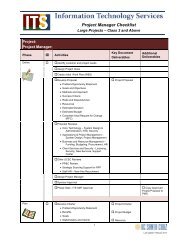
Technical requirements - Information Technology Services
Technical requirements - Information Technology Services
Technical requirements - Information Technology Services
- No tags were found...
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
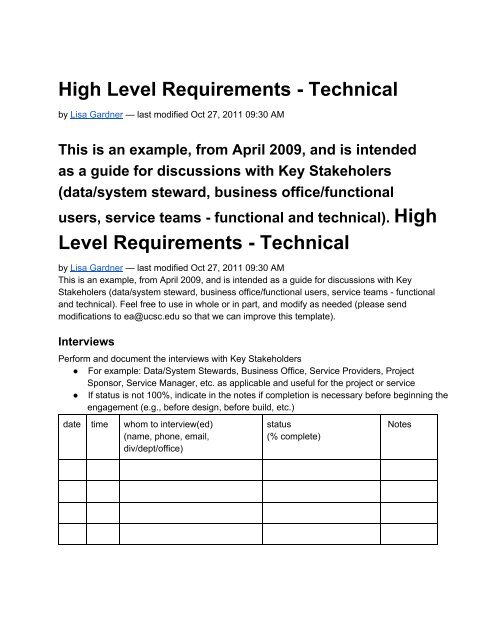
High Level Requirements <strong>Technical</strong><br />
by Lisa Gardner — last modified Oct 27, 2011 09:30 AM<br />
This is an example, from April 2009, and is intended<br />
as a guide for discussions with Key Stakeholers<br />
(data/system steward, business office/functional<br />
users, service teams functional and technical). High<br />
Level Requirements <strong>Technical</strong><br />
by Lisa Gardner — last modified Oct 27, 2011 09:30 AM<br />
This is an example, from April 2009, and is intended as a guide for discussions with Key<br />
Stakeholers (data/system steward, business office/functional users, service teams functional<br />
and technical). Feel free to use in whole or in part, and modify as needed (please send<br />
modifications to ea@ucsc.edu so that we can improve this template).<br />
Interviews<br />
Perform and document the interviews with Key Stakeholders<br />
● For example: Data/System Stewards, Business Office, Service Providers, Project<br />
Sponsor, Service Manager, etc. as applicable and useful for the project or service<br />
● If status is not 100%, indicate in the notes if completion is necessary before beginning the<br />
engagement (e.g., before design, before build, etc.)<br />
date time whom to interview(ed)<br />
(name, phone, email,<br />
div/dept/office)<br />
status<br />
(% complete)<br />
Notes
List of Questions/Common ITS Practices<br />
During interviews, validate the following technical <strong>requirements</strong>:<br />
● Describe the requirement (add to, remove from, or modify the list below, where<br />
appropriate)<br />
● Provide an example use case(s) (full use cases should be documented separately, and<br />
are used for testing unit, functional, technical, load, and user acceptance)<br />
● Identify who requested the requirement, and what they consider is the risk of doing/not<br />
doing<br />
● Confirm the Ranking (cost/benefit), where<br />
○ 1 = Must Have; a “show stopperâ€requirement, without which the solution is<br />
of little use or benefit<br />
○ 2 = Preferred; if demonstrable efficiency, cost savings, or income producing; may<br />
be deferred or canceled if unacceptable scope risk (cannot accommodate cost,<br />
time, resources, quality)<br />
○ 3 = Optional; Intangible or small benefits only; shall be deferred or canceled if cost<br />
>= benefit<br />
● Confirm the Priority, where<br />
○ Order of completion is necessary to distinguish multiple requests/deliverables<br />
competing for same resources, budget, and/or schedule<br />
# requirement<br />
use case(s)<br />
other notes of interest<br />
0 Confirm Data/System Steward<br />
Contact Info<br />
● name, email, phone,<br />
div/dept/office<br />
● add contact info for any<br />
person with delegated<br />
authority<br />
1 Data Types & Classification<br />
requester<br />
risk of<br />
doing<br />
risk of<br />
not<br />
doing<br />
ranking<br />
priority<br />
1a<br />
Includes restricted or confidential<br />
data (see IS2 andIS3)<br />
● Use Case (example):<br />
1099 information<br />
containing SSN (PII,<br />
restricted)<br />
● Use Case (example):<br />
Worker's comp report
●<br />
●<br />
●<br />
(HIPAA, restricted)<br />
Use Case (example):<br />
Student home address<br />
(FERPA, restricted)<br />
Use Case (example):<br />
Payment information<br />
(PCI, restricted)<br />
Use Case (example):<br />
Contract information<br />
containing vendor<br />
proprietary data<br />
(confidential)<br />
1b<br />
1c<br />
Includes standard file types (text,<br />
doc, xls, etc.) and/or<br />
nonstandard file types<br />
● Use Case (example):<br />
Excel files sent to/from<br />
UCOP for corporate<br />
reporting<br />
● Use Case (example):<br />
XML and XSD files sent<br />
from vendor to UCSC ITS<br />
Service Provider<br />
Includes multimedia<br />
● Use Case (example):<br />
JPG, TIFF, MOV, WMP<br />
2 Request & Account<br />
Management<br />
2a<br />
Account request processing is<br />
handled by whom (e.g.,<br />
processing account<br />
activation/revocation)<br />
● Use Case (example):<br />
Anyone can submit a<br />
request through IT<br />
Request.<br />
● Use Case (example):<br />
Only Data Steward will<br />
submit a request through
●<br />
IT Request.<br />
Use Case (example):<br />
Account management is<br />
handled within the<br />
business office.<br />
2b<br />
Who approves account requests<br />
Data Steward, Bus Ofc, other<br />
● Use Case (example):<br />
Data steward approves<br />
user to have access to<br />
limited dataset vs full<br />
dataset.<br />
● Use Case (example):<br />
Bus Ofc approves user to<br />
business office data.<br />
2c Who approves permissions <br />
rwxd vs crud Are permissions<br />
persistent or adhoc Are<br />
permissions between users<br />
and/or systems<br />
● Use Case (example):<br />
Data steward approves<br />
user to have read access<br />
