Oracle JHeadstart Developer's Guide - Downloads - Oracle
Oracle JHeadstart Developer's Guide - Downloads - Oracle
Oracle JHeadstart Developer's Guide - Downloads - Oracle
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
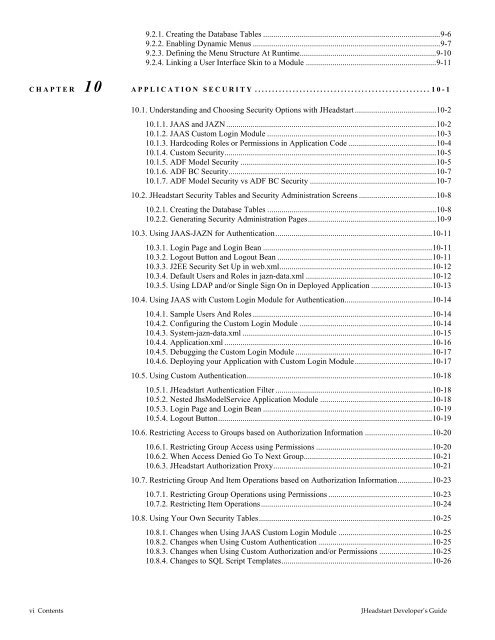
9.2.1. Creating the Database Tables .......................................................................................9-6<br />
9.2.2. Enabling Dynamic Menus ............................................................................................9-7<br />
9.2.3. Defining the Menu Structure At Runtime...................................................................9-10<br />
9.2.4. Linking a User Interface Skin to a Module ................................................................9-11<br />
CHAPTER 10 APPLICATION SECURITY ...................................................10-1<br />
10.1. Understanding and Choosing Security Options with <strong>JHeadstart</strong>........................................10-2<br />
10.1.1. JAAS and JAZN .......................................................................................................10-2<br />
10.1.2. JAAS Custom Login Module ...................................................................................10-3<br />
10.1.3. Hardcoding Roles or Permissions in Application Code ...........................................10-4<br />
10.1.4. Custom Security........................................................................................................10-5<br />
10.1.5. ADF Model Security ................................................................................................10-5<br />
10.1.6. ADF BC Security......................................................................................................10-7<br />
10.1.7. ADF Model Security vs ADF BC Security ..............................................................10-7<br />
10.2. <strong>JHeadstart</strong> Security Tables and Security Administration Screens ......................................10-8<br />
10.2.1. Creating the Database Tables ...................................................................................10-8<br />
10.2.2. Generating Security Administration Pages...............................................................10-9<br />
10.3. Using JAAS-JAZN for Authentication.............................................................................10-11<br />
10.3.1. Login Page and Login Bean ...................................................................................10-11<br />
10.3.2. Logout Button and Logout Bean ............................................................................10-11<br />
10.3.3. J2EE Security Set Up in web.xml...........................................................................10-12<br />
10.3.4. Default Users and Roles in jazn-data.xml ..............................................................10-12<br />
10.3.5. Using LDAP and/or Single Sign On in Deployed Application ..............................10-13<br />
10.4. Using JAAS with Custom Login Module for Authentication...........................................10-14<br />
10.4.1. Sample Users And Roles ........................................................................................10-14<br />
10.4.2. Configuring the Custom Login Module .................................................................10-14<br />
10.4.3. System-jazn-data.xml .............................................................................................10-15<br />
10.4.4. Application.xml ......................................................................................................10-16<br />
10.4.5. Debugging the Custom Login Module ...................................................................10-17<br />
10.4.6. Deploying your Application with Custom Login Module......................................10-17<br />
10.5. Using Custom Authentication...........................................................................................10-18<br />
10.5.1. <strong>JHeadstart</strong> Authentication Filter .............................................................................10-18<br />
10.5.2. Nested JhsModelService Application Module .......................................................10-18<br />
10.5.3. Login Page and Login Bean ...................................................................................10-19<br />
10.5.4. Logout Button.........................................................................................................10-19<br />
10.6. Restricting Access to Groups based on Authorization Information .................................10-20<br />
10.6.1. Restricting Group Access using Permissions .........................................................10-20<br />
10.6.2. When Access Denied Go To Next Group...............................................................10-21<br />
10.6.3. <strong>JHeadstart</strong> Authorization Proxy..............................................................................10-21<br />
10.7. Restricting Group And Item Operations based on Authorization Information.................10-23<br />
10.7.1. Restricting Group Operations using Permissions ...................................................10-23<br />
10.7.2. Restricting Item Operations....................................................................................10-24<br />
10.8. Using Your Own Security Tables.....................................................................................10-25<br />
10.8.1. Changes when Using JAAS Custom Login Module ..............................................10-25<br />
10.8.2. Changes when Using Custom Authentication ........................................................10-25<br />
10.8.3. Changes when Using Custom Authorization and/or Permissions ..........................10-25<br />
10.8.4. Changes to SQL Script Templates..........................................................................10-26<br />
vi Contents <strong>JHeadstart</strong> Developer’s <strong>Guide</strong>