encouraging the reuse <strong>of</strong> information services to promote moreefficient acquisition management decisions. Cost avoidance willpresent a return on investment. Other potential long-term benefits<strong>of</strong> SOA are:• Establishing managed authoritative DoD acquisition datasources;• Improving data availability and reliability to decision makers;• Improving situational awareness <strong>of</strong> the acquisition status <strong>of</strong>each MDAP;• Separating data from business tools and applications;• Improving program management and oversight efficiencies;• Reducing burdensome oversight reporting; and• Reducing the acquisition cost for future business systems.A critically important governance function is to identify whereresponsibility for maintaining the single authoritative copy <strong>of</strong> anindividual data element should reside. For those data elements forwhich the service acquisition executives and program executive <strong>of</strong>ficesare responsible, there is no problem with the services controllingtheir own data.The vast majority <strong>of</strong> data for a program, however, is what may becalled “state data” such as the program name, fiscal year, departmentcode and contract number. Under SOA, these data would betransparently visible throughout the enterprise.For users, there is one place to go for any data element governedby the SOA middleware server. Each data element would come withdate and time stamps: the “pull date” when the data was accessedand the “shelf date” when the data was last updated.Data maintainers will have a streamlined method <strong>of</strong> updatingdata. The SOA governance mechanism will issue documents thatexplicitly identify what <strong>of</strong>fices are responsible for maintaining eachindividual data element. In general, data maintainers will be ableto ensure that a specific spreadsheet, for example, is kept currentwith the correct values and stored in a specific server directory. Theresult will be the elimination <strong>of</strong> continuous management requestsfor updated data tables.SOA Pilot ProjectBased on the success and lessons learned from the AT&L SOADemo, a two-phased pilot project is underway led by Bliss andKrzysko. Phase 1 was initiated in April 2008, and the initial capabilitieswill be completed by fall 2008. An additional 25 MDAPs havebeen added to the original 12 for a total <strong>of</strong> 37 which equates to acquisitiondata representing 75 percent <strong>of</strong> existing MDAPs — a $1.3trillion portfolio.The technical center for the SOA Acquisition Visibility pilots wasestablished at the Space and Naval Warfare Systems Center Atlantic,formerly SSC Charleston, with David Howard as the infrastructurelead, supporting Bliss and Krzysko.Through Phase 1 efforts, defense acquisition decision making willmove to a new paradigm <strong>of</strong> “seamless authoritative data transparency”based upon underlying governance provided by the WSLM.Figure 3 illustrates the technical approach.Phase 2, performed concurrently with Phase 1, involves developingan initial operating capability for a DoD-wide SOA infrastructurecompliant with pertinent DoD IT standards to include full competitivesource selection for technical products or solutions.Going ForwardThe primary goal <strong>of</strong> this effort is to make ACAT I programs dataconsistent across the DoD. As this is accomplished, the WSLM CBM,which includes representation from other communities, such assystems engineering, science and technology, test and evaluationand contract management, will work to align data using WSLM definitions.The result will be the establishment <strong>of</strong> a durable data governancemechanism for regulating DoD’s acquisition data, as wellas the provision <strong>of</strong> a data infrastructure and SOA services, whichmakes data as a service a reality in the acquisition domain.Martin Fairclough is a senior principal consultant supporting the AT&L SOATeam.Authoritative Data• <strong>Navy</strong> Dashboard• Army AIM• Air Force SMART• DAMIRAIM – Acquisition <strong>Information</strong> Management is an enterpriseacquisition management tool that serves as an earned valuecentral repository and exhibits the probability <strong>of</strong> success <strong>of</strong> anacquisition program.Dashboard – database for strategic management and procurementin Acquisition Category (ACAT) I and II programs.Kaleidoscope – DoD tool designed to provide greater portfoliomanagement, data visibility and access to analytic commercialtools.SMART - System Metrics and Reporting Tool is a tracking toolto manage hundreds <strong>of</strong> contracts for current cost, schedule andperformance information; perform contract reviews; do trendanalysis; and get customized portfolios <strong>of</strong> programs.Demonstration PhaseTechnical DemonstrationQueryResponseDemo SOAAuthoritative Data• <strong>Navy</strong> Dashboard• Army AIM• Air Force SMART• DAMIR• Central Repository• OtherBI toolWeb Service• Earned Value Management• Program Management (General)• Unit Cost (Nunn-McCurdy)• Science and Technology• Milestones• Budget/POM BES/Current EstimatePilot Phase ICollaborative ApproachOpen Source/IntegratedCOTSIntegratedProductSuite BI toolESB 2 BI toolOpenSourceProductSuite3 BI toolCommon access pointfor OSD toolsFigure 3. Acquisition Data Technical Approach.50 CHIPS www.chips.navy.mil Dedicated to Sharing <strong>Information</strong> - Technology - Experience“Accurate, timely, coherent data use within theacquisition community is fundamental to betterdecision making … SOA which is widely used in thecommercial sector, separates data governance fromthe tools that use the data. It makes data immediatelyavailable to users — irrespective <strong>of</strong> institutionalhierarchy — and facilitates efficient acquisitionmanagement decisions”John J. Young Jr.USD AT&LPhase II - Product EnvironmentAuthoritative Data• <strong>Navy</strong> Dashboard• Army AIM• Air Force SMART• DAMIR• Central Repository• OtherWeb Service - TBDAny BI tool for anydecision makingpurposeSOA product suite - TBD