to limited dataset vs full<br />
dataset.<br />
● Use Case (example):<br />
Bus Ofc approves<br />
external system to have<br />
execute permissions for<br />
script that process<br />
business office data and<br />
transmits to UCOP.<br />
2d<br />
Who sets and/or can modify<br />
permissions of the directory<br />
structure(s) and/or data file(s)<br />
Are permissions persistent or<br />
adhoc<br />
● Use Case (example):<br />
Process Owner sets<br />
permissions to bus ofc
●<br />
data and directory<br />
structures.<br />
Use Case (example): Bus<br />
Ofc POC can set<br />
onetime permissions to<br />
bus ofc data and directory<br />
structures when<br />
permission process fails<br />
or an exception request is<br />
necessary.<br />
2e<br />
What do we capture in the audit<br />
logs (system, app, database,<br />
etc.) And, who has access to<br />
review and/or interrogate the<br />
audit logs, at what frequency<br />
● Use Case (example):<br />
Audit logs capture new<br />
account, account change,<br />
account revocation,<br />
successful login<br />
attempts, failed login<br />
attempts, login attempts<br />
source/destination, etc.<br />
● Use Case (example):<br />
Service Provider<br />
interrogates audit logs<br />
and submits report to<br />
data stewards, on a<br />
quarterly basis<br />
3 User Communities<br />
3a<br />
Within UCSC and/or UC, who<br />
can use the system and what<br />
roles do they have<br />
● Use Case (example):<br />
Students have "student"<br />
role (crud and rwxd only<br />
their own records).<br />
● Use Case (example): Bus<br />
Ofc POC has "officer"<br />
role (crud and rwxd to
●<br />
their bus ofc group of<br />
records).<br />
Use Case (example): Bus<br />
Ofc admin has "admin"<br />
role (configures business<br />
rules, and can<br />
RWXD/CRUD on dev/test<br />
and training; no RWXD<br />
and no CRUD to stage/qa<br />
or production).<br />
3b<br />
Who are the external<br />
(nonUCSC/UC) users of the<br />
system and what roles do they<br />
have<br />
●<br />
●<br />
●<br />
Use Case (example):<br />
Contractor accts with<br />
RWXD/CRUD to<br />
nonproduction systems,<br />
duration of<br />
implementation only.<br />
Use Case (example):<br />
Vendor accts with Read<br />
access to production<br />
system for interface<br />
processing.<br />
Use Case (example):<br />
Limited acct Read<br />
access to stage/qa that<br />
autoexpires after<br />
nnhours.<br />
3b<br />
1 REPEAT THIS AS 3a1 to<br />
IDENTIFY IF USING GOLD vs.<br />
BLUE vs LOCAL<br />
Group password for<br />
systemtosystem processing<br />
UCSC, UC, or external<br />
source/destination
●<br />
Use case (example):<br />
Group pwd for ODBC<br />
connect between UCSC<br />
source and UCOP<br />
destination.<br />
3c<br />
What tools or technologies will<br />
clients need to access the<br />
system<br />
Example: Use of secure<br />
protocols such as VPN, SSH,<br />
SCP, SFTP<br />
Exaple: Use of secure application<br />
methods (such as encryption)<br />
that don't expose data or user<br />
information (account/pwd)<br />
MOVE REMAINING to Security<br />
SECTION<br />
Will secure client be required for<br />
access, authentication, data xfer,<br />
etc<br />
● Use case (example):<br />
SSH, VPN<br />
● Use case (example):<br />
Shibboleth<br />
● Use case (example):<br />
SCP/SFTP<br />
3d<br />
COMBINE WITH 3a (and delete<br />
3d)<br />
Accessible by other UC system<br />
(sister campus and/or UCOP),<br />
and what permissions<br />
● Use Case (example):<br />
allow RSYNC between
●<br />
UCSC and UCOP<br />
systems, utilizing VPN<br />
connection, for file copy<br />
to/from.<br />
Use Case (example):<br />
allow manual data xfer via<br />
SCP/SFTP between<br />
UCSC and Vendor<br />
system, to be launched<br />
by vendor system.<br />
3e<br />
COMBINE WITH 3a (and delete<br />
3e)<br />
Limit usage to<br />
business/administrative<br />
● Use Case (example):<br />
Administrative Bus Ofc<br />
only.<br />
3f<br />
Anonymous file drop/retrieve<br />
● Use Case (example):<br />
Allow Bus Ofc POC at<br />
UCOP to put files on<br />
system.<br />
4 Help & User Support<br />
4a<br />
NEEDS WORK<br />
Who provides user support for<br />
setup/removal of connection,<br />
bugs or problems, directory<br />
structure/file standards, and<br />
permission problems AND<br />
HOW<br />
Incident vs. Service Request vs.<br />
<strong>Information</strong> Request<br />
Service Now functionality may<br />
address this
How do you support external<br />
users<br />
●<br />
●<br />
●<br />
Use Case (example):<br />
User submits request for<br />
help via IT Request; ticket<br />
is assigned to ITS<br />
Service Provider.<br />
Use Case (example):<br />
User submits request for<br />
help via IT Request; ticket<br />
is assigned to Bus Ofc.<br />
Use Case (example):<br />
User contacts Bus Ofc to<br />
request help, and Bus<br />
Ofc responds (ITS is not<br />
part of support process).<br />
4c<br />
Who provides user<br />
documentation, faqs, and<br />
training<br />
● Use Case (example):<br />
data steward will create<br />
user guides and faqs, and<br />
make available to users,<br />
training is not provided.<br />
● Use Case (example): ITS<br />
will create technician<br />
