trademark
2c2kIhh
2c2kIhh
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
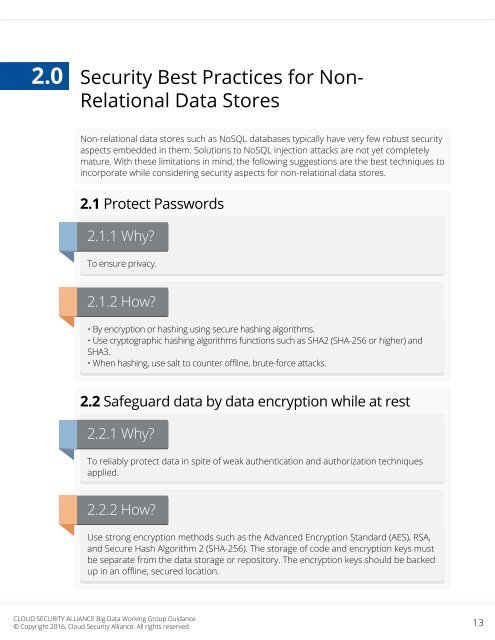
2.0<br />
Security Best Practices for Non-<br />
Relational Data Stores<br />
Non-relational data stores such as NoSQL databases typically have very few robust security<br />
aspects embedded in them. Solutions to NoSQL injection attacks are not yet completely<br />
mature. With these limitations in mind, the following suggestions are the best techniques to<br />
incorporate while considering security aspects for non-relational data stores.<br />
2.1 Protect Passwords<br />
2.1.1 Why?<br />
To ensure privacy.<br />
2.1.2 How?<br />
• By encryption or hashing using secure hashing algorithms.<br />
• Use cryptographic hashing algorithms functions such as SHA2 (SHA-256 or higher) and<br />
SHA3.<br />
• When hashing, use salt to counter offline, brute-force attacks.<br />
2.2 Safeguard data by data encryption while at rest<br />
2.2.1 Why?<br />
To reliably protect data in spite of weak authentication and authorization techniques<br />
applied.<br />
2.2.2 How?<br />
Use strong encryption methods such as the Advanced Encryption Standard (AES), RSA,<br />
and Secure Hash Algorithm 2 (SHA-256). The storage of code and encryption keys must<br />
be separate from the data storage or repository. The encryption keys should be backed<br />
up in an offline, secured location.<br />
CLOUD SECURITY ALLIANCE Big Data Working Group Guidance<br />
© Copyright 2016, Cloud Security Alliance. All rights reserved.<br />
13