Communication Theory of Secrecy Systems - Network Research Lab
Communication Theory of Secrecy Systems - Network Research Lab
Communication Theory of Secrecy Systems - Network Research Lab
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
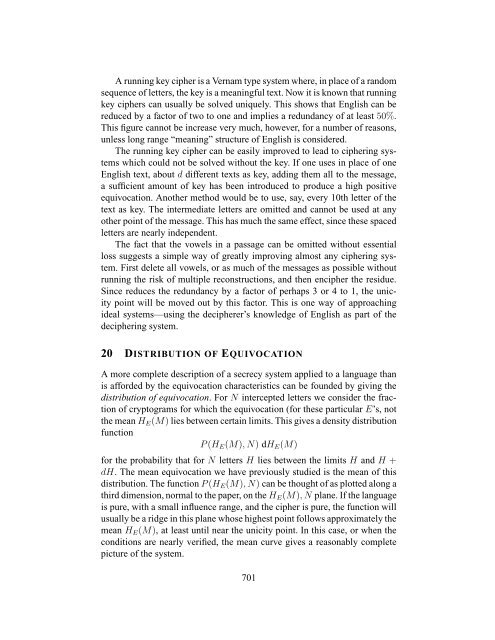
A running key cipher is a Vernam type system where, in place <strong>of</strong> a random<br />
sequence <strong>of</strong> letters, the key is a meaningful text. Now it is known that running<br />
key ciphers can usually be solved uniquely. This shows that English can be<br />
reduced by a factor <strong>of</strong> two to one and implies a redundancy <strong>of</strong> at least 50%.<br />
This figure cannot be increase very much, however, for a number <strong>of</strong> reasons,<br />
unless long range “meaning” structure <strong>of</strong> English is considered.<br />
The running key cipher can be easily improved to lead to ciphering systems<br />
which could not be solved without the key. If one uses in place <strong>of</strong> one<br />
English text, about d different texts as key, adding them all to the message,<br />
a sufficient amount <strong>of</strong> key has been introduced to produce a high positive<br />
equivocation. Another method would be to use, say, every 10th letter <strong>of</strong> the<br />
text as key. The intermediate letters are omitted and cannot be used at any<br />
other point <strong>of</strong> the message. This has much the same effect, since these spaced<br />
letters are nearly independent.<br />
The fact that the vowels in a passage can be omitted without essential<br />
loss suggests a simple way <strong>of</strong> greatly improving almost any ciphering system.<br />
First delete all vowels, or as much <strong>of</strong> the messages as possible without<br />
running the risk <strong>of</strong> multiple reconstructions, and then encipher the residue.<br />
Since reduces the redundancy by a factor <strong>of</strong> perhaps 3 or 4 to 1, the unicity<br />
point will be moved out by this factor. This is one way <strong>of</strong> approaching<br />
ideal systems—using the decipherer’s knowledge <strong>of</strong> English as part <strong>of</strong> the<br />
deciphering system.<br />
20 DISTRIBUTION OF EQUIVOCATION<br />
A more complete description <strong>of</strong> a secrecy system applied to a language than<br />
is afforded by the equivocation characteristics can be founded by giving the<br />
distribution <strong>of</strong> equivocation. For N intercepted letters we consider the fraction<br />
<strong>of</strong> cryptograms for which the equivocation (for these particular E’s, not<br />
the mean HE(M) lies between certain limits. This gives a density distribution<br />
function<br />
P (HE(M), N) dHE(M)<br />
for the probability that for N letters H lies between the limits H and H +<br />
dH. The mean equivocation we have previously studied is the mean <strong>of</strong> this<br />
distribution. The function P (HE(M), N) can be thought <strong>of</strong> as plotted along a<br />
third dimension, normal to the paper, on the HE(M), N plane. If the language<br />
is pure, with a small influence range, and the cipher is pure, the function will<br />
usually be a ridge in this plane whose highest point follows approximately the<br />
mean HE(M), at least until near the unicity point. In this case, or when the<br />
conditions are nearly verified, the mean curve gives a reasonably complete<br />
picture <strong>of</strong> the system.<br />
701