trademark
2c2kIhh
2c2kIhh
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
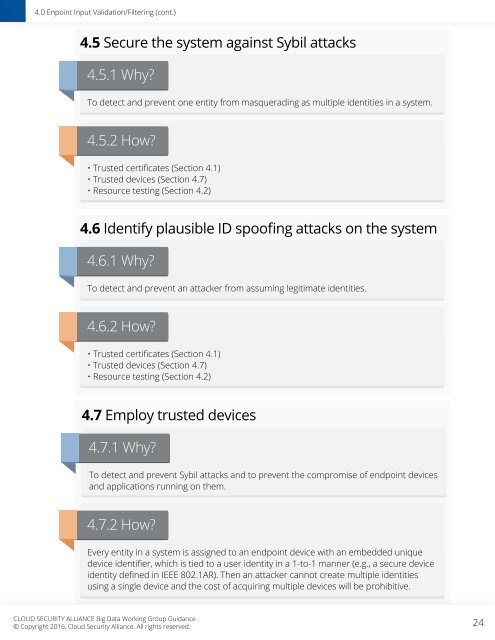
4.0 Enpoint Input Validation/Filtering (cont.)<br />
4.5 Secure the system against Sybil attacks<br />
4.5.1 Why?<br />
To detect and prevent one entity from masquerading as multiple identities in a system.<br />
4.5.2 How?<br />
• Trusted certificates (Section 4.1)<br />
• Trusted devices (Section 4.7)<br />
• Resource testing (Section 4.2)<br />
4.6 Identify plausible ID spoofing attacks on the system<br />
4.6.1 Why?<br />
To detect and prevent an attacker from assuming legitimate identities.<br />
4.6.2 How?<br />
• Trusted certificates (Section 4.1)<br />
• Trusted devices (Section 4.7)<br />
• Resource testing (Section 4.2)<br />
4.7 Employ trusted devices<br />
4.7.1 Why?<br />
To detect and prevent Sybil attacks and to prevent the compromise of endpoint devices<br />
and applications running on them.<br />
4.7.2 How?<br />
Every entity in a system is assigned to an endpoint device with an embedded unique<br />
device identifier, which is tied to a user identity in a 1-to-1 manner (e.g., a secure device<br />
identity defined in IEEE 802.1AR). Then an attacker cannot create multiple identities<br />
using a single device and the cost of acquiring multiple devices will be prohibitive.<br />
CLOUD SECURITY ALLIANCE Big Data Working Group Guidance<br />
© Copyright 2016, Cloud Security Alliance. All rights reserved.<br />
24