Communication Theory of Secrecy Systems - Network Research Lab
Communication Theory of Secrecy Systems - Network Research Lab
Communication Theory of Secrecy Systems - Network Research Lab
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
in which E, M and K are the cryptogram, message and key and<br />
P (E, K) is the probability <strong>of</strong> key K and cryptogram E<br />
PE(K) is the a posteriori probability <strong>of</strong> key K if cryptogram E<br />
is intercepted.<br />
P (E, M) and PE(M) are the similar probabilities for message instead<br />
<strong>of</strong> key.<br />
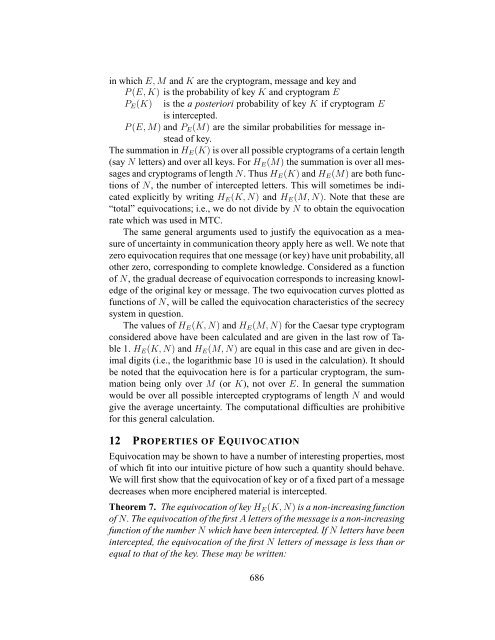
The summation in HE(K) is over all possible cryptograms <strong>of</strong> a certain length<br />
(say N letters) and over all keys. For HE(M) the summation is over all messages<br />
and cryptograms <strong>of</strong> length N. Thus HE(K) and HE(M) are both functions<br />
<strong>of</strong> N, the number <strong>of</strong> intercepted letters. This will sometimes be indicated<br />
explicitly by writing HE(K, N) and HE(M, N). Note that these are<br />
“total” equivocations; i.e., we do not divide by N to obtain the equivocation<br />
rate which was used in MTC.<br />
The same general arguments used to justify the equivocation as a measure<br />
<strong>of</strong> uncertainty in communication theory apply here as well. We note that<br />
zero equivocation requires that one message (or key) have unit probability, all<br />
other zero, corresponding to complete knowledge. Considered as a function<br />
<strong>of</strong> N, the gradual decrease <strong>of</strong> equivocation corresponds to increasing knowledge<br />
<strong>of</strong> the original key or message. The two equivocation curves plotted as<br />
functions <strong>of</strong> N, will be called the equivocation characteristics <strong>of</strong> the secrecy<br />
system in question.<br />
The values <strong>of</strong> HE(K, N) and HE(M, N) for the Caesar type cryptogram<br />
considered above have been calculated and are given in the last row <strong>of</strong> Table<br />
1. HE(K, N) and HE(M, N) are equal in this case and are given in decimal<br />
digits (i.e., the logarithmic base 10 is used in the calculation). It should<br />
be noted that the equivocation here is for a particular cryptogram, the summation<br />
being only over M (or K), not over E. In general the summation<br />
would be over all possible intercepted cryptograms <strong>of</strong> length N and would<br />
give the average uncertainty. The computational difficulties are prohibitive<br />
for this general calculation.<br />
12 PROPERTIES OF EQUIVOCATION<br />
Equivocation may be shown to have a number <strong>of</strong> interesting properties, most<br />
<strong>of</strong> which fit into our intuitive picture <strong>of</strong> how such a quantity should behave.<br />
We will first show that the equivocation <strong>of</strong> key or <strong>of</strong> a fixed part <strong>of</strong> a message<br />
decreases when more enciphered material is intercepted.<br />
Theorem 7. The equivocation <strong>of</strong> key HE(K, N) is a non-increasing function<br />
<strong>of</strong> N. The equivocation <strong>of</strong> the first A letters <strong>of</strong> the message is a non-increasing<br />
function <strong>of</strong> the number N which have been intercepted. If N letters have been<br />
intercepted, the equivocation <strong>of</strong> the first N letters <strong>of</strong> message is less than or<br />
equal to that <strong>of</strong> the key. These may be written:<br />
686