guides and faqs, and<br />
provide for technician<br />
training.<br />
5 Directory and/or Data<br />
Structures and File Naming<br />
standards as they affect the<br />
UX or UI<br />
5a<br />
What is the directory/data<br />
structure needed to inform<br />
design solution, and based on<br />
customer <strong>requirements</strong>
5b<br />
What is the file naming<br />
convention needed to inform<br />
design solution, and based on<br />
customer <strong>requirements</strong><br />
6 <strong>Technical</strong>/Operational<br />
6a<br />
6b<br />
Service Availability (pick one)<br />
● Tier 3 24x7x365,<br />
excluding maintenance<br />
window, incident<br />
response, and cold<br />
backups, see also 7b<br />
● Tier 2 MF 77,<br />
excluding campus<br />
holidays or closures,<br />
maintenance window,<br />
incident response, cold<br />
backups, see also 7b<br />
● Tier 1 MF 85,<br />
excluding campus<br />
holidays or closures,<br />
maintenance window,<br />
incident response, cold<br />
backups, see also 7b<br />
Maintenance Window (which<br />
may be defined to occur outside<br />
of business/service hours):<br />
1. Frequency (pick one or<br />
more): Daily, Weekly,<br />
Monthly, Qrtly, Yearly<br />
2. Day of Week (pick one or<br />
more, must be within<br />
Service Availability Tier):<br />
MTuWThFSaSu<br />
3. Time of Day: based on<br />
Tier 1 or 2 Service<br />
Availability; if Tier 3 pick<br />
time range (must start<br />
after, and finish before)<br />
4. Exception: Security<br />
patches will be applied
outside the regular<br />
maintenance window,<br />
depending on<br />
risk/vulnerability, and/or<br />
as directed by ITS<br />
Security or campus<br />
<strong>Information</strong> Security<br />
Officer (ISO)<br />
6c<br />
6d<br />
Incident/Response:<br />
1. Response within eight<br />
business hours of receipt<br />
based on Service<br />
Availability Tier (see #6a,<br />
above), or Service Level<br />
Agreement (see #7,<br />
below)<br />
2. Repairs may be effected<br />
during business hours<br />
and pending outage<br />
tolerance of steward<br />
○ Mean Time To<br />
Repair (MTTR) is<br />
dependent on<br />
completion of root<br />
cause analysis,<br />
identification and<br />
execution of<br />
mitigation options,<br />
may be limited by<br />
vendor<br />
maintenance<br />
agreement<br />
3. Repairs may be<br />
shortterm (e.g., bring<br />
system/service online,<br />
but additional repair work<br />
is required, and will be<br />
scheduled as needed)<br />
SHAWN TO WORDSMITH<br />
Privileged Access (Application,
Database, and System<br />
Administrators)<br />
1. Will adhere to service<br />
provider guidelines<br />
2. Will use secure access<br />
methods (SSH, VPN, or<br />
other approved method)<br />
3. Will include account and<br />
access information within<br />
quarterly report to data<br />
stewards (see 2e, above)<br />
6e<br />
LISA TO WORDSMITH<br />
remaining of 6 with Eric Keisler<br />
Where Hosted Who supports<br />
the hosting What hosting<br />
functions are included<br />
Use Case: If System will be<br />
housed in the ITS Data Center or<br />
another ITSsupported facility,<br />
consider the following <br />
○ ITS Administrators<br />
will manage the<br />
systems<br />
(application,<br />
database,<br />
hardware and<br />
operating system)<br />
○ Includes<br />
monitoring of<br />
system health,<br />
and alert when<br />
performance<br />
targets degrade<br />
■ Confirm if<br />
nonITS<br />
service<br />
provider<br />
will receive<br />
alerts
●<br />
○ Hardware refresh<br />
occurs on a<br />
fiveyear lifecycle,<br />
or as otherwise<br />
identified by the<br />
vendor (typically<br />
endoflife<br />
notifications)<br />
○ Software<br />
lifecycles are<br />
performed per<br />
vendor distribution<br />
and/or endoflife<br />
notifications<br />
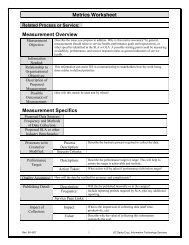
Log Management<br />
○ Logs (system,<br />
app, database,<br />
etc.) may capture<br />
the following data<br />
(including but not<br />
limited to): new<br />
account, account<br />
change, account<br />
revocation,<br />
successful login<br />
attempts, failed<br />
login attempts,<br />
login attempt<br />
source/destination<br />
; activity (get/put,<br />
copy, move,<br />
remove, execute);<br />
duration of activity;<br />
web page<br />
source/destination<br />
○ Administrators<br />
periodically review<br />
and/or interrogate<br />
the audit logs,<br />
including post<br />
incident to support<br />
root cause and/or
●<br />
●<br />
statistical analysis<br />
○ Logs may be<br />
made available to<br />
ITS Security for<br />
breach<br />
investigation<br />
and/or forensics<br />
○ Results of log<br />
reviews may be<br />
made available to<br />
Data/System<br />
Steward and/or<br />
other authorities,<br />
upon request and<br />
per policy<br />
System will adhere to UC<br />
BFB IS series (IS3 and<br />
IS12)<br />
Criteria for Design<br />
Review, before<br />
production build occurs<br />
○ Class 3 or above<br />
○ Spans multiple<br />
units, or single<br />
unit budgetary<br />
discretion<br />
○ High or unknown<br />
risk<br />
○ High political value<br />
○ New or unfamiliar<br />
