A Network Approach to E-identification
A Network Approach to E-identification
A Network Approach to E-identification
- No tags were found...
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
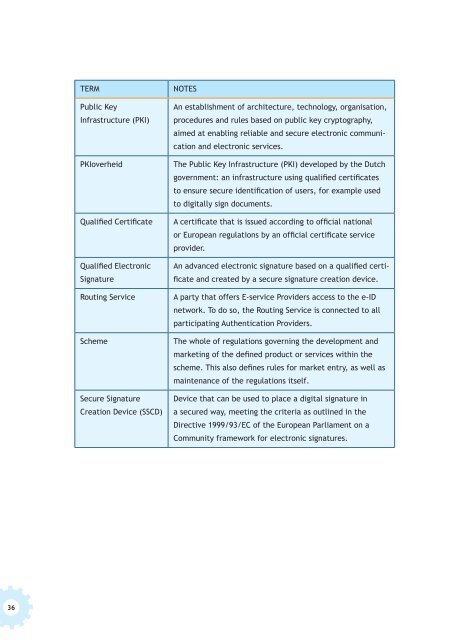
TERM<br />
Public Key<br />
Infrastructure (PKI)<br />
PKIoverheid<br />
Qualified Certificate<br />
Qualified Electronic<br />
Signature<br />
Routing Service<br />
Scheme<br />
Secure Signature<br />
Creation Device (SSCD)<br />
NOTES<br />
An establishment of architecture, technology, organisation,<br />
procedures and rules based on public key cryp<strong>to</strong>graphy,<br />
aimed at enabling reliable and secure electronic communication<br />
and electronic services.<br />
The Public Key Infrastructure (PKI) developed by the Dutch<br />
government: an infrastructure using qualified certificates<br />
<strong>to</strong> ensure secure <strong>identification</strong> of users, for example used<br />
<strong>to</strong> digitally sign documents.<br />
A certificate that is issued according <strong>to</strong> official national<br />
or European regulations by an official certificate service<br />
provider.<br />
An advanced electronic signature based on a qualified certificate<br />
and created by a secure signature creation device.<br />
A party that offers E-service Providers access <strong>to</strong> the e-ID<br />
network. To do so, the Routing Service is connected <strong>to</strong> all<br />
participating Authentication Providers.<br />
The whole of regulations governing the development and<br />
marketing of the defined product or services within the<br />
scheme. This also defines rules for market entry, as well as<br />
maintenance of the regulations itself.<br />
Device that can be used <strong>to</strong> place a digital signature in<br />
a secured way, meeting the criteria as outlined in the<br />
Directive 1999/93/EC of the European Parliament on a<br />
Community framework for electronic signatures.<br />
36