Enterprise Library Test Guide - Willy .Net
Enterprise Library Test Guide - Willy .Net
Enterprise Library Test Guide - Willy .Net
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
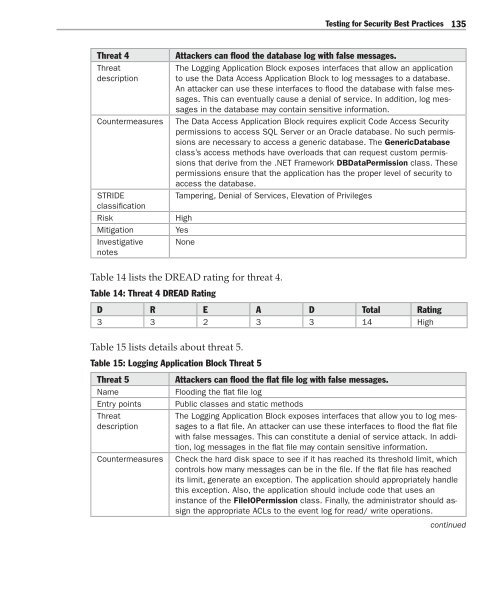
<strong>Test</strong>ing for Security Best Practices 135<br />
Threat 4<br />
Threat<br />
description<br />
Countermeasures<br />
STRIDE<br />
classification<br />
Risk<br />
Mitigation<br />
Investigative<br />
notes<br />
Attackers can flood the database log with false messages.<br />
The Logging Application Block exposes interfaces that allow an application<br />
to use the Data Access Application Block to log messages to a database.<br />
An attacker can use these interfaces to flood the database with false messages.<br />
This can eventually cause a denial of service. In addition, log messages<br />
in the database may contain sensitive information.<br />
The Data Access Application Block requires explicit Code Access Security<br />
permissions to access SQL Server or an Oracle database. No such permissions<br />
are necessary to access a generic database. The GenericDatabase<br />
class’s access methods have overloads that can request custom permissions<br />
that derive from the .NET Framework DBDataPermission class. These<br />
permissions ensure that the application has the proper level of security to<br />
access the database.<br />
Tampering, Denial of Services, Elevation of Privileges<br />
High<br />
Yes<br />
None<br />
Table 14 lists the DREAD rating for threat 4.<br />
Table 14: Threat 4 DREAD Rating<br />
D R E A D Total Rating<br />
3 3 2 3 3 14 High<br />
Table 15 lists details about threat 5.<br />
Table 15: Logging Application Block Threat 5<br />
Threat 5<br />
Name<br />
Entry points<br />
Threat<br />
description<br />
Countermeasures<br />
Attackers can flood the flat file log with false messages.<br />
Flooding the flat file log<br />
Public classes and static methods<br />
The Logging Application Block exposes interfaces that allow you to log messages<br />
to a flat file. An attacker can use these interfaces to flood the flat file<br />
with false messages. This can constitute a denial of service attack. In addition,<br />
log messages in the flat file may contain sensitive information.<br />
Check the hard disk space to see if it has reached its threshold limit, which<br />
controls how many messages can be in the file. If the flat file has reached<br />
its limit, generate an exception. The application should appropriately handle<br />
this exception. Also, the application should include code that uses an<br />
instance of the FileIOPermission class. Finally, the administrator should assign<br />
the appropriate ACLs to the event log for read/ write operations.<br />
continued