Data Encryption Based On Protein Synthesis - Nguyen Dang Binh
Data Encryption Based On Protein Synthesis - Nguyen Dang Binh
Data Encryption Based On Protein Synthesis - Nguyen Dang Binh
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
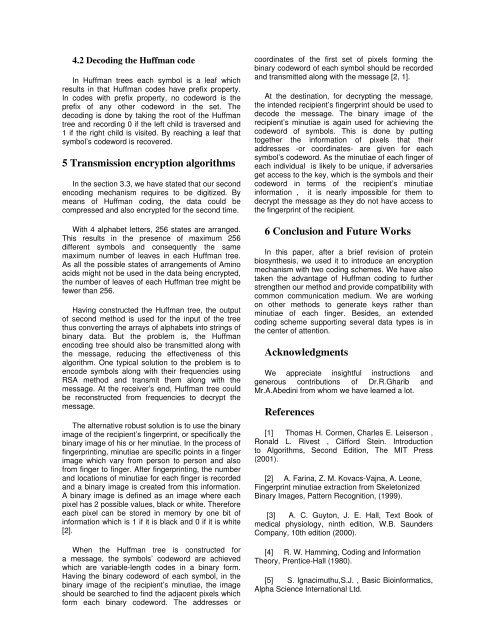
4.2 Decoding the Huffman code<br />
In Huffman trees each symbol is a leaf which<br />
results in that Huffman codes have prefix property.<br />
In codes with prefix property, no codeword is the<br />
prefix of any other codeword in the set. The<br />
decoding is done by taking the root of the Huffman<br />
tree and recording 0 if the left child is traversed and<br />
1 if the right child is visited. By reaching a leaf that<br />
symbol’s codeword is recovered.<br />
5 Transmission encryption algorithms<br />
In the section 3.3, we have stated that our second<br />
encoding mechanism requires to be digitized. By<br />
means of Huffman coding, the data could be<br />
compressed and also encrypted for the second time.<br />
With 4 alphabet letters, 256 states are arranged.<br />
This results in the presence of maximum 256<br />
different symbols and consequently the same<br />
maximum number of leaves in each Huffman tree.<br />
As all the possible states of arrangements of Amino<br />
acids might not be used in the data being encrypted,<br />
the number of leaves of each Huffman tree might be<br />
fewer than 256.<br />
Having constructed the Huffman tree, the output<br />
of second method is used for the input of the tree<br />
thus converting the arrays of alphabets into strings of<br />
binary data. But the problem is, the Huffman<br />
encoding tree should also be transmitted along with<br />
the message, reducing the effectiveness of this<br />
algorithm. <strong>On</strong>e typical solution to the problem is to<br />
encode symbols along with their frequencies using<br />
RSA method and transmit them along with the<br />
message. At the receiver’s end, Huffman tree could<br />
be reconstructed from frequencies to decrypt the<br />
message.<br />
The alternative robust solution is to use the binary<br />
image of the recipient’s fingerprint, or specifically the<br />
binary image of his or her minutiae. In the process of<br />
fingerprinting, minutiae are specific points in a finger<br />
image which vary from person to person and also<br />
from finger to finger. After fingerprinting, the number<br />
and locations of minutiae for each finger is recorded<br />
and a binary image is created from this information.<br />
A binary image is defined as an image where each<br />
pixel has 2 possible values, black or white. Therefore<br />
each pixel can be stored in memory by one bit of<br />
information which is 1 if it is black and 0 if it is white<br />
[2].<br />
When the Huffman tree is constructed for<br />
a message, the symbols’ codeword are achieved<br />
which are variable-length codes in a binary form.<br />
Having the binary codeword of each symbol, in the<br />
binary image of the recipient’s minutiae, the image<br />
should be searched to find the adjacent pixels which<br />
form each binary codeword. The addresses or<br />
coordinates of the first set of pixels forming the<br />
binary codeword of each symbol should be recorded<br />
and transmitted along with the message [2, 1].<br />
At the destination, for decrypting the message,<br />
the intended recipient’s fingerprint should be used to<br />
decode the message. The binary image of the<br />
recipient’s minutiae is again used for achieving the<br />
codeword of symbols. This is done by putting<br />
together the information of pixels that their<br />
addresses -or coordinates- are given for each<br />
symbol’s codeword. As the minutiae of each finger of<br />
each individual is likely to be unique, if adversaries<br />
get access to the key, which is the symbols and their<br />
codeword in terms of the recipient’s minutiae<br />
information , it is nearly impossible for them to<br />
decrypt the message as they do not have access to<br />
the fingerprint of the recipient.<br />
6 Conclusion and Future Works<br />
In this paper, after a brief revision of protein<br />
biosynthesis, we used it to introduce an encryption<br />
mechanism with two coding schemes. We have also<br />
taken the advantage of Huffman coding to further<br />
strengthen our method and provide compatibility with<br />
common communication medium. We are working<br />
on other methods to generate keys rather than<br />
minutiae of each finger. Besides, an extended<br />
coding scheme supporting several data types is in<br />
the center of attention.<br />
Acknowledgments<br />
We appreciate insightful instructions and<br />
generous contributions of Dr.R.Gharib and<br />
Mr.A.Abedini from whom we have learned a lot.<br />
References<br />
[1] Thomas H. Cormen, Charles E. Leiserson ,<br />
Ronald L. Rivest , Clifford Stein. Introduction<br />
to Algorithms, Second Edition, The MIT Press<br />
(2001).<br />
[2] A. Farina, Z. M. Kovacs-Vajna, A. Leone,<br />
Fingerprint minutiae extraction from Skeletonized<br />
Binary Images, Pattern Recognition, (1999).<br />
[3] A. C. Guyton, J. E. Hall, Text Book of<br />
medical physiology, ninth edition, W.B. Saunders<br />
Company, 10th edition (2000).<br />
[4] R. W. Hamming, Coding and Information<br />
Theory, Prentice-Hall (1980).<br />
[5] S. Ignacimuthu,S.J. , Basic Bioinformatics,<br />
Alpha Science International Ltd.