trademark
2c2kIhh
2c2kIhh
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
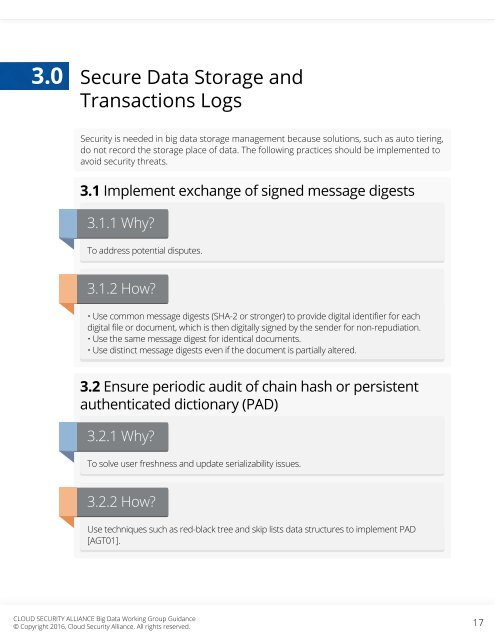
3.0<br />
Secure Data Storage and<br />
Transactions Logs<br />
Security is needed in big data storage management because solutions, such as auto tiering,<br />
do not record the storage place of data. The following practices should be implemented to<br />
avoid security threats.<br />
3.1 Implement exchange of signed message digests<br />
3.1.1 Why?<br />
To address potential disputes.<br />
3.1.2 How?<br />
• Use common message digests (SHA-2 or stronger) to provide digital identifier for each<br />
digital file or document, which is then digitally signed by the sender for non-repudiation.<br />
• Use the same message digest for identical documents.<br />
• Use distinct message digests even if the document is partially altered.<br />
3.2 Ensure periodic audit of chain hash or persistent<br />
authenticated dictionary (PAD)<br />
3.2.1 Why?<br />
To solve user freshness and update serializability issues.<br />
3.2.2 How?<br />
Use techniques such as red-black tree and skip lists data structures to implement PAD<br />
[AGT01].<br />
CLOUD SECURITY ALLIANCE Big Data Working Group Guidance<br />
© Copyright 2016, Cloud Security Alliance. All rights reserved.<br />
17