LANDesk Management Suite 9 Best Practices for Agent - Community
LANDesk Management Suite 9 Best Practices for Agent - Community
LANDesk Management Suite 9 Best Practices for Agent - Community
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
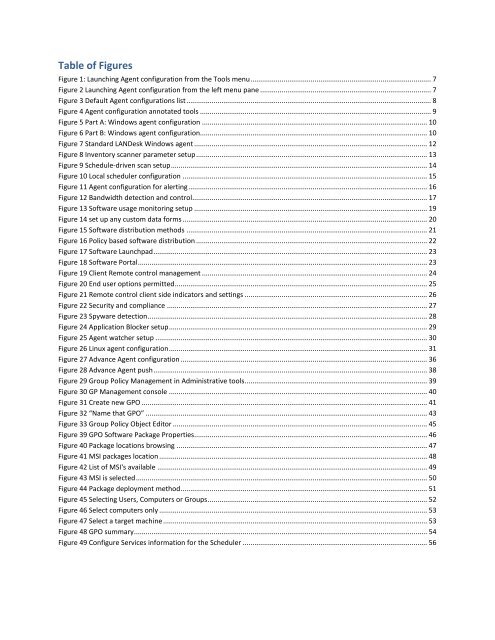
Table of Figures<br />
Figure 1: Launching <strong>Agent</strong> configuration from the Tools menu ............................................................................................. 7<br />
Figure 2 Launching <strong>Agent</strong> configuration from the left menu pane ........................................................................................ 7<br />
Figure 3 Default <strong>Agent</strong> configurations list .............................................................................................................................. 8<br />
Figure 4 <strong>Agent</strong> configuration annotated tools ....................................................................................................................... 9<br />
Figure 5 Part A: Windows agent configuration .................................................................................................................... 10<br />
Figure 6 Part B: Windows agent configuration..................................................................................................................... 10<br />
Figure 7 Standard <strong>LANDesk</strong> Windows agent ........................................................................................................................ 12<br />
Figure 8 Inventory scanner parameter setup ....................................................................................................................... 13<br />
Figure 9 Schedule-driven scan setup .................................................................................................................................... 14<br />
Figure 10 Local scheduler configuration .............................................................................................................................. 15<br />
Figure 11 <strong>Agent</strong> configuration <strong>for</strong> alerting ........................................................................................................................... 16<br />
Figure 12 Bandwidth detection and control ......................................................................................................................... 17<br />
Figure 13 Software usage monitoring setup ........................................................................................................................ 19<br />
Figure 14 set up any custom data <strong>for</strong>ms .............................................................................................................................. 20<br />
Figure 15 Software distribution methods ............................................................................................................................ 21<br />
Figure 16 Policy based software distribution ....................................................................................................................... 22<br />
Figure 17 Software Launchpad ............................................................................................................................................. 23<br />
Figure 18 Software Portal ..................................................................................................................................................... 23<br />
Figure 19 Client Remote control management .................................................................................................................... 24<br />
Figure 20 End user options permitted .................................................................................................................................. 25<br />
Figure 21 Remote control client side indicators and settings .............................................................................................. 26<br />
Figure 22 Security and compliance ...................................................................................................................................... 27<br />
Figure 23 Spyware detection ................................................................................................................................................ 28<br />
Figure 24 Application Blocker setup ..................................................................................................................................... 29<br />
Figure 25 <strong>Agent</strong> watcher setup ............................................................................................................................................ 30<br />
Figure 26 Linux agent configuration ..................................................................................................................................... 31<br />
Figure 27 Advance <strong>Agent</strong> configuration ............................................................................................................................... 36<br />
Figure 28 Advance <strong>Agent</strong> push ............................................................................................................................................. 38<br />
Figure 29 Group Policy <strong>Management</strong> in Administrative tools.............................................................................................. 39<br />
Figure 30 GP <strong>Management</strong> console ..................................................................................................................................... 40<br />
Figure 31 Create new GPO ................................................................................................................................................... 41<br />
Figure 32 “Name that GPO” ................................................................................................................................................. 43<br />
Figure 33 Group Policy Object Editor ................................................................................................................................... 45<br />
Figure 39 GPO Software Package Properties........................................................................................................................ 46<br />
Figure 40 Package locations browsing ................................................................................................................................. 47<br />
Figure 41 MSI packages location .......................................................................................................................................... 48<br />
Figure 42 List of MSI's available ........................................................................................................................................... 49<br />
Figure 43 MSI is selected ...................................................................................................................................................... 50<br />
Figure 44 Package deployment method ............................................................................................................................... 51<br />
Figure 45 Selecting Users, Computers or Groups ................................................................................................................. 52<br />
Figure 46 Select computers only .......................................................................................................................................... 53<br />
Figure 47 Select a target machine ........................................................................................................................................ 53<br />
Figure 48 GPO summary ....................................................................................................................................................... 54<br />
Figure 49 Configure Services in<strong>for</strong>mation <strong>for</strong> the Scheduler ............................................................................................... 56