Investigation of Linux.Mirai Trojan family
u97CXm
u97CXm
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
48<br />
48<br />
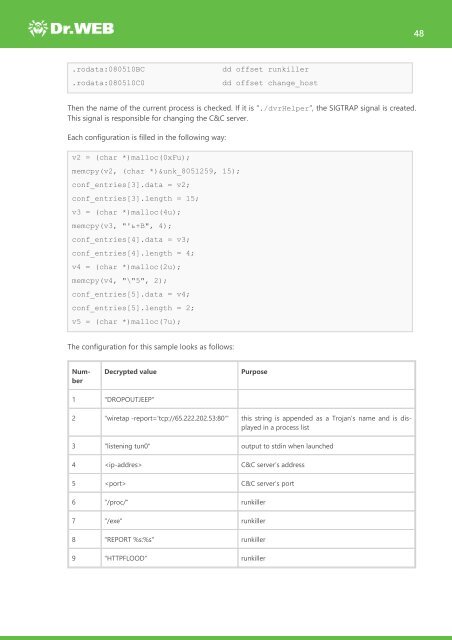
.rodata:080510BC<br />
.rodata:080510C0<br />
dd <strong>of</strong>fset runkiller<br />
dd <strong>of</strong>fset change_host<br />
Then the name <strong>of</strong> the current process is checked. If it is “./dvrHelper”, the SIGTRAP signal is created.<br />
This signal is responsible for changing the C&C server.<br />
Each configuration is filled in the following way:<br />
v2 = (char *)malloc(0xFu);<br />
memcpy(v2, (char *)&unk_8051259, 15);<br />
conf_entries[3].data = v2;<br />
conf_entries[3].length = 15;<br />
v3 = (char *)malloc(4u);<br />
memcpy(v3, "'ь+B", 4);<br />
conf_entries[4].data = v3;<br />
conf_entries[4].length = 4;<br />
v4 = (char *)malloc(2u);<br />
memcpy(v4, "\"5", 2);<br />
conf_entries[5].data = v4;<br />
conf_entries[5].length = 2;<br />
v5 = (char *)malloc(7u);<br />
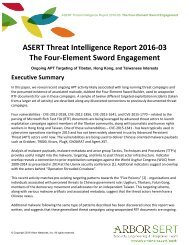
The configuration for this sample looks as follows:<br />
Number<br />
Decrypted value<br />
Purpose<br />
1 "DROPOUTJEEP"<br />
2 "wiretap -report='tcp://65.222.202.53:80'" this string is appended as a <strong>Trojan</strong>’s name and is displayed<br />
in a process list<br />
3 "listening tun0" output to stdin when launched<br />
4 C&C server’s address<br />
5 C&C server’s port<br />
6 "/proc/" runkiller<br />
7 "/exe" runkiller<br />
8 "REPORT %s:%s" runkiller<br />
9 "HTTPFLOOD" runkiller