DoD Implementation Guide for CAC PIV End-Point - Common ...
DoD Implementation Guide for CAC PIV End-Point - Common ...
DoD Implementation Guide for CAC PIV End-Point - Common ...
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
<strong>DoD</strong> <strong>Implementation</strong> <strong>Guide</strong> <strong>for</strong> <strong>CAC</strong> <strong>PIV</strong> <strong>End</strong>-<strong>Point</strong><br />
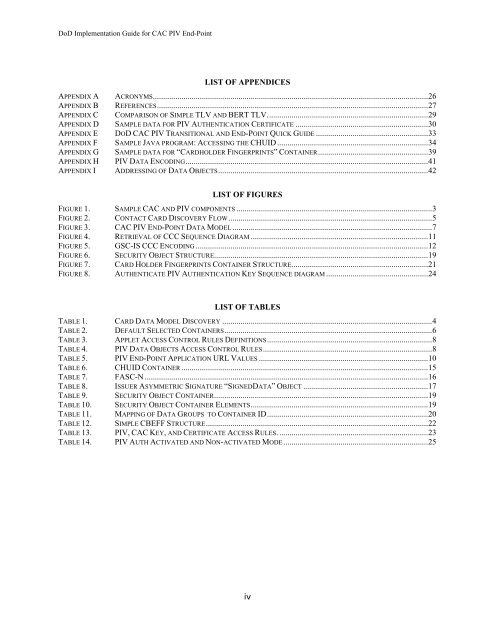
LIST OF APPENDICES<br />
APPENDIX A ACRONYMS.......................................................................................................................................26<br />
APPENDIX B REFERENCES.....................................................................................................................................27<br />
APPENDIX C COMPARISON OF SIMPLE TLV AND BERT TLV...............................................................................29<br />
APPENDIX D SAMPLE DATA FOR <strong>PIV</strong> AUTHENTICATION CERTIFICATE .................................................................30<br />
APPENDIX E DOD <strong>CAC</strong> <strong>PIV</strong> TRANSITIONAL AND END-POINT QUICK GUIDE .......................................................33<br />
APPENDIX F SAMPLE JAVA PROGRAM: ACCESSING THE CHUID ..........................................................................34<br />
APPENDIX G SAMPLE DATA FOR “CARDHOLDER FINGERPRINTS” CONTAINER......................................................39<br />
APPENDIX H <strong>PIV</strong> DATA ENCODING.......................................................................................................................41<br />
APPENDIX I ADDRESSING OF DATA OBJECTS.......................................................................................................42<br />
LIST OF FIGURES<br />
FIGURE 1. SAMPLE <strong>CAC</strong> AND <strong>PIV</strong> COMPONENTS ................................................................................................3<br />
FIGURE 2. CONTACT CARD DISCOVERY FLOW....................................................................................................5<br />
FIGURE 3. <strong>CAC</strong> <strong>PIV</strong> END-POINT DATA MODEL..................................................................................................7<br />
FIGURE 4. RETRIEVAL OF CCC SEQUENCE DIAGRAM .......................................................................................11<br />
FIGURE 5. GSC-IS CCC ENCODING ..................................................................................................................12<br />
FIGURE 6. SECURITY OBJECT STRUCTURE.........................................................................................................19<br />
FIGURE 7. CARD HOLDER FINGERPRINTS CONTAINER STRUCTURE...................................................................21<br />
FIGURE 8. AUTHENTICATE <strong>PIV</strong> AUTHENTICATION KEY SEQUENCE DIAGRAM ..................................................24<br />
LIST OF TABLES<br />
TABLE 1. CARD DATA MODEL DISCOVERY .......................................................................................................4<br />
TABLE 2. DEFAULT SELECTED CONTAINERS......................................................................................................6<br />
TABLE 3. APPLET ACCESS CONTROL RULES DEFINITIONS.................................................................................8<br />
TABLE 4. <strong>PIV</strong> DATA OBJECTS ACCESS CONTROL RULES...................................................................................8<br />
TABLE 5. <strong>PIV</strong> END-POINT APPLICATION URL VALUES ...................................................................................10<br />
TABLE 6. CHUID CONTAINER .........................................................................................................................15<br />
TABLE 7. FASC-N ...........................................................................................................................................16<br />
TABLE 8. ISSUER ASYMMETRIC SIGNATURE “SIGNEDDATA” OBJECT .............................................................17<br />
TABLE 9. SECURITY OBJECT CONTAINER.........................................................................................................19<br />
TABLE 10. SECURITY OBJECT CONTAINER ELEMENTS.......................................................................................19<br />
TABLE 11. MAPPING OF DATA GROUPS TO CONTAINER ID...............................................................................20<br />
TABLE 12. SIMPLE CBEFF STRUCTURE.............................................................................................................22<br />
TABLE 13. <strong>PIV</strong>, <strong>CAC</strong> KEY, AND CERTIFICATE ACCESS RULES. .........................................................................23<br />
TABLE 14. <strong>PIV</strong> AUTH ACTIVATED AND NON-ACTIVATED MODE.......................................................................25<br />
iv