Communication Theory of Secrecy Systems - Network Research Lab
Communication Theory of Secrecy Systems - Network Research Lab
Communication Theory of Secrecy Systems - Network Research Lab
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
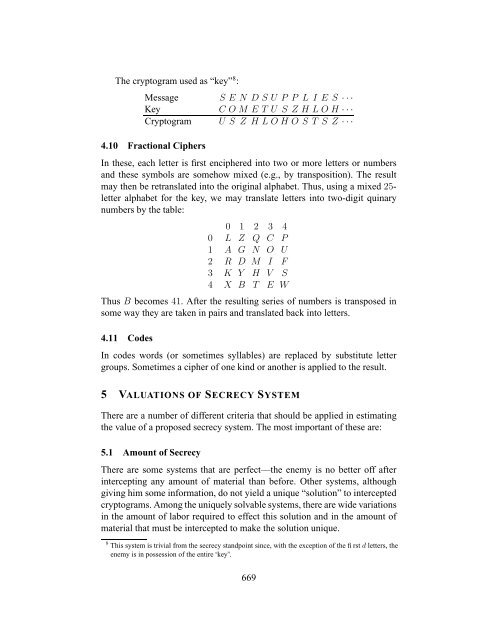
The cryptogram used as “key” 8 :<br />
Message S E N D S U P P L I E S · · ·<br />
Key C O M E T U S Z H L O H · · ·<br />
Cryptogram U S Z H L O H O S T S Z · · ·<br />
4.10 Fractional Ciphers<br />
In these, each letter is first enciphered into two or more letters or numbers<br />
and these symbols are somehow mixed (e.g., by transposition). The result<br />
may then be retranslated into the original alphabet. Thus, using a mixed 25letter<br />
alphabet for the key, we may translate letters into two-digit quinary<br />
numbers by the table:<br />
0 1 2 3 4<br />
0 L Z Q C P<br />
1 A G N O U<br />
2 R D M I F<br />
3 K Y H V S<br />
4 X B T E W<br />
Thus B becomes 41. After the resulting series <strong>of</strong> numbers is transposed in<br />
some way they are taken in pairs and translated back into letters.<br />
4.11 Codes<br />
In codes words (or sometimes syllables) are replaced by substitute letter<br />
groups. Sometimes a cipher <strong>of</strong> one kind or another is applied to the result.<br />
5 VALUATIONS OF SECRECY SYSTEM<br />
There are a number <strong>of</strong> different criteria that should be applied in estimating<br />
the value <strong>of</strong> a proposed secrecy system. The most important <strong>of</strong> these are:<br />
5.1 Amount <strong>of</strong> <strong>Secrecy</strong><br />
There are some systems that are perfect—the enemy is no better <strong>of</strong>f after<br />
intercepting any amount <strong>of</strong> material than before. Other systems, although<br />
giving him some information, do not yield a unique “solution” to intercepted<br />
cryptograms. Among the uniquely solvable systems, there are wide variations<br />
in the amount <strong>of</strong> labor required to effect this solution and in the amount <strong>of</strong><br />
material that must be intercepted to make the solution unique.<br />
8 This system is trivial from the secrecy standpoint since, with the exception <strong>of</strong> the first d letters, the<br />
enemy is in possession <strong>of</strong> the entire “key”.<br />
669