trademark
2c2kIhh
2c2kIhh
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
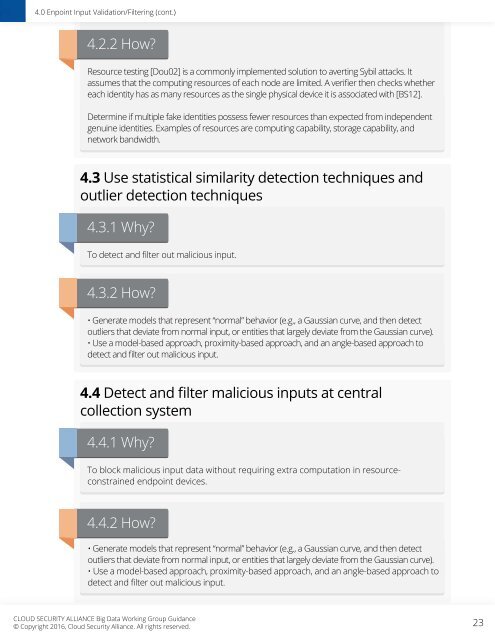
4.0 Enpoint Input Validation/Filtering (cont.)<br />
4.2.2 How?<br />
Resource testing [Dou02] is a commonly implemented solution to averting Sybil attacks. It<br />
assumes that the computing resources of each node are limited. A verifier then checks whether<br />
each identity has as many resources as the single physical device it is associated with [BS12].<br />
Determine if multiple fake identities possess fewer resources than expected from independent<br />
genuine identities. Examples of resources are computing capability, storage capability, and<br />
network bandwidth.<br />
4.3 Use statistical similarity detection techniques and<br />
outlier detection techniques<br />
4.3.1 Why?<br />
To detect and filter out malicious input.<br />
4.3.2 How?<br />
• Generate models that represent “normal” behavior (e.g., a Gaussian curve, and then detect<br />
outliers that deviate from normal input, or entities that largely deviate from the Gaussian curve).<br />
• Use a model-based approach, proximity-based approach, and an angle-based approach to<br />
detect and filter out malicious input.<br />
4.4 Detect and filter malicious inputs at central<br />
collection system<br />
4.4.1 Why?<br />
To block malicious input data without requiring extra computation in resourceconstrained<br />
endpoint devices.<br />
4.4.2 How?<br />
• Generate models that represent “normal” behavior (e.g., a Gaussian curve, and then detect<br />
outliers that deviate from normal input, or entities that largely deviate from the Gaussian curve).<br />
• Use a model-based approach, proximity-based approach, and an angle-based approach to<br />
detect and filter out malicious input.<br />
CLOUD SECURITY ALLIANCE Big Data Working Group Guidance<br />
© Copyright 2016, Cloud Security Alliance. All rights reserved.<br />
23