technology<br />
○ Upon request<br />
6f<br />
Fault Tolerance and Disaster<br />
Recovery (see IS12)<br />
● Consider redundancy of<br />
system components<br />
(reduction of<br />
singlepointsof failure)<br />
where feasible<br />
● Minimum number of<br />
environments = two
●<br />
(dev/test and prod)<br />
○ If "necessary" or<br />
"essential" then<br />
minimum number<br />
of environments =<br />
3 (dev/test,<br />
stage/qa, prod)<br />
(where stage/qa<br />
can accurately<br />
predict production<br />
behavior)<br />
If "essential"<br />
○ Stage/qa<br />
environment must<br />
be equal to prod<br />
(e.g., use as an<br />
alternative host in<br />
the event that<br />
production host<br />
fails and is<br />
irreparable)<br />
■ Consider<br />
automated<br />
failover vs.<br />
manual<br />
failover,<br />
depending<br />
on<br />
feasibility<br />
○ Consider a<br />
remote location<br />
for data and/or<br />
system replication<br />
(may place<br />
stage/qa in<br />
remote location)<br />
○ Establish and<br />
perform periodic<br />
disaster recovery<br />
exercises<br />
6g<br />
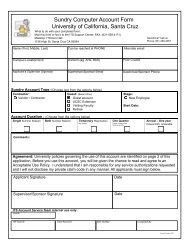
Authentication
●<br />
●<br />
For UCSC access<br />
(students, faculty, staff),<br />
pending technical<br />
feasibility<br />
○ Utilize Identity<br />
Management<br />
(IDM) Shibboleth<br />
or LDAPBind, or<br />
○ Utilize local<br />
authentication<br />
For nonUCSC access<br />
○ Establish "sundry"<br />
accounts within<br />
IDM, or<br />
○ Utilize local<br />
account<br />
management<br />
6h<br />
Storage Management<br />
● Locallyattached vs. SAN<br />
vs NAS<br />
● Compression, duplication<br />
(RAID)<br />
● Capacity (GB vs TB)<br />
● Quotas and/or usage<br />
○ single reminder<br />
when at 75%<br />
○ weekly reminder<br />
when >= 80%<br />
○ daily reminder<br />
when >= 90%<br />
● Data "pruning" performed<br />
periodically<br />
○ specify timespan<br />
since last update,<br />
when data is<br />
considered aged<br />
○ specify if aged<br />
data can be<br />
pruned<br />
automatically<br />
○ reminder and/or
notification of<br />
pruning<br />
Data Security<br />
● Must be secure deleted<br />
● Storage device must be<br />
secure destroyed when<br />
retired, recycled, or<br />
6i<br />
Backups<br />
1. Specify includes and<br />
excludes (e.g., directory<br />
structure & permissions,<br />
user/data files,<br />
application, database,<br />
operating system, etc.)<br />
2. Specify frequency for<br />
incremental and full<br />
(typically nightly<br />
incremental, weekly full)<br />
3. Specify backup media<br />
(typically to disc then tape<br />
within same 24hour<br />
period)<br />
4. Specify backup retention<br />
period other than default<br />
(see<br />
http://its.ucsc.edu/policies<br />
/backup.html for default<br />
term)<br />
○<br />
Consider<br />
restoration<br />
feasibility if<br />
retention period is<br />
longer than 3<br />
years (e.g., you<br />
will need to<br />
assure restoration<br />
capabilities for the<br />
life of the retention<br />
period, for each<br />
backup that is<br />
maintained)
7 Service<br />
○ Consider default<br />
retention period<br />
may be sufficient<br />
for those systems<br />
that retain all<br />
historical data<br />
within the<br />
transactional<br />
system versus<br />
those that archive<br />
data outside of the<br />
transactional<br />
system<br />
5. Specify onsite and offsite<br />
stores (typically cycled<br />
weekly into onsite ITS<br />
vault, then 2nd week<br />
offsite to Iron Mountain,<br />
current as of Oct 2011<br />
and subject to change)<br />
6. Specify recycle of backup<br />
media (typically quarterly)<br />
○ Secure delete of<br />
backup media<br />
before reentry<br />
into backup cycle<br />
(regardless of IS3)<br />
7. Periodic restore test<br />
a. Perform once<br />
prior to production<br />
deployment,<br />
yearly thereafter<br />
(minimum)<br />
b. Perform tests for<br />
single file and full<br />
system restores<br />
7a<br />
Utilize ITS and Campus Service<br />
Level Agreement(SLA) or<br />
serviceunique SLA (template
available)<br />
7b<br />
7c<br />
7d<br />
Utilize common Operations Level<br />
Agreement (OLA) or<br />
serviceunique OLA (template<br />
available)<br />
ITS Practices<br />
● Request intake process<br />
and procedures<br />
● Project management<br />
methodology (andtoolkit)<br />
● SDLC for design, build,<br />
test, deploy (see<br />
alsoIS10)<br />
● Service Management<br />
Toolkit<br />
○ Incident and<br />
Change<br />
Management<br />
processes and<br />
procedures<br />
● Security Policies<br />
● Inventory tracking<br />
● Billing and Recharge<br />
Configuration and <strong>Technical</strong><br />
Documentation and Procedures<br />
● Developed, maintained,<br />
and resides with<br />
technician group<br />
Questions<br />
1. Besides business offices, who else needs access to the new system/service and/or<br />
data<br />
2. What is the existing legacy business process and/or system Can it be<br />
upgraded/enhanced or must it be replaced/retired in full or in part<br />
3. What is ITS current service commitment regarding the existing legacy business process<br />
and/or system<br />
4.
