Investigation of Linux.Mirai Trojan family
u97CXm
u97CXm
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
22<br />
22<br />
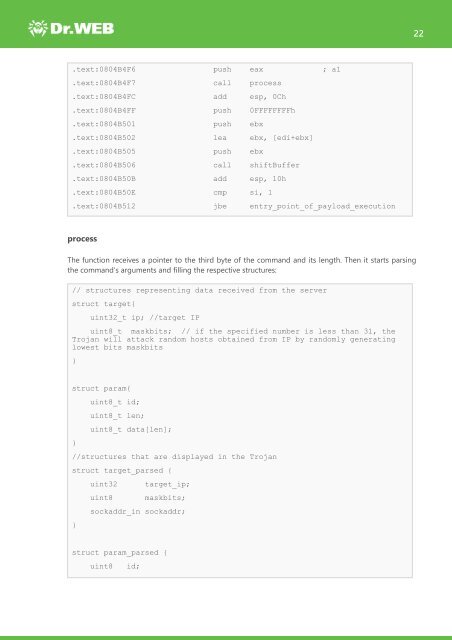
.text:0804B4F6 push eax ; a1<br />
.text:0804B4F7 call process<br />
.text:0804B4FC add esp, 0Ch<br />
.text:0804B4FF push 0FFFFFFFFh<br />
.text:0804B501 push ebx<br />
.text:0804B502 lea ebx, [edi+ebx]<br />
.text:0804B505 push ebx<br />
.text:0804B506 call shiftBuffer<br />
.text:0804B50B add esp, 10h<br />
.text:0804B50E cmp si, 1<br />
.text:0804B512 jbe entry_point_<strong>of</strong>_payload_execution<br />
process<br />
The function receives a pointer to the third byte <strong>of</strong> the command and its length. Then it starts parsing<br />
the command’s arguments and filling the respective structures:<br />
// structures representing data received from the server<br />
struct target{<br />
uint32_t ip; //target IP<br />
uint8_t maskbits; // if the specified number is less than 31, the<br />
<strong>Trojan</strong> will attack random hosts obtained from IP by randomly generating<br />
lowest bits maskbits<br />
}<br />
struct param{<br />
uint8_t id;<br />
uint8_t len;<br />
uint8_t data[len];<br />
}<br />
//structures that are displayed in the <strong>Trojan</strong><br />
struct target_parsed {<br />
uint32 target_ip;<br />
uint8 maskbits;<br />
sockaddr_in sockaddr;<br />
}<br />
struct param_parsed {<br />
uint8<br />
id;