Lectures for 2008 - KTH
Lectures for 2008 - KTH
Lectures for 2008 - KTH
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
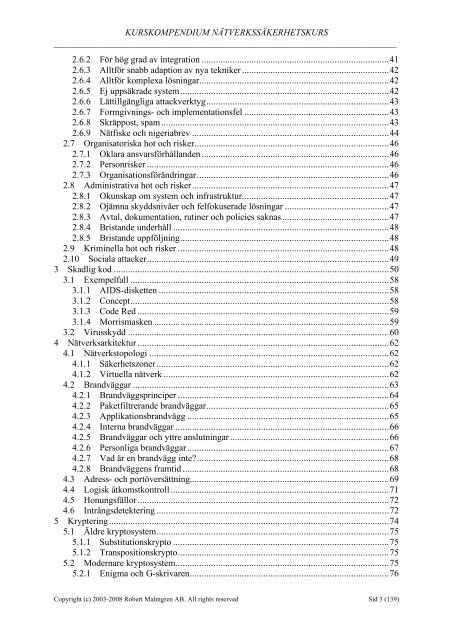
KURSKOMPENDIUM NÄTVERKSSÄKERHETSKURS<br />
___________________________________________________________________________<br />
2.6.2 För hög grad av integration ...............................................................................41<br />
2.6.3 Alltför snabb adaption av nya tekniker ..............................................................42<br />
2.6.4 Alltför komplexa lösningar................................................................................42<br />
2.6.5 Ej uppsäkrade system........................................................................................42<br />
2.6.6 Lättillgängliga attackverktyg.............................................................................43<br />
2.6.7 Formgivnings- och implementationsfel .............................................................43<br />
2.6.8 Skräppost, spam................................................................................................43<br />
2.6.9 Nätfiske och nigeriabrev ...................................................................................44<br />
2.7 Organisatoriska hot och risker..................................................................................46<br />
2.7.1 Oklara ansvarsförhållanden ...............................................................................46<br />
2.7.2 Personrisker ......................................................................................................46<br />
2.7.3 Organisationsförändringar.................................................................................46<br />
2.8 Administrativa hot och risker...................................................................................47<br />
2.8.1 Okunskap om system och infrastruktur..............................................................47<br />
2.8.2 Ojämna skyddsnivåer och felfokuserade lösningar ............................................47<br />
2.8.3 Avtal, dokumentation, rutiner och policies saknas .............................................47<br />
2.8.4 Bristande underhåll ...........................................................................................48<br />
2.8.5 Bristande uppföljning........................................................................................48<br />
2.9 Kriminella hot och risker .........................................................................................48<br />
2.10 Sociala attacker......................................................................................................49<br />
3 Skadlig kod ....................................................................................................................50<br />
3.1 Exempelfall .............................................................................................................58<br />
3.1.1 AIDS-disketten .................................................................................................58<br />
3.1.2 Concept.............................................................................................................58<br />
3.1.3 Code Red ..........................................................................................................59<br />
3.1.4 Morrismasken ...................................................................................................59<br />
3.2 Virusskydd ..............................................................................................................60<br />
4 Nätverksarkitektur ..........................................................................................................62<br />
4.1 Nätverkstopologi .....................................................................................................62<br />
4.1.1 Säkerhetszoner..................................................................................................62<br />
4.1.2 Virtuella nätverk ...............................................................................................62<br />
4.2 Brandväggar ............................................................................................................63<br />
4.2.1 Brandväggsprinciper .........................................................................................64<br />
4.2.2 Paketfiltrerande brandväggar.............................................................................65<br />
4.2.3 Applikationsbrandvägg .....................................................................................65<br />
4.2.4 Interna brandväggar ..........................................................................................66<br />
4.2.5 Brandväggar och yttre anslutningar ...................................................................66<br />
4.2.6 Personliga brandväggar.....................................................................................67<br />
4.2.7 Vad är en brandvägg inte?.................................................................................68<br />
4.2.8 Brandväggens framtid .......................................................................................68<br />
4.3 Adress- och portöversättning....................................................................................69<br />
4.4 Logisk åtkomstkontroll ............................................................................................71<br />
4.5 Honungsfällor..........................................................................................................72<br />
4.6 Intrångsdetektering ..................................................................................................72<br />
5 Kryptering......................................................................................................................74<br />
5.1 Äldre kryptosystem..................................................................................................75<br />
5.1.1 Substitutionskrypto ...........................................................................................75<br />
5.1.2 Transpositionskrypto.........................................................................................75<br />
5.2 Modernare kryptosystem..........................................................................................75<br />
5.2.1 Enigma och G-skrivaren....................................................................................76<br />
Copyright (c) 2003-<strong>2008</strong> Robert Malmgren AB. All rights reserved Sid 3 (139)