Assumptions<br />
1. Business office will perform fitgap (comparison of legacy business process vs. design<br />
solution); gaps will be accepted (implies business process reengineering), rejected<br />
(implies mitigation such as reengineering technical or business processes, and/or<br />
boltons, to address the gap), or transferred (defer mitigation as future enhancement<br />
after deployment of solution).<br />
2. Full cost a new system/service will be charged to the data/system steward, business<br />
office, and/or shared across the user community.<br />
3. If ITS SMT does not approve the new system/service, existing legacy business process<br />
and/or system will remain unchanged.<br />
4.<br />
Acronym Soup<br />
see also ITS Glossary of PolicyRelated Terms<br />
● BFB IS = Business and Finance Bulletins, <strong>Information</strong> Systems<br />
● CRUD = Create, Read, Update, Delete<br />
● CruzID = user ID managed by ITS Identity Management service<br />
● EOL = end of life<br />
● FERPA = Family Educational Rights and Privacy Act<br />
● MTTR = Mean Time to Response/Repair/Restore (duration)<br />
● OLA = Operations Level Agreement<br />
● PCI = Payment Card Industry<br />
● PII = Personal Identity <strong>Information</strong><br />
● RWXD = Read, Write, Execute, Delete<br />
● SDLC = Systems Development Life Cycle<br />
● SLA = Service Level Agreement<br />
● SMT = Senior Management Team (comprised of ITS VCIT and Directors)<br />
● SSH = Secure Shell<br />
● VPN = Virtual Private Network<br />
Feel free to use in whole or in part, and modify as needed (please send modifications to<br />
ea@ucsc.edu so that we can improve this template).<br />
Interviews<br />
Perform and document the interviews with Key Stakeholders<br />
● For example: Data/System Stewards, Business Office, Service Providers, Project<br />
Sponsor, Service Manager, etc. as applicable and useful for the project or service<br />
● If status is not 100%, indicate in the notes if completion is necessary before beginning the
engagement (e.g., before design, before build, etc.)<br />
date time whom to interview(ed)<br />
(name, phone, email,<br />
div/dept/office)<br />
status<br />
(% complete)<br />
Notes<br />
List of Questions/Common ITS Practices<br />
During interviews, validate the following technical <strong>requirements</strong>:<br />
● Describe the requirement (add to, remove from, or modify the list below, where<br />
appropriate)<br />
● Provide an example use case(s) (full use cases should be documented separately, and<br />
are used for testing unit, functional, technical, load, and user acceptance)<br />
● Identify who requested the requirement, and what they consider is the risk of doing/not<br />
doing<br />
● Confirm the Ranking (cost/benefit), where<br />
○ 1 = Must Have; a “show stopperâ€requirement, without which the solution is<br />
of little use or benefit<br />
○ 2 = Preferred; if demonstrable efficiency, cost savings, or income producing; may<br />
be deferred or canceled if unacceptable scope risk (cannot accommodate cost,<br />
time, resources, quality)<br />
○ 3 = Optional; Intangible or small benefits only; shall be deferred or canceled if cost<br />
>= benefit<br />
● Confirm the Priority, where<br />
○ Order of completion is necessary to distinguish multiple requests/deliverables<br />
competing for same resources, budget, and/or schedule<br />
# requirement<br />
use case(s)<br />
other notes of interest<br />
0 Confirm Data/System Steward<br />
Contact Info<br />
● name, email, phone,<br />
div/dept/office<br />
● add contact info for any<br />
requester<br />
risk of<br />
doing<br />
risk of not<br />
doing<br />
ranking<br />
priority
person with delegated<br />
authority<br />
1 Data Types & Classification<br />
1<br />
a<br />
1<br />
b<br />
1<br />
c<br />
Includes restricted or confidential<br />
data (see IS2 andIS3)<br />
● Use Case (example): 1099<br />
information containing SSN<br />
(PII, restricted)<br />
● Use Case (example):<br />
Worker's comp report (HIPAA,<br />
restricted)<br />
● Use Case (example): Student<br />
home address (FERPA,<br />
restricted)<br />
● Use Case (example):<br />
Payment information (PCI,<br />
restricted)<br />
● Use Case (example):<br />
Contract information<br />
containing vendor proprietary<br />
data (confidential)<br />
Includes standard file types (text, doc,<br />
xls, etc.) and/or nonstandard file<br />
types<br />
●<br />
●<br />
Use Case (example): Excel<br />
files sent to/from UCOP for<br />
corporate reporting<br />
Use Case (example): XML<br />
and XSD files sent from<br />
vendor to UCSC ITS Service<br />
Provider<br />
Includes multimedia<br />
● Use Case (example): JPG,<br />
TIFF, MOV, WMP<br />
2 Request & Account Management<br />
2<br />
a<br />
Account request processing is<br />
