DoD Implementation Guide for CAC PIV End-Point - Common ...
DoD Implementation Guide for CAC PIV End-Point - Common ...
DoD Implementation Guide for CAC PIV End-Point - Common ...
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
<strong>DoD</strong> <strong>Implementation</strong> <strong>Guide</strong> <strong>for</strong> <strong>CAC</strong> <strong>PIV</strong> <strong>End</strong>-<strong>Point</strong><br />
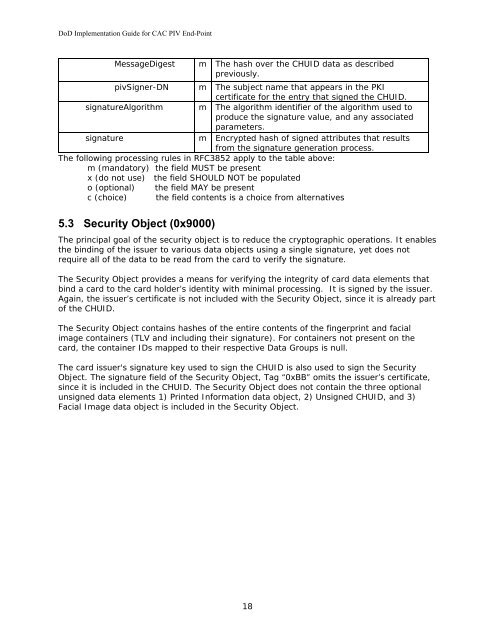
MessageDigest m The hash over the CHUID data as described<br />
previously.<br />
pivSigner-DN m The subject name that appears in the PKI<br />
certificate <strong>for</strong> the entry that signed the CHUID.<br />
signatureAlgorithm m The algorithm identifier of the algorithm used to<br />
produce the signature value, and any associated<br />
parameters.<br />
signature m Encrypted hash of signed attributes that results<br />
from the signature generation process.<br />
The following processing rules in RFC3852 apply to the table above:<br />
m (mandatory) the field MUST be present<br />
x (do not use) the field SHOULD NOT be populated<br />
o (optional) the field MAY be present<br />
c (choice) the field contents is a choice from alternatives<br />
5.3 Security Object (0x9000)<br />
The principal goal of the security object is to reduce the cryptographic operations. It enables<br />
the binding of the issuer to various data objects using a single signature, yet does not<br />
require all of the data to be read from the card to verify the signature.<br />
The Security Object provides a means <strong>for</strong> verifying the integrity of card data elements that<br />
bind a card to the card holder’s identity with minimal processing. It is signed by the issuer.<br />
Again, the issuer’s certificate is not included with the Security Object, since it is already part<br />
of the CHUID.<br />
The Security Object contains hashes of the entire contents of the fingerprint and facial<br />
image containers (TLV and including their signature). For containers not present on the<br />
card, the container IDs mapped to their respective Data Groups is null.<br />
The card issuer's signature key used to sign the CHUID is also used to sign the Security<br />
Object. The signature field of the Security Object, Tag “0xBB” omits the issuer’s certificate,<br />
since it is included in the CHUID. The Security Object does not contain the three optional<br />
unsigned data elements 1) Printed In<strong>for</strong>mation data object, 2) Unsigned CHUID, and 3)<br />
Facial Image data object is included in the Security Object.<br />
18