Lectures for 2008 - KTH
Lectures for 2008 - KTH
Lectures for 2008 - KTH
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
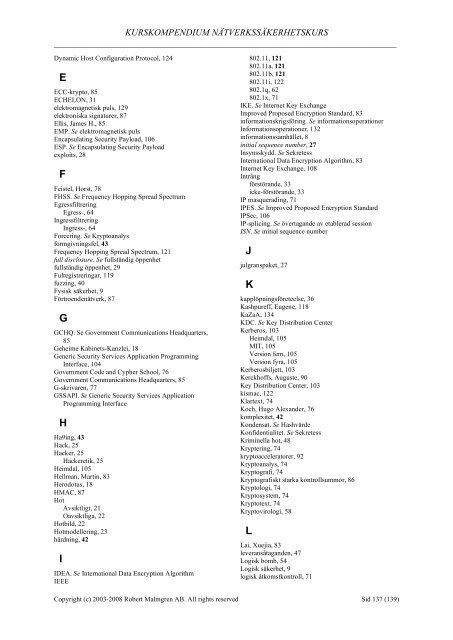
KURSKOMPENDIUM NÄTVERKSSÄKERHETSKURS<br />
___________________________________________________________________________<br />
Dynamic Host Configuration Protocol, 124<br />
E<br />
ECC-krypto, 85<br />
ECHELON, 31<br />
elektromagnetisk puls, 129<br />
elektroniska signaturer, 87<br />
Ellis, James H., 85<br />
EMP. Se elektromagnetisk puls<br />
Encapsulating Security Payload, 106<br />
ESP. Se Encapsulating Security Payload<br />
exploits, 28<br />
F<br />
Feistel, Horst, 78<br />
FHSS. Se Frequency Hopping Spread Spectrum<br />
Egressfiltrering<br />
Egress-, 64<br />
Ingressfiltrering<br />
Ingress-, 64<br />
Forcering. Se Kryptoanalys<br />
<strong>for</strong>mgivningsfel, 43<br />
Frequency Hopping Spread Spectrum, 121<br />
full disclosure. Se fullständig öppenhet<br />
fullständig öppenhet, 29<br />
Fulregistreringar, 119<br />
fuzzing, 40<br />
Fysisk säkerhet, 9<br />
Förtroendenätverk, 87<br />
G<br />
GCHQ. Se Government Communications Headquarters,<br />
85<br />
Geheime Kabinets-Kanzlei, 18<br />
Generic Security Services Application Programming<br />
Interface, 104<br />
Government Code and Cypher School, 76<br />
Government Communications Headquarters, 85<br />
G-skrivaren, 77<br />
GSSAPI. Se Generic Security Services Application<br />
Programming Interface<br />
H<br />
Ha9ing, 43<br />
Hack, 25<br />
Hacker, 25<br />
Hackeretik, 25<br />
Heimdal, 105<br />
Hellman, Martin, 83<br />
Herodotus, 18<br />
HMAC, 87<br />
Hot<br />
Avsiktligt, 21<br />
Oavsiktliga, 22<br />
Hotbild, 22<br />
Hotmodellering, 23<br />
härdning, 42<br />
I<br />
IDEA. Se International Data Encryption Algorithm<br />
IEEE<br />
802.11, 121<br />
802.11a, 121<br />
802.11b, 121<br />
802.11i, 122<br />
802.1q, 62<br />
802.1x, 71<br />
IKE. Se Internet Key Exchange<br />
Improved Proposed Encryption Standard, 83<br />
in<strong>for</strong>mationskrigsföring. Se in<strong>for</strong>mationsoperationer<br />
In<strong>for</strong>mationsoperationer, 132<br />
in<strong>for</strong>mationssamhället, 8<br />
initial sequence number, 27<br />
Insynsskydd. Se Sekretess<br />
International Data Encryption Algorithm, 83<br />
Internet Key Exchange, 108<br />
Intrång<br />
förstörande, 33<br />
icke-förstörande, 33<br />
IP masquerading, 71<br />
IPES. Se Improved Proposed Encryption Standard<br />
IPSec, 106<br />
IP-splicing. Se övertagande av etablerad session<br />
ISN. Se initial sequence number<br />
J<br />
julgranspaket, 27<br />
K<br />
kapplöpningsföreteelse, 36<br />
Kashpureff, Eugene, 118<br />
KaZaA, 134<br />
KDC. Se Key Distribution Center<br />
Kerberos, 103<br />
Heimdal, 105<br />
MIT, 105<br />
Version fem, 105<br />
Version fyra, 105<br />
Kerberosbiljett, 103<br />
Kerckhoffs, Auguste, 90<br />
Key Distribution Center, 103<br />
kismac, 122<br />
Klartext, 74<br />
Koch, Hugo Alexander, 76<br />
komplexitet, 42<br />
Kondensat. Se Hashvärde<br />
Konfidentialitet. Se Sekretess<br />
Kriminella hot, 48<br />
Kryptering, 74<br />
kryptoacceleratorer, 92<br />
Kryptoanalys, 74<br />
Kryptografi, 74<br />
Kryptografiskt starka kontrollsummor, 86<br />
Kryptologi, 74<br />
Kryptosystem, 74<br />
Kryptotext, 74<br />
Kryptovirologi, 58<br />
L<br />
Lai, Xuejia, 83<br />
leveransåtaganden, 47<br />
Logisk bomb, 54<br />
Logisk säkerhet, 9<br />
logisk åtkomstkontroll, 71<br />
Copyright (c) 2003-<strong>2008</strong> Robert Malmgren AB. All rights reserved Sid 137 (139)