handled by whom (e.g., processing
account activation/revocation)<br />
● Use Case (example): Anyone<br />
can submit a request through<br />
IT Request.<br />
● Use Case (example): Only<br />
Data Steward will submit a<br />
request through IT Request.<br />
● Use Case (example): Account<br />
management is handled<br />
within the business office.<br />
2<br />
b<br />
2<br />
c<br />
2<br />
d<br />
Who approves account requests <br />
Data Steward, Bus Ofc, other<br />
● Use Case (example): Data<br />
steward approves user to<br />
have access to limited<br />
dataset vs full dataset.<br />
● Use Case (example): Bus<br />
Ofc approves user to<br />
business office data.<br />
Who approves permissions rwxd vs<br />
crud Are permissions persistent or<br />
adhoc Are permissions between<br />
users and/or systems<br />
● Use Case (example): Data<br />
steward approves user to<br />
have read access to limited<br />
dataset vs full dataset.<br />
● Use Case (example): Bus<br />
Ofc approves external system<br />
to have execute permissions<br />
for script that process<br />
business office data and<br />
transmits to UCOP.<br />
Who sets and/or can modify<br />
permissions of the directory<br />
structure(s) and/or data file(s) Are<br />
permissions persistent or adhoc<br />
● Use Case (example):<br />
Process Owner sets<br />
permissions to bus ofc data
●<br />
and directory structures.<br />
Use Case (example): Bus Ofc<br />
POC can set onetime<br />
permissions to bus ofc data<br />
and directory structures when<br />
permission process fails or an<br />
exception request is<br />
necessary.<br />
2<br />
e<br />
What do we capture in the audit logs<br />
(system, app, database, etc.) And,<br />
who has access to review and/or<br />
interrogate the audit logs, at what<br />
frequency<br />
● Use Case (example): Audit<br />
logs capture new account,<br />
account change, account<br />
revocation, successful login<br />
attempts, failed login<br />
attempts, login attempts<br />
source/destination, etc.<br />
● Use Case (example): Service<br />
Provider interrogates audit<br />
logs and submits report to<br />
data stewards, on a quarterly<br />
basis<br />
3 User Communities<br />
3<br />
a<br />
Within UCSC and/or UC, who can<br />
use the system and what roles do<br />
they have<br />
● Use Case (example):<br />
Students have "student" role<br />
(crud and rwxd only their own<br />
records).<br />
● Use Case (example): Bus Ofc<br />
POC has "officer" role (crud<br />
and rwxd to their bus ofc<br />
group of records).<br />
● Use Case (example): Bus Ofc<br />
admin has "admin" role<br />
(configures business rules,
and can RWXD/CRUD on<br />
dev/test and training; no<br />
RWXD and no CRUD to<br />
stage/qa or production).<br />
3<br />
b<br />
Who are the external<br />
(nonUCSC/UC) users of the system<br />
and what roles do they have<br />
●<br />
●<br />
●<br />
Use Case (example):<br />
Contractor accts with<br />
RWXD/CRUD to<br />
nonproduction systems,<br />
duration of implementation<br />
only.<br />
Use Case (example): Vendor<br />
accts with Read access to<br />
production system for<br />
interface processing.<br />
Use Case (example): Limited<br />
acct Read access to stage/qa<br />
that autoexpires after<br />
nnhours.<br />
3<br />
b<br />
1<br />
REPEAT THIS AS 3a1 to IDENTIFY<br />
IF USING GOLD vs. BLUE vs LOCAL<br />
Group password for<br />
systemtosystem processing<br />
UCSC, UC, or external<br />
source/destination<br />
● Use case (example): Group<br />
pwd for ODBC connect<br />
between UCSC source and<br />
UCOP destination.<br />
3<br />
c<br />
What tools or technologies will clients<br />
need to access the system<br />
Example: Use of secure protocols<br />
such as VPN, SSH, SCP, SFTP<br />
Exaple: Use of secure application
methods (such as encryption) that<br />
don't expose data or user information<br />
(account/pwd)<br />
MOVE REMAINING to Security<br />
SECTION<br />
Will secure client be required for<br />
access, authentication, data xfer,<br />
etc<br />
● Use case (example): SSH,<br />
VPN<br />
● Use case (example):<br />
Shibboleth<br />
● Use case (example):<br />
SCP/SFTP<br />
3<br />
d<br />
COMBINE WITH 3a (and delete 3d)<br />
Accessible by other UC system<br />
(sister campus and/or UCOP), and<br />
what permissions<br />
● Use Case (example): allow<br />
RSYNC between UCSC and<br />
UCOP systems, utilizing VPN<br />
connection, for file copy<br />
to/from.<br />
● Use Case (example): allow<br />
manual data xfer via<br />
SCP/SFTP between UCSC<br />
and Vendor system, to be<br />
launched by vendor system.<br />
3<br />
e<br />
COMBINE WITH 3a (and delete 3e)<br />
Limit usage to<br />
business/administrative<br />
● Use Case (example):<br />
Administrative Bus Ofc only.