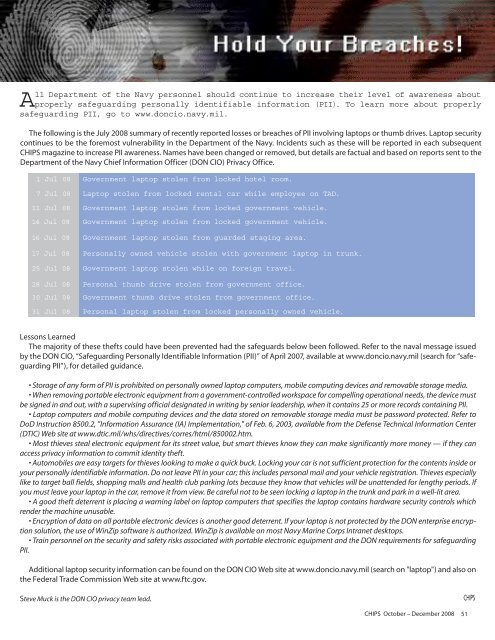
All <strong>Department</strong> <strong>of</strong> the <strong>Navy</strong> personnel should continue to increase their level <strong>of</strong> awareness aboutproperly safeguarding personally identifiable information (PII). To learn more about properlysafeguarding PII, go to www.doncio.navy.mil.The following is the July 2008 summary <strong>of</strong> recently reported losses or breaches <strong>of</strong> PII involving laptops or thumb drives. Laptop securitycontinues to be the foremost vulnerability in the <strong>Department</strong> <strong>of</strong> the <strong>Navy</strong>. Incidents such as these will be reported in each subsequentCHIPS magazine to increase PII awareness. Names have been changed or removed, but details are factual and based on reports sent to the<strong>Department</strong> <strong>of</strong> the <strong>Navy</strong> <strong>Chief</strong> <strong>Information</strong> <strong>Officer</strong> (DON CIO) Privacy Office.1 Jul 08 Government laptop stolen from locked hotel room.7 Jul 08 Laptop stolen from locked rental car while employee on TAD.11 Jul 08 Government laptop stolen from locked government vehicle.14 Jul 08 Government laptop stolen from locked government vehicle.16 Jul 08 Government laptop stolen from guarded staging area.17 Jul 08 Personally owned vehicle stolen with government laptop in trunk.25 Jul 08 Government laptop stolen while on foreign travel.28 Jul 08 Personal thumb drive stolen from government <strong>of</strong>fice.30 Jul 08 Government thumb drive stolen from government <strong>of</strong>fice.31 Jul 08 Personal laptop stolen from locked personally owned vehicle.Lessons LearnedThe majority <strong>of</strong> these thefts could have been prevented had the safeguards below been followed. Refer to the naval message issuedby the DON CIO, “Safeguarding Personally Identifiable <strong>Information</strong> (PII)” <strong>of</strong> April 2007, available at www.doncio.navy.mil (search for “safeguardingPII”), for detailed guidance.• Storage <strong>of</strong> any form <strong>of</strong> PII is prohibited on personally owned laptop computers, mobile computing devices and removable storage media.• When removing portable electronic equipment from a government-controlled workspace for compelling operational needs, the device mustbe signed in and out, with a supervising <strong>of</strong>ficial designated in writing by senior leadership, when it contains 25 or more records containing PII.• Laptop computers and mobile computing devices and the data stored on removable storage media must be password protected. Refer toDoD Instruction 8500.2, "<strong>Information</strong> Assurance (IA) Implementation," <strong>of</strong> Feb. 6, 2003, available from the Defense Technical <strong>Information</strong> Center(DTIC) Web site at www.dtic.mil/whs/directives/corres/html/850002.htm.• Most thieves steal electronic equipment for its street value, but smart thieves know they can make significantly more money — if they canaccess privacy information to commit identity theft.• Automobiles are easy targets for thieves looking to make a quick buck. Locking your car is not sufficient protection for the contents inside oryour personally identifiable information. Do not leave PII in your car; this includes personal mail and your vehicle registration. Thieves especiallylike to target ball fields, shopping malls and health club parking lots because they know that vehicles will be unattended for lengthy periods. Ifyou must leave your laptop in the car, remove it from view. Be careful not to be seen locking a laptop in the trunk and park in a well-lit area.• A good theft deterrent is placing a warning label on laptop computers that specifies the laptop contains hardware security controls whichrender the machine unusable.• Encryption <strong>of</strong> data on all portable electronic devices is another good deterrent. If your laptop is not protected by the DON enterprise encryptionsolution, the use <strong>of</strong> WinZip s<strong>of</strong>tware is authorized. WinZip is available on most <strong>Navy</strong> Marine Corps Intranet desktops.• Train personnel on the security and safety risks associated with portable electronic equipment and the DON requirements for safeguardingPII.Additional laptop security information can be found on the DON CIO Web site at www.doncio.navy.mil (search on "laptop") and also onthe Federal Trade Commission Web site at www.ftc.gov.Steve Muck is the DON CIO privacy team lead.CHIPS October – December 2008 51