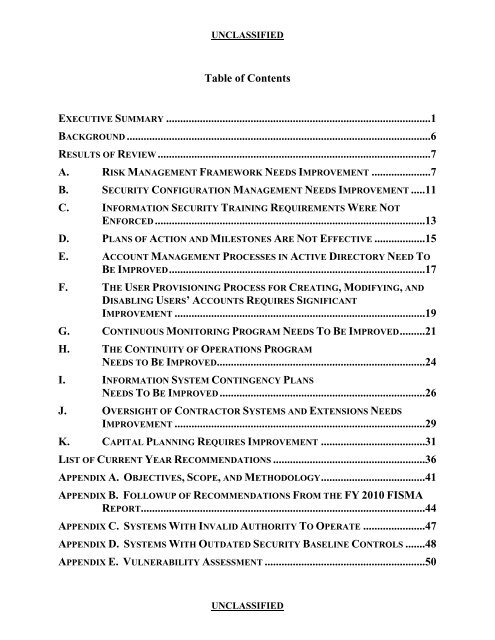
Table <strong>of</strong> Contents<br />
EXECUTIVE SUMMARY ..............................................................................................1<br />
BACKGROUND ............................................................................................................6<br />
RESULTS OF REVIEW .................................................................................................7<br />
A. RISK MANAGEMENT FRAMEWORK NEEDS IMPROVEMENT .....................7<br />
B. SECURITY CONFIGURATION MANAGEMENT NEEDS IMPROVEMENT .....11<br />
C. INFORMATION SECURITY TRAINING REQUIREMENTS WERE NOT<br />
ENFORCED ................................................................................................13<br />
D. PLANS OF ACTION AND MILESTONES ARE NOT EFFECTIVE ..................15<br />
E. ACCOUNT MANAGEMENT PROCESSES IN ACTIVE DIRECTORY NEED TO<br />
BE IMPROVED...........................................................................................17<br />
F. THE USER PROVISIONING PROCESS FOR CREATING, MODIFYING, AND<br />
DISABLING USERS’ ACCOUNTS REQUIRES SIGNIFICANT<br />
IMPROVEMENT .........................................................................................19<br />
G. CONTINUOUS MONITORING PROGRAM NEEDS TO BE IMPROVED.........21<br />
H. THE CONTINUITY OF OPERATIONS PROGRAM<br />
NEEDS TO BE IMPROVED..........................................................................24<br />
I. INFORMATION SYSTEM CONTINGENCY PLANS<br />
NEEDS TO BE IMPROVED .........................................................................26<br />
J. OVERSIGHT OF CONTRACTOR SYSTEMS AND EXTENSIONS NEEDS<br />
IMPROVEMENT .........................................................................................29<br />
K. CAPITAL PLANNING REQUIRES IMPROVEMENT .....................................31<br />
LIST OF CURRENT YEAR RECOMMENDATIONS ......................................................36<br />
APPENDIX A. OBJECTIVES, SCOPE, AND METHODOLOGY.....................................41<br />
APPENDIX B. FOLLOWUP OF RECOMMENDATIONS FROM THE FY 2010 FISMA<br />
REPORT.....................................................................................................44<br />
APPENDIX C. SYSTEMS WITH INVALID AUTHORITY TO OPERATE ......................47<br />
APPENDIX D. SYSTEMS WITH OUTDATED SECURITY BASELINE CONTROLS .......48<br />
APPENDIX E. VULNERABILITY ASSESSMENT .........................................................50<br />
UNCLASSIFIED