3<br />
f<br />
Anonymous file drop/retrieve<br />
● Use Case (example): Allow<br />
Bus Ofc POC at UCOP to put<br />
files on system.<br />
4 Help & User Support<br />
4<br />
a<br />
NEEDS WORK<br />
Who provides user support for<br />
setup/removal of connection, bugs or<br />
problems, directory structure/file<br />
standards, and permission<br />
problems AND HOW<br />
Incident vs. Service Request vs.<br />
<strong>Information</strong> Request<br />
Service Now functionality may<br />
address this<br />
How do you support external users<br />
●<br />
●<br />
●<br />
Use Case (example): User<br />
submits request for help via IT<br />
Request; ticket is assigned to<br />
ITS Service Provider.<br />
Use Case (example): User<br />
submits request for help via IT<br />
Request; ticket is assigned to<br />
Bus Ofc.<br />
Use Case (example): User<br />
contacts Bus Ofc to request<br />
help, and Bus Ofc responds<br />
(ITS is not part of support<br />
process).<br />
4<br />
c<br />
Who provides user documentation,<br />
faqs, and training<br />
● Use Case (example): data<br />
steward will create user<br />
guides and faqs, and make
●<br />
available to users, training is<br />
not provided.<br />
Use Case (example): ITS will<br />
create technician guides and<br />
faqs, and provide for<br />
technician training.<br />
5 Directory and/or Data Structures<br />
and File Naming standards as they<br />
affect the UX or UI<br />
5<br />
a<br />
5<br />
b<br />
What is the directory/data structure<br />
needed to inform design solution, and<br />
based on customer <strong>requirements</strong><br />
What is the file naming convention<br />
needed to inform design solution, and<br />
based on customer <strong>requirements</strong><br />
6 <strong>Technical</strong>/Operational<br />
6<br />
a<br />
6<br />
b<br />
Service Availability (pick one)<br />
● Tier 3 24x7x365, excluding<br />
maintenance window, incident<br />
response, and cold backups,<br />
see also 7b<br />
● Tier 2 MF 77, excluding<br />
campus holidays or closures,<br />
maintenance window, incident<br />
response, cold backups, see<br />
also 7b<br />
● Tier 1 MF 85, excluding<br />
campus holidays or closures,<br />
maintenance window, incident<br />
response, cold backups, see<br />
also 7b<br />
Maintenance Window (which may be<br />
defined to occur outside of<br />
business/service hours):<br />
1. Frequency (pick one or more):<br />
Daily, Weekly, Monthly, Qrtly,<br />
Yearly
2. Day of Week (pick one or<br />
more, must be within Service<br />
Availability Tier):<br />
MTuWThFSaSu<br />
3. Time of Day: based on Tier 1<br />
or 2 Service Availability; if Tier<br />
3 pick time range (must start<br />
after, and finish before)<br />
4. Exception: Security patches<br />
will be applied outside the<br />
regular maintenance window,<br />
depending on<br />
risk/vulnerability, and/or as<br />
directed by ITS Security or<br />
campus <strong>Information</strong> Security<br />
Officer (ISO)<br />
6<br />
c<br />
Incident/Response:<br />
1. Response within eight<br />
business hours of receipt<br />
based on Service Availability<br />
Tier (see #6a, above), or<br />
Service Level Agreement (see<br />
#7, below)<br />
2. Repairs may be effected<br />
during business hours and<br />
pending outage tolerance of<br />
steward<br />
○ Mean Time To Repair<br />
(MTTR) is dependent<br />
on completion of root<br />
cause analysis,<br />
identification and<br />
execution of mitigation<br />
options, may be<br />
limited by vendor<br />
maintenance<br />
agreement<br />
3. Repairs may be shortterm<br />
(e.g., bring system/service<br />
online, but additional repair<br />
work is required, and will be
scheduled as needed)<br />
6<br />
d<br />
6<br />
e<br />
SHAWN TO WORDSMITH<br />
Privileged Access (Application,<br />
Database, and System<br />
Administrators)<br />
1. Will adhere to service provider<br />
guidelines<br />
2. Will use secure access<br />
methods (SSH, VPN, or other<br />
approved method)<br />
3. Will include account and<br />
access information within<br />
quarterly report to data<br />
stewards (see 2e, above)<br />
LISA TO WORDSMITH remaining of<br />
6 with Eric Keisler<br />
Where Hosted Who supports the<br />
hosting What hosting functions are<br />
included<br />
Use Case: If System will be housed<br />
in the ITS Data Center or another<br />
ITSsupported facility, consider the<br />
following <br />
○ ITS Administrators will<br />
manage the systems<br />
(application, database,<br />
hardware and<br />
operating system)<br />
○ Includes monitoring of<br />
system health, and<br />
alert when<br />
performance targets<br />
degrade<br />
■ Confirm if<br />
nonITS<br />
service<br />
provider will<br />
receive alerts
●<br />
○ Hardware refresh<br />
occurs on a fiveyear<br />
lifecycle, or as<br />
otherwise identified by<br />
the vendor (typically<br />
endoflife<br />
notifications)<br />
○ Software lifecycles<br />
are performed per<br />
vendor distribution<br />
and/or endoflife<br />
notifications<br />
Log Management<br />
○ Logs (system, app,<br />
database, etc.) may<br />
capture the following<br />
data (including but not<br />
limited to): new<br />
account, account<br />
change, account<br />
revocation, successful<br />
login attempts, failed<br />
login attempts, login<br />
attempt<br />
source/destination;<br />
activity (get/put, copy,<br />
move, remove,<br />
execute); duration of<br />
activity; web page<br />
source/destination<br />
○ Administrators<br />
periodically review<br />
and/or interrogate the<br />
audit logs, including<br />
post incident to<br />
support root cause<br />
and/or statistical<br />
analysis<br />
○ Logs may be made<br />
available to ITS<br />
Security for breach<br />
investigation and/or
●<br />
●<br />
forensics<br />
○ Results of log reviews<br />
may be made<br />
available to<br />
Data/System Steward<br />
and/or other<br />
authorities, upon<br />
request and per policy<br />
System will adhere to UC<br />
BFB IS series (IS3 and IS12)<br />
Criteria for Design Review,<br />
before production build occurs<br />
○ Class 3 or above<br />
○ Spans multiple units,<br />
or single unit<br />
budgetary discretion<br />
○ High or unknown risk<br />
○ High political value<br />
○ New or unfamiliar<br />
technology<br />
○ Upon request<br />
6<br />
f<br />
Fault Tolerance and Disaster<br />
Recovery (see IS12)<br />
