EXPLOITING EMBEDDED SYSTEMS THE SEQUEL!
Exploitation - CanSecWest
Exploitation - CanSecWest
- No tags were found...
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
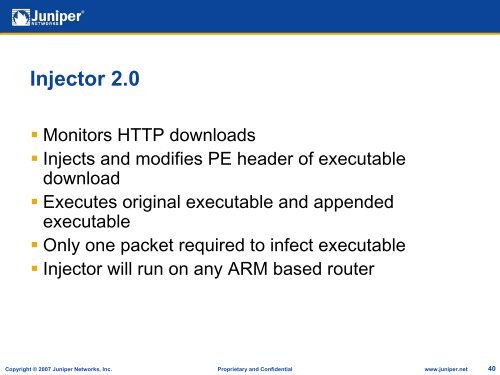
Injector 2.0• Monitors HTTP downloads• Injects and modifies PE header of executabledownload• Executes original executable and appendedexecutable• Only one packet required to infect executable• Injector will run on any ARM based routerCopyright © 2007 Juniper Networks, Inc. Proprietary and Confidential www.juniper.net 40