DoD Implementation Guide for CAC PIV End-Point - Common ...
DoD Implementation Guide for CAC PIV End-Point - Common ...
DoD Implementation Guide for CAC PIV End-Point - Common ...
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
<strong>DoD</strong> <strong>Implementation</strong> <strong>Guide</strong> <strong>for</strong> <strong>CAC</strong> <strong>PIV</strong> <strong>End</strong>-<strong>Point</strong><br />
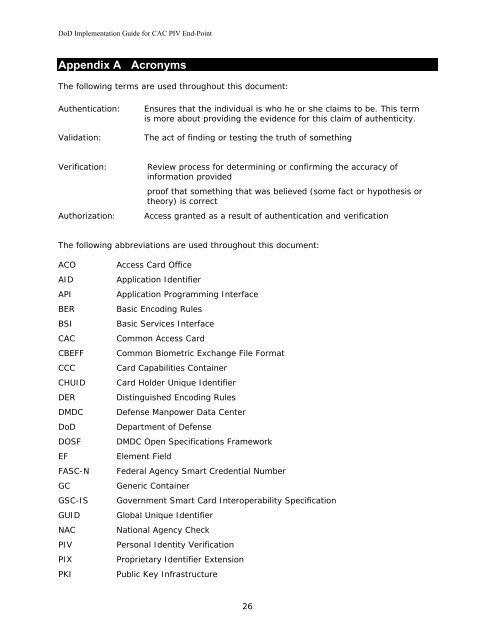
Appendix A Acronyms<br />
The following terms are used throughout this document:<br />
Authentication: Ensures that the individual is who he or she claims to be. This term<br />
is more about providing the evidence <strong>for</strong> this claim of authenticity.<br />
Validation: The act of finding or testing the truth of something<br />
Verification: Review process <strong>for</strong> determining or confirming the accuracy of<br />
in<strong>for</strong>mation provided<br />
The following abbreviations are used throughout this document:<br />
ACO Access Card Office<br />
AID Application Identifier<br />
API Application Programming Interface<br />
BER Basic Encoding Rules<br />
BSI Basic Services Interface<br />
<strong>CAC</strong> <strong>Common</strong> Access Card<br />
CBEFF <strong>Common</strong> Biometric Exchange File Format<br />
CCC Card Capabilities Container<br />
CHUID Card Holder Unique Identifier<br />
DER Distinguished Encoding Rules<br />
DMDC Defense Manpower Data Center<br />
<strong>DoD</strong> Department of Defense<br />
DOSF DMDC Open Specifications Framework<br />
EF Element Field<br />
FASC-N Federal Agency Smart Credential Number<br />
GC Generic Container<br />
GSC-IS Government Smart Card Interoperability Specification<br />
GUID Global Unique Identifier<br />
NAC National Agency Check<br />
<strong>PIV</strong> Personal Identity Verification<br />
PIX Proprietary Identifier Extension<br />
PKI Public Key Infrastructure<br />
proof that something that was believed (some fact or hypothesis or<br />
theory) is correct<br />
Authorization: Access granted as a result of authentication and verification<br />
26