● Consider redundancy of<br />
system components<br />
(reduction of singlepointsof<br />
failure) where feasible<br />
● Minimum number of<br />
environments = two (dev/test<br />
and prod)<br />
○ If "necessary" or<br />
"essential" then<br />
minimum number of<br />
environments = 3<br />
(dev/test, stage/qa,<br />
prod) (where stage/qa<br />
can accurately predict<br />
production behavior)<br />
● If "essential"<br />
○ Stage/qa environment<br />
must be equal to prod
○<br />
○<br />
(e.g., use as an<br />
alternative host in the<br />
event that production<br />
host fails and is<br />
irreparable)<br />
■ Consider<br />
automated<br />
failover vs.<br />
manual<br />
failover,<br />
depending on<br />
feasibility<br />
Consider a remote<br />
location for data and/or<br />
system replication<br />
(may place stage/qa in<br />
remote location)<br />
Establish and perform<br />
periodic disaster<br />
recovery exercises<br />
6<br />
g<br />
6<br />
h<br />
Authentication<br />
● For UCSC access (students,<br />
faculty, staff), pending<br />
technical feasibility<br />
○ Utilize Identity<br />
Management (IDM)<br />
Shibboleth or<br />
LDAPBind, or<br />
○ Utilize local<br />
authentication<br />
● For nonUCSC access<br />
○ Establish "sundry"<br />
accounts within IDM,<br />
or<br />
○ Utilize local account<br />
management<br />
Storage Management<br />
● Locallyattached vs. SAN vs<br />
NAS<br />
● Compression, duplication
(RAID)<br />
● Capacity (GB vs TB)<br />
● Quotas and/or usage<br />
○ single reminder when<br />
at 75%<br />
○ weekly reminder when<br />
>= 80%<br />
○ daily reminder when<br />
>= 90%<br />
● Data "pruning" performed<br />
periodically<br />
○ specify timespan<br />
since last update,<br />
when data is<br />
considered aged<br />
○ specify if aged data<br />
can be pruned<br />
automatically<br />
○ reminder and/or<br />
notification of pruning<br />
Data Security<br />
● Must be secure deleted<br />
● Storage device must be<br />
secure destroyed when<br />
retired, recycled, or<br />
6<br />
i<br />
Backups<br />
1. Specify includes and excludes<br />
(e.g., directory structure &<br />
permissions, user/data files,<br />
application, database,<br />
operating system, etc.)<br />
2. Specify frequency for<br />
incremental and full (typically<br />
nightly incremental, weekly<br />
full)<br />
3. Specify backup media<br />
(typically to disc then tape<br />
within same 24hour period)<br />
4. Specify backup retention<br />
period other than default (see<br />
http://its.ucsc.edu/policies/bac
kup.html for default term)<br />
○ Consider restoration<br />
feasibility if retention<br />
period is longer than 3<br />
years (e.g., you will<br />
need to assure<br />
restoration capabilities<br />
for the life of the<br />
retention period, for<br />
each backup that is<br />
maintained)<br />
○ Consider default<br />
retention period may<br />
be sufficient for those<br />
systems that retain all<br />
historical data within<br />
the transactional<br />
system versus those<br />
that archive data<br />
outside of the<br />
transactional system<br />
5. Specify onsite and offsite<br />
stores (typically cycled weekly<br />
into onsite ITS vault, then 2nd<br />
week offsite to Iron Mountain,<br />
current as of Oct 2011 and<br />
subject to change)<br />
6. Specify recycle of backup<br />
media (typically quarterly)<br />
○ Secure delete of<br />
backup media before<br />
reentry into backup<br />
cycle (regardless of<br />
IS3)<br />
7. Periodic restore test<br />
a. Perform once prior to<br />
production<br />
deployment, yearly<br />
thereafter (minimum)<br />
b. Perform tests for<br />
single file and full<br />
system restores
7 Service<br />
7<br />
a<br />
7<br />
b<br />
7<br />
c<br />
7<br />
d<br />
Utilize ITS and Campus Service Level<br />
Agreement(SLA) or serviceunique<br />
SLA (template available)<br />
Utilize common Operations Level<br />
Agreement (OLA) or serviceunique<br />
OLA (template available)<br />
ITS Practices<br />
● Request intake process and<br />
procedures<br />
● Project management<br />
methodology (andtoolkit)<br />
● SDLC for design, build, test,<br />
deploy (see alsoIS10)<br />
● Service Management Toolkit<br />
○ Incident and Change<br />
Management<br />
processes and<br />
procedures<br />
● Security Policies<br />
● Inventory tracking<br />
● Billing and Recharge<br />
Configuration and <strong>Technical</strong><br />
Documentation and Procedures<br />
● Developed, maintained, and<br />
resides with technician group<br />
Questions<br />
1. Besides business offices, who else needs access to the new system/service and/or<br />
data<br />
2. What is the existing legacy business process and/or system Can it be<br />
upgraded/enhanced or must it be replaced/retired in full or in part<br />
3. What is ITS current service commitment regarding the existing legacy business process<br />
and/or system<br />
4.
Assumptions<br />
1. Business office will perform fitgap (comparison of legacy business process vs. design<br />
solution); gaps will be accepted (implies business process reengineering), rejected<br />
(implies mitigation such as reengineering technical or business processes, and/or<br />
boltons, to address the gap), or transferred (defer mitigation as future enhancement<br />
after deployment of solution).<br />
2. Full cost a new system/service will be charged to the data/system steward, business<br />
office, and/or shared across the user community.<br />
3. If ITS SMT does not approve the new system/service, existing legacy business process<br />
and/or system will remain unchanged.<br />
4.<br />
Acronym Soup<br />
see also ITS Glossary of PolicyRelated Terms<br />
● BFB IS = Business and Finance Bulletins, <strong>Information</strong> Systems<br />
● CRUD = Create, Read, Update, Delete<br />
● CruzID = user ID managed by ITS Identity Management service<br />
● EOL = end of life<br />
● FERPA = Family Educational Rights and Privacy Act<br />
● MTTR = Mean Time to Response/Repair/Restore (duration)<br />
● OLA = Operations Level Agreement<br />
● PCI = Payment Card Industry<br />
● PII = Personal Identity <strong>Information</strong><br />
● RWXD = Read, Write, Execute, Delete<br />
● SDLC = Systems Development Life Cycle<br />
● SLA = Service Level Agreement<br />
● SMT = Senior Management Team (comprised of ITS VCIT and Directors)<br />
● SSH = Secure Shell<br />
● VPN = Virtual Private Network